2.4 For the general two-state chain with transition matrix P: a b (72) P a and initial distribution a = (a₁, a₂), find the following: (a) the two-step transition matrix (b) the distribution of X₁
Q: 7). The microcontroller has only one or two instructions to move data between memory and CPU. A.…
A: Introduction: The MOV instruction in the 8051 microcontrollers is used to move data from CPU…
Q: An 8-bit computer has a 16-bit address bus. The first 15 lines of the address are used to select a…
A: What Is Address Bus? A computer's hardware address of the physical memory, which is kept as a…
Q: What justification did the RISC architecture have?
A: RISC Architecture: Uncomplicated Instructions When compared to other microprocessor designs,…
Q: Q. Give an Example of Italic H1 heading HTML?
A: Given Question is asking for a html code to show H1 heading in italic. Code for this question is in…
Q: Provide some instances of waste and errors that may occur in an IS system, as well as their causes…
A: Introduction: The unused or underutilized system features: A lack of training or understanding of…
Q: Give a proof of
A: Let x and y be arbitrary objects. Suppose that for all x and y, x=y implies that for all y,…
Q: <!DOCTYPE html><html><head><title>Home…
A: HTML stands for a hypertext markup language. It is used for designing static web pages along with…
Q: Give an example code for bold text tag in html?
A: Given question wants a sample code in html using bold text tag.
Q: Describe the user support processes, such as user education and help desks.
A: The question is describe the user support processes, such as user education and help desks.
Q: online behavior might make becoming a victim online more likely. Can the principle of normal actions…
A: Answer: Victimization is when someone is unjustly treated or made to feel as if they are in a wrong…
Q: An app uses to assist study room management at the library. Main problems are the students cant…
A: A new library app uses artificial intelligence and facial recognition to struggle with student…
Q: ABCDEFGHIJKL Figure 4: Block of data a) Determine which block of data are allocated at location 8, 9…
A: Solution:: Following is the distribution in RAID-6 :: a) Location 8 = G Location 9 = H Location…
Q: Give instances to make your point. How information security ideas are merged with controls and…
A: An Overview of Information Safety and Assurance: The internet is not a single network but rather a…
Q: Provide some instances of waste and errors that may occur in an IS system, as well as their causes…
A: 1. Unused or underutilized system features: The cause of this is typically a lack of training or…
Q: What is function overloading and operator overloading?
A:
Q: Exercise 1.5 What are the responsibilities of a DBA? If we assume that the DBA is never interested…
A: A Database Administrator (DBA) design, implement, administers and monitors data management systems…
Q: Discuss how the word "firewall" is used in network topologies and what it means in the context of…
A: A firewall is a kind of cybersecurity equipment that is used to filter network traffic. Firewalls…
Q: What is the disk capacity? What is the average access time? Assume this file is stored in successive…
A: Consider a magnetic disk drive with 8 surfaces, 512 tracks per surface, and 64 sectors per track.…
Q: Calculate the number of nodes in a complete binary tree with height h. Where h is equal to the 3rd…
A: A binary tree is a tree with at most 2 child nodes in which the left node is always lesser than the…
Q: Give a context-free grammar that generates the following language: k≥ 2, each x; € {a,b], and for…
A: Context-free grammar is used in compiler design to test the possible string patterns within a given…
Q: The CIST department of CGTC needs a list of all CIST students who made the Dean’s List this…
A: Given data, The CIST department of CGTC needs a list of all CIST students who made the Dean’s List…
Q: Name five benefits and five drawbacks of mobile displays.
A: Name five benefits and five drawbacks of mobile displays.
Q: Which command is used to list the contents of the current working directory including the hidden…
A: Hidden File in Linux: The easiest way to show hidden files on Linux is to use the ls command with…
Q: restricted access protocol.
A: If a protocol is enabled for Data ONTAP, you can restrict the protocol's access to the storage…
Q: distances between nodes in an eight-node network is presented in the from-to distance table below.…
A: Here, from the question In the given problem, the graph contains 8 nodes from 1 to 8 in it.. The…
Q: Can you explain to me what CISC and RISC are and how they differ?
A: Solution::
Q: Provide the asymptotic characterization of the following recurrence relation using the Master…
A: Master's theorem is used to find the time complexity of the recurrence relation. The general format…
Q: To access a database, we need to open a connection to it first and close it once our job is done.…
A: The answer is as follows.
Q: List at least two benefits of OOP over PP alone.
A: There are different types of programming:- Functional Programming:- This is programming language…
Q: Briefly define the seven RAID levels.
A: Your answer is given below. Introduction :- RAID represents a redundant array of independent disks.…
Q: Write Java code that uses class IntBTNode to construct the following binary tree and then print the…
A: The question is to write JAVA code for the given problem.
Q: Does having a high bias underfits data and produces a model that is too simple and general, while…
A: Bias & variance is used to train the model basically it is an error rate of testing data.
Q: Give a single example of a sensor utilized in a mobile device.
A: The question has been answered in step2
Q: 2. Use a paper-and-pencil approach to compute the following division in binary. i. Dividend = 1110,…
A: Given that use a paper and pencil approach to compute the following division in binary. Dividend =…
Q: What exactly is the purpose of Artificial Intelligence (AI)? Identify its several domains and…
A: The question has been answered in step2
Q: Res.
A: For the given range: 225.10.20.0/24
Q: Social networking platforms are popular (such as Facebook and Twitter). Determine why people choose…
A: Individuals prefer digital social networks due the following reasons:1. Introverts find it easy to…
Q: Problem Suggest reasons why RAMS traditionally have been organized as only 1 bit per chip whereas…
A: The answer of the question is given below:
Q: Explain the benefits that come from using Cleanroom Software Engineering. Demonstrate the benefits…
A: Cleanroom Software engineering:- This is based on set of formal specifications which describes the…
Q: Create a program that a user can use to manage the primary email address and phone number for a…
A: Since no programming language is mentioned, I am using python. Code: contacts=[[1,"Guido van…
Q: Describe the role that LSI chips typically play in a contemporary personal computer.
A: Personal Computer: A personal computer (PC) is a multifunctional a microcomputer that is…
Q: C Programming 1.Enter an integer into n 2.Use malloc to dynamically allocate an array of size n,…
A: The above question is solved in step 2 :-
Q: For this question, you need to provide a function definition and a simple testing code. -- Define a…
A: Coded using C++.
Q: Consider the synchronous state machine described by the attached ASM. For this machine: a) Define…
A: Q1. A D flip-flop should be used for the state memory. State machines have two states, S0 and S1,…
Q: Define the concept of Resource allocation?
A: According to the question useful resource for the allocation this is a method of planning, managing,…
Q: assume you have 50 to 100 employees whose ids are in the rage of 1000 to 1099, and you have a file…
A: Here is complete solution explained
Q: What is the output for the following pseudocode segment? List all output. S = 1 t = 4 u = 6 while s…
A:
Q: Give an example of a situation in which multicast addresses might be beneficial.
A: Multicast Address:- A multicast address is a specific type of IP address labeling a network location…
Q: . For n No let w(n) denote the number of 1s in the binary representation of n. For example, w(9) =…
A:
Q: Give THREE (3) instances of vulnerabilities in a network and briefly define the word "vulnerability"…
A: Three Vulnerabilities: You should keep an a eye out for the following three system vulnerabilities…
2.4
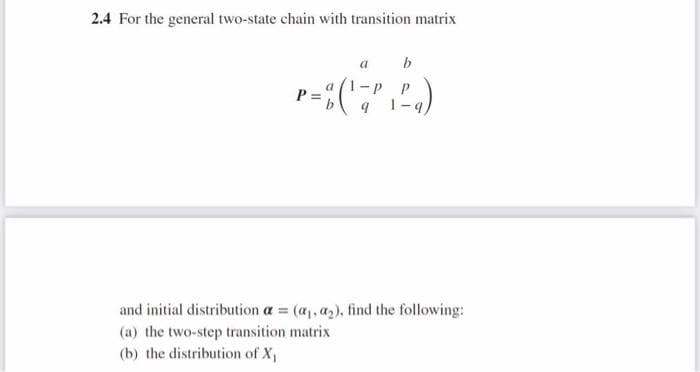
Step by step
Solved in 2 steps with 2 images

- For the transition probability matrix P = 1 2 3 4 5 1 0.2 0.1 0.15 0 0.55 2 0 1 0 0 0 3 0.35 0.2 0.2 0.1 0.15 4 0 0 0 1 0 5 0.25 0.2 0.15 0.25 0.15 (a) Rewrite P in the canonical form, clearly identifying R and Q. (b) For each state, i, calculate the mean number of times that the process is in a transient state j, given it started in i. (c) For each state i, find the mean number of transitions before the process hits an absorbing state, given that the process starts in a transient state i. (d) For each state i, find the probability of ending in each of the absorbing states.Simplify the following Boolean functions, using K-maps: F (w, x, y, z)=Σ(11, 12, 13, 14, 15)In Sammon mapping, if the mapping is linear, namely, g(x)W) = Wt x, how can W that minimizes the Sammon stress be calculated?
- Consider a three-qubit quantum system, with each qubit described by the computational basis states |0⟩ and |1⟩. The system is in the following quantum state: (a) Find the reduced density matrix ρA for the first qubit (from the left) by tracing out the other two qubits. (b) Show that the state |Ψ⟩ is entangled by proving that it cannot be written as a product state of the form |ψA⟩ ⊗ |ψBC ⟩.Prove that the following instance of PCP does not have a match [aba, bb], [ab, a], [bab, aa], [ab, ba]Consider the Markov chain with three states,S={1,2,3}, that has the following transition matrix P= Draw the state transition diagram for this chain. If we know P(X1=1) =P(X1=2) =1/4, find P(X1=3, X2=2,X3=1)
- 3.6 a. Use the hybrid (binary/bipolar) form of Hebb rule learning as described in Example 3.6 to find the weight matrix for the associative memory network based on the following binary input-output vector pairs: s=0100 0 (=01 0 =01 001 @@= 0 s3) =0 1.0 0 t3)=0 1 s@=0 110 H4) =@ 1) b. Using the unit step function (with threshold 0) as the output units’ activation function, test the response of your network on each of the input patterns. Describe the results obtained. c. Test the response of your network on various combinations of input patterns with “‘mistakes” or ‘‘missing-data’ (as in Example 3.8). Discuss the results you ob- serve.In which case are Sobol coefficients not a good measure of sensitivity ? a. if the model can be well approximated with a gPC expansion b. If many of the the higher order moments of the output are large c. if the input random variables are dependentHere is the Berkeley Madonna code: {Top model} {Reservoirs} d/dt (Q) = + Stimulus - Imemb INIT Q = -65/cap {Flows} Stimulus = Intensity*SquarePulse(3,.5) {at t=3 of 0.5 duration} Imemb = IL+IK+INa {Functions} Intensity = 100 {microamps} cap = 1 E = Q/cap {Submodel "INa_"} {Functions} ENa = 50 INa = gNa*(E-ENa) GNaMax = 120 gNa = GNaMax*m*m*m*h {Submodel "m_gates"} {Reservoirs} d/dt (m) = + m_prod - m_decay INIT m = am/(am+bm) {Flows} m_prod = am*(1-m) m_decay = bm*m {Functions} am = 0.1*(E+40)/(1-exp(-(E+40)/10)) bm = 4*exp(-(E+65)/18) {Submodel "h_gates"} {Reservoirs} d/dt (h) = + h_prod - h_decay INIT h = ah/(ah+bh) {Flows} h_prod = ah*(1-h) h_decay = bh*h {Functions} ah = 0.07*exp(-(E+65)/20) bh =…
- Consider a system with input x(t) and output y(t) . The relationship between input and output is y(t) = x(t)x(t − 2) a. Is the system causal or non-causal?b. Determine the output of system when input is Aδ(t) , where A is any real orcomplex number?Consider the following time series:Yt=Yt−1−0.25Yt−2+wt−0.5wt−1,wt is a white noise process with variance σw^2. Simulate a sample from the reduced model and calculate the sample ACF and PACF. Plot the sample ACF and theoretical ACF on one graph, and the sample PACF and the theoretical PACF on the other graph. Show the two graphs on one figure. (Please provide R codes).Given the complement of a graph G is a graph G' which contains all the vertices of G, but for each unweighted edge that exists in G, it is not in G', and for each possible edge not in G, it is in G'. What logical operation and operand(s) can be applied to the adjacency matrix of G to produce G'? AND G's adjacency matrix with 0 to produce G' XOR G's adjacency matrix with 0 to produce G' XOR G's adjacency matrix with 1 to produce G' AND G's adjacency matrix with 1 to produce G'

