2. Make an R command to make a sales chart on 5 clothing brands "V", "W", "X", "Y", "Z" which sell 40, 30, 50, 65, 85 pcs each week. 08 09 40 2 W Bar chart
2. Make an R command to make a sales chart on 5 clothing brands "V", "W", "X", "Y", "Z" which sell 40, 30, 50, 65, 85 pcs each week. 08 09 40 2 W Bar chart
Chapter5: Data Manipulation And Transaction Control
Section: Chapter Questions
Problem 8HOA: Execute a command that undoes the change in Step 7.
Related questions
Question
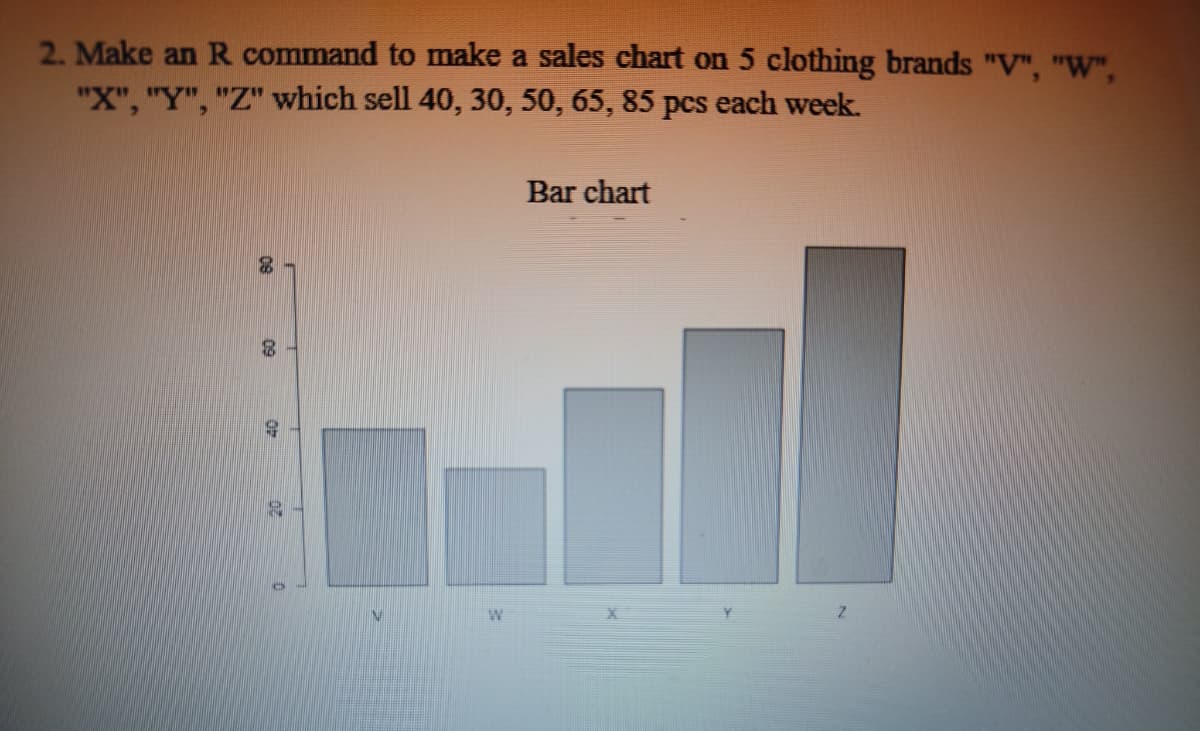
Transcribed Image Text:2. Make an R command to make a sales chart on 5 clothing brands "V", "W",
"X", "Y", "Z" which sell 40, 30, 50, 65, 85 pcs each week.
80
09
9
35
W
Bar chart
7
Z
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you


Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage


Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage