14. 215 => BIN a. 1101 0111B b. 1101 1000B c. 1101 1001B d. 1101 1010B
Q: How do you manage security in an office with shared resources such as a printer?
A: Solution:
Q: When it comes to dealing with computers and technology, what are the benefits of being computer…
A: Introduction: In order to improve language learning, a combination of computer-related hardware or…
Q: Create a java program that generates elements (randomly from 10 – 75) of a 2-dimensional array (5x5)…
A: As per our company guidelines, we are supposed to answer only three subparts. Please repost other…
Q: What is the relationship between a database and an information system, and how does this…
A: INTRODUCTION: Any collection of data or information that is particularly arranged for quick search…
Q: What are some reasons for restoring data if your backups come up successful? Also, from a compliance…
A: What are some reasons for restoring data if your backups come up successful? Data restore makes a…
Q: Describe a consensus procedure and the issue it addresses.
A: Introduction: Blockchain, a distributed decentralized network, has immutability, security, privacy,…
Q: Why is it more common to engage in multitasking, also known as multithreading, as opposed to having…
A: Having multiple processes means, each process having its own virtual memory. These are separate.…
Q: 14 What will be the output of the given program class A { int m-20, n-D30; void display() t of stion…
A: The problem is based on the basics of inheritance in java programming language.
Q: Explain how to design e-commerce software that adheres to the separation of concerns principle.
A: Deciding on the boundaries of issues in software design involves setting criteria. There should be a…
Q: Why is multitasking, or multithreading, more common than background processes? Explain.
A: Multitasking means at a time more tasks are run in the CPU by shared the processor. That means…
Q: How many gates are needed to implement equation F- XYZ+ XYZ + XZ , Draw the equivalent circuit…
A:
Q: - Construct a MATLAB function to apply the formula y = x for any input value.
A: The following is the required MATLAB function for calculating the forth power of the input: function…
Q: Explain the many types of memory technology.
A: Introduction: Memory is a computing system or component that stores data in a computer or other…
Q: router and hub are a network devices
A: Note: As per bartleby guidelines, I have answered only first two question in step 2.
Q: Write a C++ program to sort characters (numbers and punctuation symbols are not included) in a…
A: Program code: #include <iostream> using namespace std; //main function int main() {…
Q: What exactly is fragmentation, and how does it effect your life? Provide examples to distinguish…
A: Fragmentation is a problem where the memory blocks cannot be allocated to the processes due to their…
Q: What are the consequences of the cloud computing revolution? Have you got Collaboration on your…
A: The goal of the research is to provide an overview of the advantages and dangers of cloud computing…
Q: What is the difference between the Physical Data Model and the Logical Data Model?
A: Difference between physical amd logical data model is explained in step 2
Q: Q:write the Boolean function for the following the micro - operation F F AVB V A'A B O F=(X+Y) +X'.…
A: The answer is (X+Y)+X' . Y (option 1) Explanation:- we have given the micro operation that is A v B…
Q: Exercise 4 Write a program that uses nested for loops to print literally the following…
A: Note: As No programming Language is mention in the question so I will answer this question using…
Q: How do multimedia systems work? Explain the problems that multimedia systems run into and what they…
A: Introduction: A multimedia system is in charge of developing a multimedia application. A multimedia…
Q: Distinguish the significance of discrete mathematics in computer science and mathematics.
A: Importance of discrete mathematics in computer science and mathematics: Discrete mathematics is…
Q: Provide a mechanism for identifying the number of key components in a dataset that should be…
A: INTRODUCTION: Here we need to provide a method for determining and the number of major components in…
Q: How was the NOKIA implementing the concept of design and evaluation together? in human-computer…
A: INTRODUCTION: Nokia, along with Apple, which pioneered the smartphone as we know it today, has been…
Q: Why aren't the people responsible for designing and deploying the database and applications also in…
A: Introduction: Your business objectives heavily influence the deployment pattern you pick. For…
Q: this is an R programming
A: Given:
Q: 9. Show that (p V q) ^ (¬p V r) → (q V r) is a tautology.
A:
Q: Multitasking, often called multithreading, is more common than background processes. Explain.
A: What is Multitasking? Multitasking is the ability of hardware, software, or any computer device to…
Q: how to add listbox elements from the properties window to a listbox
A: Given: The list box elements may be filled in either via the properties window or during runtime. To…
Q: How do you keep an office printer, for example, secure while everyone in the organisation has access…
A: Introduction: Security: When numerous distant computers are connected to the same local area network…
Q: A GSM system uses 124 channels and each channel is dded intoime sots. What is the maimum umber of…
A: The answer is
Q: The advantages of vertical and horizontal partitioning differ. What exactly are they?
A: Intro The benefits of vertical and horizontal partitioning?
Q: Q:Examples of interrupts caused by internal error conditions like (one of them is not)
A: Lets see the solution.
Q: Q:write the Boolean function for the following the micro - operation F+ AVBVA'A B O F=(X+Y) +X'. Y O…
A: Option A is correct answer
Q: Define a class called Box. Objects of this class type will represent boxes (that can store things).…
A: Programclass Box: """ Box class""" def __init__(self, label, width, height): """…
Q: Write a JAVA program that will maintain a phone directory using Classes, and Objects. The program…
A: Java code for the above question: The PhoneDirectory class: import java.io.*; public class…
Q: Design a 3 variable logical function, using 4-to-1 and 2-to-1 MUXS types only. F(x, y, z)=E m(1, 2,…
A: To design a 3 variable logical function using 4-to-1 and 2-to-1 MUXs
Q: Provide some concrete examples to illustrate the key distinctions between a two-tier and a…
A: distinctions between a two-tier and three-tier application architecture. Two-Tier Database…
Q: Identify assembly constraints used in Autodesk Inventor 2021.
A: Note: This is a multiple-question-based problem. As per company guidelines, only the first question…
Q: Q:A CISC has large variety of addressing modes typically O from 5 to 20 different modes O from 10 to…
A: The computer with large number of instructions is classified as complex instruction set computer,…
Q: research of bandwith impact on performance
A: Introduction: Most data can be sent through an internet connection in a certain period of time.…
Q: There are several advantages to employing both logical and physical partitions on the same personal…
A: A partition is a way to tell your computer that you want to split your hard drive into a number of…
Q: Managing security in a workplace with shared resources like a printer and other computers is a…
A: Introduction: Security: When numerous distant computers are connected to the same local area network…
Q: What exactly do you mean when you say static semantics? Give examples of static semantic norms that…
A: Static Semantic Rules: These type of rules are not directly related to the meaning of an executing…
Q: In the discipline of computer science, what role does Human Computer Interaction (HCI) play? What…
A: Given: What function does Human-Computer Interaction (HCI) play within the field of computer…
Q: Write a DHCP report (Dynamic Host Configuration Protocol). A research review, benefits, and…
A: Fill out a DHCP report (Dynamic Host Configuration Protocol). A review of the literature and…
Q: Converting from.. to ., include divide by two, to keep track of the remainder O Binary to Decimal…
A: The conversion of the decimal to binary includes the division by two with keeping track of the…
Q: What is "gid computing"? What is "cloud computing"?
A: Given: Grid computing is the utilisation of a large number of devices, generally distributed…
Q: Justify why record allocation to blocks affects database system performance significantly.
A: The question is why record allocation to blocks affects database system performance significantly.
Q: 2:Examples of interrupts caused by hternal error conditions like (one of hem is not)
A: Lets see the solution.
This is all about BINARY CODES... PLEASE GIVE SHORT SOLUTION ONLY PLEASE! show the process how you are able to arrive with your chosen answer
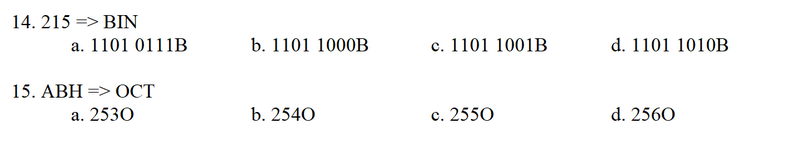
Step by step
Solved in 2 steps with 1 images

- An ISBN-10 (International Standard Book Number) consists of 10 digits: d1d2d3d4d5d6d7d8d9d10. The last digit, d10, is a checksum, which is calculated from the other nine digits using the following formula: (d1 * 1 + d2 * 2 + d3 * 3 + d4 * 4 + d5 * 5 + d6 * 6 + d7 * 7 + d8 * 8 + d9 * 9) % 11 If the checksum is 10, the last digit is denoted as X according to the ISBN-10 convention. Write a program that prompts the user to enter the first 9 digits and displays the 10-digit ISBN (including leading zeros). Sample Run 1 Enter the first 9 digits of an ISBN as a string: 3601267 Incorrect input. It must have exact 9 digits Sample Run 2 Enter the first 9 digits of an ISBN as a string: 013601267 The ISBN-10 number is 0136012671 Sample Run 3 Enter the first 9 digits of an ISBN as a string: 013031997 The ISBN-10 number is 013031997X **PYTHON***python: def dna_slice(strand, first_nucleotides, last_nucleotides): """ Question 3 - Regex You are working with a long strand of DNA. Your task is to find and return the length of the first substrand that begins with the two-letter sequence specified in first_nucleotides and ends with the sequence specified in last_nucleotides. THIS MUST BE DONE IN ONE LINE. Args: strand (str) first_nucleotides (str) last_nucleotides (str) Returns: int strand_1 = 'TATGGGTCGAGCATGT' >>> dna_slice(strand_1, 'AT', 'CG') 8 >>> dna_slice(strand_1, 'GT', 'TG') 10 """ strand_1 = 'TATGGGTCGAGCATGT' pprint(dna_slice(strand_1, 'AT', 'CG')) pprint(dna_slice(strand_1, 'GT', 'TG'))This is Computer Machine Architecture! Please include comments in the code You are to write a program in MIPS that computes N! using recursion. Remember N! is the product of all the numbers from 1 to N inclusive, that is 1 x 2 x 3 x (N – 1) x N. It is defined as 1 for N = 0 and is undefined for values less than 0. The programs first requests the user to input the value of N (display a prompt first so the user knows what to do). If the input value is less than 0, the program is to display “N! undefined for values less than 0” and then requests the user to input the value of N again. If the value input is non-negative, it is to compute N! using a recursive function, that is one that calls itself.
- Binary numbers need more places for counting because: A. 0's and 1's can be added in front of them B. 0's and 1's have to be properly placed C. They are always big numbers D. Binary base is small E. None of the aboveAssignment for Computer Architecture: N Factual by Recusion *please have comments in the code* You are to write a program in MIPS that computes N! using recursion. Remember N! is the product of all the numbers from 1 to N inclusive, that is 1 x 2 x 3 x (N – 1) x N. It is defined as 1 for N = 0 and is undefined for values less than 0. The programs first requests the user to input the value of N (display a prompt first so the user knows what to do). If the input value is less than 0, the program is to display “N! undefined for values less than 0” and then requests the user to input the value of N again. If the value input is non-negative, it is to compute N! using a recursive function, that is one that calls itself. You are to have your name, the assignment number, and a brief description of the program in comments at the top of your program. Since this is an assembly language program, I expect to see comments on almost every line of code in the program. Also make the…C++ 3.23 LAB: Interstate highway numbers Primary U.S. interstate highways are numbered 1-99. Odd numbers (like the 5 or 95) go north/south, and evens (like the 10 or 90) go east/west. Auxiliary highways are numbered 100-999, and service the primary highway indicated by the rightmost two digits. Thus, I-405 services I-5, and I-290 services I-90. Given a highway number, indicate whether it is a primary or auxiliary highway. If auxiliary, indicate what primary highway it serves. Also indicate if the (primary) highway runs north/south or east/west. Ex: If the input is: 90 the output is: I-90 is primary, going east/west. Ex: If the input is: 290 the output is: I-290 is auxiliary, serving I-90, going east/west. Ex: If the input is: 0 the output is: 0 is not a valid interstate highway number.
- Binary-Decimal / Decimal Binary . Between 0 and 255 a number will be decided randomly by computer. Then asks to user 3 times a random digit of binary value of the that number. If user enters wrong number for a digit program will select another random number and ask random times random digit. Every time user enters input will be counted as one hour in that planet. For example: Computer selected number as 163 ( Which is 10100011) What is the digit 2 (question 1/3) :User enter 1 CorrectWhat is the digit 4 (question 2/3) : User enter 0 CorrectWhat is the digit 7 (question 3/3) : User enter 0 CorrectUser finished the quest with 3 input .4.16 LAB: Interstate highway numbers Primary U.S. interstate highways are numbered 1-99. Odd numbers (like the 5 or 95) go north/south, and evens (like the 10 or 90) go east/west. Auxiliary highways are numbered 100-999, and service the primary highway indicated by the rightmost two digits. Thus, I-405 services I-5, and I-290 services I-90. Given a highway number, indicate whether it is a primary or auxiliary highway. If auxiliary, indicate what primary highway it serves. Also indicate if the (primary) highway runs north/south or east/west. Ex: If the input is: 90 the output is: I-90 is primary, going east/west. Ex: If the input is: 290 the output is: I-290 is auxiliary, serving I-90, going east/west. Ex: If the input is: 0 the output is: 0 is not a valid interstate highway number. Ex: If the input is: 200 the output is: 200 is not a valid interstate highway number. See Wikipedia for more info on highway numbering. 344614.2153518.qx3zqy7 Use Python. Don't use Java cause that's…Hello. Please answer the following Algorithms question correctly. You don't have to give a long explanation.*If you answer the question correctly, I will give you a thumbs up. Thanks.Question: The following set of points is in two-dimensional space. Determine the distance between the closest two points in the set (using standard Euclidean distance). If needed, you can write code for the question. Each answer should be given rounded to three decimal digits. {{197.351, 4.27984}, {3.06597, 128.957}, {37.99, 74.3384}, {124.171,181.56}, {185.334, 105.891}, {67.9829, 27.9514}, {55.4808, 5.43746},{172.69, 75.6131}, {105.146, 113.841}, {122.043, 118.358}, {158.448,153.185}, {55.2954, 90.2764}, {117.584, 107.245}, {27.6208, 124.549},{170.213, 27.1905}, {98.635, 109.141}, {171.204, 113.844}, {116.499,84.3058}, {24.0263, 29.095}, {108.102, 100.635}, {143.54, 188.221},{25.5321, 111.688}, {157.607, 68.0304}, {51.4829, 68.6934}, {169.019,102.569}, {147.57, 87.6102}, {137.112, 9.2236}, {25.7515,…
- Numbers between 0 and 15 are stored in the memory location starting from physical address B000Fh randomly. Write a program which finds the element order number in the string starting from 0 to 15 and writes to physical address C000Fh. (Eg: "1" is 2nd element in the first string, "2" is 4th element, ....etc)JAVA and Netbeans Using Looping Statement, Create a simple Multiplication Table for user input number (same as below):C++ Language Write a program that prints a custom conversion table from Celsius temperatures to Fahrenheit and Newton (Links to an external site.) temperatures. The formula for the conversion from Celsius to Fahrenheit is : F=9/5*C+32 F is the Fahrenheit temperature, and C is the Celsius temperature. The formula for the conversion from Celsius to Newton is C = 100/33*N N is the Newton Temperature and C is the Celsius temperature Your program should prompt the user for a lower value and upper value for a range of temperatures in Celsius. It should then prompt the user for the amount they want to increment by. Then use a loop to output to a file named conversion_table.txt a table of the Celsius temperatures and their Fahrenheit and Newton equivalents within the range of values using the increment given by the user. Make sure to format your output to 2 decimal places. INPUT VALIDATION: Ensure the second number is greater than the first number, and make sure the increment is greater…

