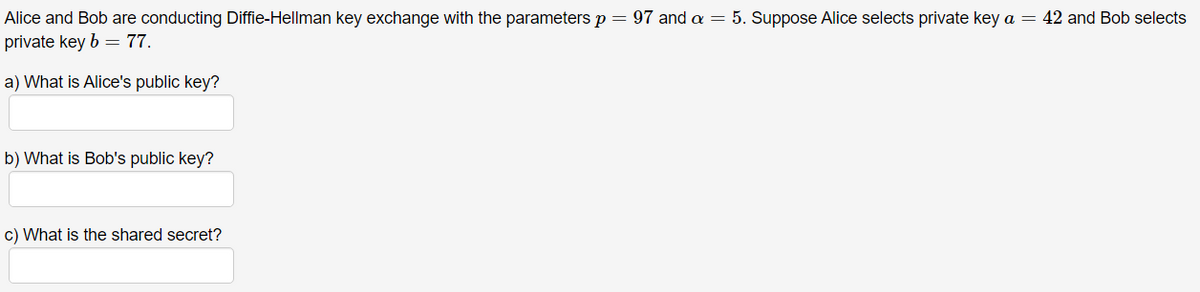
Alice and Bob are conducting Diffie-Hellman key exchange with the parameters p = 97 and a = 5. Suppose Alice selects private key a = 42 and Bob selects private key b = 77. a) What is Alice's public key? b) What is Bob's public key? c) What is the shared secret?
Q: number of cycles with at most 5 vertices: ________ Please list down the cycles. Will thumbs up if…
A: Here, we are given a undirected weighted graph and asked the number of cycles with at most 5…
Q: Discuss some fundamental differences between the process of constructing models and assembling a…
A: #include <sys/types.h>#include <sys/socket.h>#include <netinet/in.h>#include…
Q: Create a relational database that is at the very least in 3NF.
A: Relational database management system: A relational database organizes data into tables that may be…
Q: An authentication system that uses challenges and responses should be described in detail. What…
A: Given: Password-based authentication is used in client-server databases. It is not safe to send a…
Q: Would appreciate it if you could clarify the distinctions between the ARM and core i3 architectures.…
A: Given: The fundamental concept is simple software with sophisticated hardware. It indicates more…
Q: Step-by-step instructions on how to install and evaluate a computer system
A: State of planning or prerequisites: This is the stage in which the developer gathers all of the…
Q: What is the significance of RTOS in the Internet of Things?
A: RTOS is also known as real time operating system.
Q: What is Control Flow Graph?Calculate M.C. Cabe’s cyclometric complexity for the following code using…
A: McCabe cyclometric-complexity It is the software metric that is used to measure the complexity of…
Q: have a question about the following code, why do they have different output, please explain to me.
A: Given data: Program 1: class Test { private: int x; int y; public: Test(int x = 0, int y = 0)…
Q: A computer system's hardware and software are like two sides of the same coin. Discuss.
A: The computer system comprises two major components: computer hardware and software. Software for…
Q: How is software versioned? Explain the versioning information and protocols utilized in an online…
A: In fact, the information provided is versioned software systems. The following has been provided:…
Q: How many hosts can you have with a subnet of 192.168.1.0/25? O 14 27
A: The given address is 192.168.1.0/25
Q: ow would you answer this? Explain how the E-mail message exchanges from Sender and Re
A: Lets see the solution.
Q: What are the circumstances that lead to a system being stuck in a stalemate state?
A: The following circumstances imply a systemic deadlock: Circular Waiting Situation Condition of Hold…
Q: When participating in online meetings through Cisco WebEx or Citrix GoToMeeting, what new or…
A: MEETING LAYOUTS CAN BE CUSTOMIZED: Summary of the Meeting. On Linux, you may use the WebEx…
Q: Is it possible to break deadlocks and terminate processes in two separate ways?
A: It is possible to break deadlocks and terminate processes in two different ways described below.
Q: A primary key is always required in a database. Select one: O True O False
A: Primary Key: The primary key constraint uniquely identifies each record in a table. Primary keys…
Q: Describe what a challenge-response authentication system is and how it works. What makes it more…
A: Given: In the world of computer security, challenge-response authentication is a collection of…
Q: You should use the Exit method to close a sequential access file as soon as you finished using the…
A: The Exit statement transfers the control from a procedure or a block immediately to the statement…
Q: Is there a benefit to using Responsibility Driven Design? Explain with an appropriate example.
A: The following are some of the benefits of using Responsibility Driven Design: Responsibility-driven…
Q: Each phase of the conventional system development process should be explained in detail.
A: The traditional system development process is a structured approach to system development that…
Q: Define HTTP and explain how it differs between non-persistent and persistent HTTP.
A: HTTP stand for Hypertext Transfer Protocol.
Q: Create a function in Javascript that takes two numbers as arguments (num, length) and returns an…
A: JavaScript Code for above : // required function for abovefunction ReqdFunction(num, length) {…
Q: Explain the special purpose and general purpose register of 8051 microcontroller in detail. Analyze…
A: General Purpose Register of 8051 Microcontroller General purpose registers are the registers which…
Q: Sam is monitoring a banking system.He is required to define the bank statement by creating the…
A: Flow chart is a step by step process which consists of sequence of steps. In this flow chart, start…
Q: What are the types of testing techniques predominantly used ? Select one: a. Partition based,…
A: To find what are the types of testing techniques predominantly used.
Q: Because of the fast advancement of technology, the nature of cyberspace contact is changing swiftly.…
A: Given: The term "cyberspace" refers to a global network that links millions of digital devices. The…
Q: It is the layer that connects a VB program to a database file
A: Answer: Data Access Layer (DAL)
Q: Make it clear what a process is. Exactly what's the difference between a programme and a procedure?
A: High-level process definition: A high-level process map is a basic representation of a process' four…
Q: What was the "Analytical Engine" and how did it work?
A: answer is
Q: It is the standard computer language (by ANSI and ISO) that creates and manages relational…
A: SQL, structured query language, is the ISO/ANSI standard language for creating and maintaining…
Q: Why do we need the Seven-Layer OSI model? What will happen If we don’t have it
A: Introduction of Seven-Layer OSI Model: OPEN SYSTEM INTERCONNECTION MODEL it is a layered framework…
Q: Analyze certain items and provide suggestions based on your use experience. It's for an HCI Action…
A: Let's see the solution in the next steps
Q: In a VPN connection, which of the following devices are able to see the original destination IP…
A: Given: In a VPN connection, which of the following devices are able to see the original…
Q: What are the ramifications of a failure of an SDN controller system? Please provide an example of a…
A: SDN controller system: Multiple controllers are installed in a distributed SDN controller…
Q: It is necessary to provide an explanation of what a challenge–response system for authentication is…
A: Challenge Response Authentication Mechanism (CRAM): The most often used method of authenticating…
Q: 11. Given the following sample of the Web graph: a) Compute the transition matrix M.…
A: According to our guidelines we solve first three:…
Q: What is the designation of comments in PHP code?
A: Comments are typically written within a block of PHP code to explain how the code works. It will…
Q: I continued sorting and after the THIRD pass of the same algorithm, the list is [1, 2, 2, 5, 3, 4,…
A: The program is written in Java. Check the program screenshot for the correct indentation. Please…
Q: Explain the operation of a challenge–response authentication system. What makes it more secure than…
A: Definition: Password-based authentication is often used in client-server databases. The password…
Q: Q.1: MIPS is an architecture having its own Assembly Language. You are learning x86 assembly…
A: The answer is
Q: Show that p Aq=q^p.
A: Propositional Logic: It is a collection of declarative statements which has either a truth value…
Q: Describe the idea of a system model in your own words. What considerations should be made while…
A: Model of the System: Information flows between modules are represented as impacts or flows in the…
Q: Distinguish between a security standard and an information security policy. Explain why they're both…
A: The following table summarizes the distinctions between an information security policy and a…
Q: Distinguish between a security standard and an information security policy. Explain why they're both…
A: In comparison with information security standards security policies in current days are considered…
Q: Multiple Choice D] The question(s) that follow refer to the problem of finding the minimum spanning…
A: We are given a undirected weighted graph and asked the DFS and BFS traversal. DFS stands for Depth…
Q: Describe and explain in DETAILED the attacks on cryptosystems (reaction paper). Thank you.
A: A cryptosystem attack is a method of circumventing the security of cryptographic system by finding a…
Q: Is there a benefit to using Responsibility Driven Design? Explain with an appropriate example.
A: The following are some of the benefits of using Responsibility Driven Design: Responsibility-driven…
Q: What are the main advantages of Angular?
A: Angular is an open-source front-end framework maintained by Google.
Q: 3. Input four numbers and work out their sum, average and sum of the squares of the numbers.
A: Answer
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Alice and Bob use the Diffie-Hellman key exchange technique with a common prime q=41and a primitive root α=2 . a) If Alice has private key XA =3,what is Alice’s public key? b) If Bob has private key XB = 7 ,what is Bob’s public key? c) What is the shared secret key?Alice and Bob use the Diffie-Hellman key exchange technique with a common prime q=23 and a primitive root α=5. (a) If Bob has a public key YB=10, what is Bob’s private key XB? (b) If Alice has a public key YA=8, what is the shared secret key K with Bob?referring to Diffie Hellman, if the prime q is 353, alpha is 5, random secret key Xa is 110 and random secret key Xb is 92, then the public key would be:
- For the given scenario where Alice and Bob are trying to establish a shared secret key using Diffie-Hellman key exchange protocol, fill the values in the table.Question2 part 1. d. In Diffie-Hellman key exchange is based on the use of the prime number q = 353 and aprimitive root of 353, in this case α = 3. A and B select secret keys XA = 97 and XB = 233,respectively. Use this information to compute public key for both sender A and Receiver B.Once the public key is calculated then compute a common secrete key.You witness Alice and Bob agree on a secret key using the Diffie-Hellman key exchange. Alice andBob chose p = 97 and g = 5. Alice send Bob the number 3 and Bob sent Alice the number 7. Bruteforce crack their code: What is the secret key that Alice and Bob agreed upon? What were theirsecret keys?
- Let's say that Alice and Bob are exchanging keys using Diffie-Hellman key exchange using multiplicative group Z*499 and generator g=7. Let's say that Alice chooses secret exponent x=5 and receives the number 123 from Bob. What number should Alice send to Bob?_______ What number do Alice and Bob compute as their shared secret?________ Express each of your answers as an integer.Answer the given question with a proper explanation and step-by-step solution. Alice and Bob are using the Diffie Hellman key exchange to establish a secret key among them. Bob sends Alice [719, 3, 191]. Alice responds with, 543. If Bob's secret number, x, is 16. What is the secret key stablished?Let's say that Alice and Bob are exchanging keys using Diffie-Hellman key exchange using multiplicative group Z*401 and generator g=17. Let's say that Alice chooses secret exponent x=231 and receives the number 99 from Bob. What number should Alice send to Bob?____ What number do Alice and Bob compute as their shared secret?_____
- Pretend you are Alice and have agreed with Bob to carry out Diffie-Hellman key exchange with parameters p = 23 and g = 5. You may use a calculator to answer the following, but write down and label all the quantities you use. Assume you choose the secret random value x = 19. Compute the value gx (mod p) that you will send to Bob. In the protocol, you receive the value gy = 18 from Bob. Compute your shared secret value. Now pretend you are an eavesdropping adversary. From g, p and gy, find Bob’s secret y (it’s possible!) Describe how you found the value in part (c), and comment on how this reflects the security of Diffie-Hellman key exchange.Alice and Bob wish to perform the Diffie-Hellman key exchange. Let p = 1009 and g = 11. Suppose Alice chooses a = 268 for her secret value and Bob chooses b = 752. Explain the formulas needed for Alice and Bob to calculate a shared key. Use both formulas to calculate both Alice's and Bob’s values and show that they are the same. Note: you must show all calculations.Suppose you and your friend would like to use Diffie-Hellman key exchange system to exchange a keyword. Both of you have decided to use the following p = 4138327577, q = 3742197127.If you decide b = 1767005, and your friend has picked a number a that you don’t know. But you havereceived q a mod p from your friend, and the number is 980246808. Find out the common shared key.

