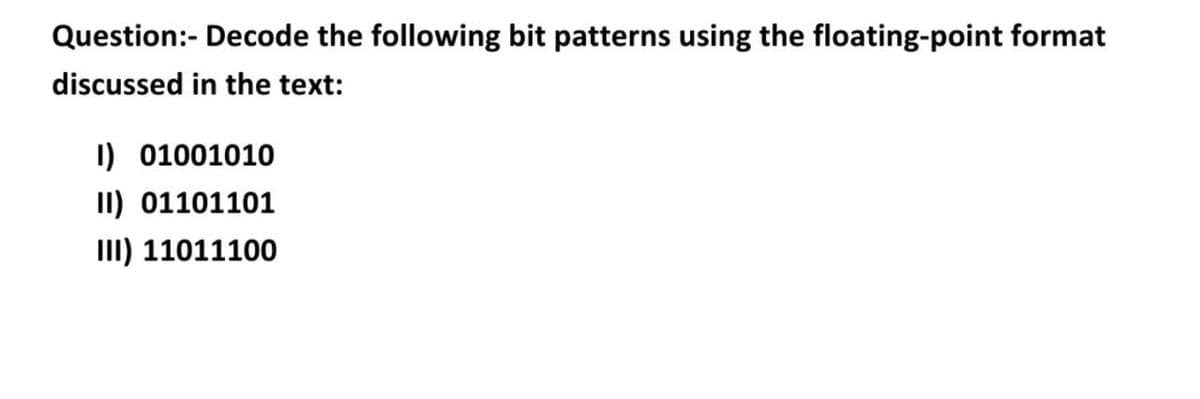
Question:- Decode the following bit patterns using the floating-point format discussed in the text: I) 01001010 II) 01101101 II) 11011100
Q: Use a diagram to describe the objective of software testing. Use this definition of software testing...
A: What is software Testing: Software Testing is a system to check whether the real software product ...
Q: what is the output of the following codes : code 1. class A { { System.out.print(1)...
A: code1: //lets trace the code for outputclass A { { System.out.print(1);//this prints 1 ...
Q: Examine the advantages and disadvantages of various system models.
A: 1 - Can collect the requirements when you want. 2 - Can improve your understanding when it will be w...
Q: What exactly is anti-forensics, and how does it function?
A: Introduction: Anti-forensic methods are content acts that are designed to hinder or harden good fore...
Q: Sex Name Address SSN PERSON BirthDate Salary MajorDept EMPLOYEE ALUMNUS STUDENT Degrees Degree Major...
A: A relational schema is a blueprint used in database design to represent the data to be entered into ...
Q: Question 2: Consider the following premises: 1. A - (B - A) is a Theorem of Propositional Calculus/L...
A: Given The answer is given below.
Q: What are the four key security flaws in purchasing and merchandising systems? Examine the causes and...
A: Introduction: Security breaches occur when an attacker or intruder gets unauthorized access to an or...
Q: The organization and connectivity of a computer's many components are referred to as its architectur...
A: According to the information given: We have to define the architecture that's component referred to...
Q: Do you have any recommendations for data flow recording methods?
A: According to the information given we have to recommend data flow recording method.
Q: When utilizing IPsec, how do you ensure that each workstation has its own private key pair?
A: A workstation is a computer developed specifically for technical or scientific purposes. They're usu...
Q: When was security the most important in the history of computing?
A: Computing: Computing is the process of completing a job using a computer or computer technology. The...
Q: a) i) Give an inductive formula for the sum of the first n odd numbers: 1+3 +5 + .. + 2n -1 Show you...
A: As per guidelines, Im supposed to answer the first question, so i request you repost the other quest...
Q: he Apriori algorithm only consider distinct items in a transaction. In practice, multiple occurrence...
A: The Apriori algorithm is a very well data mining technique that has been used to a wide range of pro...
Q: Determine the difference between a virtual machine and a virtual machine.
A: Introduction: Even though it is usually abbreviated as "VM," the term refers to the same thing as an...
Q: 1. The input integer, n Constraints The value is >= 1 Output The first line will contain a message p...
A: Algorithm: Include standard header file and namespace std. Create a main function Declare the vari...
Q: In a bridged network, two bus segments are interconnected via a bridge. There are two hosts attached...
A: Collisions domain names: This default gateway is really a software framework that is coupled by a sh...
Q: In a field where an expert system could help you, provide at least five rules for the knowledge base...
A: 1. Small amount of information can held in mind and used for execution of cognitive tasks. It though...
Q: Write an assembly program that prints Hello World five times and then prints Bye world. Hints: Use u...
A: Algorithm: Start. Initialize a loop. Print hello World for five times. End loop. Print bye world. ...
Q: Given a list in Python [1,2,3,4,5,6,7,8,9,10]. Write a Python program to create a new list that cont...
A: Given: A list in Python [1,2,3,4,5,6,7,8,9,10]. Requirement: Write a Python program to create a ne...
Q: Is there a fundamental distinction between declarative/functional and procedural/imperative programm...
A: Introduction : Programming Paradigms: Generally speaking, the word "paradigm" refers to a model or ...
Q: What exactly is auditability? Why is it such a crucial security concept? Explain.
A: Auditability is one of the major task carried in an organisation, whether it be IT organisation or t...
Q: What data types are generally available for SQL table columns? What are tables, rows, and columns? W...
A: Step 1) What data types are generally available for SQL table columns . Exact Numeric Data Type : Us...
Q: Determine the difference between a virtual machine and a virtual machine.
A: Your answer is here in detail of the difference between a virtual machine and a virtual server.
Q: Split the following string into a list by splitting on the space character: U "NOS is going virtual!...
A: The commented codes and outputs are below of all programs.
Q: Write a Java program to find the second highest number from an user entered array of integers.
A: Required:- Write a java program to find the second highest number from a user-entered array of integ...
Q: What is the value of a good reputation?
A: Introduction: Reputation: A person's subjective qualitative belief in a brand, person, organisation,...
Q: sacramento.py Use the sacramento.csv file to complete the following assignment. Create a file, sacra...
A: To answer this question of mismanagement, we have a tendency to use it, we have to draw a line to do...
Q: Batch-function normalization's What settings should we tweak for batch normalization? What is the be...
A: One of the most prevalent issues that data scientists face is avoiding over-fitting. Over fitting is...
Q: Multiprocessor systems allow users to access shared memory. These kinds of procedures aren't common ...
A: Introduction: A multiprocessing system with symmetric architecture. When using an SMP system, progra...
Q: Write what will be printed on the computer screen after execution This part of the program: Dim A(3,...
A: The machine has completed the startup process: This same BIOS chip instructs it to hunt for a partic...
Q: n oracle sql,Ask the user their name and how many times they want to output their name (using a for ...
A: in oracle sql,Ask the user their name and how many times they want to output their name (using a for...
Q: A common bus system which is capable of transferring 8 bits at time with number of registers are 4 a...
A: Given the information, The total number of registers is four. Each register has an 8-bit value. The ...
Q: process from the notes} to con
A: Given Use the !{process from the notes} to construct a NFA N_5 that recognizes the @lang L(N_1)*. U...
Q: hat command gets you a long list of all your files in your current directory, including their permis...
A: The ls command lists and displays detailed information about the file system's files and directories...
Q: From time to time Yetis who live high up in the Himalayan mountain ranges come down from the mountai...
A: Step 1 : Start Step 2 : Define a function isValidYeti() which takes the code as argument and return ...
Q: Write a assembly language program in 8086 to make a counter that counts up from 0 to 99 in BCD and d...
A: The algorithm is a term that refers to a set of instructions used to In Accumulator, convert an inte...
Q: Compare full mesh topology and dual-home implementation in Wide Area Network.
A: Compare full mesh topology and dual-home implementation in Wide Area Network.
Q: The finite state machine (FSM): a b. a A B C generates the regular language, L = {a"b™ | a 2 1 and m...
A: #include <iostream> #include <cassert> #include <string> using namespace std; ...
Q: Given the list of the following cloud service providers (CSPs): Savvis, AT&T. Compare the above CSP...
A: You'll need to hire a cloud service provider if your firm wants to use public cloud services (CSP). ...
Q: What does it mean to have a privilege?
A: Given To know about the it mean to have a privillege
Q: Isn't it true that different systems place disk folders at different track places on the disk for a ...
A: The answer is
Q: With A = {5, 9, 2, 13, 1, 7}, trace the algorithm showing your steps and counting them as you go. Ho...
A: Since you had asked multiple question's so only 1st 3 will be answered.
Q: 3+1011111111111
A: Note :- You have not mention language to calculate your query , So i am doing in C++ language.
Q: Use the following schema and query plan to answer the corresponding questions S(d,e,f,g) B(S) = 1000...
A: I'm providing the answer to above question. I hope this will be helpful for you.
Q: rupt-driven operating systems outperfo
A: given - Why do interrupt-driven operating systems outperform non-interrupted operating systems in te...
Q: Determine number of memory accesses in following code For i =1 to 15 A(i)=A(i+5)+5 Suggest one impro...
A: Given statement : A(i)=A(i+5)+5 i=1 to 15 We need to determine the number of memory accesses. Lets u...
Q: 1. MOH codes are a 5-digit combination of alpha and digit numeric and an alpha suffix Create a table...
A: Below i have answered:
Q: Is it possible to negate access control by taking particular steps?
A: Answer: I have given answered in the brief explanation
Q: Cloud computing creates at least two challenges in terms of business security
A: Answer: In today's world what is actually want in the business is that we have to secure all your co...
Q: A flattened Neural Network for handwritten digital classification takes in 43X43 pixel images. How m...
A: For a flattened neural network, Each neuron acts as a pixel. Here it is given that the pixel resolut...
Urgent
Step by step
Solved in 4 steps with 3 images

- Convert each of the following bit patterns into real numbers. Assume the values are stored using the floating point bit model. 11000001000101101011100001010010 =1. Using even parity, add parity bits to the following bit patterns: a. 0110 100 b. 1011 011 c. 0000 000 2. Using odd parity, add parity bits to the following bit patters: a. 0110 100 b. 1011 011 c. 0000 000Decode the following bit patterns using the floating-point format discussed in the text: 01001010 01101101 11011100
- What bit pattern is stored for the following characters assuming an 8-bit byte? a. A b. a c. 8 d. % 2. What character is represented by the following bit patterns? a. 0011 0000 b. 0100 0011 c. 0111 1000 d. 0010 1010Please find 1.25's corresponding bit pattern as stored in memory in hexadecimal! And show the steps because i dont know how to find hexadecimal with a floating point number.64. ________ is normally referred to as mB/nB coding; it replaces each m-bit group with an n-bit group. a. Block coding b. Line coding c. Scrambling d. None of the above
- Are you able to differentiate between the least significant bit and the most significant bit in a given set of data?How many check bits are needed if the Hamming error correction code is used to detect single bit error in a 128 –bit data word?2. Convert the following binary numbers to floating point format. Assume a binary format consisting of a sign bit (negative = 1), a base 2, 8-bit, excess-128 exponent, and 23 bits of mantissa, with the implied binary point to the right of the first bit of the mantissa.a. 110110.011011b. −1.1111001c. 0.1100×236d. 0.1100×2−36
- 98. Usually, it takes 10-bits to represent one character. How many characters can be transmitted at a speed of 1200 BPS? a. 12 b. 120 c. 1200 d. 12000Show Steps Please 8. Decode the following ASCII message, assuming 7-bit ASCII characters and no parity: 1001010 1001111 1001000 1001110 0100000 1000100 1001111 1000101Hi I need help with this data encoding problem, no computer coding is involved. 6. Add the two's complement (16 bit) values as indicated, writing your answer in the space provided. Indicate whether there was 'Overflow' or 'No overflow' and 'Truncation' or 'No truncation as appropriate. Remember, each answer must have exactly 16 bits. 0001 0100 1000 1101 + 0100 0010 0010 0111= ______ Did overflow occur? Y or N Did truncation occur? Y or N

