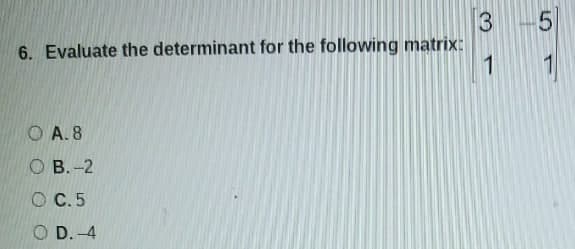
3 6. Evaluate the determinant for the following matrix: 1 O A. 8 ОВ. -2 O C. 5 O D. -4 LO
Q: The word "API" refers to a programming interface for applications. What does this mean in terms of…
A: API is a representation of hardware components on the software level, which is generated from a…
Q: What is the most vital component of computer hardware?
A: The most integral and important component of the computer hardware is CPU or the Central processing…
Q: Discuss, in some detail, the difference between "extends" and "implements" with respect to classes…
A: Ans: the difference between "extends" and "implements" with respect to classes and interfaces.…
Q: When should a network update be scheduled?
A: Introduction: Network: It is a group of computers that pool their resources and make them available…
Q: Given ?(?|?) , ?(?) ,and ?(?′|?) , solve the following a. Draw the probability tree for the main…
A: The answer to 1st question is given below. As per policy can answer three subparts at a time,…
Q: us ticket booking system using dart and run the program using java compiler need to have 1) 40…
A: It is defined as a high level, robust, object-oriented and secure programming language. It is known…
Q: K-number digits for variables, etc.) to compare the impacts of CISC-architecture, hardware-oriented…
A: Using the conceptual topics, develop sample codes (based on your own fictitious architectures, at…
Q: What happens if the stack grows too large?
A: Let us see what happens if the stack grows too large,
Q: What are some of the dangers to the safety of your data? Afterwards, we'll talk about how to avoid…
A: Define: A cyber or cybersecurity threat is an attempt to hurt, steal, or disrupt digital life in…
Q: What does database security entail? What are two ways to protect a database?
A: Explanation: Database protection: Data has become one of the most important aspects of our everyday…
Q: Create a "Functionality Requirement Analysis" document that educates technical personnel about the…
A: In the context of business intelligence (BI) and analytics, a data warehouse is a kind of data…
Q: The nodes represent places and number represent the distance between two places in miles. If you…
A: In the following step, the shortest distance travelled from E to a has been calculated and showed,…
Q: new_list =[10, 20, 30, 40] for i in range(len(new_list)): if new list[i] != new_list[-1]:…
A: The content of list is 10,20,30,40 Indexing starts from 0 len(new_list) = 4 since number of element…
Q: Construct a transition table and draw a transition graph for the sequential circuit shown in Figure.…
A: Transition Table Transition Graph
Q: Consider how computer technology may be utilised to benefit a variety of industries, including…
A: As per company guidelines we are suppose to answer only 1 question. Kindly re-post other questions…
Q: Determine the all the output waveforms for the 74HC195 when its input sigr are shown below CLK
A:
Q: B) 1-what are the suitable way to write the name of program by MATLAB? 2- What are the steps to…
A: What are the suitable way to write the name of program by MATLAB? What are the steps to create the…
Q: The characteristic equation for the recurrence relation , - Sa,-1- 6a,-2 is 2-5r+ 6 0 True False
A: Answer: True Note: Please go through the below image to understand the complete reason.
Q: (a) Consider a convolutional neural network (CNN) with the following structure for classification of…
A: In the below steps you can find the python to build cnn model using image dataset.
Q: (2) In asynchronous transmission, why do we keep the number of data bits between the start bit and…
A: The start and stop bits are used in asynchronous communication as a means of timing or synchronizing…
Q: You thuve to ereateaprogram in Clanguage in which the ser enters the mass tand length L of a…
A: Solution: C Program: #include <stdio.h> int main() { // Declare the variables float…
Q: Which of the following declare an array and initializes them some known values without an error?…
A: According to the rule of array declaration and array initialization Correct option will be char…
Q: In many aspects, ubiquitous computing varies from conventional desktop computing, which is also…
A: Given: Another word for ubiquitous computing is "pervasive computing."This study topic is about when…
Q: Components that are common to all forms of multimedia are essential. Distinguish between the…
A: Multimedia Components: Text, audio, graphics, video, and animation are all types of multimedia. With…
Q: What are the fundamental stages to troubleshooting a computer?
A: The introductory phrase: When evaluating a computer that is malfunctioning, we must follow…
Q: Which of the following is an instance created by the code given below? 0. class Employee: def _init…
A: class Employee: def _init_(self): self.id=0 self.name='ABC'…
Q: What will be the Inorder traversal of the following tree?* 11, 20, 29, 32, 41, 50, 65, 72,…
A: The answer of the question is given below.
Q: What is the output? def find sqrCa): t = a * a return t square = find_sqr(10) print(square) O 10 O…
A: The function name is find_sqr() which accepts a value and return it's square.
Q: PWM and PPM
A: Introduction The network basically defines a collection of devices that is in simple terms known as…
Q: Question 6 Which is the correct syntax for opening a file in Python? O (my_file…
A: The answer for the given question is as follows.
Q: Why aren't computer and mobile phone improvements like these recognised as adaptable?
A: Start: The inquiry is more subjective, and the response will be similar. Even if the technologies…
Q: This is because computers nowadays are so strong. What reasons have led to computers being so…
A: We must emphasize the importance of using computers in our educational system and why they are…
Q: Q1/Talk in detail about advantages of Semantic Analysis.
A: Your answer is given below in detail. Introduction :- A mathematical method for computer modelling…
Q: Multimedia relies heavily on standard building blocks. Multimedia may be utilised to develop an…
A: Elements of Multimedia: Textual Materials Text harkens back to the origins of the Internet as a…
Q: In a computer, why is the CPU the most vital component?
A: Reason The Central Processing Unit (CPU) is the most significant component of a computer system,…
Q: When surfing online, you get some strange data on an apparently secure website, and you realize you…
A: Introduction: A website is a collection of web pages, and related material recognized by a common…
Q: This is owing to the fact that computers are now very powerful. What causes have led to computers…
A: Answer to the given question During the 1980s and 1990s, wide-spread computer network…
Q: Write a function named ConvertC2F2C that accepts two parameters: a value of typ num that represents…
A: Answer :
Q: Consider baking a cake to be the same as running three loops on a computer in parallel. Find and…
A: Introduction: A loop is a programming structure in computer science that repeats a sequence of…
Q: What is Onion network?
A: Answer is given below:
Q: Computer Science create a simple app in javafx using GUI that saves data and can access the saved…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Before…
Q: Give an example of both open source and proprietary word processing and presentation software to…
A: Word Processing and Presentation Software: Word processing is used to enter and edit simple text,…
Q: It's hard to pinpoint exactly where Charles Babbage got the idea for the first computer.
A: Charles Babbage: The calculating engines created by the English scientist Charles Babbage…
Q: Show how hierarchical routing improves scalability and administrative autonomy. Distinguish between…
A: Introduction: In the previous section, "the network" was described as a collection of routers that…
Q: What can you tell me about the development of computers?
A: Answer
Q: (base) sebasjr@sebasjr-ubuntu:~/C/challenges$ ./a.out Please insert word1 and word2: a b False…
A: Answer is given below-
Q: What are the additional sorts of input devices that computers are equipped with?
A: Input Devices: Device for entering data noun. computing a peripheral device that takes data and…
Q: What does it mean "computer"?
A: A computer is an electronic device that updates information, or data. It has the potential to store,…
Q: Question 26 Which of the following statements is incorrect for python dictionaries? O dict) is a…
A: Answer:
Q: Which security measures should you implement in the event of an attack?
A: You should react to security risks as described below: Consider security important Create secure…
Step by step
Solved in 2 steps with 1 images

- Enter the 5 × 5 Hilbert matrix using MATLAB software 1 1/ 2 1/ 3 1/ 4 1/ 5 1/ 2 1/ 3 1/ 4 1/ 5 1/ 6 1/ 3 1/ 4 1/ 5 1/ 6 1/ 7 1/ 4 1/ 5 1/ 6 1/ 7 1/ 8 1/ 5 1/ 6 1/ 7 1/ 8 1/ 9 H i) Find the determinant of H. ii) Find the transpose and inverse of H iii) Using the commands in the text, find the dimensions of H, the column sums, and the row sums of H.True or False The inverse of a matrix M can be calculated in Python with the command Inverse=np.linalg.inv(M)Draw the following graph as represented in the adjacency matrix below. a b c d A 1 1 1 0 B 0 1 1 0 C 0 0 1 1 d 0 0 0 1
- Replace the first row of matrix Y to vector b , b=[4 6 8 10]Replace the second column of * matrix Y to vector b, b=[4 68 10]— lupdlipanpmtisie et tmts e R 5 A, ) B S S S et Given a 2-D square matrix: B mati31l31-{11, 2 3} 14 5 6}, (7,8,9}}. Write a function transpose which varts the matrix mat into its ftranspose 3np}ae t the transpose, IN C++ language.
- I do not understand this expression. so is c[i][j] += a[i][h] * b[h][j] mean c[i][j] = a[i][h] * b[h][j] + c[i][j]?? ; We do not know about the + matrix c right?Linear Equation SystemLU Decomposition Method AlgorithmDecomposition phase The LU Decomposition (Doolittle) method has the following properties: The U matrix is identical to the upper triangular matrix resulting from the Gaussian Elimination;The elements at the bottom below the main diagonal of the matrix L are the multipliers used during the Gaussian Elimination, that is, Li*j is the multiplier that eliminated Ai*j.It is common practice to store the multipliers at the bottom of the coefficient matrix, replacing the coefficients as they are eliminated (Li*j replacing Ai*j) The diagonal elements of L do not need to be stored, as their values are understood to be unitary. The final form of the coefficient matrix would be the mixture of L and U: The initial part of the LU Decomposition Method algorithm is identified with Gaussian Elimination, except that each λ multiplier is now stored in the lower triangular portion of matrix A: solve the system of linear equations followed by the…construct a Playfair matrix with the key "largest"
- Solving system of linear equations with two variables using Cramer’s rule. In mathematics the coefficientsof linear equations are represented in the form of matrices. A matrix is a two-dimensional array inprogramming. The steps of Cramer’s rule to solve the system of equations are:Step 1: Determining the coefficient matrix from linear equations e.g. a1x+b1y=d1a2x+b2y=d2Coefficient matrix: D = Step 2: Determining the constant column C = Step 3: Finding determinant |D| = (a1*b2) - (b1*a2) and checking if |D| is not equal to zero then do thefollowing: 1. Determining X-matrix: DX = The coefficients of the x−column are replaced by the constant column a1 b1a2 b2d1d2 d1 b1d2 b2 2. Determining Y-matrix: Dy = The coefficients of the Y−column are replaced by the constant column3. To solve for x: x=|DX|/|D|4. To solve for y: y=|Dy|/|D|Note that if |D|=0 then the matrix is singular and solving the system of equationis not possible. You’re required to automate all these steps by writing a program…Find Matrix Chain Multiplication for the following four matrices (M1, M2, M3, and M4) using dynamic programming Technique. Matrix M1 M2 M3 M4 Order of Matrix 5 x 4 4 x 3 3 x 5 5 x 6python Linear Equation SystemLU Decomposition Method AlgorithmDecomposition phase The LU Decomposition (Doolittle) method has the following properties: The U matrix is identical to the upper triangular matrix resulting from the Gaussian Elimination;The elements at the bottom below the main diagonal of the matrix L are the multipliers used during the Gaussian Elimination, that is, Li*j is the multiplier that eliminated Ai*j.It is common practice to store the multipliers at the bottom of the coefficient matrix, replacing the coefficients as they are eliminated (Li*j replacing Ai*j) The diagonal elements of L do not need to be stored, as their values are understood to be unitary. The final form of the coefficient matrix would be the mixture of L and U: The initial part of the LU Decomposition Method algorithm is identified with Gaussian Elimination, except that each λ multiplier is now stored in the lower triangular portion of matrix A: 1)solve the system of linear equations…

