14 of 15
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter18: Stacks And Queues
Section: Chapter Questions
Problem 21SA
Related questions
Question
Transcribed Image Text:l LTE
10:05
Done
14 of 15
40 Listen
2
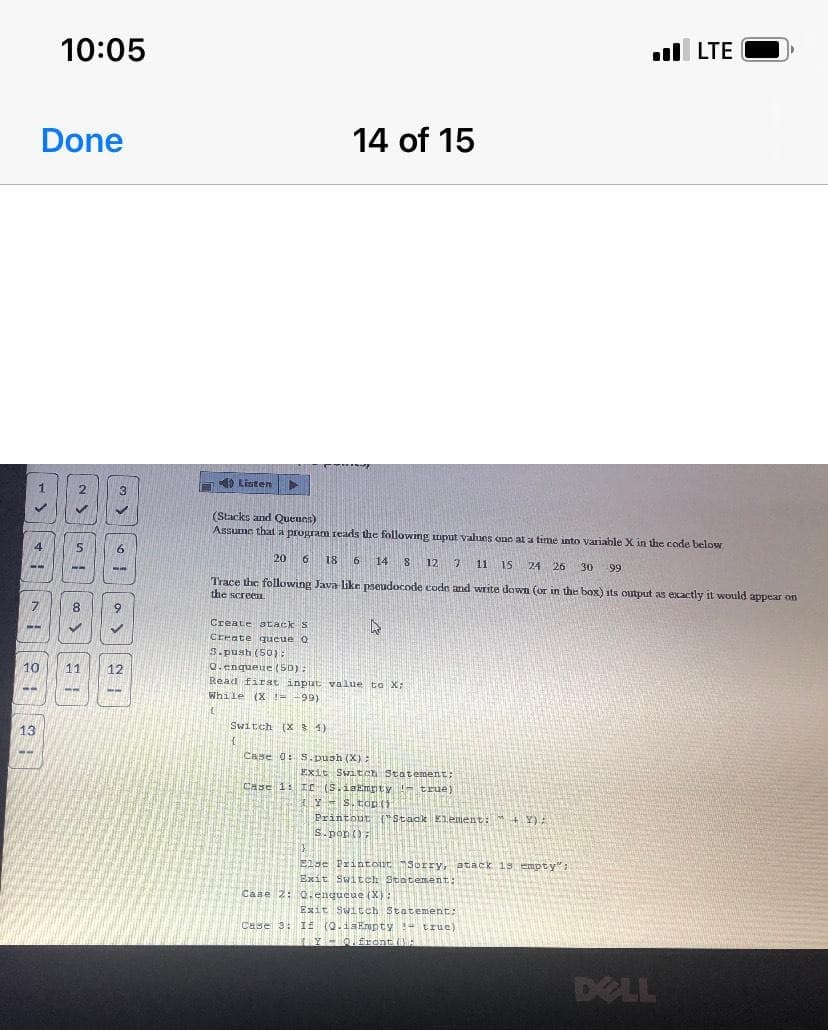
(Stacks and Queues)
Assume that a program reads the following imput values one at a time into variable X in the code below
4
6.
20 6
18 6 14 8 12 7
15 24 26
30
99
--
---
Trace the following Java like pseudocode eode and write down (or in the box) its output as exactly it would appear on
the screen
7.
8
Create atack S
Create queue O
S.push (50):
Q. enqueue (50):
10
11
12
Read first input value to X:
While (X != -99)
Switch (X 4)
13
Case 0: S. push (X):
Exit Switch Statement;
Case 1: IC (S.isEmpty !- true)
y - s. top
Y S. tdp
Printout Stack Element: + Y):
s.pop();
Else Printoiit Sorry, atack 1s empty":
Exit Switch Statement:
Case 2: 0. enqueue (X):
Exit Switeh Statement:
Case 3: If (Q.iaErmpty:- true)
Y-O front (:
DELL
Transcribed Image Text:UNJOWN Browser + Webcam
Time Left:1:25:10
Wondemu Damite: Attempt 1
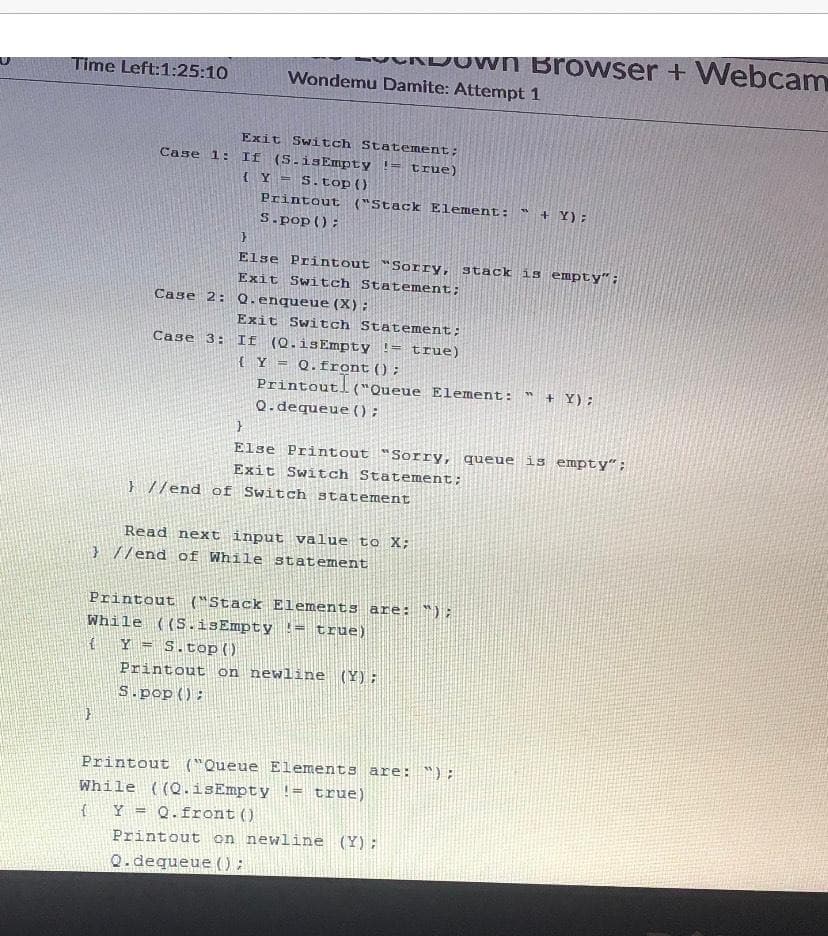
Exit Switch Statement;
Case 1: If (S.isEmpty != true)
{Y =
S.top ()
Printout ("Stack Element: " + Y):
S.pop ();
Else Printout "Sorry, stack is empty":
Exit Switch Statement;
Case 2: Q. enqueue (X):
Exit Switch Statement;
If (Q.isEmpty != true)
{Y = Q.front();
Printout!
Q.dequeue () ;
Case 3:
("Queue Element:
+ Y);
Else Printout "Sorry, queue is empty";
Exit Switch Statement;
} //end of Switch statement
Read next input value to X;
} //end of While statement
Printout ("Stack Elements are: ");
While ((S.isEmpty != true)
Y = S.top)
Printout on newline (Y);
S.pop():
Printout ("Queue Elements are: ");
While ((Q.isEmpty != true)
Y = Q.front()
Printout on newline (Y);
%3!
Q.dequeue () :
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning