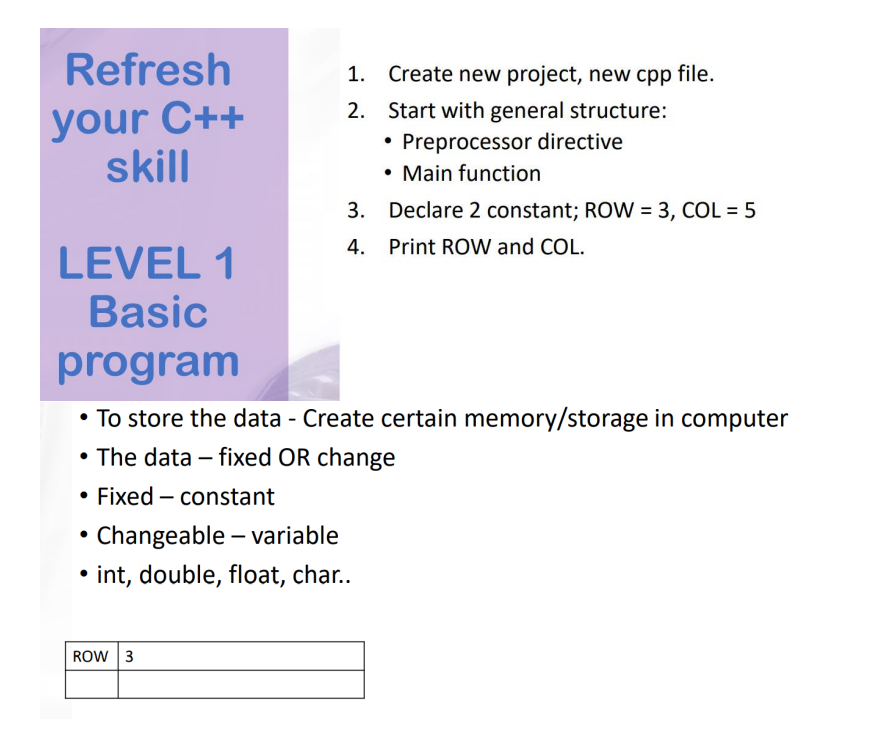
2. Start with general structure: Preprocessor directive • Main function 3. Declare 2 constant; ROW = 3, COL = 5 4. Print ROW and COL.
Q: In a few words, describe the XMM registers.
A: 1) The XMM registers are part of the Streaming SIMD(single instruction multiple data) Extension(SSE)...
Q: 1.Shów thất 200 € O(1) and 200 2. Show that 2n+5 € O(n²) 3. Show that 3 log n + log (log n) 0(log n)...
A: Time complexity: Estimation of cpu computation required to terminate algorithm.
Q: Prove that gcd(a + b, a – b) = gcd(2a, a – b) = gcd(a + b, 2b). Show your work! Justify each step.
A: Given that, Prove gcd(a+b, a-b) = gcd(2a, a-b) = gcd(a+b, 2b) Suppose d divides a+b and a-b.Then d d...
Q: using
A: given - are the two most compelling reasons for using layered protocols? Provide examples to back u...
Q: The user enters information of a student (ID, first, and last name). The user has the option to dele...
A: # code to delete a particular # data from a file # open file in read mode with open("sampl...
Q: List 3: Denial-of-service (DoS) attacks Distributed DDoS attacks Reflection attacks
A: As per company guidelines we are suppose to answer only first 3 subparts of the question. Kindly re-...
Q: 3. Convert the following sign/magnitude binary number to decimal: 101001 (2) answer choices: a) 9...
A: Given: 3. Convert the following sign/magnitude binary number to decimal: 101001 (2) answer choices: ...
Q: Types of network that the university should implement
A: Computer Network is the set of computers which shares the resources between the computer systems or ...
Q: Identify the major protocols at each TCP/IP layer and explain how they function.
A: Intro TCP/IP: TCP/Ip are two different communication protocols. TCP splits a message into packets th...
Q: Assume you want to keep track of changes to the takes relation. Can the above approach ensure that m...
A: Introduction: The basic principle of an audit trail is the supervision ( or tracking) of the usage a...
Q: public class MyClass { public static void main (String args []) { int x = 1; System.out.println(x) ;...
A: here I written given code with fully understand language with comments that how all value will assig...
Q: Explain why an application developer could choose to execute a programme via UDP rather than TCP.
A: Introduction: TCP is, in fact, a connection-oriented programming language. UDP is a programming lang...
Q: Which of the following are true regarding signal processing in C. The list of supported signal...
A: SIGKILL and SIGSTOP are two signals that cannot be captured and handled.
Q: Explain why many system developers and business leaders feel data modelling is the most critical asp...
A: Introduction: In general, each industry and area has a given quantity of data. They may contain a va...
Q: What is the memory space and computer time overhead associated with the execution of a recursive fun...
A: Introduction the question is about What is the memory space and computer time overhead associated wi...
Q: What is the connection between data and information?
A: Data: It is an assortment of values. Those values can be characters, numbers, or some other type. ...
Q: Design and write a truth table using the Karnoff map What is the name of the resulting circle?
A: Karnaugh Map: By using K-Map we can minimize the Boolean expressions of 3, 4 variables very easily w...
Q: Below C-code has a for loop which will repeat 1000 times of the operation. This code will be running...
A: The above question is about the iteration through for loop ........here , for each value of i until ...
Q: nation: First 2 digits: Year 4th and 5th digit: Department 01 = CSE, 41=CS, 21=EEE, Any other digits...
A: Code: IDs = ['20201199','21121347','19101052','19301121','20221369','21241199','19241187','20141007'...
Q: 4. Consider the following languages. ANFAFIN = {{N) | N is an NFA and L(N) is finite} EREX = {(R) | ...
A: Below is the answer to above question. I hope this will be helpful for you
Q: As a systems analyst, explain the aspects you must examine while building system architecture.
A: Introduction: Integrity and Consistency: When creating a dependable and fault-tolerant architecture,...
Q: What is the function of dex compiler in android? a. It converts class files to dex files. O b. It co...
A: Let us see the answer below,
Q: Computer 1 (C1), with a clock rate of 3 GHz, runs a program in 40 seconds. Computer 2 (C2), with a c...
A: Please refer below for your reference:
Q: Write a Python program to show the binary values of all the entries in the list below in string form...
A: #method to convert decimal to binary #and returns in string formatdef dectobin(d): if d>0: ...
Q: Modify tic-tac-toe: the 1st player x wins if she gets 3-in-a-row, otherwise the 2nd player o wins. W...
A: I have answer this question in step 2.
Q: "warni
A: given - How does canary work? What is the "warning" it will give you and when it will give you such ...
Q: Use an example to explain how business can better utilize disruptive and sustaining technologies for...
A: -innovation and technology plays vital role in modern bussiness and the working world. -the modern e...
Q: Internet service providers (routers, switches, DNS servers, web servers, end users, and so on) frequ...
A: Introduction: It is vital that various Internet entities communicate with one another.
Q: What are the different types of virtual servers and services?
A: Introduction: the question is about different types of virtual servers and services? and here is the...
Q: The drivers in android are developed in а. С++ O b. Java O c. Linux
A: b. Java
Q: 1. Consider this very simple function: def cube(x): answer = x * x return answer (a) What does this ...
A: answer is
Q: How does multifactor authentication work? What role does it play in preventing password theft?
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful. Tha...
Q: Year 0 Year 1 Year 2 Year 3 Bలe $0 $100 $200 $300 PV of Benefit $0 (1) (2) (3) NPV of all $0 (4) (5)...
A: Answer is given below-
Q: = (a*y)*x*
A: Given as, x+y*=x*y*x*
Q: Do execution paths 3 and 4 encompass the first three conditions for a deadlock to occur?
A: Introduction Do execution paths 3 and 4 encompass the first three conditions for a deadlock to occur...
Q: 49. An application uses a two-dimensional array defined as follows: int days[29] [5]; Write code tha...
A: The code here declares an 2D array which has 29 rows and 5 columns . The sum of the rows of the matr...
Q: Given a zero-terminated sequence of non-zero integers in order from smallest to largest, output the ...
A: Explanation: #first create a list in python. List = [-10 ,-4,-2,1,5,6,8,9,0] #Then create a variable...
Q: Explain how the DHCP server works to allocate IP addresses to hosts. Make a list of its procedures.
A: Intro Explain how the DHCP server works to allocate IP addresses to hosts. Make a list of its proced...
Q: What is the Final Verdict on File Integrity Monitoring Program?
A: Introduction: File Integrity Monitoring (FIM) aids in the protection and upkeep of websites, servers...
Q: How can I create a function that takes a vector as an argument and returns a new vector with the ele...
A: function v = removeDuplicates(vec) v = [];flag = 0;for i= 1:length(vec)flag = 0;for j = i+1:length(v...
Q: A description of five common network topologies should be included. Which do you consider to be the ...
A: The five common network topologies are as follows:- (1) Mesh Topology Mesh Topology is also known as...
Q: Which of the following can be exploited to direct host to malware-laced servers?
A: An exploited server is one that is no longer fully under your control. Someone else is using it for ...
Q: When do you believe it is best to keep all data and applications in-house, and when do you believe i...
A: Introduction: Yes, your knowledge is comparatively safe within the cloud—likely far more thus than o...
Q: Q2. Implement the following expression using 0-address, 1-address, 2-address, 3 address ISA's A= B*(...
A: In computer organization, computer provided by the task to perform in the form of instructions. It i...
Q: Sort DNS records by the kind of record they include. Describe each with examples and a brief explana...
A: Introduction: A typical method of deploying Content Delivery Networks is to add the CDN's address as...
Q: Explain how the avalanche effect plays a role in providing improved security in the data encryption ...
A: Introduction: A slight change in the plaintext or private key can result in a big change in the ciph...
Q: Describe an efficient method to sort a sequence of n elements if the keys fall into the range of [n2...
A: Comparison based sorting is a kind of sorting, in which, in order to find the Sorted array, the elem...
Q: In this assignment, you are required to test the well-known sorting algorithms (quicksort) performan...
A: Sorting Algorithm Sorting Algorithm are a hard and fast of commands that take an array Or list as an...
Q: ВС + АВС + АВС + АВС + АВС +АВС Denklem 1
A: We are given a minterm expression and we have to find out for rest of the input combination what we ...
Q: Can you please help me to do Snow flake in python please
A: I have answer this question in step 2.
Step by step
Solved in 2 steps with 1 images

- From Operating System Concepts By Gagne, Galvin, Silberschatz. 10th edition Chapter 2 Project, implementation has to be in C: This assignment will involve designing two kernel modules: 1. Design a kernel module that creates a /proc file named /proc/jiffies that reports the current value of jiffies when the /proc/jiffies file is read, such as with the command cat /proc/jiffies. Be sure to remove /proc/jiffies when the module is removed. 2. Design a kernel module that creates a proc file named /proc/seconds that reports the number of elapsed seconds since the kernel module was loaded. This will involve using the value of jiffies as well as the HZ rate. When a user enters the command cat /proc/seconds your kernel module will report the number of seconds that have elapsed since the kernel module was first loaded. Be sure to remove /proc/seconds when the module is removed.Hello / Good afternoon! Would you please explain for me the answer I get by adding a comment . Thanks. Question C++ program : Two sorted files (File1.txt: 1 3 4 6 7 8 11) (File2.txt: 2 3 5 6 7 9 10 11 12 13) The C++ program going to check if the file are sorted and merge them to third file (Mergefile.txt: 1 2 3 3 4 5 6 6 7 7 8 9 10 11 11 12 13) Program Plan: "Main.cpp" Include the requierd header files Declare the necessary function prototype and constants. Define the main() function Under Main function: Get the first file name from the user Check if the first file is sorted using the function "check()" Get the second file name from the user Check if the second file is sorted using function "check()" Merge the two file using the function "merge()". Print the result in to merge file "Check.h" Define the template function necessary Define the bool check "Check if the file is sorted" Declare the necessery structure variables Define the necessary function prototype. Loop…Question: Implement FCFS and SJF scheduling algorithms in C and calculate the average waiting time and average turnaround time of concurrent processes. Input: the number of processes along with the burst time and arrival time for each process. In addition to the desired scheduling algorithm (FCFS or SJF). The program should expect a file name and a scheduling algorithm as arguments. myfile.txt FCFS The file should contain the number of processes in the first line. Then, each following line should contain the burst time and arrival time of one process as follows: ``` <number of processes> <process 1 burst time> <process 2 arrival time> <process 2 burst time> <process 2 arrival time> … ``` the program should calculate the waiting time and turnaround time for each process if the selected scheduling algorithm was used and output the average waiting time and average turnaround time. Output: order of execution of the processes (ex: P1 -> P3 -> P6) and…
- Trying to figure C++ program coding using the following: File IO Control structures Looping Operator precedence Error checking (bad data, filestream fail state, etc.) Use of proper data types; type coersion and/or explict type conversion Exact output Write a program that will calculate numerical and letter grades for a student and output a report: The information will be in the provided data file txt. The data file consists of several rows of data containing a student name and information for 3 types of assignments: First Name, Last Name, number of homework grades, values for homework grades, percentage of total grade, number of program grades, values for program grades, percental of total grade, number of exam grades, values for exam grades, percentage of exam grades. For example, the first row of the data file contains the following: Sherlock Holmes 3 100 100 100 0.15 3 75 80 90 0.40 3 60 70 70 0.45 The student, Sherlock Holmes, has three homework grades, each…C++ Can someone answer the following code below in C++: Please add to the project a print statement that says how long each version ran in milliseconds please! Version 1 of the process creation hierarchy uses linked lists to keep track of child processes as described in section "The process control block", subsection "The PCB data structure". For the purposes of performance evaluation, the PCBs are simplified as follows: All PCBs are implemented as an array of size n. Each process is referred to by the PCB index, 0 through n-1. Each PCB is a structure consisting of only the two fields: parent: a PCB index corresponding to the process's creator children: a pointer to a linked list, where each list element contains the PCB index of one child process The necessary functions are simplified as follows: create(p) represents the create function executed by process PCB[p]. The function creates a new child process PCB[q] of process PCB[p] by performing the following tasks: allocate a…Write a program IN C LANGUAGE with the following features for a hospital management system:- There should be 4 options with sub-options in the main menu:o Exito Show All Records Return to Main Menu Delete Record Update Recordo Search Patient Return to Main Menu Search by ID Search by Name Search by Surnameo New Patient- Sub-options for the particular option must appear when the corresponding option isselected from the main menu.- Patients must be added to the system with Name, Surname, Birthday, E-mail andDepartment information. The ID number is assigned by the program automatically asone more than the last ID number in the file.- If there exists more than one patient with the same name/surname, search byname/surname process must put the information of each patient with the samename/surname, not just the first one it has found.- Patient information must be kept in a text file.- If any of these processes fail, an error notification must be returned for that specificprocess.A…
- Write a C or C++ Program and Screenshot the following system call operation File Management File management system calls handle file manipulation jobs like creating a file, reading, and writing, etc. Functions: Create a file Delete file Open and close file Read, write, and reposition Get and set file attributesThe lifetime of a C++ variable with dynamic storage duration is determined by which of the following:A. The programmer, via the new and delete keywords. B. The variable’s scope. C. The garbage collector. D. None of the above.TASK: This task must be written in C language. NOTE: Please, gather all files into one. Thank you. Given a file, each line of which contains numbers with spaces separated. Write a program that reads line by line from this file and writes each row in ascending numerical order to a file called output.txt. Manage memory dynamically!
- For this discussion, you will utilize functions to provide a way to clear Python’s integrated development environment (IDLE) window. In your initial post, provide the function for achieving this task and explain the process of clearing the IDLE window. Discuss some challenges that you faced in accomplishing this task. Note: The "cls" and "clear" commands are used to clear a terminal (i.e., a DOS prompt or terminal window). please fully elaborate on this I'm struggling to understandWhat is meant by dynamic memory allocation? Why is it needed? What are someimportant functions provided in the C programming language for supporting dynamicmemory allocation? Answer using suitable code snippets.A compiled program can be supplied as an executable file. An executable file is a file that is ready to run. Since an executable file cannot be run, programmers prefer to supply executables rather than source code. What is this executable file and what differentiates it from the source code? In the Python programming language, the process of source code translation is different from that in C programming, explain



