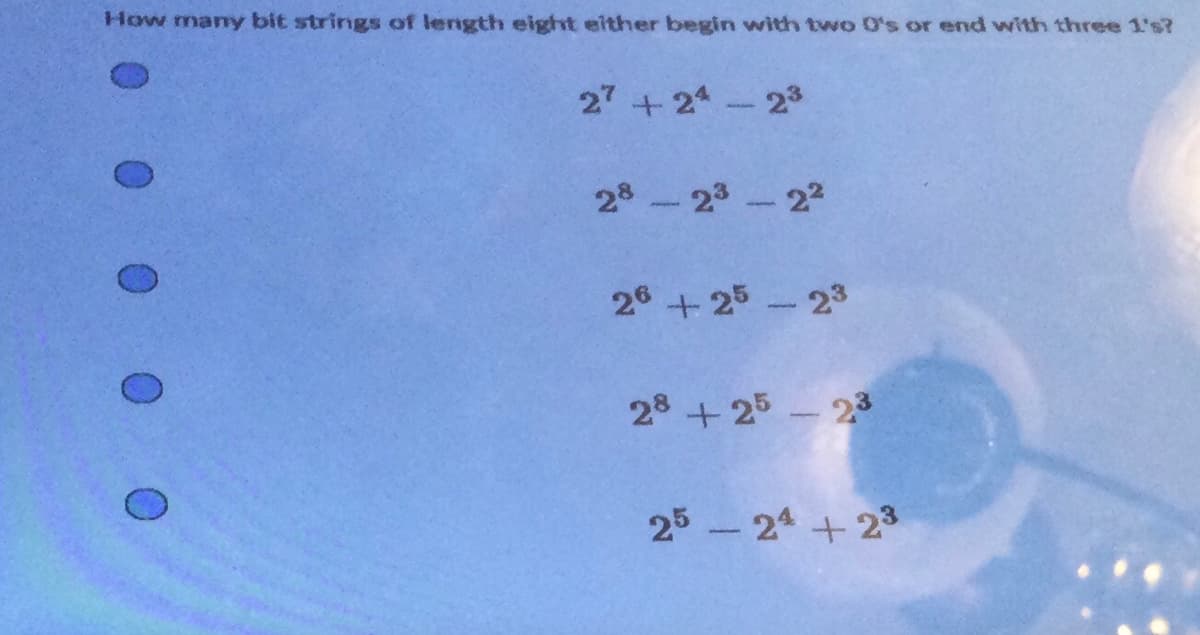
27 +21 28-23-22 26 +25-23 28 +25 - 23
Q: public class LinkedList { protected LLNode list; public void removeFirst() {
A: The removeFirst method in the given LinkedList class is incorrect. The code attempts to remove the…
Q: When starting a new process to execute a command, how does the shell determine whether or not a file…
A: The entry rights of a file can help specify whether or not it can be used. There are three…
Q: What are the many topologies that may be applied to a network, and which of them would you…
A: There are several different topologies of computer networks, and the choice of topology depends on…
Q: Devise an algorithm to scan an input array a of n elements, and output all prime numbers in the…
A: Answer: Algorithms Step1: Declared the array Step2: then find the size of the array Step3: then…
Q: What exactly is meant by the term "normalization" when referring to a database management system
A: Normalization: It is a database architectural strategy that reduces data redundancy and eliminates…
Q: For a one-dimensional dynamic programming cache, a one-dimensional dynamic programming technique is…
A: Dynamic programming is a powerful algorithmic technique used to solve optimization problems by…
Q: How can I create a form in an application that just displays the columns of one entry from a…
A: Using the Details View control, a form is developed in C# to display the columns of a single row of…
Q: What does the acronym RGB stand for?
A: Red, Green, and Blue are the three primary colours, and their abbreviations are abbreviated as RGB.…
Q: Track system architecture's evolution, focusing on the personal computer and Internet. If possible,…
A: The evolution of personal computer and Internet system architectures is an ongoing process, driven…
Q: You may describe the function of each component of a typical operating system in a single sentence…
A: The following data are displayed: Include a list of the OS parts and a brief description of their…
Q: ake use of a statement to initialize a new instance of the Transcript class.
A: here is an example statement to initialize a new instance of the Transcript class: Transcript…
Q: In the context of information technology security, what are the key differences between on-premises…
A: Information security is the practice of protecting information by mitigating information risks. It…
Q: by Codechum Admin Implement the class Student. This class should contain 4 properties: firstName a…
A: The Student class is a simple class that represents a student's information, including their first…
Q: DNS records by kind. Explain their use using examples. Can a business's web and mail servers share…
A: A typical method for deploying content delivery networks is to add the address of the Content…
Q: depicts a connection where one entity's data is represented by one instance in the other?
A: Introduction: The following is a list of the three different kinds of relationships that can be…
Q: Why is a bridge built in the first place? A device known as a bridge connects two local networks…
A: Given: To have knowledge about a bridge, which is a device that joins two local networks that use…
Q: maximize the effectiveness of virtual memory systems, what kinds of hardware operations are…
A: Virtual memory is a technique used by operating systems to allow programs to access more memory than…
Q: For the given IP address 128.168.0.1/20, calculate the Subnet mask, Network address, total number of
A: To calculate the subnet mask, network address, total number of host addresses possible, and range of…
Q: When did the internet of things begin, and what are some of its current applications?
A: The concept of the Internet of Things (IoT) originated in the late 1990s, but the term "Internet of…
Q: What much of an impact has the algorithm for deleting files had on Symbian, Android, and the iPhone?
A: Given: Has the file deletion algorithm affected Symbian, Android, and iPhone? Solution: Android uses…
Q: What are the two main advantages of layered protocols? Give evidence.
A: The transfer of files, for example, requires numerous protocols. It's common to see a series of…
Q: what are the advantages and disadvantages of raid level 5 compared to raid level 4
A: Data storage technique called RAID 4 (Redundant Array of Independent Disks level 4) employs…
Q: In the context of the administration and monitoring of a network, what role does logging play?…
A: Introduction:- Here are some of the ways in which records contribute to the tracking and…
Q: Trace the following flowchart for when input values are -12, 3, -3, 6, -11, 14, 1,10, 3, 2, 6,0 and…
A: From the above given question the input values are : -12,3,-3,6,-11,14,1,10,3,2,6,0 What we need to…
Q: technology must prioritize e
A: Artificial Intelligence (AI) technology has been advancing at an unprecedented rate in recent years,…
Q: A buddy offers you the random number generator shown below: My-Random()\sout: r is a random integer.…
A: The question asks for an explanation of how one can evaluate the effectiveness of the random number…
Q: What are the benefits of establishing parent-child ties amongst different classes
A: Parent-child ties, or parent-child relationships, refer to a concept in object-oriented programming…
Q: For what applications can SSH prove useful?
A: Applications for Secure Shell (SSH) SSH, or secure shell, is a network mechanism that enables two…
Q: What kind of impact does the blockchain have on the process known as "Systems Analysis and Design"?
A: The "disruptive" nature of blockchain technology may be linked to the fact that it introduces a…
Q: calling protocol.
A: The calling protocol is a set of rules and procedures that govern the way in which functions or…
Q: Formative evaluation may address user issues and enhance online application usability, according to…
A: Don Norman on the use of constraints: "Providing physical, logical, semantic, and cultural…
Q: What are some of the limitations of using the OSI model?
A: Given: Describe the issues that the OSI Model has. Answer: OSI Model's Drawbacks There is a lack of…
Q: What makes an infrared network unique in terms of the media that it uses?
A: Answer the above question are as follows
Q: What sets a hashtable distinct from a hashmap, and how are they both used?
A: The Hashtable and Hashmap. 1) Two of the most crucial classes in the Java Collection architecture…
Q: PYTHON PROGRAMMING ONLY PLEASE I am doing a patient portal/record keeping system i already have the…
A: The Python code is given below with output screenshot
Q: Explain "matching in algorithms."
A: Matching in algorithms refers to the process of identifying pairs of elements in a set that satisfy…
Q: What is the minimum amount of storage space necessary for a single image?
A: Solution: Given, What is the minimum amount of storage space necessary for a single image?
Q: In light of Don Norman's concept of 'user issues,' we will investigate how formative assessment…
A: Don Norman on the value of limitations: Physical, rational, semantic, and societal limitations…
Q: What are the four most common kinds of database failures that people experience?
A: The answer to the question is given below:
Q: Please provide a succinct explanation of the XMM registers.
A: The XMM registers are a set of registers in the x86-64 architecture that are specifically designed…
Q: What are the characteristics that are shared by a derived class and the base class from which it was…
A: The class that inherits from the base class is referred to as the derived class, while the class…
Q: A "balanced" tree has equal-height leaf nodes.
A: Given: All of the leaf nodes of a "balanced" tree are of the same height.
Q: What are the key distinctions between an interpreter and a compiler?
A: Compiler: A compiler is a computer software that interprets a high-level programming language, such…
Q: Define test-driven development success criteria. How would you improve it as a teaching tool at your…
A: Test-driven development (TDD) is a software development approach that involves writing automated…
Q: What are the Arduino x86's strengths, weaknesses, and embedded applications? Use a case study and…
A: The correct response to the enquiry: A wide variety of chips and regulators are used in the Arduino…
Q: In the context of operating systems, what precisely does the phrase "partitioning" refer to? Think…
A: Partitioning is an essential concept in the world of operating systems and data management, with the…
Q: Firewalls play a crucial role in maintaining a secure network environment. Can you remember to…
A: Introduction: Firewalls are an essential part of any network security strategy. They are designed to…
Q: Cybercrime Conceptual Framework? Reference your answer.
A: Several people, businesses, and governments commonly rely on the Internet daily. The way…
Q: Explain how the ideas behind the RAID organization may be implemented in a setting involving…
A: RAID stands for RAID (Redundant Array Of Independent Disk)RAID uses many discs for speed,…
Q: What exactly is meant by the phrase "azure domain"?
A: Azure Domain, a cloud computing platform from Microsoft, offers a wide range of services and goods,…
Step by step
Solved in 3 steps

- Bit strings consist of 0 and 1. How many bit strings of length 7 either start with “1” or end with the 3 bits “000”? A.80 B.72 C.64 D.16Please for thi question, kindly explain into details for me. This seems a new topic to me altogether. Thanks a lot. A bit string is a sequence of numbers consisting of 0’s and 1’s. Answer the following questions with explanation and/orclear computations.(a) How many bit strings of length 5 are there?(b) How many bit strings of length 5 contain at least three 0’s?(c) How many bit strings of length 6 are palindromic (i.e., read the same from left to right as from right to left)?(d) How many bit strings of length 8 contain at least two 1’s?Consider the following bit stream: 0100 0011 0111 1001 0110 0010 0111 0010 0010 0000 0011 0010 0011 0001 0011 0101 Number of words = ___________________ Number of doublewords = ___________________ Number of quadwords = ___________________ Decimal value of most significant byte = ___________________ Decimal value of least significant nibble = ___________________ Hexadecimal representation of bit stream = ___________________ ASCII representation of bit stream = ___________________
- Consider the following bit stream: 0100 0011 0111 1001 0110 0010 0111 0010 0010 0000 0011 0010 0011 0001 0011 0101 a) Decimal value of most significant byte = ___________________ b) Decimal value of least significant nibble = ___________________ c) Hexadecimal representation of bit stream = ___________________Consider the following bit stream: 0100 0011 0111 1001 0110 0010 0111 0010 0010 0000 0011 0010 0011 0001 0011 0101 Number of bits = __________________ Number of bytes = ___________________ Number of nibbles = _________________ Number of words = ___________________ Number of doublewords = ___________________ Number of quadwords = ___________________ Decimal value of most significant byte = ___________________ Decimal value of least significant nibble = ___________________ Hexadecimal representation of bit stream = ___________________ ASCII representation of bit stream = ___________________How can you can immediately tell if a bit stream represents an odd or even decimal number by examining the LSB. Explain why.
- IEEE 754-2008 contains a half precision that is only 16 bits wide. The leftmost bit is still the sign bit, the exponent is 5 bits wide and has a bias of 15, and the fraction is 10 bits long. A hidden 1 is assumed as part of the significand just like the IEEE-754 format we learnt in the class. Write down the bit pattern to represent −0.15625 × 100 in IEEE 754-2008 half-precision format. You need to find out the bits for the sign, the exponent, and the fraction. To answer this question, you need to convert the decimal fraction to its binary representation. Check out the link given in Q1. You have to show all steps including the fraction conversion (from decimal to binary).(Non-negative signed binary numbers) What happens if all of the zeros on the left side of a non-negative signed binary number are removed? In general, how does one convert a non-negative N-bit signed binary number to an M-bit unsigned binary number, where N ≤ M?A binary code is a string of 0's and 1's. In particular, an n-bit binary code is a string of "n" 0's and 1's. For example, the code "01001" is a 5-bit binary code. How many 5-bit binary codes can be formed?
- 1. Compact discs record two channels (left and right) of music at a sampling frequency of ??=44.1kHz for each channel. If each sample is encoded with 16 bits, and one byte is 8 bits, how many bytes are required to store 48.1 seconds of music? 2. Consider a system that uses 8-bit ASCII codes to encode letters. How long (in microseconds) will it take to transmit the bit sequence encoding Hello-World! if we use a bit time of 4 samples per bit, and transmit samples at a rate of 1MHz? 3. The ASCII table below gives the ASCII codes for common alphanumeric characters and symbols listed from MSB to LSB. What is the bit sequence encoding the message 113? Assume that we transmit the codes of each character in sequence with the LSB first.The binary number 1001 converts to the decimal number 9, with the 0th (zeroth) bit on the right representing 1 and the 3rd bit representing 8. If you're converting the decimal number 33 to binary, what is the highest numbered bit (counting from the 0th bit on the right) that will be set? a. 0th b. 1st c. 2nd d. 5th e. 6thWhat bit patterns are represented by the following hexadecimal patterns? a. 0x5FD97 b. 0x610A c. 0xABCD d. 0x0100

