10. Little Susie is trying to train her new puppy. She is trying to figure out when the puppy should get a dog biscuit as a reward. She has concluded the following: 1. Give the puppy a biscuit if it sits and wiggles but does not bark. 2. Give the puppy a biscuit if it barks and wiggles but does not sit. 3. Give the puppy a biscuit if it sits but does not wiggle or bark. 4. Give the puppy a biscuit if it sits, wiggles and barks. 3. Don't give the puppy a treat otherwise. Use the following:
10. Little Susie is trying to train her new puppy. She is trying to figure out when the puppy should get a dog biscuit as a reward. She has concluded the following: 1. Give the puppy a biscuit if it sits and wiggles but does not bark. 2. Give the puppy a biscuit if it barks and wiggles but does not sit. 3. Give the puppy a biscuit if it sits but does not wiggle or bark. 4. Give the puppy a biscuit if it sits, wiggles and barks. 3. Don't give the puppy a treat otherwise. Use the following:
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter23: Simulation With The Excel Add-in @risk
Section: Chapter Questions
Problem 8RP
Related questions
Question
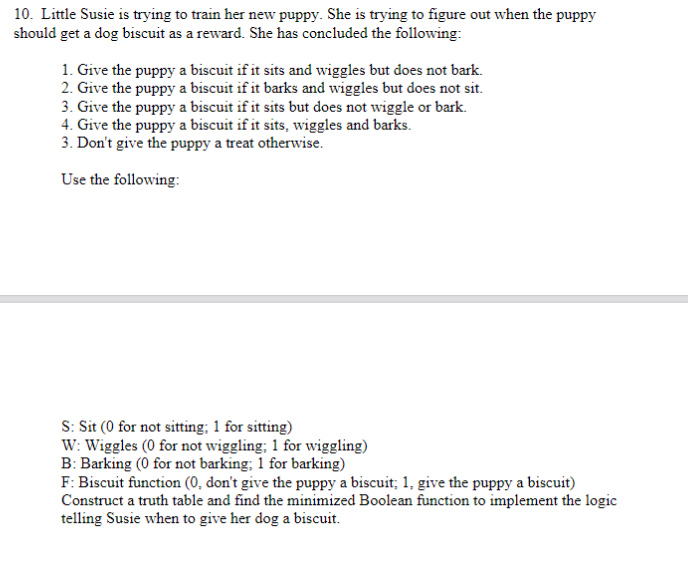
Transcribed Image Text:10. Little Susie is trying to train her new puppy. She is trying to figure out when the puppy
should get a dog biscuit as a reward. She has concluded the following:
1. Give the puppy a biscuit if it sits and wiggles but does not bark.
2. Give the puppy a biscuit if it barks and wiggles but does not sit.
3. Give the puppy a biscuit if it sits but does not wiggle or bark.
4. Give the puppy a biscuit if it sits, wiggles and barks.
3. Don't give the puppy a treat otherwise.
Use the following:
S: Sit (0 for not sitting; 1 for sitting)
W: Wiggles (0 for not wiggling; 1 for wiggling)
B: Barking (0 for not barking; 1 for barking)
F: Biscuit function (0, don't give the puppy a biscuit; 1, give the puppy a biscuit)
Construct a truth table and find the minimized Boolean function to implement the logic
telling Susie when to give her dog a biscuit.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole