13. Under the Electronic Communications Privacy Act ("ECPA"), when may a person lawfully monitor another's telephone call? A. When one of the parties to the call has given consent. B. Only when both parties to the call have given their consent. C. Ten days after providing notice of the monitoring to both parties of the call. D. Monitoring telephone calls is illegal under all circumstances.
13. Under the Electronic Communications Privacy Act ("ECPA"), when may a person lawfully monitor another's telephone call? A. When one of the parties to the call has given consent. B. Only when both parties to the call have given their consent. C. Ten days after providing notice of the monitoring to both parties of the call. D. Monitoring telephone calls is illegal under all circumstances.
Related questions
Question
please choose the most correct anwser.
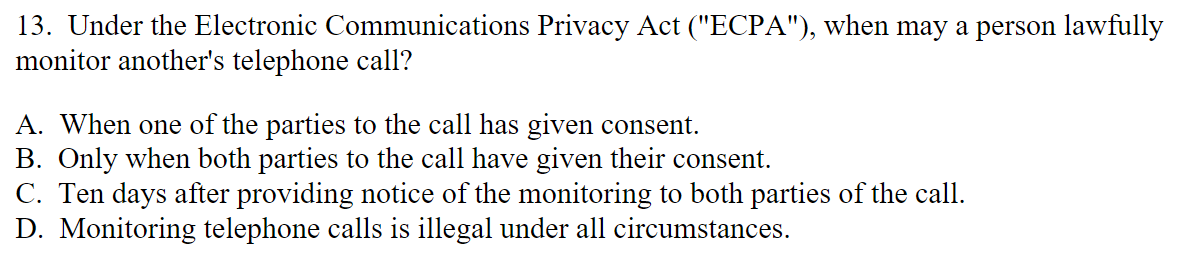
Transcribed Image Text:13. Under the Electronic Communications Privacy Act ("ECPA"), when may a person lawfully
monitor another's telephone call?
A. When one of the parties to the call has given consent.
B. Only when both parties to the call have given their consent.
C. Ten days after providing notice of the monitoring to both parties of the call.
D. Monitoring telephone calls is illegal under all circumstances.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps
