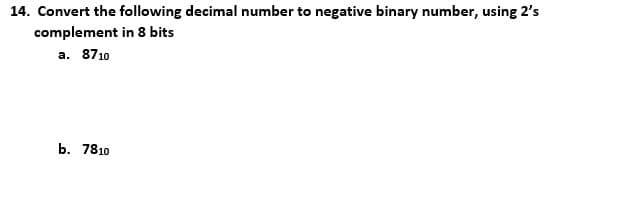
14. Convert the following decimal number to negative binary number, using 2's complement in 8 bits a. 8710 b. 7810
Q: Write an assembly language program (simply type it in the note pad and upload here) to calculate and...
A: Question 1. Write an assembly language program (simply type it in the note pad and upload here) to c...
Q: what is the output of the following codes : code 1. class A { { System.out.print(1)...
A: code1: //lets trace the code for outputclass A { { System.out.print(1);//this prints 1 ...
Q: What does the term "reduced" imply in the context of a computer with a restricted instruction set?
A: Answer: The notion of a smaller, more efficient set of instructions is known as the "reduced instruc...
Q: Write a program, in python, that checks if the last data item entered appears earlier in the list. O...
A: Answer: I have done code and also I have attached code and cod screenshot as well as output
Q: Write a Python program that counts the amount of identical values in a list below, and prints them.
A: def repeatedValue(x): repeated = [] for i in range(len(x)): k = i + 1 for j in range(k, len(x)): ...
Q: Which of the following is a legal identifier? a. 1st b. legal1 c. legalidentifier! d. Le...
A: Answer : b. legal1 Rules for legal identifier : 1. Don't start with number 2. does not contain sp...
Q: What is the difference between embedded computers and general-purpose computers?
A: Given: We have to discuss What are the fundamental differences between embedded and general-purpose ...
Q: Compare the advantage of doubly linked list over single linked list by giving a reason to perform th...
A: Advantages of doubly linked list over the single Linked list.
Q: You need to show detail work on how you get the answer. Dont use answers from other websites please...
A:
Q: Exercise 1: Write a program to calculate the volume and surface area of a sphere from its radius, gi...
A: For the given problem, we need to implement a program that calculates volume and surface area of a s...
Q: What faults in the Whetstone, Dhrystone, and Linpack benchmarks are addressed by the SPEC CPU benchm...
A: SPEC CPU benchmark addresses deficiencies in the Dhrystone, Whetstone, and Linpack benchmarks: Dhrys...
Q: What exactly is multifactor authentication and how does it work? What role does it play in password ...
A: The solution to the given problem is below.
Q: Implement the following codes a explain what happens in the out var = 3 print(var)
A: Here in this question we have two python code and we have asked to find the output of this code.
Q: A list of five common network topologies should be included. Which one do you think is the most trus...
A: check further steps for the answer :
Q: Create ERD of a hospital with these requirements "and then" write relation schema (underline primary...
A: We need to solve: Create ERD of a hospital with these requirements "and then" write relation schema ...
Q: What is the difference between embedded computers and general-purpose computers?
A: The answer is given below:-
Q: Question:- Decode the following bit patterns using the floating-point format discussed in the text: ...
A: Below is the answer to above three parts. I hope this will be helpful for you...
Q: Suppose we enhance a computer to make all multiplication instructions run four times faster. If the ...
A: Below is the answer. I hope this will meet your requirement.
Q: Q1: Explain the followings network requirement categories with suitable examples: Business requirem...
A: Dear Student, As per guidelines, I can answer only the first question with three subparts. Please re...
Q: Which kind of program-level parallelism (data or control) is best suited to SIMD? What kind of progr...
A: SIMD architectures are capable of exploiting significant parallelism not only for matrix-oriented sc...
Q: Perform Amortized Analysis for Queue (Multi-Insert & Multi-Delete) Disjoint Sets (Using Linked list ...
A: Actually, given question regarding Amortized Analysis forQueue (Multi-Insert & Multi-Delete)Disj...
Q: Network address: 220.100.100.0 Number of needed hosts: 45 Default subnet mask: New subnet mask: Numb...
A:
Q: Write a java program that creates a 4 x 5 two-dimensional array and fills it with the following numb...
A: Step 1 : Start Step 2 : Declare and Initialize the 4 x 5 Array with the given elements. Step 3 : Usi...
Q: You need to show detail work on how you get the answer. Dont use answers from other websites please...
A: Following is the RTN for the MARIE instruction Load X: The instruction retrieves datum X from memory...
Q: Create a list – l1 with element 1,2,3,4,5. Convert this list into an array name ar. What is the dime...
A: The solution is given below for the above given question:
Q: Write a program in the GO programming language that creates a CSV file to store and retrieve data su...
A: Using sort values() : Syntax: DataFrame.sort_values(by, axis=0, ascending=True, inplace=False, kind=...
Q: Question 4 (14): Consider the languages L= {a'b"a'xm |1, m> 0} and Lo = {a²'b™} |1, m> 0}. (Recall f...
A:
Q: an AWT Java program that simulate the PINCODE process. The system has a default PINCODE of 6 digit n...
A: Find the AWT code below.
Q: In terms of emphasis, what distinguishes the TPC from the SPEC?
A: The Standard Performance Evaluation Corporation (SPEC) is a non-profit organization dedicated to "pr...
Q: 2. a. What kind of hazard may exist in clock cycle 11 and why it may exist? b. Why there is no struc...
A: Below is the answer of the above question. I hope this will be helpful.
Q: implement a printAnimals() method that provides easy-to-read output displaying the details of object...
A: can suggest you to just run small parts of code separately not the entire code once
Q: Choosing RB-tree as the underlying data structure, define additional attributes to be stored in the ...
A: A red-black tree is a self-balancing binary search tree with one additional bit at each node, whic...
Q: Give a minimal state DFA that recognizes the language of strings which encode natural numbers in dec...
A: There are only three choices when dividing an integer by three. Either 0 or 1 can be used as the rem...
Q: Q3: Cool Chemicals In an alternate reality, chemistry Professors Hodge and Sibia have teamed up to d...
A: Coded using Python 3.
Q: Write a python program to get the specific line from a given File and that line number should be ent...
A: Introduction: Python provides inbuilt functions for creating, reading and writing files. There are...
Q: en an array A of si Give a linear time a ,using a O(1) addi ify why your algor
A: from collections import Counterdef printRepeat(ar, num): frequency = Counter(ar) for i in frequency:...
Q: What exactly is anti-forensics, and how does it function?
A: Introduction: Anti-forensic methods are content acts that are designed to hinder or harden good fore...
Q: Verify that the function is the general solution of the logistic ordinary differential equation. Use...
A: The general form of the logistic ordinary differential equation is as follows: dy/dx - r*y(1-y/k)=0,...
Q: V ( ץר) V ץר )ה
A:
Q: What are the two strongest justifications for layering protocols? Give examples to back up your clai...
A: One thing to note here is that layered protocols are almost present everywhere in the networking
Q: What scientific knowledge serves as a basis for the development of the internet. Explain also how in...
A: What scientific knowledge serves as a basis for the development of the internet. Explain also how in...
Q: How is multifactor authentication implemented? How does it help to prevent password theft?
A: An authentication factor is a type of credential that is used to verify an individual's identificati...
Q: Allows the use of cout without a prefix std:: a. pre-processor directive b. namespace std c....
A: b. namespace std
Q: Remove the unit production from the given CFG grammar. S → Aa |B B → A|bb A → a |bc |B
A: Process to remove Unit productions: if there is unit production A->B , then add new production ru...
Q: What are the benefits and drawbacks of caching disc write operations?
A: Benifits Caching disc write operations improves performance by allowing the operating system to av...
Q: SIX If the two values are identical, write the word "MATCH" otherwise, indicate whether the "TOP" or...
A: code to compare two numbers
Q: Write an appropriate array definition for each of the following problem situations: a. Define a one-...
A: The first will be an integer array and the next two will be character arrays The implementation of e...
Q: 15. Perform the following binary number Subtraction, using 2's complement : a. 011001, - 101110, b. ...
A: a. 0110012-1011102 Ans:- -0101012 b. 01110102-10011112 Ans:- -00101012
Q: Write an SQL query to report the movies with an odd-numbered ID and a description that is not "borin...
A: 1. To get moving we use where clause with condition and order by. 1. first we filter id by MOD inbu...
Q: For the grammar G with the productions: S -> a | c| S S s b Ciue
A: S -> aSb | x | SS The answer is an given below :
Step by step
Solved in 3 steps

- H- Assuming a three-bit exponent field and a four-bit significand, what decimal value is represented by the following bit pattern? 1 111 0000Which of the following does not use binary codes? a. Murray Code b. ASCII c. EBCDIC d. Morse CodeConvert IEEE Single-Precision Binary Format Real number 11000100101001000010101000000000 to decimal. Please show all the steps. a) [1] What is the sign? b) [1] What is the biased exponent value? c) [1] What is the unbiased exponent value? d) [2] What is the normalized representation of the number in BINARY? e) [1] What is the unnormalized representation of the number in BINARY? f) [1] What is the decimal value of the whole number part of the number? g) [2] What is the decimal value of the fractional part of the number? h) [1] What is the real number in base 10
- The binary number 1001 converts to the decimal number 9, with the 0th (zeroth) bit on the right representing 1 and the 3rd bit representing 8. If you're converting the decimal number 33 to binary, what is the highest numbered bit (counting from the 0th bit on the right) that will be set? a. 0th b. 1st c. 2nd d. 5th e. 6thD. What is the minimum number of binary bits needed to represent each of the following unsigned decimal integers?I) 65II) 409III) 16385Signed integers are represented by the following 16-bit hexadecimal numerals. Each should be converted to decimal.4CD2
- 2) What is the largest binary number that can be expressed with 16 bits? What are the equivalent decimal and hexadecimal numbers? 3) Convert the hexadecimal number 64CD to binary, and then convert it frombinary to octal.Q) Divide a 32-bit number by a 16-bit number and round the reminder for any value.To represent the decimal number 30 as an 8-bit binary number, you may use any of the following formats. One's a) Complement; b) Excess-M:?
- 2.What is the 16-bit hexadecimal representation of each of the following signed decimal integers? −21 −45 3.The following 16-bit hexadecimal numbers represent signed integers. Convert each to decimal. 6BF9 C123 4.The following 16-bit hexadecimal numbers represent signed integers. Convert each to decimal. 4CD2 8230 5.What is the decimal representation of each of the following signed binary numbers? 10110101 00101010 111100001) a.What is the decimal equivalent of the largest integer that can be represented with 12 binary bits. b.Convert the following decimal numbers to binary: 125, 610, 2003, 18944.(a) For the following two cases, please determine the radix r:(BEE)r = (2699)10(365)r = (194)10(b) Please add, subtract, and multiply in binary:100100 and 10110(c) Please add the following numbers in binary using 2’s complement to represent negative numbers.Use a word length of 6 bits (including sign) and indicate if an overflow occurs:(-11) + (-4) = ?11 + 9 = ?(-10) + (-6) = ?(d) Assume the following three cases are correct and assume three digits are used to represent positiveintegers. Determine the base of the numbers. Did any of the additions overflow?654 + 013 = 000024 + 043 + 013 + 033 = 223024 + 043 + 013 + 033 = 201

