111.111.111.111 74-29-9C-E8-FF-55 A 111.111.111.112 CC-49-DE-DO-AB-7D R 222.222.222.220 1A-23-F9-CD-06-9B 111.111.111.110 E6-E9-00-17-BB-4B B 222.222.222.222 49-BD-D2-C7-56-2A 222.222.222.221 88-B2-2F-54-1A-OF
Q: Why cyber kill chain?
A: The term "cyber kill chain" refers to a framework that outlines the various stages of a cyber…
Q: Give a scenario in which one of the four different methods of access control may be used. If there…
A: What is different methods of access control: Different methods of access control refer to various…
Q: Or, to put it another way, what is the purpose of the authentication procedure? Consider the…
A: Authentication is the process of verifying the identity of a user or entity attempting to access a…
Q: Consider the Linux filesystem directory listing shown here. Robert has the user account rsmith and…
A: File permissions determine the privileges or access granted to users or groups for interacting with…
Q: Denial-of-service attacks may impair email communication in several ways. Utilise your expertise to…
A: Denial-of-service (DoS) attack are sanctuary occurrence that occur what time attacker try to Prevent…
Q: Why did new hacking methods emerge? For a decent response, I need to know where you received this…
A: I can give you a general idea of why new hacking techniques are emerging.
Q: Q2. Explain step by step the process of hamming code detection and correction by using data as…
A: According to the information given;- We have to define the process of hamming code detection and…
Q: Do the methods we use to form our opinions and draw our conclusions have anything to teach us that…
A: The methods we use to form hypotheses and draw conclusions can provide useful information that can…
Q: Does your employer have an internet acceptable-use policy? Locate and review the policy. Summarize…
A: Internet Acceptable-Use Policy: An Internet acceptable-use policy is a document that outlines the…
Q: You are responsible for providing computer security training to your company's whole staff of around…
A: What is company: A company refers to an organization or business entity engaged in commercial…
Q: Why did these new types of hacking start to pop up? I need to know where you got this information so…
A: In recent times, we have witnessed the emergence of new types of hacking techniques that have…
Q: A DMZ is generally used for which services? Email Server HR Server CAD System Server Web Server
A: In computer science Demilitarized Zone also abbreviated as DMZ is a security tool used to shield and…
Q: How much more damage do false positives do to intrusion detection systems than false negatives? Why?
A: The impact of false positives and false negatives in intrusion detection systems (IDS) can vary…
Q: 1. The Children's Online Privacy Protection Act ("COPPA") was enacted to primarily prevent which of…
A: In this question we need to choose the main purpose of Children's Online Privacy Protection Act…
Q: 38. Which of the following accounts for more data breaches than any other intrusion meth A. Social…
A: Answer for given mcq is explained below
Q: Explain what Primary CIS Control was violated and why the control is critical A user receives an…
A: The term "Primary CIS Control" is not a specific control within the Center for Internet Security…
Q: The work you’ve done for your clients at the flooring company has helped them realize they have not…
A: In today's interconnected world, where cyber threats are becoming increasingly sophisticated, it is…
Q: Explain "cybersecurity" and why it's essential.
A: In this answer, we'll discuss cybersecurity and why it's essential.
Q: What laptop device prevents shoulder surfing?
A: There isn't a specific laptop device that is designed solely to prevent shoulder surfing. However,…
Q: What dangers and costs does a breach in a company's cyber defenses pose?
A: The question asks about the dangers and costs associated with a breach in a company's cyber…
Q: Does any one of these elements have a role in the issue of hackers breaking into websites?
A: The issue of hackers breaking into websites has become a major concern in today's digital world.…
Q: What factors must be considered in order to handle the issue of cyber security in a holistic manner?
A: What is cybercrime: Cybercrime refers to criminal activities conducted through digital means,…
Q: Which entity is responsible for spearheading the cybersecurity policy of the country?
A: What is cybercrime: Cybercrime refers to criminal activities conducted using computers, networks, or…
Q: Can cybercrime truths be deduced creatively?
A: In this question we need to explain whether we can deduce the cybercrime truths creatively or not.
Q: SANS' mission? What kind of impact does this have on the professional certification for information…
A: SANS stands for the SysAdmin, Audit, Network, Security it does provides information security…
Q: I think I am limiting my scope of knowledge in gathering information through the media somewhat.…
A: In today's digital age, the media plays a vital role in shaping public perception and disseminating…
Q: 71. Which of the following is least likely to be subject to Europe's General Data Protection…
A: Regardless of where the processing takes place, the General Data Protection Regulation (GDPR) is…
Q: If you work as the information security officer for a company with staff working around the globe,…
A: As an information security officer responsible for managing the network security of a company with…
Q: 32. Which of the following legal hurdles presents the greatest challenge to plaintiffs seeking to…
A: Lack of class certification (option b) and inability to name a defendant with particularity (option…
Q: 70. Which of the following is a useful analogy for thinking about data governance as a combination…
A: An effective metaphor for thinking of data governance as a collection of safeguards is a castle with…
Q: 10. Which of the following strategies is a company's best bet to avoid having to notify residents of…
A: One of the best ways to safeguard personal data from unauthorised access in the event of a data…
Q: What do you think are the best practises for firewall administration? Explain.
A: A firewall is a network security framework that monitors and controls approaching and active network…
Q: When you create a comprehensive MIS information security plan, what cyber security threats will you…
A: In today's digital age, the security of an organization's information management system (MIS) is…
Q: What is the United States' position on cybersecurity?
A: The United States' position on cybersecurity has become increasingly prominent and focused in recent…
Q: Nena works defensively and aggressively as a security professional. Nena who? Black Hat Suicide…
A: Hackers are typically confidential into a variety of categories base on their intentions, events,…
Q: Discuss credit card security and outline precautions to take.
A: A credit card is a payment card that allows consumers to borrow money from a bank or other financial…
Q: Firewalls are one option organisations such as Experian can use to prevent hackers from moving…
A: In this question we need to explain the best practice rules for the utilization of firewall.
Q: How can I operate firewalls in the most efficient manner possible?
A: Firewalls are an essential component of modern network security. They serve as a barrier between an…
Q: 54. Which of the following states has the most restrictive biometric legislation in effect? A. New…
A: The term "biometric" describes the use of a person's distinctive physical or behavioural features to…
Q: What organisation is officially responsible for supervising the United States' cybersecurity policy?
A: Cybersecurity is the process of preventing unauthorised access, theft, damage, and disruption to…
Q: What can we conclude about internet crime based on this information?
A: Internet crime, also known as cybercrime, poses significant challenges in the digital age.
Q: Is there anything we can learn by exercising imagination and deducing truths from the cybercrime…
A: Exploring the realm of cybercrime can offer valuable insights and knowledge through the exercise of…
Q: 11. Which of the following statements accurately describe National Security Letters ("NSLs")? A.…
A: The FBI may issue National Security Letters ("NSLs") to request specific information, such as…
Q: What is the netcat command on Linux that allows a system at 192.168.70.32 to setup a listening…
A: Answer is as follows
Q: How does a honeypot operate in conjunction with other security measures like an IDS and a firewall?
A: Honeypot Honeypot is a security mechanism that creates the virtual trap to the attackers.…
Q: Does cybercrime need more study at this time?
A: Continuing research is essential to resolving cyber threats and protecting people, organizations and…
Q: nformation security personnel may have prevented the Target breach.
A: The Target breach serves as a significant example highlighting the importance of information…
Q: Identity theft is one of the most widespread types of cybercrime, and it affects millions of people…
A: Identity theft has become one of the most common forms of cybercrime in recent years. Criminals use…
Q: Instructions Research the eight exceptions to information blocking. What are the objectives of these…
A: The 21st Century Cures Act, enacted in 2016, includes eight data protection exemptions that allow…
Q: 34. Which rule within the HIPAA Privacy Rule requires transfer of only the protected health…
A: In this question we need to choose the correct HIPAA privacy rule which requires transfer of the…
In the following figure, assume computer A is sending a message to computer B. For the message from computer A to router R, what is the source and destination IP and the source and destination MAC?
Source IP:
Destination IP:
Source IP:
Destination MAC:
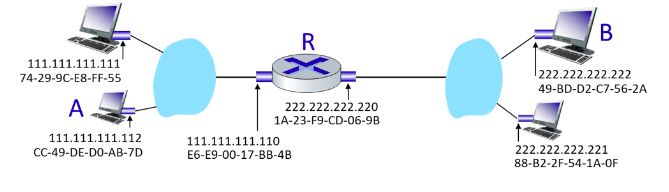
Step by step
Solved in 3 steps
