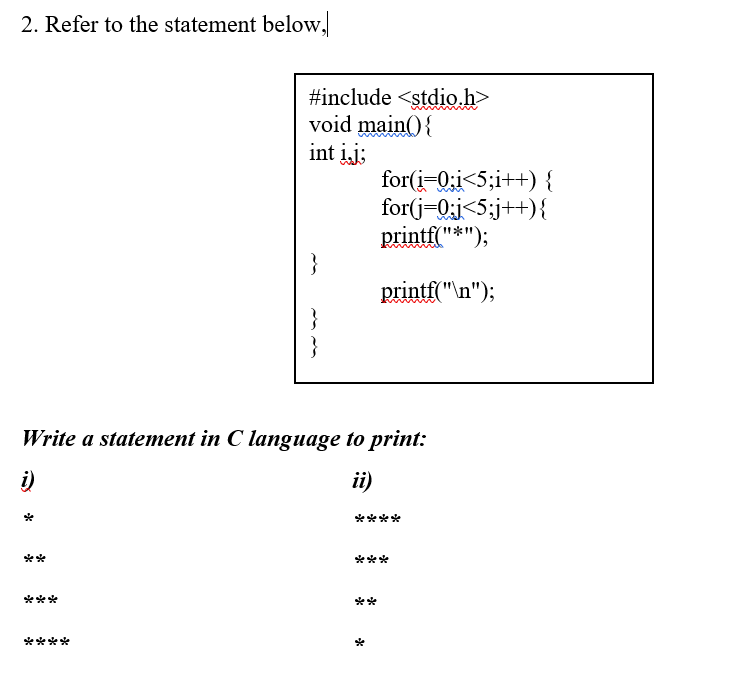
2. Refer to the statement below, #include void main(){ int ij: for(i-0;i<5;i++) { for(j-0;j<5;j++){ printf("*"); printf("\n"); Write a statement in C language to print: i) ii) *** *** ** ****
Q: Given the following binary number in 32-bit (single precision) IEEE-754 format, the decimal value cl...
A:
Q: Computer science What is it about the transistor that makes it so much better than a vacuum tube?
A: Introduction: A vacuum tube is a glass tube with its gas removed, resulting in a vacuum. Vacuum tube...
Q: 7. TestScores Class Write a class named TestScores. The class constructor should accept an array of ...
A: // Custom exception class InvalidTestScores extends Exception { public InvalidTestScores (Str...
Q: Briefly show if it is true or false and explain. A,B, and C are sets. If A ∈ B and B ∈ C, then is i...
A: Belongs to symbol: Belongs to symbol refer to an element must be in the set.
Q: What is the procedure for storing
A: Single-precision floating point values with float type have 4 bytes, comprising of a sign bit, a 8-...
Q: In the calculation of the maximum available valid host addresses in each subnet, the total addresses...
A: Here in this multi part question we have asked that while calculating valid host address ,2 host add...
Q: Complete the following sentence. The function takes in a string as input and returns the characters ...
A: below is the function used to convert input string to numeric codes
Q: Explain how the TCP/IP and OSI models are utilised in the communication process to enable standardis...
A: The TCP/IP model and OSI model are used to facilitate standardization in the communication process -
Q: What languages are included in the oops concept?
A: Question. What languages are included in the oops concept?
Q: What is the most essential part of transitioning from serial to batch processing on a computer?
A: Introduction: The most important aspect of the transition from serial to batch processing systems. T...
Q: What is information validation in the Microsoft Access application, and how does it work?
A: Data validation is a method for checking the accuracy and quality of data. In Microsoft Access, the ...
Q: What Is Macro in Computer Science?
A: Introduction: A macro is an automated task or a recorder of instructions that are executed repeatedl...
Q: What are the canonical and standard forms of Boolean function? Give example for each.
A:
Q: What is a digital security risk, and what causes it? Explain in a few words two digital security iss...
A: Given To know about the digital security risk and two digital security issues
Q: Write a swap function, that swaps the values of two variables in main, but use pointers instead of r...
A: Please refer to the following steps for the complete solution to the problem above.
Q: undamental functionalities of a network operatin
A: Network operating system:- The networking role of the Network Operating System (NGO) is to allow fil...
Q: pick a provider model example and explain the benefits and drawbacks of that particular model.
A: IaaS(Infrastructure as a service) IaaS is a sort of distributed computing administration that offer...
Q: How do I get the total of bal of top4(
A: Get the list Then sort the list in reverse order Extract first 4 elements and store its sum
Q: PLEASE HELP TO CONVERT THIS FOR LOOP TO FOREACH LOOP
A: foreach is used to iterate over an iterable like an array or list to get each element one at a time ...
Q: What are the distinctions between the Mobile First and Desktop First approaches to responsive web de...
A: Introduction: It is tough to determine whether to develop a responsive web design on the desktop fir...
Q: What phrase is widely used to refer to elements displayed in a program's graphical user interface, s...
A: Answer: - The term commonly used to refer to objects like TextBoxes, Labels, and Buttons that are vi...
Q: Q1 Direct proof is a method of mathematical proof. Name at least two other methods of proof: Us...
A: Direct proof example and to other method in below step
Q: Suggestions for security procedures that you can consider implementing in order to protect against d...
A: Introduction: It's a set of processes designed to keep sensitive and protected information from the ...
Q: Logic and Reasoning Implications and Equivalence Give two examples of remarks from your daily life t...
A: Introduction The question is: Give two example statements of implications encountered in everyday ...
Q: Discuss software maintenance techniques with examples
A: let's see the solution
Q: Separate the phrases "validation" and "verification." Examples should be provided.
A: Intro Verification: Verification is the process of checking that a software program achieves its ai...
Q: What are the fundamental roles of a network operating system?
A: Network Operating System is one of the significant sorts of working frameworks. Network Operating Sy...
Q: have a 70000x785 dataset (70000 instances and 785 features) consisting of 10 different types of clas...
A: Here as given,10 different classes , in which we have 7000 instances and 785 features. =============...
Q: Write a user-defined MATLAB function that converts speed given in units of miles per hour to speed i...
A: The solution for the above-given question is given below:
Q: Is there a distinction between mobile devices and laptop computers? Give an example to back up your ...
A: Introduction: The most obvious distinction between a mobile phone and a personal computer is their s...
Q: Can you tell the difference between data definition commands, data manipulation commands, and data c...
A: We are going to understand DDL(data definition commands),DML(data manipulation commands) and DCL(dat...
Q: Could you perhaps describe the most prevalent types of OS intruders in a few words?
A: Answer :
Q: following algorithm Algorithm ABC2(X,p,m) if (1==m) then print(X[1:m]) else { for i = p to m do { te...
A: Here in this question we have given a code segment and we have asked to find the time complexity of ...
Q: the number of available addresses on a network by the Supernetting hosts ID. 16 Choose one a. Decrea...
A: Supernetting is a process of combining small networks into big networks. It is also called as aggreg...
Q: define and explain network administration and network maintenance and no plagiarism of definition an...
A: Answer :
Q: Write a program that allows the user to navigate the lines of text in a file. The program should pro...
A: Here I have taken the filename as input from the user and then opened the corresponding file in read...
Q: Explanation and examples: 1)The primary SRAM 2)first-generation DRAM
A: Intro RAM It is a component of the computer's Main Memory, which the CPU can access directly. Rand...
Q: What will happen if you use JOptionPane.showMessageDialog statement in your program? Select one: O a...
A: Answer: Answer-1: The correct option is (e): The program will display a message dialog box Explanati...
Q: What is the length of the array: int[] intArray = { 1, 2, 3, 5, 6, 7 }; Select one: О а. 4 O b. 7 O ...
A: Given To know about the 1) length of array :: int array[]={1,2,3,5,6,7} 2) value of x after execute...
Q: Write a program called asyncFileCount.js that prints the number of files with a given extension in a...
A: Introduction
Q: 6. Modify the previous program to find every prime number less than or equal to n.
A: Python Program: from math import sqrt def prime(n): divisor = 2 found = False max_diviso...
Q: Describe briefly the contents of the following Linux files, displaying the first five lines of each:...
A: intro What is Linux: Linux is the most well-known and widely used open-source operating system is L...
Q: Subject : Data Structure Language : C Topic : Hash Table Sub Topic : - Pop - Push - Search Case ...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: Hardware description language Lab Creating appropriate Eight-Line Multiplexer source code using Data...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: Show if the statements are true or false and provide a brief explaination as to why. If A ∈ B and B...
A: Show if the statements are true or false and provide a brief explaination as to why. If A ∈ B and B ...
Q: For the input line:29 88.7 CSC103 What will be in the variables after executing the following C++ co...
A: Given code is int t1; double t2,t3; string ts; cin >> t2>> t1>> ts; Given that o...
Q: Computer science What is the most effective approach to use the IT simulation viewer?
A: Introduction: IT simulation viewers are programs that allow you to view and run simulations created ...
Q: When it comes to computer abuse, what are the computer etiquette guidelines?
A: Computer etiquette is the appropriate method for conveying while at the same time interacting with i...
Q: Examine the differences between the two schools of thinking when it comes to defining "information t...
A: Introduction: An information system is an integrated set of components for collecting, storing, and...
Q: How does a computer save the following information? picture, audio, video, and word document?
A: All of this is stored on computers in digital format, which is understandable by machine alone in co...
Step by step
Solved in 2 steps with 2 images

- T/F 1. Java interprets a negative value as false and a non-zero value as real, much like the other C family languages (C, C++, C#).T/F 2. In Java, only if and if-else expressions are used in selection statements.C++ Please! Also please don't use functions, arrays, or classes. Just basic c++ please. Password Verifier Write a C++ program to verify that a user’s password meets the following criteria: 1. The password should be at least 6 characters long. 2. The password should contain at least one uppercase and one lowercase letter. 3. The password should have at least one digit. Your program should ask the user for a password and verify that it meets the following criteria. If it doesn’t a message should be displayed telling the user why.
- Write a c++ program to display a calendar for a given year. Type of Branches such as switch statements, if-else, and etc. should be used as well. You can't define functions or use Void. Everything should be written inside int main(). Code should be written in this type of format: #include <iostream>using namespace std; int main() { /* Type your code here. */ return 0;} Ask a user to enter the year and the new year's day of the year entered: cout <<"Enter a calendar year to display?"; cout <<" what is the new year's day?"; a leap year is: IF year%4 = 0 AND year%100 != 0 OR year%400 = 0 An example of what the program should display as a result is in the two images attached.Using C#, write a program that takes a decimal value between 1 and 10 and displays its equivalent Roman numeral value. Display an error message ifthe value entered is outside of the acceptable range. Write a two classsolution. The second class should allow the user to input a test value.In java Develop a function that takes two integers and returns the sum of the values from the first to the second (the two inputs may be in any order). Call the function at least twice with different arguments Develop a void function PrintLineOfChar that accepts a single character and an integer. The function prints a single line of the character repeated the integer number of times. Call the function at least twice with different arguments.
- please do this in program in c++ and follow these simple guidelines 1. Please read the directions clearly, so your using the same data values 2. Avoid using any strings/manipulators/ advanced external libraries 3. Please dont forget to firstly ask user to input their 3 intials in the start of the program.. ** Previous responses have been incorrect for failing to include some of these things, please do not waste your time and mine, by sending me repeat solutions that are incorrect. ThanksIn C++ Find the five errors. For each error, state the line number, explain the error and show a correction. #include<iostream> #include<iomanip> using namespace std; class colorCode { public: void setRGB(int); //accepts an int parameter and sets the RGB to the value of the parameter void setName(string);//accepts a string parameter and sets the name of the object to the value of the parameter string getName() const;//returns the name of the object int getRGB() const;//returns the RGB of the object void changeColor();// adds 10 to the RGB value private: string name; int RGB; } int main() { colorCode paintCans[10]; int i; for (i = 0; i < 10; i++){ paintCans.setRGB[i] = 0;} paintCans[5].setName(GREEN); paintCan[5].setRGB(192000); cout << paintCans[5].getName << ' ' << paintCans[5].getRGB() << endl; return 0; }Question 10 Write a program in Java that finds the Least common multiple of 2 numbers,please include comments and fully explain what the code does because I am not really understanding what loops are doing ! (I need a manual way to calculate the lcm and not use a function(method) or "findlcm"..!
- USE C++ programming language 1) State whether the following declarations are valid or invalid. Give reasons for the invalid declarations and draw memory layout for the valid declarations i)int var, *ptr;ptr = &var; ii)float fvar;int *ptr = &fvar;User Defined Function: Void Function Create a JAVA program that will add, subtract, multiply and divide two numbers. Use user defined function for each operator Any number divided by zero will result to undefined Use int or double data type only for all variables declaredEXPECTED OUTPUT:Please circle True or False for each of the following statements. C++ You can create multiple instances of any class in C++. TRUE FALSE





