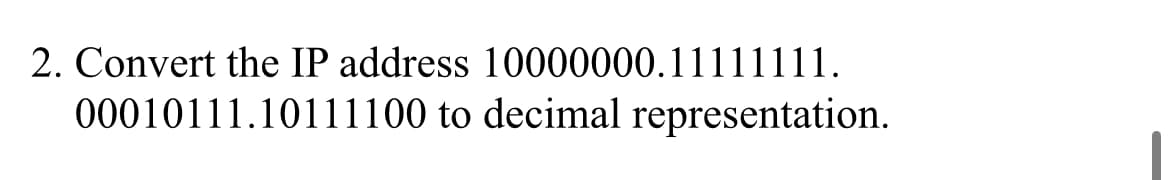
2. Convert the IP address 10000000.11111111. 00010111.10111100 to decimal representation.
Q: Describe the five factors that ACLs employ to allow or deny traffic on a router.
A: Introduction: ACL is a collection of rules for managing network traffic and reducing network…
Q: Connected with 512 neurons ---> Fully Connected with 512 neurons -- ---> Fully Connected w
A: The answer is
Q: Only for issues relating to information technology security will the proposed remedy be developed.
A: overview of IT security concerns: It is described as a collection of cyber security methods that…
Q: What is padding and when padding occurs?
A: What is padding : The CSS padding properties are utilized to produce space around a component's…
Q: It is essential to have a solid understanding of which aspects of the Compiler Phases are the most…
A: Compiler operates in various phases and in each phase it will transform the source program from one…
Q: Some systems analysts find it better to start with a decision table, and then construct a decision…
A: The Answer is in step2
Q: What are some of the benefits that come along with utilising the Collection Framework that Java…
A: The following are some of the benefits of using the Java Collections Framework: It Reduces the…
Q: True or False: To verify the fiber closure requirements, a 10 to 20-foot water head test shall be…
A: The correct answer is given below with explanation
Q: What should you bear in mind while migrating from one system to the next? Why don't you go into…
A: Introduction: A single organisational component change has no impact on hierarchical execution.
Q: Could you please explain what the word "security service" means?
A: Answer the above question are as follows
Q: It is possible for malicious traffic to be rerouted from one VLAN to another, which would then…
A: Answer: 1. Strengthen Access Control as a Preventive Measure The control of access is a crucial…
Q: Describe the components that make up the CSMA protocol.
A: CSMA: CSMA is an acronym that stands for Carrier Sense Multiple Access. Stations may detect what…
Q: What are some of the potential hazards that may develop during a server database transfer project?
A: Introduction: Data migration is the act of moving data from one system to another utilising a number…
Q: What are some of the telltale symptoms that the operating system of a laptop has been compromised,…
A: Start: Hacking is defined as getting unauthorised access to any account or computer system in order…
Q: Show the steps for performing the followings: a) Search 75 b) Insert 100 c) d) Delete 5 min and max…
A: We have a Binary Tree given. We need to write steps to perform the following operations on the tree-…
Q: Recognize and describe the five primary areas or fields that are concerned with internet governance,…
A: 1. (10) Digital realpolitik: from values to interestsRealpolitik dominated digital policy since the…
Q: Write a Java program that prints out the sum of 1 + 2 + .. + 10 reversely (using a for loop) and…
A: In the given program we have to calculate the sum from 1 to 10 in reverse order using for loop and…
Q: Relate the partial-products method and array you drew for the previous exercise to the steps in the…
A: When you use the array (table, box) approach to the partial products multiplication, you prepare a…
Q: Identify and describe five different domains or disciplines that are connected to internet…
A: Beginning: One of the most common definitions of Internet Governance is the improvement and…
Q: Given a class named Person with a private String field named name and a private integer field named…
A: part 1. function definition syntax acess_modifier data_type functionName(data type…
Q: in1 in2 out 1 1 0 1 2 1 2 1 1 2 2 0 2. Can you perform the task above using a radial basis function…
A: Note: Answering the question as no programming language is mentioned. Task : Define the data. Train…
Q: Please provide an illustration of the differences between the client-server architecture and the…
A:
Q: 67. The router's rou ng entries: <address Interfa 28.11.0 4 28. 26.0 1
A:
Q: ince health and fitness motion sensors are now more inexpensive, what research avenues do they open…
A: Introduction: Today, the majority of individuals are focusing on and devoting more time to health…
Q: It's possible that data breaches have an effect on cloud security, but how significant will that…
A: Data breach on the cloud: A data breach is the deliberate or inadvertent disclosure of…
Q: Do you believe Bill Gates personal drive contributed to Microsoft becoming a leader in the software…
A: According to the information given:- We have to describe Bill Gates personal drive contributed to…
Q: What would be the long-term repercussions of a data breach that occurred on the cloud? What are some…
A: Justification: Database corruption, leaking of confidential information, intellectual property…
Q: Where can I get information on the primary advantages, fundamental models, and possible…
A: Start: The practises of storing and accessing data and computer resources through the Internet is…
Q: Discussion is had on the numerous different models, advantages, and downsides of keeping data in the…
A: Cloud computing: Cloud computing provides on-demand, pay-as-you-go IT services through the Internet.…
Q: # NAMA :Idham Azis Muhaimin # NIM :19/446688/TK/49793 # Kelas C T = [2, 6, 8, 7, 9] P = [1,…
A: The flowchart for the code is given below with code output
Q: What is done to the fiber optic cable before it is inserted into a connector? O the fiber is…
A: Answer:
Q: Rerouting malicious data from one virtual local area network (VLAN) to another might be one method…
A: Given that malicious data might be rerouted from one VLAN to another as part of a network intrusion,…
Q: Define a Recursive Function that will display the reverse of the num data are provided]. Write a…
A: Please find the answer below :
Q: What are the most often encountered computer security threats?
A: INTRODUCTION: A computer system threat is anything that causes data loss or corruption, as well as…
Q: What are the top six reasons why someone should educate oneself about compilers?
A: A compiler changes over a program's sort or the language in which it is composed to another. Certain…
Q: Explain your thoughts on the software structure review process using examples.
A: Introduction: Software Review is a systematic evaluation of the programme carried out by one or more…
Q: What are the benefits of operating systems that are not dependent on a certain hardware platform?
A: Answer: OpenSyncTM is an open-source piece of software that communicates and manages your evolving…
Q: Assume you are travel vlogger, therefore, you are facing an issue to find shortest path to visit all…
A:
Q: What contingency plans are in place to deal with the possibility that the project's scope may need…
A: Introduction: To address shifting demands, use a new approach and work in Agile-style two-week…
Q: What is the most significant difference between mainframe operating systems and operating systems…
A: Introduction: The following are the key distinctions between two categories of operating systems:
Q: What is the definition of data analytics? And, in terms of application and methodologies, how does…
A: Introduction: Data analytics is a term that describes the process of drawing conclusions about the…
Q: A GUI program has the following design: ENTER COUNT: Single COUNT 1: TIME: COUNT 2: TIME: COUNT 3:…
A: The program has three components: a java.awt.Label "Counter";a non-editable java.awt.TextField to…
Q: A. Using algebraic manipulation to prove: A(A+B)(AB+C)(A BC + D)= ABCD B. Transform to only using…
A:
Q: The operating system of a computer may be used to create, inspect, and manage files and directories…
A: Inspection: The file system is the component of the operating system that manages files and…
Q: What is a finite state machine, and why is it significant?
A: What is meant by the term "finite state machine"? A finite state machine is a specific kind of…
Q: Assume you are travel vlogger, therefore, you are facing an issue to find shortest path to visit all…
A: Genetic Algorithms (GA) use principles of natural evolution.There are five important features of GA:…
Q: Create a C++ program of movie booking system. Must have a menu for movies, available seats, total…
A: C++ code of booking system : #include <iostream> #include <stdio.h> #include…
Q: Choose the correct answer : Execute the instruction: BSA X: X is memory location, need : a) 5 steps…
A: Instruction BSA X D) 5 steps and 3 Micro-operations
Q: The distinction between oops and functional programming
A: Introduction: Object-oriented programming uses objects to address things (now and again true…
Q: What are some of the most major advantages of keeping data on the cloud, as well as some of the most…
A: The following are some of the benefits of storing data in the cloud: When you save the data on the…
Step by step
Solved in 3 steps with 3 images

- ) find the binary equivalent for an IP address such as: 192.68.10.40Answer the following: a) Rewrite the given IPv4 address using dotted-decimal notation and find the class. 01011110 10110000 01110101 00010101 b) Rewrite the given IPv4 address in binary representation and find the class.q27- Given IP address 150.15.131.64 and subnet mask of 255.255.255.224; which of the following statements describes this address? Select one: A. This is a network address. B. This is not a valid address C. This is a usable host address. D. This is a broadcast address.
- Rewrite the following IP addresses using binary notation: 135.11.5.95 14.70.16.64 192.24.44.35 Rewrite the following IP addresses using dotted-decimal notation: 01011110 00110001 01100101 10010100 10001011 10001111 11010100 10110011 01010111 00100100 00111111 00101111 3. 17.0.0.0 is the first address. What is the 200th address? What will be the 258th address?Are the following two IP addresses in the same subnet? Answer either 'yes' or 'no'. 2001:69a0:75:60c9:6a10::1/64 2001:69A0:7500:60C9:632e:d456:3c95:72c2/64Question 9 Convert the following IPv4 address into dot decimal address, and determine which type of these addresses are. a) 10000001 00001011 00001011 11101111 b) 11000001 10000011 00011011 11111111 c) 11100111 11011011 10001011 01101111 Computer network Full explain this question
- q22- An IP address of 132.192.191.250 with a mask of 255.255.255.248 what is the broadcast address of the subnet in which the IP address is belong to? Select one: A. 132.192.191.255 B. 132.192.191.249 C. 132.192.191.251 D. 132.192.191.248 E. 132.192.191.252Write the following IPv6 address in its smallest or most abbreviated format: AD89:00C0:0204:0000:0000:ABC0:000B:0000Identify the classes of the following IP addresses by placing an A, B, C, D, or E next to the IP address: ____ 18.125.189.76 ____ 195.12.98.100 ____ 135.208.47.159 ____ 250.54.22.101
- A bit string, 0111101111101111110, needs to be transmitted at the data link layer. What is the string actually transmitted after bit stuffng? Write a computer code to do this job.Addresses starting with fe80 are called link-local IPv6 addresses. True or falseWhat can the following full IPv6 Address be formatted to when you remove the leading zeros? fe80:0000:0000:A510:0000:0000:0000:C912





