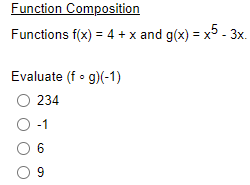
Function Composition Functions f(x) = 4 + x and g(x) = x5 - 3x. Evaluate (fog)(-1) O 234 O -1 06 09
Q: for a switching network. Calculate the total data times needed when the following switching…
A: The answer is
Q: Given the following below what is the fifth term? b₁ = 1, b2 = 3, and bn = bn-1 - 7bn-2, for n ≥ 3 O…
A: Introduction b1 = 1 ancd b2 = 3 Now we have to find the value for the fifth term . For the values…
Q: Discuss how to prevent data loss and computer crashes by doing regular maintenance and using…
A: Introduction: In the event of a crucial information failure, it creates a copy of the data that can…
Q: Write the pseudocode snippet to declare and populate the following array: Temperature 23 19 29 27…
A: Answer: I have provided the C++ pseudo code and running code with proper outputs: initialize an…
Q: Describe the three extensions that are commonly included in the various versions of EBNF ?
A: Dear Student, The required elaborate answer with example has been given below.
Q: Question 4 A grammar that generates a sentential form for which there are two or more distinct parse…
A: Below is the answer to above question. I hope this will be helpful for you...
Q: The first two bytes of a 2M x 16 main memory have the following hex values: 1. Byte 0 is FE 2. Byte…
A: ANSWER:
Q: Organize the components of SCI according to their importance in the Software development. Justify…
A: I have answered this question in step 2.
Q: In today's environment, what function does information security management play?
A: Introduction: In today's businesses, information security is seen as the domain of professionals who…
Q: Talk about how important system administration is to an organisation.
A: Introduction: The term "system administrator" refers to the person in charge of configuring and…
Q: Ques. Explain about Exhaustive Search.
A: The Answer is given below step.
Q: 3. Implement the OMOEA-II NSGA-II and SPEA2 using the DTLZ test functions and compare it with…
A: Implementation of OMOEA-II and comparasion of it with NSGA-II AND SPEA2 using DTLZ is explained in…
Q: function template
A: Introduction C++ programming language is a type of programming language that is been used for OOP…
Q: Pearson Charity: Donation Form Please complete the form. Mandatory fields are marked with a*…
A: Output
Q: What are the implications of a data breach for cloud security? What are some of the potential…
A: Introduction: The loss of client confidence is the most severe long-term effect of a data breach.…
Q: h tree B₁ by inserti into an empty binar nother binary searc umbers into an em
A:
Q: Question: Using the information above: Write instructions about how to print a document via a…
A: First, connect wireless printer to the laptop using the steps given below: Switch on the printer.…
Q: f I have two identical molecules, which I know the coordinates of these molecules, How Can I write a…
A: Steps to do so - StartInstate the factors.Play out the tasks.Print the result.Exit.
Q: using the SMART criteria as part of the Balanced scorecard methodology. how would i do that?
A: INTRODUCTION In a Balanced Scorecard, the executive's execution metric is utilized to distinguish…
Q: lect one: Oa. 4810 b. 7110 O c. 4210 O d. 7310 Oe. 3610 mich of the following equation is incorrect?…
A: 1. Option 'c'
Q: If I have two identical molecules, which I know the coordinates of these molecules, How Can I write…
A: Start Initialize the variables. Perform the operations. Print the output. Exit.
Q: What are the core principles of a wireless network?
A: The question is to write the core principles of a wireless network.
Q: How are disc blocks accessed if the Linux operating system doesn't keep a FAT?
A: Introduction: This is unquestionably supported by Linux. It is, along with the built-in partition…
Q: In a few words, explain how to keep a process from being starved during priority scheduling.
A: Introduction: High priority processes continue to execute while low priority processes are stalled…
Q: the use of enterprise data mashups
A: Enterprise data mashups The term enterprise mashup is frequently used to separate a business-related…
Q: How many bits would you need to represent 2018 in binary? How many bytes is that?
A: The above question is solved in step 2 :-
Q: Suggest 3 mitigation you may use as a symbol of acknowledging uniqueness
A: Mitigation is the reduction of harmful effects and also it includes the measures that are taken to…
Q: Design a sequential detector that detects the code 1011 using T flip flops and any other gates. Show…
A: answer starts from step 2
Q: As a result of technical improvements, the majority of appliances are now wirelessly enabled. Is it…
A: Introduction: There is a growing trend in the residential, commercial, and industrial sectors to…
Q: ive four reasons why many system designers believe data modelling is an important, if not the most…
A: Introduction: Data Modelling: Data Modelling is the process used to describe and organise the data…
Q: Based on Figure 4 below, identify in detail the process of: Temporal redundancy (inter-frame)…
A: Temporal Redundancy: Temporal Redundancy is one the technique in compression. It is used to in video…
Q: is affect developing nations. One reason may be the lack o . What are the advantages and…
A: Wireless network: Wireless networking is a strategy by which homes, telecommunications organizations…
Q: Why would someone use a line printer?
A: Introduction: Line printers utilize persistent structure paper which is generally punctured rather…
Q: All the methods as well as the main method/tester statements must be written in one class. DO NOT…
A: ANSWER:
Q: Write the equivalent assembly code if you were to translate from C to Assembly: for (i=0; i<10; i++)…
A: The given question instructs to convert the given c code to its equivalent assembly code: The given…
Q: Three processes P1, P2 and P3 with related information are given in the following table: Process…
A: In Preemptive the process whose run time is shortest is taken irrespective of the arrival time For…
Q: The high degree of computational redundancy provided by a Hadoop installation is one of its…
A: Introduction: The fact that Hadoop is a highly scalable storage technology that can store and…
Q: Why is a computer's cooling system important? What alternative cooling methods are there?
A: Solution: The waste heat produced by computer components is eliminated via computer cooling. By…
Q: Why is it important that accumulator variables are initialised correctly?
A: Introduction: Initializing the Accumulator Variable: In a programme, the running total value is kept…
Q: Complete the following exercise: Using your student table select all students that have a last name…
A: The name of the table is student Attributes of the student table are ID, FirstName, LastName ,…
Q: Discuss Bluetooth protocol stack with neat schematic.
A:
Q: Write the pseudocode for the following scenario: A manager at a 2nd hand car dealership wants to…
A: As Pseudocode is basically blueprint of Algorithm. It is not a complete code. It is usually steps…
Q: As Per the AWS Acceptable Use Policy, penetration testing of EC2 instances can happen or not?
A: Question is asking for penetration testing of AWS EC2 instances.
Q: You have been asked by Kimiko to design a guest registration form using html5. You have also been…
A: HTML is the hypertext markup languages used to create the web applications, Databases, to create the…
Q: 2. (P→ Q) ^ (¬R → S) PV¬R : ¬Q → S 1 2 3 4 5 6 STATEMENT (P → Q) ^ (¬R → S) R→ S QVS ¬Q → S REASON…
A: Answer: We have explain in more details also i have filled the table with suitable logic
Q: Write a program that generates a random number between 1 and 500 and asks the user to guess what the…
A: C++ Program: #include <iostream>#include<cstdlib> using namespace std; //Main…
Q: Which type of bus do you choose for your computer's central processor unit and memory, synchronous…
A: Intro Synchronous: A bus is a group of cables that connect one or more subsystems inside a device.…
Q: Describe the steps in the standard system development process.
A: Answer The Core Processes cover the entire spectrum, from agreement on a standard idea to drafting…
Q: Describe the TM that accepts the language, L = {w = {a,b,c}* | w contains equal number of a's, b's…
A: The language is generating six types of string and a, b, c can be in any order but contains equal…
Q: Explain how Transnet could respond to the above - mentioned risk by making use of the ' risk…
A: Please find the detailed answer in the following steps.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Write the following three functions in c programming language: a) The function gets an array A of length n of ints, and a boolean predicate pred. It returns the smallest index i such that pred(A[i])==true.If no such element is not found, the function returns -1.int find(int* A, int n, bool (*pred)(int)); b) The function gets an array A of length n of ints, and a function f. It applies f to each element of A.void map(int* A, int n, int (*f)(int)); c) The function gets an array A of length n of ints, and a function f. The function f gets 2 ints and works as follows: Start with accumulator = A[0] For i=1...length-1 compute accumulator=f(accumulator, A[i]) Return accumulator For example, if f computes the sum of the two inputs, then reduce() will compute the sum of the entire array.int reduce(int* A, int n, int (*f)(int,int));Define Constant Arrays as Formal Parameters.In C programing Write a recursive function that returns the product of the digits of its integer input parameter, n. You may assume that n is non-negative. For example, productDigits(243) should return 24, since 2 x 4 x 3 = 24.int productDigits (int n) {
- Computer science Write the definition of the function add, which takes two integer parameters and returns the sum of those numbers.Write a program in C language To input array of 10 elements from the user and implement following functions 1) Sort an array 2) Find out the mean 3) Find out the medianDefine a function in C++ language that takes an integer n as the parameter and then multiplies it by 8 without using the '*' operator or any loop. Return the value of n after multiplying it with 8.
- implement pass-by-value parameter passing method.USE C LANGUAGEPlease write Lisp code for the following problem. Write a function that computes the surface area of a cylinder. In other words use surface area = 2(pi xr2)+(2 xpi xr) xh, where r = radius and h = height. Test your function on at least: (r h) = (2 1); (r h) = (8 2); (r h) = (3 7).Programming Language: C Write the following three functions: a) The function gets an array A of length n of ints, and a boolean predicate pred. It returns the smallest index i such that pred(A[i])==true. If no such element is not found, the function returns -1. int find(int* A, int n, bool (*pred)(int)); b) The function gets an array A of length n of ints, and a function f. It applies f to each element of A. void map(int* A, int n, int (*f)(int)); c) The function gets an array A of length n of ints, and a function f. The function f gets 2 ints and works as follows: 1. Start with accumulator = A[0] 2. For i=1...length-1 compute accumulator=f(accumulator, A[i]) 3. Return accumulator For example, if f computes the sum of the two inputs, then reduce() will compute the sum of the entire array. int reduce(int* A, int n, int (*f)(int,int)); Test for the functions: // used for test Q3-find bool is_even(int x) { return x%2 == 0; } bool is_positive(int x) { return x>0; } void…
- in c++, excute Function y = 0.05*x3+6sin(3x)+4, Range From -2.5 to 2.5, step 0.5, Specified value ofy = -2, the image show the example of output, comment each line of code.Write a function below that will take a 2d array of booleans representing a map as a parameter which will construct a vgraph as a searchable graph. You many use go, python or java do to this.Implement a recursive C++ function which takes two integers num and den as arguments and returns theinteger quotient that will result when num is divided by den. The prototype of your function should be:int quotient (int num, int den)Hint: Think about repeated subtraction



