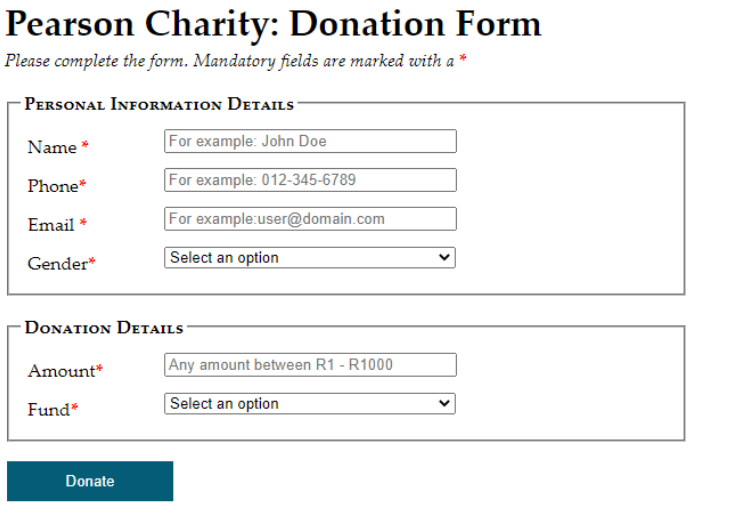
Pearson Charity: Donation Form Please complete the form. Mandatory fields are marked with a* PERSONAL INFORMATION DETAILS Name * Phone* Email * Gender* For example: John Doe For example: 012-345-6789 For example:user@domain.com Select an option
Q: DNS records, authoritative and root servers, iterated and unified queries, and everything in between…
A: Introduction: DNS is an overview of the Domain Name System:
Q: I keep getting invalid syntax for line 4 and I am not sure what I did wrong when running a test for…
A: The above program is solved using python programming language:
Q: In order for a CPU to comprehend and write instructions, what is the only programming language that…
A: Introduction An operating system is one of the product programs which fills in as a center layer…
Q: Design a sequential detector that detects the code 1011 using T flip flops and any other gates. Show…
A: ANSWER:-
Q: Enter a character to convert lowercase English letters to uppercase use switch-case Can't be use…
A: In order to convert a single lowercase character into uppercase there is no need to use the switch…
Q: Define what a Object Oriented Design is in Systems Analysis and Design.
A: Object-oriented analysis and design (OOAD) is a specialized methodology utilized in the…
Q: Explain the following terms and describe what they are used for: HTML, URL, XML, Java, JSP, XSL,…
A: HTML is a hypertext markup language designed for the formatting system for displaying material…
Q: Name four reasons why databases fail, and then offer a way (or methods) you'll utilise to prevent…
A: Introduction: The following are the four primary reasons why databases fail:
Q: Consider the crossing river problem,on one side of a river, there are an adult, two children, and a…
A: Crossing the River Eight adults and two children need to cross a river. A small boat is available…
Q: what is the ouput of the following code ? String valid="true"; if (valid)…
A: Java: For many years, one of the most used programming languages has been Java. Java is oriented…
Q: Please describe some of the differences between Linux and other operating systems in your own words.…
A: Intro Linux - Linux is introduced by Linus Torvalds in 1991. It is an open-source operating system…
Q: Design an application that declares an array of 10 StockTransactionobjects. Prompt the user for data…
A: Given : Design an application that declares an array of 10 StockTransactionobjects. Prompt the user…
Q: A petroleum cut has the following TBP Distillation data: Volume % distillate 0 10 30 50 70 90 95…
A:
Q: Convert this C code into MIPS Assembly Language #define WINNER_NONE 0 int check_winner(void) {…
A: Given Code: #define WINNER_NONE 0 int check_winner(void) { for (int row = 0; row <…
Q: Provide a Big Data Architecture for a business that offers its clients a flight information service.
A: Big data architecture is used to handle ingestion, analysis and processes of data which is too big…
Q: A Read Replica appears "stuck" after a Multi-AZ failover and is unable to obtain or apply updates…
A: Question wants solution for a problem in AWS AZ.
Q: Explain the cache memory in detail.
A:
Q: What did you discover or find interesting in your Network Fundamentals class? Is there anything you…
A: Introduction: A detailed review of fundamental network conceptsRouters, switches, firewalls, access…
Q: What is the layered approach to building an operating system? What are the benefits and drawbacks of…
A: Intro Layered: The layered approach is a method that refers to the process of breaking down an…
Q: Q.4.1 Differentiate between symmetric and asymmetric encryption using examples.
A: Encryption is the process of changing the form of any message to protect it from being read by…
Q: Computer Science Write a scalar function that converts kilograms to pounds and vice versa. Your…
A: Given Solution: function convert($value, $unit) { if($value >= 0) { if($unit == "kg") {…
Q: Please define the phrases "Trojan Horse," "Computer Virus," and "Worm." Which viruses rely the most…
A: A file or a code that delivered over the internet and infected the computers is called malware. It…
Q: Explain the five distinctions between Prim's and Kruskal's algorithms.
A: Intro Prims Algorithm would initiate to draw or build the minimum spanning tree from the given…
Q: Write a program that uses an array (of size 10) to demonstrate how to use the linear search…
A: Java: Java is a high level, class based, object oriented programming language. It was developed by…
Q: The post-implementation review is carried out by who? When ought to it be carried out? Would a…
A: Part(a) The full management system's installation phase essentially includes the…
Q: components of mot
A: Motherboard: A motherboard (also called mainboard, main circuit board,[1] mb, mboard, backplane…
Q: 2. Explain Simple classification Techniques ? (discuss all 4)
A: Simple Classification Techniques: In this section, we will discuss different classification…
Q: Explain the need for a System Development Process in Software Development Projects.
A: Introduction: A series of methodical procedures, activities, or phases are used to build and…
Q: Describe the security procedures used to control employee conduct and stop information from being…
A: Answer : dividing up the jobs of the workforce. On-demand disclosure of the information is ideal.…
Q: plain the cache memory
A: Introduction: Below describe the cache memory in detail.
Q: C++ Input an integer, output the absolute value of the integer。 use switch-case Can't be use…
A: #include< iostream > #include< cstdlib > using namespace std ; int main () { int number…
Q: If you want to launch Amazon Elastic Compute Cloud (EC2) instances and assign each instance a…
A: Question is querying for a problem related to aws ec2.
Q: Write a note on Computer virus
A: As of when a biological virus enters a body it hampers the normal working of a human body without…
Q: A = {[(¬P → Q) AR] V ¬Q} → (QAR)
A: Answer: Answer is given in step 2
Q: Explain following in IEEE 802.11 WLANs with timing diagram. i) DFWMAC-DC ii) DFWMAC-DCF with…
A:
Q: What are two well-known examples of software programmes used in the child care industry? Quicken and…
A: Intro Software applications designed to be utilized in child care unit are usually called child care…
Q: Question 8 The syntax analysis part of a compiler is a the compiler translates. In this role, the…
A: Syntaxes analysis or parsing is a second phase of a compiler. In this we can learn the basic…
Q: What are generics used for primarily? Why do generics in C++ and Ada have a wider purpose than they…
A: The principal purpose of generics is to parameterize entire classes meaning allowing the programmer…
Q: You have been provided with the following elements • Sheunesu • Katlego • Andries • Buhle • Avinash…
A: Inbuilt funtions/ method used, overview. // Adding an elements to LinkedHashSet // using add()…
Q: You are an information Systems consultant and have an entrepreneurial client who needs assistance in…
A: “Since you have posted a question with multiple sub-parts, we will solve first three subparts for…
Q: ax2 + bx + c = z (in programming format)
A: Note: The programming language is not mentioned in the question so the python programming language…
Q: rite a Java program to take the marks of students from roll numbers 0 to 4 and store them in an…
A: Introduction: Below the java program to take the marks of students from roll numbers 0 to 4 and…
Q: Given the Boolean function: F1(X, Y, W, Z) = (0,1,2,4,5,6,8,9,12,13,) 1. Construct the truth table.…
A: 1. Truth table X Y W Z Output 0 0 0 0 1 0 0 0 1 1 0 0 1 0 1 0 0 1 1 0 0 1 0 0 1 0 1…
Q: WEEK 3 ASSIGNMENT Complete the following exercise: Using the student table you created in week…
A: Note: Due to company policies I am compelled to solve only the first three sub parts of the…
Q: Computer science: What are the three points that should be briefly discussed in the project…
A: Project management plan:- The project management plan is made up of a collection of all project data…
Q: What is information security governance, and what are the five parameters for achieving successful…
A: Information security governance is a system by which we can control and direct the organization's…
Q: In order for a CPU to comprehend and write instructions, what is the only programming language that…
A: A computer understands only machine language. Machine language uses only binary digits for…
Q: How would you use SQL to change the layout of a table? What kinds of changes are generally possible?…
A: Introduction: Tables, which are database objects, are used as containers for the data in the…
Q: Determine the time complexity function of the program snippet below, int f1(int n) { if (n = 1)…
A: These re recursive functions and we have to find their time complexity by recurrence relation. We…
Q: Write the equivalent assembly code if you were to translate from C to Assembly: for (i=0; i<10; i++)…
A: Given C language code is: for(i=0;i<10;i++) sum +=i; This code adds the numbers from 0 to 9…
Step by step
Solved in 2 steps with 1 images

- Which depicts a has-a relationship? classStudent{stringname;intage;intgrade;};classTeacher{stringname;intexperience;stringforGrades;};classSchool{vector<Teacher>teachers;}; Group of answer choices: Student-Grade Teacher-Student School-Teacher School-StudentCreate two enumerations that hold colors and car modeltypes. You will use them as field types in a Car class and write ademonstration program that shows how the enumerations are used.Fix the errors in the Customer class and the Program. DATA FILE ThinkAbout Tech 344 Park Ave, NY, NY 10022 Kemp Technologies 3601 Broadway, NY, NY 10021 Verizon 6 Hudson Street, NY, NY 10001 Merrill Lynch 7 World Financial Center, NY, NY 10001 Philips Laboratories 345 Scarborough Rd, Briarcliff Manor, NY 10510 CODE #include <iostream> #include <fstream>#include <string>using namespace std; class Customer { // Constructorvoid Customer(string name, string address) : cust_name(name), cust_address(address){acct_number = this.getNextAcctNumber();} // Accessor to get the account numberconst int getAcctNumber() { return acct_number; } // Accessor to get the customer namestring getCustName(} const { return cust_name; } // Accessor to get the customer addressstring getCustAddress() const { return cust_address; } // Set a customer name and addressstatic void set(string name, string address); // Set a customer addressvoid setAddress(string cust_address) { cust_address =…
- How do I use the member selection arrow operator -> to show how you can set the lastLogin time of *userPtr to 16 hours, 43 minutes, and 39 seconds? Below is my code #include <iostream> using namespace std; ; struct Time { int hours; int minutes; int seconds; }; struct User { string username; string password; int userID; Time lastLogin; } newUser; User* userPtr = &newUser int main () { return 0; }The dealership sells different types of vehicles: cars and trucks. All vehicles have a make, model, and year. However, a truck has an additional attribute - maximum load capacity (in pounds). Create a class named Vehicle with the following attributes: make, model, and year. Include the following methods: display_info(): This method should print all these details in a formatted string. get_age(): This method should calculate and return the age of the vehicle based on the current year. Tip: You will need to import functionality from the datetime module to do this. Create a class named Truck that inherits from the Vehicle class. This class should have an additional attribute, max_load, which represents the maximum load capacity of the truck. Include the following methods: display_info(): This method should override the method from Vehicle, and when it's called, it should display the truck's make, model, year, and maximum load capacity. can_carry(weight): This method should take a…Use this code template to continue the code: public Item(String name, double weight, int value) Initializes the Item’s =ields to the values that are passed in; the included =ield is initialized to false public Item(Item other) Initializes this item’s fields to the be the same as the other item’s public double getWeight() public int getValue() public boolean isIncluded() Getter for the item’s fields (you don’t need a getter for the name) Given code: public class Item { private final String name; private final double weight; private final int value; private boolean included; public Item(String name, double weight, int value) { this.name = name; this.weight = weight; this.value = value; } public Item(Item item){ name = item.name; weight = item.weight; value = item.value; } public void…
- 3.Rose Theater Company For this assignment you will modify the Rose Theater Company assignment created in chapter 2. Rose Theater company sells tickets to their productions. There are three seating options for purchase at Rose's theater; Orchestra seats, Center Stage seats, and Outer Stage seats. Orchestra seats cost $75 each, Center Stage seats cost $50 each, and Outer Stage seats cost $25 each. The theater company also gives a discount of 5% on tickets to the local theater group members. The user will enter the number of Orchestra, Center State, and/or Outer stage seats the customer wants to purchase along with whether the customer is a member of the local theater group. The program will calculate and display the income from each type of seat sale along with the discount, and total sale. Requirements Must include use of named constants Must include meaningful variable names Must include a main function with a call to the main function. Must include at least one value returning…The above screen is used to browse the products table it uses the ProductDAO.java file, it calls the getProductByCriteria() function which should accept a parameter, this parameter should be the criteria that would be built from the two combo boxes and the text box, and queries the products table.The getProductByCriteria() function should return a list of Product objects that matches the criteria specified. Modify the function so that it accepts a string paramater consisting of the fields from the combo boxes and a price number from the text box separated by commas and use this string to modify the query in the function to return the desired result set. public List<Product> getProductByCriteria() //MAKE MODIFICATIONS TO THIS FUNCTION SO IT CAN TAKE PARAMETER(S) { if (openConnection()) { try{ List<Product> items = new ArrayList <> (); Product temp = null; String…visual basic, make a code that display a savings account balance for each of 5 years using rates from 3% to 7% in increments of 1%. Private Sub btnCalc_Click(sender As Object, e As EventArgs) Handles btnCalc.Click Dim dblDeposit As DoubleDim dblBalance As Double Double.TryParse(txtDeposit.Text, dblDeposit) txtBalance.Text = "Rate" & ControlChars.Tab &"Year" & ControlChars.Tab & "Balance" &ControlChars.NewLine End Sub
- Help me correct my C++ code please! Pictures included. My current code with the error picture; #include <iostream> using namespace std; class Employee{ public: string first_name; string last_name; int monthly_sal; Employee() { first_name=""; last_name=""; monthly_sal=0; } void setFirst_Name(string first_name) { this->first_name=first_name; } void setLast_Name(string last_name) { this->last_name=last_name; } void setSal(int monthly_sal) { if(monthly_sal<0) this->monthly_sal=0; this->monthly_sal=monthly_sal; } string getFirst_Name() { return first_name; } string getLast_Name() { return last_name; } int get_salary() { return monthly_sal; } int get_yearly_salary() { return 12*monthly_sal; }}; int main(){ Employee ob; string first_name,last_name; int monthly_sal;…The Inventory class contains a Private variable named strId. The variable is associated with the Public ItemId property. An application instantiates an Inventory object and assigns it to a variable named onHand. Which of the following can be used by the application to assign the string "XG45 to the strId variable? a. onHand.ItemId = "XG45" b. ItemId.strId = "XG45" c. onHand.strId = "XG45" d. ItemId.strId = "XG45"Each of the following files in the Chapter.08 folder of your downloadable student files has syntax and/or logical errors. In each case, determine the problem, and fix the program. After you correct the errors, save each file using the same filename preceded with Fixed. For example, DebugEight1.cs will become FixedDebugEight1.cs. a. DebugEight1.cs b. DebugEight2.cs c. DebugEight3.cs d. DebugEight4.cs







