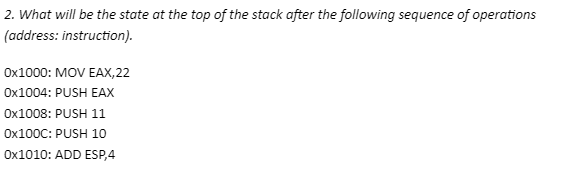
2. What will be the state at the top of the stack after the following sequence of operations (address: instruction). 0x1000: MOV EAX,22 Ox1004: PUSH EAX Ox1008: PUSH 11 0x100C: PUSH 10 0x1010: ADD ESP,4
Q: Which firewall architecture is most popular among businesses today?Why? Explain.
A: Introduction: A firewall is a device that filters traffic on a network in order to fulfil…
Q: The output will be as shown in Snippet 3.65: 10 15 20 25 30 35 80 85 90 Snippet 3.65
A: Note: The programming language is not mentioned in the question so the python programming language…
Q: parallel programming What is the output of the code. Explain your answer
A: Computer software or the programming that are written in the conventionally for the normal…
Q: What layer of the OSI Model is responsible for bit-bit delivery?
A: Introduction: OSI model is nothing but an open system interconnection and it is a reference model…
Q: Corporate governance is defined as the framework of rules and practices by a company’s board of…
A: The question has been answered in step2
Q: What should be written in Q4? (Update for nUnits for O nUnits += nRev%10 - 1; O nUnits *= 10; O…
A: The answer of first case - correct option is nUnits-=1
Q: Is there a specific protocol that is especially vulnerable to assault since so many people depend on…
A: The question is to find a specific protocol that is especially vulnerable to assault since so many…
Q: Write a finite automaton for a language that accepts all words starting with an alphabet character…
A: Automation State 1: Input: a Output: Go to state 2 State 2: Input: [a-zA-Z0-9] Output:…
Q: Processes and programmes that run on a large computer may be divided up into smaller units called…
A: Below is the complete solution with explanation in detail for the given question.
Q: After doing the following statement, the linked list becomes Head P.Link Head 4800 10 4900 4800…
A: The correct option is as follows: contains two nodes.
Q: How can we use e-tailing concept in agriculture sector ?
A: E-tail stands for "Electronic retail store". In the era of digital revolution, e-commerce has become…
Q: The supercomputer is also known as ……. A. Number Counter B. Number Cashier C. Number Crunchier D.…
A: Answer:
Q: What does "process starvation" mean in priority scheduling and how may it be avoided?
A: Given: Low priority processes will go hungry if higher priority processes keep arriving. Processes…
Q: The dining philosopher problem is a classic problem in deadlock management. The problem can be…
A: PROGRAM INTRODUCTION: Include the required header files. Define the values of the required…
Q: If the organization's users are largely reliant on the network, name three protocols that are weak…
A: Introduction: It is another sort of cyber security attack, where new application weakness continues…
Q: What is the optimal policy π for the reinforcement learning problem below (same as related…
A:
Q: On the basis of multiple definitions of operating systems, it is debatable whether operating systems…
A: Definition: Based on different operating system definitions, there is disagreement about whether…
Q: For the formulation of system requirements, provide three guiding concepts, and briefly explore each…
A: Given: System requirements are another name for the settings that must be met in order for the…
Q: Assuming a 4-KB page size (4096 bytes), what are the page Numbers and offsets for the following…
A:
Q: What are the benefits and drawbacks of cloud migration?
A: Introduction: Migration to the cloud paves the way for cloud computing, in which the cloud serves as…
Q: What kind of shifts may we see in the educational system as a consequence of the development of new…
A: This is the response to your query: What modifications to the educational system have been brought…
Q: How do we determine the quality of a software model?
A: Our software development team and Quality Assurance (QA) collaboration together to guarantee that…
Q: Draw a DFA that is defined by a language L that contains all possible integer literals in C
A: The DFA for this language would have to accept all possible integer values as input
Q: How cryptocurrency can disrupt soft drink industry? Please list at least 5 disruptions for…
A: Below is the answer to above question..
Q: 2. Make a program to accept n random numbers then test each if ODD or EVEN.. Then Display how many…
A: do-while loop is used to find the even or odd number. #include <stdio.h> int main(){ int…
Q: What is the microkernel design philosophy of the operating system? Is this method distinct from the…
A: Introduction: The microkernel operating system is based on the concept of minimising the role of the…
Q: An operating system is a collection of programmes that controls computer resources, functions as the…
A: Given: A computer's operating system (OS) is a group of software that manages the hardware resources…
Q: 1 - Discuss a case study on LAN based loT environment (restaurant), and Discussion on THREE (3) LAN…
A: Introduction: Prior to the point of transmission through leased telecommunication lines, a network…
Q: a) Use predecessor instead of successor. When there are choices between single or double rotate,…
A: A Binary tree is the tree of the data structure at which the each node has the at most the two…
Q: In order to replace the code snippet, create a new function and use recursive principles.
A: Here I have defined the function named getMax(). Next, in the function, I have written the base case…
Q: What are the benefits and downsides of dispersed data processing that should be considered while…
A: The range is the difference between the data's largest and smallest observations. The primary…
Q: Assuming a 4-KB page size (4096 bytes), what are the page Numbers and offsets for the following…
A: As per guidelines I can answer only three sub-parts. Thank You. Page size: 4KB : 4096 bytes a) Page…
Q: create a PYTHON program that will make a m Sale Management system. The inventory must have 5…
A: Python is the programming languages which is high level, interpreted, general purpose of the…
Q: 1. Implement the following calculation in assembler using AX,BX,CX and DX registers and describe…
A: We need to implement the given calculation in 8086 and find the final state of CF.
Q: Please translate the following English sentence into a sentence of FOL: use quantifiers "Lucia owns…
A: Quantifiers are a language of fundamental computers that helps in the generation of quantification.…
Q: Write a denotational semantics mapping function for switch statement
A: Switch statement in java Switch(exp) { Case const_exp: Case const_exp: Case const_exp: Default: }
Q: Given AVL Tree in Figure 1. Simulate nodes in the tree by using the given insert operations* +25,…
A: We need to insert the given values in the AVL tree.
Q: What ethical issues does Big Data raise?
A: Introduction: Big data refers to the massive amount of information, both structured and…
Q: Splitting the overall design into several user views when doing user research is a good idea.
A: In conclusion, research suggests: That between three and twenty persons may offer valid results,…
Q: Examine OLAP's role in descriptive analytics.
A: Introduction: Descriptive analytics is a statistical approach for exploring and summarising…
Q: Because the RGB colour model doesn't work well for blown-up images.
A: Answer:
Q: reflection paper is a one page reflection about what you have learned in Computer Programming and…
A: SUMMARYSkills LearnedComputer programming lessons give you a broader understanding of various…
Q: Please answer Values 6-10. Complete the following Incomplete LMC program by filling out the vacant…
A: An instruction model of the computer called Little Man Computer. It has simple von Neumann…
Q: **The below screenshot has VBA codes in the editor windo 3 subs. The instructions on the expected…
A: According to the information given:- We have to define VBA codes on the basis of instructions…
Q: Given a single link of length 800 Km and transmission speed of 49 Mbps between a client and a web…
A: Answer:- Given : Distance between sender and receiver over a link = 800 Km => 800,000 m (1…
Q: How does one go about setting up a communications system?
A: Definition: Through communications links, two or more nodes may communicate with one another and…
Q: Do you use computers and information systems in your daily routine?
A: Introduction: A computer information system (CIS) is a grouping of humans and computers that cycle…
Q: The risk that is faced by businesses that are dependent on information technology has either grown…
A: Introduction: Let's start by examining the purpose of information security. By averting security…
Q: Problem Solving, Design, Implementation and Testing in MATLAB (a) Write a function isPrime (n) that…
A: Answer:- (A) ================================================ function outcome = isPrime(n)outcome =…
Q: A coworker should be briefed about the ARP protocol. Find out what layer it is a part of and what it…
A: Intro It is our responsibility to inform folks about the ARP protocol's workings.The address…
Can you solve this?
Step by step
Solved in 2 steps

- If a microprocessor has a cycle time of 0.5 nanoseconds, what’s the processor clock rate? If the fetch cycle is 40% of the processor cycle time, what memory access speed is required to implement load operations with zero wait states and load operations with two wait states?Considering the following contents of Stack Segment (SS) Register and Stack Pointer (SP) Register: SS = A5B0H, SP = 4DF0H (a) Calculate the values of Top of Stack (ToS) and Bottom of Stack (BoS)? (b) Consider the following operations on the stack: PUSH AX PUSH [CX] PUSH 10 POP [BX] POP AX What is the value of ToS after all these operations? Also, provide the value of ToS after each instruction.A program stack is to use 800 h bytes and SS= 0300 h, A = 1234 h and B = 6AB3 h. Shows the contents of the stack, stack pointer, and physical address using appropriate diagram after the instruction PUSH BX
- (a) Which registers are used to access the stack ?(b) With each PUSH instruction, the stack pointer register SP is incremente or decremented by 2.(c) With each POP instruction, SP is incremented or decremented by 2.(d) List three possible logical addresses corresponding to physical address 143F0.(e) The ADD instruction can affect which bits of the flag register ?(f) The carry flag will be set to 1 in an 8-bit ADD if there is a carry out from bit . . .(g) CF will be set to 1 in a 16-bit ADD if there is a carry out from bit . . .5- What is the 8085 Assembly Language Instruction That do the follwing The contents of the memory location pointed to by the stack pointer register are copied to the registerConsider your stack contains two parameters A and C each of 4 Bytes. Give an instruction that will be used to empty the stack after execution of your main program.
- By using an equation off = ( a - b ) / [ ( d x e ) + c ];(a) illustrate the step to realize this equation by using the stack concept. (b) construct its’ CISC zero address format. (c) construct its CISC one address format. (d) construct the CISC two address format by using only 3 register. (e) In your opinion, do we need to have at least as possible instruction line? Do it will reflectthe performance of computer execution time?What are the values of ECX, EBP, and ESP registers after executing the following instruction? push ECX Before ECX: 0xBABE EBP: 0x0012FF24 ESP: 0x0012FF24 After ECX: EBP: ESP:write a subroutine (in assembly) for ARMcortex-A9 that 1. accepts a memory address A passed in register r0 2. Sum the words incrementing from address A, until the accumulating sum would be considered a negative number ( A is first address read). 3. Return the final value in r 0 . Should preserve state of system using the stack pointer (sp). If you are unable to write Assembly code to complete this problem, please use comments and/or pseudocode as much as possible to describe what should be done.
- Write MIPS assembly for the following function. Assume N is passed to yourfunction in register $a0. Your output should be in register $v0 at the end of yourfunction. Note: You must implement this function recursively. The purpose of thisassignment is to learn how to manipulate the stack correctly in MIPS. int Myfun (int N){ if (N<3) return 1; return ( 2* Myfun(N-1)+ Myfun(N-2));}Please explain each instruction with a comment. Please submit your source codeand a screenshot that shows the registers with correct output value for N=3, i.e.,Myfun(3) returns 3 and Myfun(4) returns 7Create a stack-based program which computes: 7 & (9 | 8). Your answer should include an illustration which shows the state of the stack after each instruction and show the workings of all the calculations that are required.Explain the Memory stack organization of 16 locations of stack( 0 to 15). take the initial value of thestack pointer is SP = 0E in Hex. Explain the following push and pop instructions through the Memorystack organization diagram.(1) PUSH R5 WHERE R5 = XX in Hex(2) POP R4 WHERE R4 = (XX + 3 ) Hex for example roll no 64 is having the data in R5 = 64Hex and R4 is ( 64+3 = 67 Hex)

