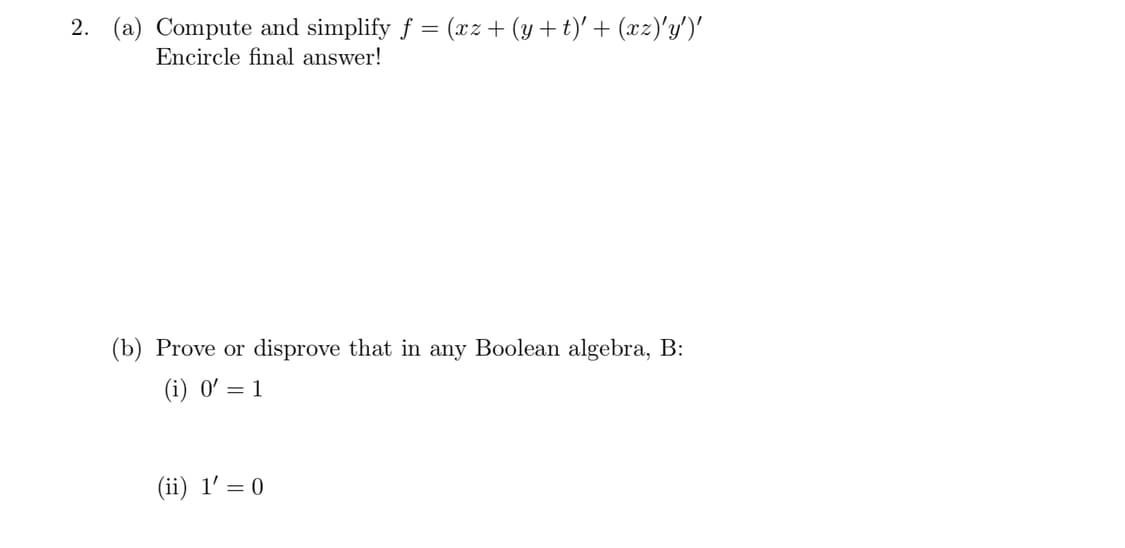
2. (a) Compute and simplify f = (xz+ (y+t)' + (xz)'y')' Encircle final answer! (b) Prove or disprove that in any Boolean algebra, B: (i) 0' = 1
Q: What separates a design from a user interface? How about you show me some samples of user interfaces…
A: A user interface (UI) is the means through which a user interacts with a device or software. It…
Q: 3. Consider the following C program, 1 2 3 4 5 6 7 8 9 10 11 int main() { 3; } int a = int *b; int…
A: The solution is given below for the above-given question:
Q: Examine the getBalance method's header and body, and then evaluate how they stack up against those…
A: Introduction: To examine the get Balance and get Price methods' headers and bodies respectively.
Q: In Java programming. Write the code to create an object of each type of class. The names of the…
A: Creating class objects is a typical activity in Java programming. The procedure entails establishing…
Q: In this brief article, we'll go over the basics of source data automation (SDA) and highlight two…
A: Source Data Automation: Source Data Automation (SDA) is a technique for acquiring digital values at…
Q: Provide a quick overview and explain whether or not adaptive initiatives outperform predictive ones.
A: Compared to the predictive model, the adaptive approach takes a lot longer to develop a usable…
Q: Declare a class named Phone which has manufacturer and model as its member variables. Also, include…
A: Below is a possible class declaration for the Phone class in Python:
Q: Write some code to generate an instance where variable x has both the static and dynamic types T and…
A: In the event that the variable x is assigned the static type T, the expression that defines That…
Q: I'm curious as to how "Race Condition" affects various operating systems
A: Answer is
Q: When you don't want to give someone what they want (when the computer doesn't reply to the user),…
A: Introduction: A Denial of Service attack disables a resource like a website, application, or…
Q: Analyzing enormous datasets, or "big data," may be a difficult task, but it can provide useful…
A: Big data analytics is the sometimes challenging process of poring through vast volumes of data to…
Q: Provide some background on what OneDrive is and how it compares to a conventional hard disk. Why is…
A: Answer is
Q: An IT manager will delegate maintenance responsibilities to a programmer or systems analyst who has…
A: INTRODUCTION: A person who uses various methods of analysis and design to address business…
Q: As comparison to Microsoft Excel, why is Access preferable for handling this kind of data?
A: MS Access and MS Excel: Microsoft's most powerful data analysis and reporting tools are Access and…
Q: What use do algorithmic computations serve?
A: Introduction :- Algorithmic computations serve a wide range of purposes, from solving mathematical…
Q: I wrote this code in JAVA but I don't want to change it from regex to use a loop. Not sure if I…
A: Here are two options for refactoring the code to not use regex, using both a for loop and an…
Q: Provide your thoughts about the evolution of computing from the first to the fifth generation in…
A: Throughout the previous several decades, technology has advanced: In five words or fewer, explain…
Q: Just what do we mean when we talk about "hardware" and "software"?
A: Hardware:- Every analogue or digital physical part of a computer is referred to as hardware. As…
Q: When a web client attempts to get access to protected resources hosted by a web server, it is…
A: Introduction: The question is asking for two persuasive arguments in favor of using layered…
Q: Explain why simulations of computers don't provide support for certain instruction sets.
A: According to the information given:- We have to define why simulations of computers don't provide…
Q: Please provide the two strongest arguments in favor of layered protocols.
A: First, let us know about the 'Layered protocols'. Then we will provide the strongest arguments.…
Q: Determine the differences between the three levels of data modeling.
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: Imagine a consumer who has never connected to the internet before. Explain the function of network…
A: According to the information given:- We have to define a consumer who has never connected to the…
Q: When conversing through email, what methods may be employed to improve clarity and comprehension?…
A: Answer When conversing via email, there are several methods that can be used to improve clarity and…
Q: Explain the process of data conversion and any changes that need to be made.
A: Data conversion is the process of transforming data from one format, structure or system to another.…
Q: how does an actual cache hierarchy look like?
A: We have to explain the actual cache hierachy. how the cache architechture look like.
Q: Think of a project and draw a plan for it, both with and without any architectural features. What…
A: Project: Building a Mobile Application for a Food Delivery Service Plan without architectural…
Q: Which is superior, threads at the user level or the kernel level? How are threads at the user level…
A: Introduction: Threads are the smallest units of execution within a program. They enable concurrent…
Q: Explain why it is beneficial to use cloud computing. Find out whether there are any risks associated…
A: In accordance with the question, we must outline the benefits of cloud computing. We must also…
Q: WAN stands for what?
A: A computer network is what? A set of computers, mainframes, network devices, servers, peripherals,…
Q: Mutual Exclusion (ME) is discussed at length as an essential feature for an OS to function properly.
A: Mutual Exclusion (ME) as an essential feature:
Q: This is a three-part question about critical path calculation. Consider a simple single-cycle…
A: Here is solution of Question 1 Part A.Please find in below steps.
Q: If you desire to swiftly access data in a centralized database, what design choices are made…
A: Introduction: It is common practice to classify databases as either Relational or Sequence…
Q: Provide an in-depth analysis of the following within the framework of an Information System. Illegal…
A: In this question we have to understand and dicuss on framework of an Information System. Illegal…
Q: Kocher’s timing attacks on cryptosystems illustrate this [1084]. Kocher notes that the instructions…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: Modify LiveExample 12.12 EvaluateExpression.cpp to add operators ^ for exponent and % for modulus.…
A: Algorithm: The algorithm works as follows: Create two stacks, one for operands and one for…
Q: A communication plan may outline the importance of a security awareness program and how it might aid…
A: Answer : Communication plan is basically a series of documents that need to outline , it helps to…
Q: Is it possible to infer, from the constructor arguments, the types of some of the Book class's…
A: What are the primary categories of the Book class? fields get their values from the arguments in the…
Q: Think up a project that involves software engineering, and explain how it might look.
A: For instance, you need have an architectural plan if you need to build a home. If you don't have an…
Q: Which ONE or MORE of the following, if any, ARE characteristics of Object-Oriented Programming?…
A: The solution is given below for the above given question:
Q: Utilizing free public Wi-Fi for business reasons is risky.
A: Risks Associated with Using Public Wi-Fi: A wireless connection is a method that allows electronic…
Q: The air interface between mobile devices, base stations, and towers is completely cable and…
A: Yes, cellular backhaul does require additional infrastructure to function properly. While the air…
Q: Which of the following is not an effective technique to create variety while using only one…
A: changing weight, size, letterspacing, and color - can be effective ways to create variety while…
Q: Let S = {3, 8, 12, 19}. Which of the following expression(s) is/are true? a. 12 ∈ S b. 3 + 8 ∈ S…
A: Solution The correct answer is a. 12∈S (True) The element 12 is present in the set S, so this…
Q: Is a network of computers even possible? How many different things make up the network and what are…
A: Is a network of computers even possible? How many different things make up the network and what are…
Q: Error correction works best in wireless contexts. To what extent do you agree or disagree with this…
A: Correction of errors: Error correction works best in wireless networks or applications and is seen…
Q: Convert to f string: print("{:4.1f}% {:^25}".format(course, avg_grade, " ".join("{:>4}%".format(y)…
A: In this question we have to convert f string Let's covert and hope this helps if you have any…
Q: For a distributed denial of service attack to be effective, the hacker must first download malware…
A: The answer to the following question:-
Q: We'll go through the drawbacks of a LAN in more detail down below.
A: Local Area Networks (LANs) are a term used in the field of computer science to refer to sets of…
Q: What will be printed out as a result of the following code? int x = 5, y = 7;…
A: Introduction : The question is a programming-related one that involves analyzing a code snippet…
Step by step
Solved in 3 steps

- Boolean Algebra Simplify the following functions to a minimum number of literals. Show step-by-step simplification and indicate the theorem/postulate used in each step. Draw the logic diagram of each of the simplified functions. (x’y’ + z)’ + z + xy + wz4. Simplify the following Boolean function F, together with the don’t-care conditions d, and then express the simplified function in sum-of-minterms form: a. F(x,y,z) = Σ(0,1,4,5,6) d(x,y,z) = Σ(2,3,7) b. F(A,B,C,D) = Σ(0,6,8,13,14) d(A,B,C,D) = Σ(2,4,10)solve problem D Given the Boolean function: F = xy' + z'y'z + xyz d) List the truth table or the functlon from the simplified expression and show that it is the same as the truth table in part (a).
- Simplify the following Boolean function F, together with don’t care conditions d and then express the simplified function in sum-of-minterms form. (a) F (x,y,z) = ∑ (0,1,4,5,6) d (x,y,z) = ∑ (,2,3,7)9. Show that De Morgan's Law applies to Boolean algebra, by showing that for all x and y, (x ⋁ y)’ =x’ ⋀ y’ dan (x ⋀ y)’ = x’ ⋁ y’Demonstrate the validity of the following identities by means of truth tables: The distributive law: x + yz = ( x + y ) ( x + z )
- Boolean Algebra Simplify the following functions to a minimum number of literals. Show step-by-step simplification and indicate the theorem/postulate used in each step. Draw the logic diagram of each of the simplified functions. (A’ + C)(A’ + C’)(A + B + C’D)Answer the given question with a proper explanation and step-by-step solution. Which of the following minterm expansion forms represents the Boolean function f(x,y):f(0,0)=0, f(0,1)=0,f(1,0)=1,f(1,1)=1 ?1. Simplify the following Boolean functions, using three-variable Kmaps: (a) F(x, y, z) = Σ(0, 1, 5, 7) (b) F(x, y, z) = Σ(1, 2, 3, 6, 7) (c) F(x, y, z) = Σ(2, 3, 4, 5)
- Simplify the following Boolean function F, together with the don’t-care conditions d, and then express the simplified function in sum-of-minterms form: F (x, y, z)=Σ(0, 1, 4, 5, 6) d(x, y, z)=Σ(2, 3, 7)6: Prove the identity of each of the following Boolean equations, usingalgebraic manipulation:(a) XY + XY + XY = X + Y(b) AB + BC + AB + BC = 1(c) Y + XZ + XY = X + Y + Z(d) XY + YZ + XZ + XY + YZ = XY + XZ + YZDemonstrate the validity of the following identities by means of truth tables: DeMorgan’s theorem for three variables: ( x + y + z ) ′ = x ′ y ′ z′ and ( xyz ) ′ = x ′ + y ′ + z ′

