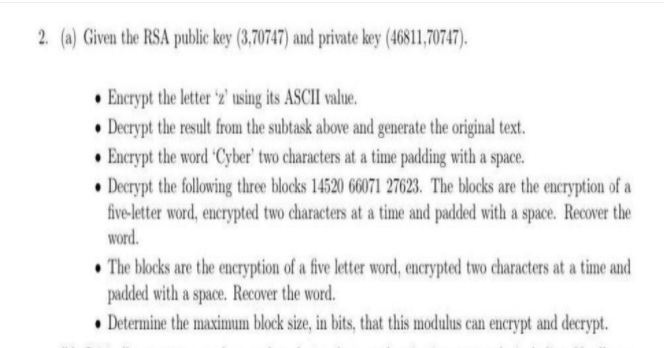
2. (a) Given the RSA public key (3,70747) and private key (46811,70747).
Chapter8: Data And Network Communication Technology
Section: Chapter Questions
Problem 41VE
Related questions
Question
dont dont dont answer if you are not 100% sure else strict compliant skip if dont know
Transcribed Image Text:2. (a) Given the RSA public key (3,70747) and private key (46811,70747).
• Encrypt the letter 'z2' using its ASCII value.
• Decrypt the result from the subtask above and generate the original text.
• Encrypt the word Cyber' two characters at a time padding with a space.
• Decrypt the following three blocks 14520 66071 27623. The blocks are the encryption of a
five-letter word, encrypted two characters at a time and padded with a space. Recover the
word.
• The blocks are the encryption of a five letter word, encrypted two characters at a time and
padded with a space. Recover the word.
• Determine the maximum block size, in bits, that this modulus can encrypt and decrypt.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning