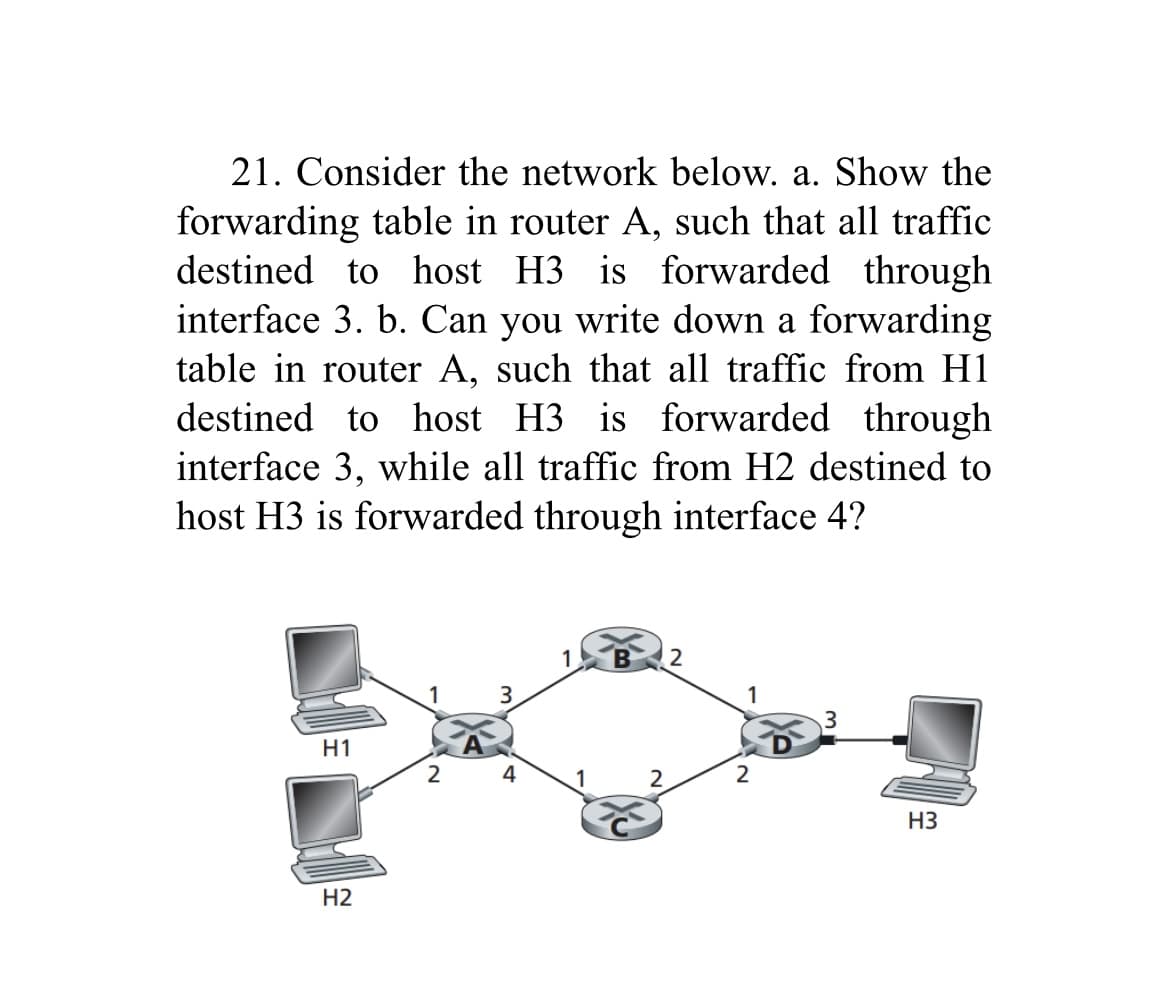
21. Consider the network below. a. Show the forwarding table in router A, such that all traffic destined to host H3 is forwarded through interface 3. b. Can you write down a forwarding table in router A, such that all traffic from H1 destined to host H3 is forwarded through interface 3, while all traffic from H2 destined to host H3 is forwarded through interface 4? H1 H2 2 3 4 1 B 2 2. 2 3 H3
Q: What causes DFDs to be unbalanced?
A: Data Flow Diagrams (DFDs) are graphical representations of how data flows within a system or…
Q: Your great-aunt and -uncle gave you a new computer monitor with affection. You attempt to connect…
A: What is computer monitor:A computer monitor is an output device that displays visual information…
Q: Which implementation of the size and isEmpty methods would you use if you had the potential for a…
A: The size and isEmpty functions should be implemented as efficiently as possible while taking into…
Q: 4. Given the language L = {wxwR: w ∈ {a, b}*, x is a fixed terminal symbol}, answer the following…
A: L = {wxwR: w ∈ {a, b}*, x is a fixed terminal symbol}
Q: How does the data dictionary work into each of the six phases of the DBLC?
A: The Data Dictionary is a crucial component in the design and development of a database system. It…
Q: IP, Subnet Mask, Subnet Information? field value Host IP subnet mask Subnet bitcount Subnet count…
A: The provided information includes an IP address, subnet mask, and subnet details.
Q: Describe how colour codes are utilised in the BFS algorithm. Give a concise description of every co
A: In the BFS (Breadth-First Search) algorithm, color codes are often used to keep track of the state…
Q: Technically, RAM stands for random-access memory. Each list should have its own separate list. Why…
A: Random Access Memory (RAM) is vital in embedded approaches due to its fast interpretation and symbol…
Q: What distinguishes the numerous unsigned binary formats, other than the underscore character?
A: It is possible to represent positive numbers or zero using unsigned binary formats, which represent…
Q: Problem 3: For each of the two graphs below, determine whether they are planar. Justify your answer:…
A: In graph theory, a planar graph is a graph that can be embedded in the plane, using the kuratowski's…
Q: Some content creators have formed their own communities. How would you characterize Google's…
A: With the rise of digital platforms, content creators have been able to form their own communities…
Q: What ethical and safety considerations may arise if a corporation misused business intelligence…
A: Ethical technical alludes to a bunch of values that tends to how you use innovation in your business…
Q: How does the data dictionary work into each of the six phases of the DBLC?
A: The Database Life Cycle (DBLC) is a systematic approach to managing and maintaining databases…
Q: How does a computer function?
A: In today's time, there are many types of computer system, that is, from Micro to Super ones. So,…
Q: Name at least three widespread computer systems that collect user data and describe the pros and…
A: Micro Computer The littlest among them are micro PCs. They are little in actual size (the greater…
Q: Explain how contemporary cloud computing usage have helped the world.
A: Contemporary cloud computing has revolutionized the way individuals and organizations store,…
Q: Who or what within the United States is responsible for cyber policy?
A: As technology continues to advance, so does the need for robust cyber security measures to protect…
Q: Which firewall regulation methods work best? Explain.
A: There is no one-size-fits-all strategy for firewall regulation that is suitable in every…
Q: Write a program that initializes a blank array and allows the user to input their own numbers (0 to…
A: Initialize a blank array of size n (5 <= n <= 20) to store user inputs.Create a loop that will…
Q: What purpose does the information security management system serve?
A: A organization for management information security (ISMS) is a systematic approach to managing…
Q: Please elaborate on the significance of database architecture in the classroom.
A: Database architecture refers to the overall design and structure of a database system. It…
Q: Which of the following actions will improve database performance? A) Cache data in memory…
A: Database performance is basically to optimization of all resources in right way , and possible…
Q: Use drawings to show the differences between scalar and superscalar processors. Compared to scalar…
A: It is type of processor that executes the scalar data it executes integers instructions and uses…
Q: Q2) a) Use Boolean Algebra to simplify the following expression. AC[B+B(B+C)]
A: Boolean Algebra:It is a mathematical structure and branch of algebra which deals with the variables…
Q: Create a library database that includes two tables, one for books and the other for accounts, and…
A: Certainly! Here's an example of creating a library database with two tables (books and accounts) in…
Q: DNS converts IP addresses to names. Creative sector companies use www.cr.indusry.com. Identify the…
A: The Domain Name System (DNS) plays a crucial role in making the internet user-friendly. It…
Q: In comparison to a traditional telephone network, what do you consider to be the internet's most…
A: What is traditional telephone network: A traditional telephone network refers to the analog-based…
Q: What are the cost and performance distinctions between primary and secondary storage?
A: The question is asking about the cost and performance differences between primary and secondary…
Q: Assume that the output.txt file contains: First Line Given the following snippet of code: File…
A: File output = new File("output.txt"); try { Files.writeString(output.toPath(), "Second Line",…
Q: 333: E8B3 8B3: 0A12 A12: 2153 Since the contents of the relevant addresses are 333 in the…
A: According to the information given:-We have to define the contents of the relevant addresses are 333…
Q: 2] have the following unique permutations: [ [1,1,2], [1,2,1], [2,1,1] ] """ def…
A: This function takes a list of integers nums as input and returns a list of all unique permutations…
Q: Create a SinglyLinkedList method named reverse that reverses the order of the list's items. This…
A: Linked lists are data structures that consist of nodes with data and pointers to the next node. The…
Q: What do you think are the most striking features of the internet when compared to a traditional…
A: It becomes clear that the internet has a number of distinguishing qualities when compared to a…
Q: If possible, please describe at least three distinct examples of the responsibilities held by the…
A: What is (initialization) function: The "(initialization) function" refers to the WinMain function in…
Q: The distinction between Internet Explorer and Chrome
A: Understanding Internet Explorer and ChromeInternet Explorer and Chrome are both web browsers that…
Q: Is there a fixed number of linked lists in an m-size hash table? Please tell me what a hash function…
A: In an m-size hash table, the number of linked lists is not fixed. The number of linked lists depends…
Q: In which situation is it helpful to use Oracle Dedicated Region Cloud@Customer? To support…
A: According to the information given:-We have to choose the correct option to satisfy the statement.
Q: 111.111.111.111' 74-29-9C-E8-FF-55 A 111.111.111.112 CC-49-DE-DO-AB-7D R 222.222.222.220…
A: IP Address:An IP (Internet Protocol) address is a unique numerical identifier assigned to each…
Q: Hash tables are more efficient than linear lists in many respects. What's wrong? hashtable-based…
A: Hash tables are widely used data structures in computer science due to their efficiency in storing…
Q: You received a new computer monitor from your great-aunt and uncle. The monitor won't connect to any…
A: Receiving a new computer monitor might be exciting, but it can also be annoying if it won't connect…
Q: To what end does a firewall primarily serve? My current project is a packet-filtering programme.…
A: Firewalls are essential network security components that act as a barrier between internal and…
Q: RAID live backups may limit hard disc storage. Are backups worth half your disc space? What RAID…
A: RAID (Redundant Array of Independent Disks) configuration plays an important role in protecting data…
Q: DBA upkeep after DBMS selection and implementation?
A: The folder administrator (DBA) plays a vital role in controlling and sustaining the record…
Q: The new wireless network infrastructure causes patient monitor connection concerns in many…
A: In the context of a healthcare ability, the wireless network communications is a dangerous part of…
Q: Prove that the following language is non-regular, using the Pumping Lemma. L = {ambcr | m, n, r =…
A: The pumping lemma is a fundamental result in formal language theory that provides a way to prove…
Q: Which of the following is NOT an essential function performed by a firewall? What are the best…
A: What is firewall: A firewall is a network security device that monitors and controls incoming and…
Q: Within the Management Studio, you can build a SQL statement without having to write your own code by…
A: A computer language called SQL (Structured Query Language) is used to manage and work with…
Q: hello. This is my code: #include #include #include typedef struct HuffmanNode { int…
A: Huffman Tree:The Huffman tree is a binary tree used in data compression algorithms. It assigns…
Q: Describe how colour codes are utilised in the BFS algorithm. Give a concise description of every…
A: Color codes are frequently used in the BFS (Breadth-First Search) method to identify and monitor the…
Q: Would you visit a comparable web page? Why?
A: In the vast realm of the internet, the decision to visit a comparable web page requires thoughtful…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- P1. Consider the network below. a. Show the forwarding table in router A, such that all traffic destined to host H3 is forwarded through interface 3. b. Can you write down a forwarding table in router A, such that all traffic from H1 destined to host H3 is forwarded through interface 3, while all traffic from H2 destined to host H3 is forwarded through interface 4? (Hint: This is a trick question.)1. Below is a nested MPLS network by MTN. With the assumption that Customer 6 (C6) is connected to Router 6 (R6), execute a Dijkstra Algorithm on a Link State routing to determine the shortest path for Customer 6 to transmit packets to every other Customer/Destination connected to the rest of the Routers on the network. (a) i. Tabulate the executed iteration for the Dijkstra Algorithm using the table below. Iteration Nodes R1 R2 R3 R4 R5 R7 R8 R9 R10 0 [6] 1 [6,3] 2 [6,3,2] 3 [6,3,2,1] 4 [6,3,2,1,4] 5 [6,3,2,1,4,5] 6 [6,3,2,1,4,5,7]…55. The problem with unicast delivery is that the : a. memory allocation is difficult b. server must establish a seperate unicast session for each client c. the routers must support unicasting d. the clients must be close to the server
- 22. A datagram subnet allows routers to drop packets whenever they need to. The probability of a router discarding a packet is p. Consider the case of a source host connected to the source router, which is connected to the destination router, and then to the destination host. If either of the routers discards a packet, the source host eventually times out and tries again. If both host-router and router-router lines are counted as hops, what is the mean number of a. (a) hops a packet makes per transmission? b. (b) transmissions a packet makes? (c) hops required per received packet?22. A datagram subnet allows routers to drop packets whenever they need to. The probability of a router discarding a packet is p. Consider the case of a source host connected to the source router, which is connected to the destination router, and then to the destination host. If either of the routers discards a packet, the source host eventually times out and tries again. If both host-router and router-router lines are counted as hops, what is the mean number of a. (a) hops a packet makes per transmission? b. (b) transmissions a packet makes? c. (c) hops required per received packet?Below is a nested MPLS network by MTN. With the assumption that Customer 6 (C6) is connected to Router 6 (R6), execute a Dijkstra Algorithm on a Link State routing to determine the shortest path for Customer 6 to transmit packets to every other Customer/Destination connected to the rest of the Routers on the network. Tabulate the executed iteration for the Dijkstra Algorithm using the table below. Iteration Nodes R1 R2 R3 R4 R5 R7 R8 R9 R10 0 [6] 1 [6,3] 2 [6,3,2] 3 [6,3,2,1] 4 [6,3,2,1,4] 5 [6,3,2,1,4,5] 6 [6,3,2,1,4,5,7]…
- Below is a nested MPLS network by MTN. With the assumption that Customer 6 (C6) is connected to Router 6 (R6), execute a Dijkstra Algorithm on a Link State routing to determine the shortest path for Customer 6 to transmit packets to every other Customer/Destination connected to the rest of the Routers on the network. Tabulate the executed iteration for the Dijkstra Algorithm using the table below. Iteration Nodes R1 R2 R3 R4 R5 R7 R8 R9 R10 0 [6] 1 [6,3] 2 [6,3,2] 3 [6,3,2,1] 4 [6,3,2,1,4] 5 [6,3,2,1,4,5] 6 [6,3,2,1,4,5,7]…A router has the following four active flows, and each flow has packets to transmit. Given FQ is being used on the router, what is the order that the packets will be transmitted?We have 5 routers labled A-E. Suppose we have the forwarding tables shown below after the routingalgorithm is stable. Let all links have cost 1. a. If a message is originated from A and a destination is E. Which path does it take?b. If a message is originated from C and a destination is D. Which path does it take?c. Give a diagram of a possible network consistent with these tables.
- (a) Where might a datagram be queued inside a router to wait for further processing? (b) How does the head-of-the-line blocking occur?Consider the network shown below, and Dijkstra’s link-state algorithm. Suppose that Dijkstra's algorithm has been run to compute the least cost paths from node E to all other nodes. Now suppose that source node E has a packet to send to destination node A. What is the first router to which E will forward this packet on its path to A?Consider a computer 1 that communicates with a computer 2 via LAN1, router R1, and LAN2. The sending computer1 is running two processes at this time with port addresses k and l. The receiving computer 2 is running three processes at this time with port addresses f, g and h. Process k in the sending computer 1 needs to communicate with process g in the receiving computer 2. Draw the network and show the contents of segments, packets and frames at the network, data link, and transport layer for each hop. Note: Computer 1 has: Physical address=15, Logical address=A Router R1 has: Physical address in the side of LAN 1=20, Logical address in the side of LAN1=B Physical address in the side of LAN 2=50, Logical address in the side of LAN2=D. Computer 2 has: Physical address=77, Logical address=E.

