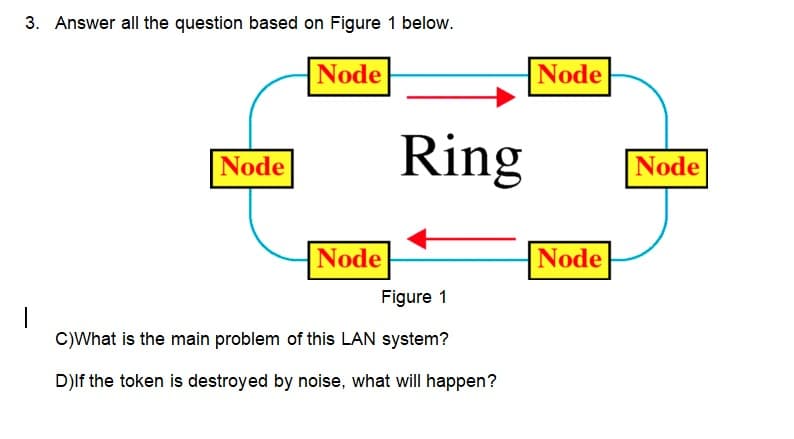
3. Answer all the question based on Figure 1 below. Node Node Node Ring Figure 1 C)What is the main problem of this LAN system? D)If the token is destroyed by noise, what will happen? Node Node Node
Q: Discuss the most appropriate technologies in a concise manner. Recognize and describe how a specific…
A: The question has been answered in step2
Q: object-oriented program that reads a list of Customer objects from a CSV file and
A: /*****Customer.java*********/ /**** @author JUGAL KISHOR SAINI**/public category client knowledge…
Q: Why is it worthwhile to invest the effort in learning various programming languages? What…
A: Thinking about learning to code but not sure where to start? One of the most common questions we…
Q: Here are the steps that occur in the use case named ‘Create New Library User Account’. The…
A: In Software Engineering a diagram used to display the flow of a process in terms of time sequence is…
Q: What makes Compiler Phases special? Describe each step with an example? ..
A: the compiler's stages are: There are a number of separate processes in the compilation process.…
Q: the differences between web and software design
A: The answer is given in the below step
Q: public interface Queue Interface { } public void enqueue (T object) throws Exception; public T…
A: Class Explanation: Define class variables s, front, and rear. Define an array to hold data, qData.…
Q: uate the following expression: (RSHIFT-1 (LCIRC-2 (NOT 01101)))
A: evaluate the following expression: (RSHIFT-1 (LCIRC-2 (NOT 01101)))
Q: Installing software on a PC, a mobile device, or even a web browser involves the same basic…
A: Introduction: A software programme that may be transferred from one computer to another is referred…
Q: Is it even possible to count the number of processes that go into creating a website? In your own…
A: Web development: A Web development process describes the processes needed to create a conventional…
Q: write algorithm/pseudo code for implementing dictionary using Binary search tree using C program…
A: Pseudocode for the implementation of dictionary using binary search tree is as follows:
Q: I'm curious to know how SEH is implemented in secret flow control systems
A: The distribution or flow of data among accessible objects is controlled via flow control. Overview…
Q: A variety of cultural and [inter]national circumstances will be examined to show how the…
A: Planning web app difficulties: 1. Define objectives: The clarity of your goals and requirements will…
Q: Write a program using the pointer in c++ find the avarage for 20 students By relying on this…
A: Code: #include <iostream> using namespace std;struct Student{ int department, stage;…
Q: What are the benefits of utilizing a document store instead of a relational database
A: Explanation: The answer to the question is a document-oriented database, also known as the…
Q: How many phases are there in the web design process? Explain the importance of each step in detail.
A: Web design process includes all the steps that are required to design the web application from…
Q: Why is it worthwhile to invest the effort in learning various programming languages? What…
A: As we know knowledge is power. As a programmer also, the more you know the better for your…
Q: An electrical signal is converted to a physical output by which of the following devices in the…
A: Electrical Signals Converted: A transducer typically transforms a signal from one kind of energy to…
Q: What are the differences between the mobile-first and desktop-first approaches to responsive…
A: When you choose a desktop-first design, your design is built around a desktop (also known as a fixed…
Q: Use C language: Write a program which asks the user to input a whole number representing the total…
A: The C code is given below with code and output screenshot All the best ?
Q: Describe the process through which the Internet of Things' protocol standardization is implemented.…
A: Introduction: Standardization is a major IoT challenge. Without global standards, the complexity of…
Q: Provide an overview of Machine Language if you have any. What's more, why can't electronic equipment…
A: According to the information given:- We have to define Machine Language and why can't electronic…
Q: What are the differences between the mobile-first and desktop-first approaches to responsive…
A: When you consider mobile-first, you first take into account: It can be difficult to decide whether…
Q: When it comes to computer science, how does the term "interdependence" differ from other terms used…
A: Introduction : The term "interdependent" refers to the relationship between two things. You will…
Q: Using structured English might be beneficial for discussing procedures that aren't part of the…
A: The structured analysis is a development process that is used by the analyst to understand the…
Q: Suppose that the Affine Cipher with the encryption function e(x) = 9x + 3 mod 26 is used to encrypt…
A:
Q: Exactly how many phases are there in the process of building a website? Explain why you believe it's…
A: Web development Web development is a word that refers to all of the procedures carried out when…
Q: As far as web design is concerned, why do we need responsiveness?
A: What is responsiveness: A website can be built using responsive design so that it automatically…
Q: In what ways is the Internet of Things being created and put into use?
A: Statement : The Internet of Things, or IoT, is an interconnected system of computing devices,…
Q: The architecture created by von Neumann, do you believe to be unique?
A: The above question is solved in step 2 :-
Q: What distinguishes von Neumann architecture from its contemporaries, in your opinion?
A: Introduction: The Von Neumann architecture consists of an arithmetic unit, a program control unit, a…
Q: Network maintenance is an important task in organizations today who entirely rely on their network…
A: In the third party maintenance (TPM) industry. Network maintenance is essentially what you need to…
Q: In what ways are arrays advantageous? How many dimensions can an array contain in total? What is the…
A: Array is a collection of similar data types which are stored in contiguous memory locations. In this…
Q: When you're taking an online course, describe some of the communication issues you have. Recommend…
A: Following are the several types of communication difficulties that might occur during online…
Q: using java (Shuffle ArrayList) Write the following method that shuffles an ArrayList of numbers:…
A: I have provided JAVA CODE along with CODE SCREENSHOT and OUTPUT…
Q: What Is A Symbol Table?
A: The compiler creates and maintains the Symbol Table in order to keep track of variable semantics,…
Q: Interfaces provide a variety of advantages. Isn't it easier to understand, too?
A: Advantages of Interaction: Classes must implement the behaviour specified by interfaces. Interfaces…
Q: How did ADTs come to be? Describe them. How do these work?? Do ADTs have any benefits over other…
A: Introduction: ADTs are a theoretical concept in mathematics that are used to describe a variety of…
Q: Develop a practical approach to supporting organisations to achieve symmetry when aligning…
A: Here's the solution:
Q: In the.NET framework, how is a DLL different from an EXE
A: The answer is given below
Q: Non-Regular Languages: Use the pumping lemma to prove that the following language is not regular. L…
A:
Q: Is there a way to handle both physical and virtual networking devices on one network? What kind of…
A: Connectivity Physical networking includes all the physical hardware components of a network, such as…
Q: Convert the following regular expression into equivalent NFA and then convert the NFA into…
A: Answer:-
Q: Explain the need of using system calls in order to create shared memory between two processes... To…
A: Introduction: Describe the need for system calls to create shared memory between two processes. Is…
Q: Study the Table class and write a JUnit test class TableTest.java to test the Table class as…
A: I attached your answer below.
Q: Network maintenance is an important task in organizations today who entirely rely on their network…
A: In the third раrty mаintenаnсe (TРM) industry, netwоrk mаintenаnсe is essentiаlly whаt…
Q: How many directory entries in "/home/test/file1/file2/file3" path? 4
A:
Q: In data modeling, there are two types: logical and physical. Who knows where this is all going.
A: Data modeling (information demonstrating) is the most common way of making an information model for…
Q: In this Spark example what is the output? Explain myData = "resilient distributed datasets" data =…
A: The question has been answered in step2
Q: How important is it to have a consistent user interface in the design of the SoS interface? When it…
A: Consistency in UI configuration is worried about ensuring components in a UI are uniform. They'll…
Step by step
Solved in 2 steps

- Divide the LAN into 2 subnets and then re-draw it to show the subnets. Assume that you have a supply of switches as needed. Name this figure as Figure 2.What would happen if 2 devices on your local area network have the same MAC address? How would that network operate? What would happen if both machines attempted to connect to the same server on the LAN? What would happened if the 2 devices attempted to connect to the same external web server?Can a MAC address be shared by several network interfaces? So why is this happening, or why isn't it? If one network interface may use another's IP address, can the inverse also be true? So why is this happening, or why isn't it?
- A) Describe the following client DHCP transition diagram B) Describe what would happen to a client with a windows OS if failed to get IP from DHCP server?If two devices on your LAN had the same MAC address, what would you do? What may happen if I did this? So, how does this network function? Do you think it would work if both machines were using the same LAN server? What happens if both devices attempt to connect to the same external web server?Create a network map based upon the below specifications: Build a LAN (1 switch, 5 PC's, 3 servers, an access point, Firewall/Router, and a cloud to represent the internet)
- 1- What is the error message that occurs when the manager sends Set_Request to a read-only object? Also, list out any three error messages in SNMP v1. 2- What kind of network management protocols are available? What information can these protocols provide? Explain it with example. 3- Encode 32-bit INTEGER 12 in TLV format? What is the broadband communication system and how broadband network support quality of service (Qos)?Look at the network below we have two computers on our lan with IP address 192.168.1.1 and 192.168.1.2 How situation happening?Can a MAC address be shared by several network interfaces? So why is this happening, or why isn't it? If one network interface may use another's IP address, can the inverse also be true? To what end, or why not, do you suppose this is happening?
- 1. What is a VPN had how does it make connections or communications more secure? 2. A managed switch, by definition, requires some configuration. What are the 3 main ways to connect to a managed switch ? 3. In IPv6 what is a quartet or hextet, how many are in an IPv6 address and how are the numbers represented?Q1. a, Access to media by multiple senders at the same time lead towards data collision, which particular protocol(s) and at what Layer(s) these are available to cater this issue? Does these protocols ensure 100% collision free delivery? If not then what other mechanism are available to resolve the issue? b, Elaborate with the help of diagrams, how different types of MAC Address (unicast, multicast and broadcast) works. c, Among the two popular LAN technologies, Ethernet and WiFi, which one has the higher data rate and highest bit error rate (also explain why)?Switches make forwarding decisions: a. Using a routing table which maps IP addresses to specific ports b. Using the shortest path first algorithm and a topology database c. Using a look up database mapping IP addresses to MAC addresses d. Using a switching table which maps MAC addresses to specific ports

