2. Most ARM processors support both Big Endian and Little Endian. ARM processor is Little Endian by default. Endian big little First byte (lowest address) most significant least significant Memory Address 0x8000 0x8001 0x8002 0x8003 0x8004 Middle bytes *** Memory Data OXEE 0x8C 0x90 OxA7 OxFF By default setting, the word stored at address 0x8000 is: Last byte (highest address) least significant most significant
2. Most ARM processors support both Big Endian and Little Endian. ARM processor is Little Endian by default. Endian big little First byte (lowest address) most significant least significant Memory Address 0x8000 0x8001 0x8002 0x8003 0x8004 Middle bytes *** Memory Data OXEE 0x8C 0x90 OxA7 OxFF By default setting, the word stored at address 0x8000 is: Last byte (highest address) least significant most significant
Principles of Information Systems (MindTap Course List)
13th Edition
ISBN:9781305971776
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter3: Hardware And Mobile Devices
Section: Chapter Questions
Problem 6SAT: LI is the fastest type of cache memory built into a computer, faster even than DDR4 SDRAM memory....
Related questions
Topic Video
Question
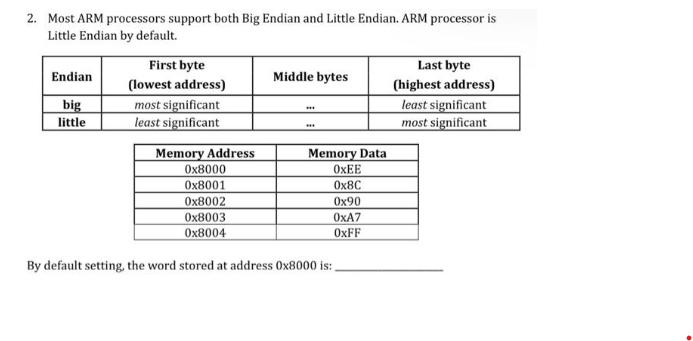
Transcribed Image Text:2. Most ARM processors support both Big Endian and Little Endian. ARM processor is
Little Endian by default.
Endian
big
little
First byte
(lowest address)
most significant
least significant
Memory Address
0x8000
0x8001
0x8002
0x8003
0x8004
Middle bytes
***
Memory Data
OXEE
0x8C
0x90
OxA7
OxFF
By default setting, the word stored at address 0x8000 is:.
Last byte
(highest address)
least significant
most significant
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning