2) Create in PL/SQL a stored procedure called 'Del Details' to delete the record of orderedProduct table for which it receives as input the order number (orderNO) and the
2) Create in PL/SQL a stored procedure called 'Del Details' to delete the record of orderedProduct table for which it receives as input the order number (orderNO) and the
Chapter8: Sql Functions And Procedures
Section: Chapter Questions
Problem 6CAT
Related questions
Question
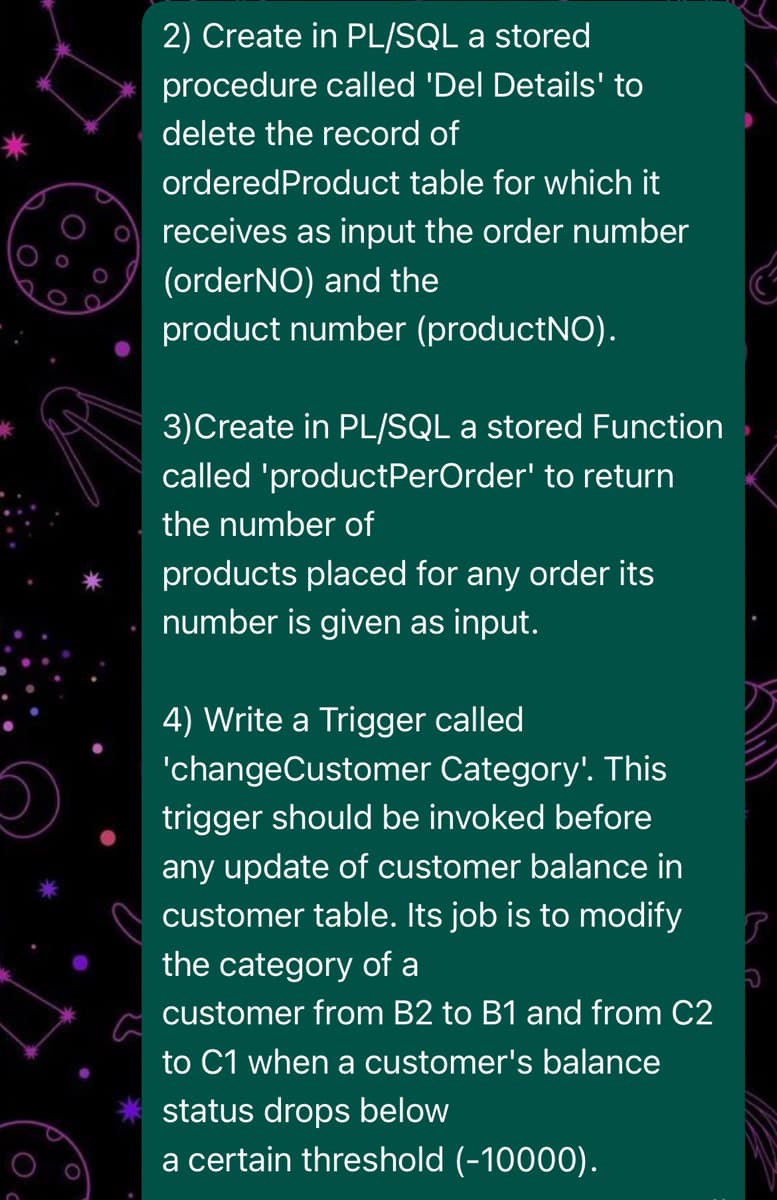
Transcribed Image Text:2) Create in PL/SQL a stored
procedure called 'Del Details' to
delete the record of
orderedProduct table for which it
receives as input the order number
(orderNO) and the
product number (productNO).
3)Create in PL/SQL a stored Function
called 'productPerOrder' to return
the number of
products placed for any order its
number is given as input.
4) Write a Trigger called
'changeCustomer Category'. This
trigger should be invoked before
any update of customer balance in
customer table. Its job is to modify
the category of a
customer from B2 to B1 and from C2
to C1 when a customer's balance
status drops below
a certain threshold (-10000).
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

A Guide to SQL
Computer Science
ISBN:
9781111527273
Author:
Philip J. Pratt
Publisher:
Course Technology Ptr


Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning

A Guide to SQL
Computer Science
ISBN:
9781111527273
Author:
Philip J. Pratt
Publisher:
Course Technology Ptr


Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning