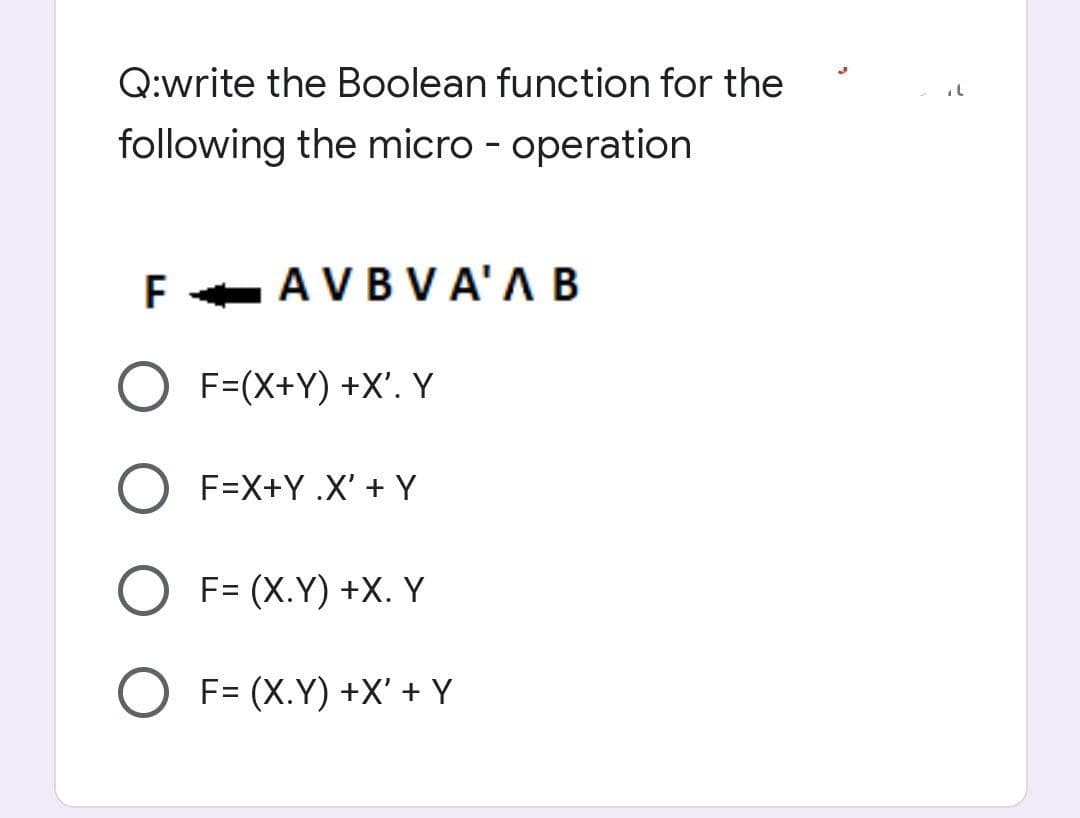
Q:write the Boolean function for the following the micro - operation F F AVB V A'A B O F=(X+Y) +X'. Y O F=X+Y .X' + Y F= (X.Y) +X. Y F= (X.Y) +X' + Y
Q: If all you have is a lousy security system, how are you going to stop technology?
A: By adopting the following actions, we can restrict the use of technologies with weak security.
Q: When packets traverse networks, what happens to their MAC addresses? When IP addresses traverse…
A: Intro A network consists of two or more computer that are linked in order to share resources and…
Q: re about Sequential Access Files and how I may p
A: Below the process how can you put Sequential Access Files
Q: The shortest route between the source and the destination should be determined in a backbone…
A: This question tells you how to find the shortest path from the source to the destination in a…
Q: It's possible that our LMS will be the target of a denial-of-service (DDOS) assault. In what ways…
A: DoS Attack: Denial-of-service (DoS) attacks target networks, websites, and online resources to deny…
Q: Distinguish the function of a computer system's server in great detail.
A: The server is the computer that is providing information or services to the other computer.
Q: Because today's computers are so powerful, this is the situation. What factors influenced the rise…
A: Introduction: Computers have always been powerful, but they are now almost ubiquitous. Computers may…
Q: Page 1: Briefly describe your first selected domain and explain the most likely risks, threats, and…
A: Domain: Within the Internet, a domain name is a string that denotes an area of administrative…
Q: Justify why record allocation to blocks affects database system performance significantly.
A: The question is why record allocation to blocks affects database system performance significantly.
Q: Duality Principle can be : * O X(XY) = XY + XX O X(XY) = X + XY O X(XY) = YX + Y O ALL ARE WRONG O O
A: The answer is below --
Q: Ql\ Write C++ program to create a base class named Person that includes variables: name and age and…
A: In this question we have to write the programming in C++ for derived and base classes where we will…
Q: Mux, is a device that can be use to * O select one from many O many from one parallel input to…
A: The given question are multiple choice selected question.
Q: Compression using MP3 Describe in your own words what sub-band coding is in acoustics, and how it…
A: Explain what sub-band coding is in acoustics and how it is applied in MP3 compression in your own…
Q: What do you mean when you say "network security
A: What do you mean when you say "network security"? Answer: Network security is a set of technologies…
Q: How do you get the computer to look for operating system boot files on the CD-ROM before it scans…
A: Booting is the process of launching the operating system when a computer is turned on. It is the…
Q: What exactly is an infrastructure-based wireless network? Apart from infrastructure, what else does…
A: Introduction: Infrastructure-based networks are separated into those that enable mobile device…
Q: How do you keep an office printer, for example, secure while everyone in the organisation has access…
A: Security: Shared resources are any devices that are accessible by many distant computers at the same…
Q: Please give the proof process: 2n3 + 3n +10 = 0( n³).
A:
Q: write a java program to print the mirror image of right angled in x-direction after taking number of…
A: Write a java program to print the mirror image of right angled in x-direction after taking number of…
Q: Which current cybercrime tendencies should you be aware of? What should law enforcement do in…
A: Hackers rely on human error for many of their methods to penetrate businesses' computer networks.…
Q: Decoder can be considered as : * MUX O DEMUX ENCODER O ADDER
A: Answer is in step 2
Q: Q: A CISC has large number of instructions typically from 100 to 250 instructions. from 200 to 250…
A: Answer in step 2
Q: The redundancy provided by network segmentation ensures high availability. With relevant visuals,…
A: Given: Network segmentation divides a network into smaller networks; network isolation creates and…
Q: When it comes to cloud backup, what's the difference between "cloud storage" and "cloud backup"?
A: Introduction: Cloud backup may be described as software that safeguards your data, files, and system…
Q: When we talk about "artificial neural networks," we're talking about...
A: Introduction: The purpose of the component of artificial intelligence known as an artificial neural…
Q: Mux, is a device that can be use to O select one from many O many from one O parallel input to…
A: INTRODUCTION: Here we need to tell MUX is a device that can be use to.
Q: Examine how users of PCs and mobile devices respond to software and application problems. Create a…
A: Any kind of portable computer may be categorized as a "mobile device." Many of the same operations…
Q: The process of interrupt is considered as: Select one: O a. Synchronous O b. Asynchronous O c. A & B…
A: answer is
Q: hings to keep in mind while upgrading the components in your laptop
A: Upgradation of components in a laptop should be done crucially so as to get the best result.
Q: Consider the dangers and opportunities associated with cloud security. Provide specific examples…
A: Given: The architecture and strategy for cloud security are weak. Identity, credential, access, and…
Q: Why is it that almost every technological component of our life
A: Technology in our life: Modern technology has enabled the development of multifunctional gadgets…
Q: A social network like Facebook has access to so much personal information that users may have…
A: A social network like Facebook has access to so much personal data that users may be concerned about…
Q: e equivalent circuit using.
A: XYZ +XZ XZ(Y+1) XZ
Q: Emails from high-ranking individuals are sent to a server that handles them. When it comes to email…
A: High-ranking: Answer Most firms use Gmail or Outlook, so this step is straightforward. "We utilize…
Q: The process of interrupt is considered as:
A: here in the given question ask process of interrupt is synchronous or asynchronous.
Q: Draw the Ladder Logic symbols of: A. Normally Open contact. B. Normally Closed contact. C. Output or…
A: Draw the Ladder Logic symbols of: A. Normally Open contact. B. Normally Closed contact. C. Output or…
Q: Describe the benefits and drawbacks of designing business-specific apps rather than relying on…
A: The answer is given below.
Q: Provide some rules for correctly citing sources. What are the ramifications of stealing someone…
A: The research works or articles are an important and integral part of the work and advancements made…
Q: 1) Create a new Java Project named Final 2) Create a superclass VehicleRental a. Instance private…
A: Code: import java.text.DecimalFormat;class VehicleRental{ private int year; private String…
Q: Write a well-documented C++ program consisting of the following two functions. Write a function that…
A: #include<iostream>using namespace std;//below the function named called first void…
Q: What are your thoughts on eavesdropping and network sniffing? What is it about them that makes them…
A: Wiretapping is a method for passively monitoring and analyzing the data flow inside a network. The…
Q: A cellular network is designed to achieve a maximum data rate of 1 Gbps in the downlink in a 20 MHz…
A: A cellular network is designed to achieve a maximum data rate of 1 Gbps in the downlink in a 20 MHz…
Q: 4) Here's an example of an applet that a lamp with a spotted shade. Below has the complete code for…
A: Explain the given code Run and compile the lamp applet program Lets see the answer in step 2
Q: When it comes to session, what are the drawbacks?
A: In session stickiness, also known as session persistence, a load balancer builds an affinity between…
Q: What criteria should be used to assess a cloud computing service by a company?
A: Faster delivery times and cheaper infrastructure costs are transition-specific benefits. To begin,…
Q: Describe each assessment method in the realm of human-computer interaction in a few words. Testing…
A: Human-computer interaction (HCI) research, which is a multidisciplinary field of study, places a…
Q: Find three server options that a local bank may employ.
A: Introduction: It is a bank that operates for business reasons inside a community. It takes deposits,…
Q: Remove all errors from the C++ program given below asap. #include using namespace std; int main(){
A: here in the given question they ask for a remove all error from c++ program.
Q: How do the nodes of the Adhoc Network know when the topology of the network changes?
A: In wireless Ad hoc network topology, wireless capable devices communicate directly each other…
Q: What are the main distinctions between conventional on-premises data centers and cloud settings when…
A: On-premises solutions are infinitely customizable.
Step by step
Solved in 2 steps

- Write the equivalent infix expression for the following postfix expressions.a. x y * z + t -b. x y z + * w u / - c. x y - z u / * t s + -d. x y z w + - *After simplification of Boolean expression F=x+[(x+y')x]' , value of F will be waht the answerWrite a Boolean function in four variables, w, x, y, z, which equals 1 whenever an odd number of the variables have a value of 1.
- Minimize the following expression using Boolean rules: F=XY+X(Y+Z)+Y(Y+Z)Implement the following Boolean function using a multiplexer. Use A, C and D as the select lines, where A is the MSB and D is the LSB. Answer the following questions. Include a systematic solution for you answer, if applicable.1. What is the output when A=0, B=1, C=1 and D=0?A. +5VB. 0VC. B’D. More than one of the choicesE. None 2. What is the output when A=0, B=1, C=0 and D=0?A. +5VB. 0VC. BD. More than one of the choicesE. None2. Look for the dual of the following Boolean expressions:a. xyz + x'y'z'b. xz' + x⋅0 +x'⋅1
- 1) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’yz+x’yz’+xy’z’+xyz+xyz’ , can be written as: 2) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’y’z+x’yz+x’yz’+xy’z’+xyz’ , can be written as: 3)convert the following decimal fractions to binary with a maximum of six places to the right of the binary point: 1)25.84375 2)57.55 3)80.9065 4) Convert the following binary fractions to decimal: 1)100001.111 2)111111.10011 3)1001100.1011 5) Fill in the blank. The representation of 60 in binary using 8-bit signed magnitude is ______, in ones complement is ______, in two’s complement is ______, and in excess-127 is ______.Expand to an unsimplified Boolean Function: F= B + A'BD + C'D' I NEED ASAP THANK YOU!Use de-morgans laws to write the equivlant expressions of each of the following and then write a program to show that both the original expression and the new expression in each case are equivlant. Write in C programming language a) !(x< 5) && !(y>=7) b) !(a==b) || !(g != 5) c) !((x<=8) && (y> 4)) d) !(( i > 4) || !(j<=6))
- Keep the Diagram neat. Thanks. Implement the following boolean function using a) 16:1 mux b) 8:1 mux c) 4:1 mux F(A,B,C,D) =∑(0,1,2,7,8,10,11,13, 15)A function rule takes an input n and converts it into an output y by increasing one half of the input by 10. Determine the output for this rule when the input is 50 and then write an equation for the rule.Write the triple, for the expression, - (a*b)+(c + d) - (a + b + c + d).

