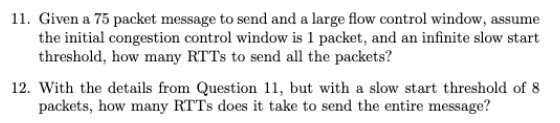
11. Given a 75 packet message to send and a large flow control window, assume the initial congestion control window is 1 packet, and an infinite slow start threshold, how many RTTs to send all the packets?
Q: Which characteristics of computer graphics are most crucial?
A: The academic field that examines how computers are utilized in the visual arts is referred to as…
Q: It's possible that data breaches may have an effect on the security of cloud storage, but how…
A: Data breaches can indeed have an impact on the security of cloud storage. Understanding the…
Q: write a java program to print the mirror image of right angled in x-direction after taking number of…
A: Required:-Write a Java program to print the mirror image of right-angled in x-direction after taking…
Q: Could you provide a brief overview of the evolution of wireless local area network (LAN) standards?
A: Wireless Local Area Network (LAN) standards, also known as Wi-Fi, have come a long way in providing…
Q: Explain in your own words what EPROM, EEPROM, and Flash Memory are and how they vary?
A: EPROM, EEPROM, and Flash Memory are all types of non-volatile memory technologies used for storing…
Q: In what manner can forensic investigators obtain authorization to retrieve data from Windows-based…
A: To extract information from Windows-based computer systems, forensic investigators must have the…
Q: Why the following statement is erroneous? SELECT dept_name, ID, avg (salary) FROM instructor GROUP…
A: The given query is trying to calculate the average salary for each department but the query contains…
Q: Could you please explain what the CSMA protocol entails?
A: Answer:The CSMA is one of the procedures that can regulate access management and allocation to some…
Q: a.Using the Google Meet platform as a practical example, discuss how it would be categorized under…
A: We will explore the practical example of Google Meet, a video conferencing platform, and its…
Q: In exArray, sort each column along the direction of the rows in ascending order. 1 # Load necessary…
A: 1Load required package numpy of the python 2Now, initialize the numpy array named exArray with…
Q: Information systems that are not interconnected generate a wide variety of issues and concerns?
A: Human error is responsible for the majority of computer-related errors, which include errors,…
Q: The Internet of Things (IoT) heavily depends on the utilization of Real-Time Operating Systems…
A: A Brief Overview of IoT and Its Functionality:The term "Internet of Things" (IoT) pertains to a…
Q: How often will you update your data to make sure you decision is reflecting the latest trends?
A: To ensure that our decisions are reflective of the latest trends, it is crucial to have a…
Q: How has the internet changed through time, and what technologies have contributed to this change?
A: The Internet is a worldwide system that links the billions of computers all over the word to one…
Q: Before wiping the hard drive, why not make a copy of the operating system and your Microsoft Office…
A: In today's digital age, our lives are intertwined with technology, relying on computers and storage…
Q: Information systems that are not interconnected generate a wide variety of issues and concerns?
A: The interoperability of information systems is essential in the digital world we live in today…
Q: Does the use of adjacency lists to represent a weighted graph present any problems?
A: The discipline of computer science relies heavily on graph theory because it makes it possible to…
Q: Write a C# Sharp prog
A: The below C# program demonstrates how to create a new list from a given list of integers removing…
Q: a.Using the Google Meet platform as a practical example, discuss how it would be categorized under…
A: The answer is given in the below step
Q: After a data breach has taken place, is it still feasible to impact the cloud's security? Is there…
A: A data breach is an incident in which sensitive information is exposed to an unauthorized person.…
Q: We've used several different kinds of computers, so we're accustomed to switching between them. Is…
A: Computers come in various forms and sizes, each designed to serve specific purposes.They come in…
Q: Both dynamic and static memory have their advantages and disadvantages?
A: Memory allocation is an essential concept in computer programming,and it can be broadly categorized…
Q: A "distributed denial of service attack" (DDoS) may be coordinated by one person. What's your…
A: A "distributed denial of service attack" (DDoS) is a cyber-attack in which multiple compromised…
Q: discuss how to creat a non-executable stack and disuss the stack's exploitable weaknesses
A: Non-executable stack (NX) is a virtual memory insurance instrument to hinder shell code infusion…
Q: Given an IP address 192.168.10.0 and the number of required subnets is 8, calculate the subnet…
A: IP addressing is a fundamental concept in networking that allows devices to communicate over a…
Q: Why is it beneficial to store data on the cloud? Which models are available, and what are the…
A: The Advantages of Storing Data in the Cloud:Cloud storage offers an open range of advantages to…
Q: Do you have the time to make a list of all the parts that go into a quantum computer and describe…
A: The following are the fundamental components that make up a quantum computer:Qubits:Qubits, which…
Q: 3. Determine the root of the following function (a) Graphically (b) By using bisection method f(x)=…
A: (a) Graphically:Define the function f(x) = 3x2 - 2x - 4.Generate a range of x values.Compute the…
Q: Write a JAVA program in which the user enters the initial velocity u, time of travel t, and the…
A: In this JAVA program, we will create a simple application that takes user inputs for initial…
Q: Has anyone ever been able to execute a distributed denial of service assault with any degree of…
A: Distributed Denial of Service (DDoS) is a type of cyber attack that aims to disrupt the normal…
Q: Is it time for a quick primer on the status of solid-state, non-volatile memory?
A: Computers that have a memory that is not volatile are able to save data even after the device is…
Q: What are the many ways in which we may communicate with one another via the internet? Can the…
A: Email is a popular form of electronic communication used for personal and professional purposes. It…
Q: a.Using the Google Meet platform as a practical example, discuss how it would be categorized under…
A: Information technology is the management and delivery of information utilizing voice, data, and…
Q: How much can a MAC-using attacker change the Tag and encrypted data? The recipient can always…
A: The acronym MAC stands for "message authentication code." A short string of information is used in…
Q: What would you say are the top five talents that a database developer or database programmer needs…
A: In the rapidly advancing world of technology, databases serve as the backbone of nearly every…
Q: Second picture is an example when the program is executed. Note: Please use "for loop", "while…
A: Logic :- (I) To generate random number in range:- arr[i][j]= Min + (int)(Math.random() * ((Max -…
Q: Title: Surveillance and Monitoring Accessible Roaming Transceiving Rover What are the objectives of…
A: In an era characterized by ever-advancing technology, the demand for innovative solutions in…
Q: Second picture is an example when the program is executed. Note: Please use "for loop", "while…
A: Logic :- (I) To generate random number in range:- arr[i][j]= Min + (int)(Math.random() * ((Max -…
Q: Data demodulation is performed differently by coherent and non-coherent psk demodulators?
A: Data demodulation is a crucial process in communication systems, especially for phase-shift keying…
Q: Formal techniques start with logic. The most prominent logics are propositional and predicate. A…
A: Formal program verification is a rigorous method of ensuring the correctness of software systems…
Q: What are the many ways in which we may communicate with one another via the internet? Can the…
A: The internet has revolutionized communication, providing a vast array of ways for individuals and…
Q: Instruction: Create a java program that generates elements (randomly from 10-75) of a 2-dimensional…
A: Here's a brief explanation of the code:Generate Random Array:The method "generateRandomArray"…
Q: Find the column that contains most number divisible by 8. There are ‘special sequences’ in the…
A: The three MATLAB tasks are as follows:Find the column that contains the most numbers divisible by 8…
Q: What are the primary differences that distinguish firewalls that are software-based from those that…
A: Firewalls play a crucial role in network security by protecting systems and data from unauthorized…
Q: "Population & Housing in San Diego County" must be analyzed. Examine any overlaps between the…
A: The analysis of population and housing dynamics in San Diego County is crucial for understanding the…
Q: In the field of quantum computing, what are some of the obstacles that must be overcom
A: In the rapidly evolving field of quantum computing, there are several significant obstacles that…
Q: PC users can access local administration settings. Some users are making unwarranted…
A: To address unwarranted security-related rule modifications by users with local administrative…
Q: List and explain clustering algorithms.
A: Clustering algorithms are unsupervised machine learning techniques used to group similar data points…
Q: An in-depth discussion of cookies, at least two types, and their effects on internet security is…
A: Cookies are small pieces of data stored on a user's device by web browsers when they visit websites.…
Q: What are some of the most significant distinctions between a traditional computer and a quantum…
A: The answer is given below step.
This a TCP question, given the context of question 11 please answer and show work for question 12
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Under the assumption of no packets loss, how long will it take TCP to send an object that is 20KB over a link with a RTT of 400 milliseconds, a MSS of 2KB, and a rate of 10KB/second when: a. TCP is in slow start, CongWin = 1 and Threshold = 10: b. TCP is in congestion avoidance, CongWin = 5 and Threshold = 54.) Suppose that a sender and a receiver are using ARQ to perform reliable data delivery. If we have to send 12 packet and window size of 4 , if every 5 th packet is being transmitted is lost, then how many retransmissions and total number of transmissions are required? (7) a. GoBack-N b. Selective RepeatA connection between two servers may transport multiple packets simultaneously. Please break down for me how much time is consumed on each phase of goods processing. Should the duration of one delay be predetermined, while the duration of the other delay is situation-dependent?
- After a timeout occurrence, we talked about doubling the timeout interval. Congestion control is achieved by the use of this method. Why does TCP require a window-based congestion-control method in addition to the doubling-timeoutinterval strategy?For the sake of this example, let's assume that a packet is being sent from its point of origin to an address at the other end of the network via the fixed route. The different delays-causing variables are also listed below: How many of the overall delays are time-dependent, and what proportion of the total delays are continuous for how long?We discussed increasing the timeout interval once a timeout occurred. This strategy is used to control traffic congestion. Why, in addition to the doubling-timeoutinterval approach, does TCP require a window-based congestion-control method?
- Consider a packet of length L that begins at end system A and travels over three links to a destination end system. These three links are connected by two packet switches. Let di, si, and Ri denote the length, propagation speed, and the transmission rate of link i, for i=1,2,3. The packet switch delays each packet by dproc. Assuming no queuing delays, in terms of di, si, Ri (i=1,2,3), and L, what is the total end-to-end delay for the packet? Suppose now the packet is 1,500 bytes, the propagation speed on all three links is 2.5*108 m/s, the transmission rates of all three links are 2 Mbps, the packet switch processing delay is 3 msec, the length of the first link is 5,000 km, the length of the second link is 4,000 km, and the length of the last link is 1,000 km. For these values, what is the end-to-end delay?Consider a packet of length L that begins at end system A and travels over three links to a destination end system. These three links are connected by two packet switches. Let di, si, and Ri denote the length, propagation speed, and the transmission rate of link i, for i=1,2,3. The packet switch delays each packet by dproc. Assuming no queuing delays, in terms of di, si, Ri, (i=1,2,3), and L, what is the total end-to-end delay for the packet? Suppose now the packet is 1,200 bytes, the propagation speed on all three links is 2.5x10^8 m/s, the transmission rates of all three links are 2 Mbps, the packet switch processing delay is 3 msec, the length of the first link is 4,000 km, the length of the second link is 3,000 km, and the length of the last link is 1,500 km. For these values, what is the end-to-end delay? In the above problem, suppose R1=R2=R3=R and dproc=0. Further suppose the packet switch does not store-and-forward packets but instead immediately transmits each bit it receives…Question 3 Consider a satellite channel running TCP/IP as shown in the figure below. Due to the long round trip time (RTT) and high bit error rate (BER) the conventional TCP congestion mechanism doesn’t work well in a satellite transmission system. 3.1 Assume traditional TCP/IP is used and that the congestion window of the TCP sender is 10k bytes, and it is in congestion avoidance (CA) state with the threshold variable equal to 8k bytes. Now, the sender receives 3 duplicated acknowledgements (ACKs). As a result, explain the effect on the congestion window size and the threshold.
- Consider a packet of length L that begins at end system A and travels over three links to a destination end system. These three links are connected by two packet switches. Let d, s, and R denotes the length, propagation speed, and the transmission rate of link i, for i=1,2,3 . The packet switch delays each packet by d . Assuming no queuing delays, in terms of d, s , R, (i=1,2,3), and L, what is the total end-to-end delay for the packet? Suppose now the packet is 1,500 bytes, the propagation speed on all three links is the transmission rates of all three links are 2 Mbps, the packet switch processing delay is 3 msec, the length of the first link is 5,000 km, the length of the second link is 4,000 km, and the length of the last link is 1,000 km. For these values, what is the end-to-end delay? In the above problem, suppose R1=R2=R3=R and dproc=0. Further, suppose the packet switch does not store-and-forward packets but instead immediately transmits each bit it receives before waiting…Consider a packet of length L that begins at end system A and travels over three links to a destination end system. These three links are connected by two packet switches. Let d, s, and R denotes the length, propagation speed, and the transmission rate of link i, for i=1,2,3 . The packet switch delays each packet by d . Assuming no queuing delays, in terms of d, s , R, (i=1,2,3), and L, what is the total end-to-end delay for the packet? Suppose now the packet is 1,500 bytes, and the propagation speed on all three links are 3125km/sec, 10000 km/sec, and 3333km/sec respectively. The transmission rates of all three links are 2 Mbps, the packet switch processing delay is 3 msec, the length of the first link is 5,000 km, the length of the second link is 4,000 km, and the length of the last link is 1,000 km. For these values, what is the end-to-end delay? In the above problem, suppose R1=R2=R3=R and dproc=0. Further, suppose the packet switch does not store-and-forward packets but…Consider a slotted ALOHA network with three nodes that always have packets to send. Suppose one of the nodes requires a mean throughput of at least 0.3 packets per slot, and that it contends for slots with probability 0.45. Suppose that one of the other nodes contends for slots with probability 0.1. What is the maximum contention probability for the third node, without violating the throughput requirement of the first node?

