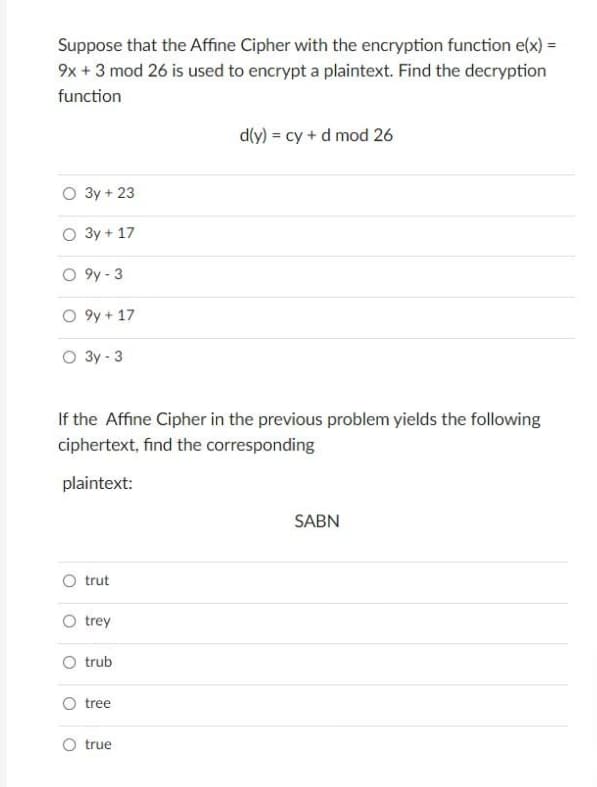
Suppose that the Affine Cipher with the encryption function e(x) = 9x + 3 mod 26 is used to encrypt a plaintext. Find the decryption function O 3y + 23 O 3y + 17 O9y-3 O 9y + 17 O 3y-3 d(y) = cy + d mod 26 If the Affine Cipher in the previous problem yields the following ciphertext, find the corresponding plaintext: SABN
Q: Why is it necessary for a systems analyst to be a translator? This might be the work of a variety of…
A: Introduction: A systems analyst must translate technical knowledge into language that non-technical…
Q: The characteristics that are inherently present in wireless networks give rise to a diverse set of…
A: The intrinsic characteristics of wireless networks produce a variety of obstacles.
Q: Let's say your child uses the school's wireless LAN to connect to the internet and types in…
A: The wireless local area network is the wireless distribution method for the two or more devices.…
Q: How important is the reflection vector when it comes to computer graphics? Expound on at least two…
A: Introduction: Vectorized reflection is used in computer graphics to simulate reflecting objects like…
Q: Explain how Excel can be used to design a database, including an example of a basic database layout…
A: The question has been answered in step2
Q: The characteristics that are inherently present in wireless networks give rise to a diverse set of…
A: The characteristics that are inherently: Present in wireless networks give rise to a variety of…
Q: Linux is the only operating system that has all of the concurrent methods that are currently being…
A: In the feild of software engineering, the word "concurrency" is used to refer to the strategies and…
Q: For what purpose does a firewall exist in the first place? At the present, I'm using software that…
A: Firewall A firewall is a security device - PC hardware or software - that can assist with…
Q: Explain the distinctions between open source and proprietary software by providing examples of both.…
A: Computer software Application software is a computer program that carries out specific academic,…
Q: 1. Write a program in a class EvensOddsAvg that counts the integers that are below the average. Read…
A: Here is the java code: The code working fine .See below steps for output.
Q: In order to gather hardware and software specs, use a request for proposal.
A: In order to gather hardware and software specs, use a request for proposal.
Q: A content management system's latency, security, availability, and migration may all be improved by…
A: security ,latency, content management system: Users of web content management systems lack…
Q: Find at least three firms that provide free or shareware CASE tools on the Internet. Let others know…
A: The answer is as below:
Q: Why is it worthwhile to invest the effort in learning various programming languages? What…
A: Thinking about learning to code but not sure where to start? One of the most common questions we…
Q: Using structured English might be beneficial for discussing procedures that aren't part of the…
A: The structured analysis is a development process that is used by the analyst to understand the…
Q: Some systems analysts don't think it's necessary to keep track of the source code. They say that by…
A:
Q: What exactly is the significance of Linux partitioning in relation to the operating system?
A: Creating and deleting partitions in Linux is a common practice because storage devices (such as hard…
Q: What algorithm is utilized to make web browser extensions or add-ons function?
A: Algorithm: An algorithm is a process used to carry out a calculation or solve a problem. In either…
Q: What is the difference between a class adapter and an object adapter? Do you think it's feasible to…
A: Introduction : The default modification of the adapter class every interface method; because we…
Q: Regardless of the browser used to access a web page, a cookie created with the statement:…
A: The question has been answered in step2
Q: Information Retrieval Given a query, how would you parse and dispatch sub-queries to the…
A: Complete answer for dispatch sub-queries to the various indexes:
Q: When adopting object-oriented design, everything is framed in terms of objects. Hot can a large (or…
A: It is defined as the involves defining the context of a system followed by designing the…
Q: puter operating systems, what are the most significant distinctions between those that function in…
A: Introduction: Real-time apps are intended to run on the real-time operating system (RTOS). Its…
Q: Vehicle Displacement You are given the velocity of a shuttle traveling in a straight line as a…
A: Below I have provided C++ Programming. Also, I have attached the screenshot of the code and output…
Q: Create two matrices called A and B of random integer in range (-100,100) with size (5,5). Then,
A: The code is given blew step:
Q: What does the word "memory void" refer to, and how is it defined? How is this even possible, and how…
A: Definition: A memory void is a mechanism for intentionally editing or cancelling unpleasant or…
Q: 9-Fully explain the following code and draw all possible outputs. var parser, xmlDoc; var text…
A: Given code: <!DOCTYPE html> <html> <body> <p…
Q: Q2/ write programme in C++ by using stack to push(insert) an alement 'J' between two elemwnts 'T'…
A: #include<iostream> #include<stack> using namespace std; void showstack(stack…
Q: int a int b = int tmp a = b; b = tmp; if (a < b) { = 5; } else { 12; = a; System.out.print (a +…
A: Java programming which refers to the object oriented programming languages that are used to create…
Q: Using Java (InputMismatchException) Write a program that prompts the user to read two integers and…
A: I have fixed issue please check it below code import java.util.InputMismatchException;import…
Q: Write EXACTLY what is printed by the code.
A: Code public class Main{ public static void main(String[] args) { int x=1; String res="";…
Q: Janet insists that the output for the following code should be y is 13. void tridec(int x) {x = 13;}…
A: Explanation: In order for the memory location to remain constant and any changes to the variable to…
Q: What are the advantages of an HTTP website versus a file system website? When it comes to…
A: Advantages of an HTTP website 1. Tending to HTTP utilizes progressed plan of tending to. It allots…
Q: User interface design requires a thorough understanding of mapping. Are there any specific mappings…
A: Introduction: A way to close the gap between a product's capabilities and the user or consumer…
Q: What JavaScript code belongs in the blank to create an object literal named shoes? let shoes = new…
A: In this question we have to select the correct option for the java script code to create the object…
Q: In a database for an airline, consider "snapshot isolation." The question is if a strategy that…
A: Serialization is a mechanism of converting the state of an object into a byte stream. The byte array…
Q: 2- Write a prolog program to take a nested list and return the number of elements in the list. For…
A: The answer for the above mentioned question is given in the following steps for your reference.
Q: Thomas wants to add a watermark to his spreadsheet and chooses a giant black plus sign. Assuming his…
A: Given that the spreadsheet is full of enough data to cover several pages and uses plain styling with…
Q: Look for methods to describe processes that aren't part of a systems analysis using Structured…
A: Given: The act of studying a procedure or business to discover its aim and purposes and build…
Q: Doing extra labor and code to prevent unnecessary class connections in object-oriented programming…
A: Here's the solution:
Q: The C++ standard library's "iterator" concept may be succinctly described.
A: Standard Template Library (STL) The Standard Template Library (STL) is a collection of C++ template…
Q: The answer to this question is a resounding yesan IT infrastructure problem at the company
A: Modern IT is becoming dominated by cloud computing. There has to be a wonderful cloud option for…
Q: What are some of the considerations that have to be made throughout the process of creating the…
A: The information system's software component includes: The information system, a group of components…
Q: Which factors, if any, contribute to the growth of the whole scope of the information repository…
A: Given: What factors contribute to the evolution of an information system's overall scope. The…
Q: Is there anything you're most concerned about while utilizing the internet?
A: The following are the primary problems associated with taking classes online: The best method to…
Q: Question 6: What is time complexity of fun()? 01 int fun(int n) { 02 int count = 0; for (int i = n;…
A: The question has been answered in step2
Q: In JavaScript and jQuery, what are events? Are there any examples of what you mean? What does it…
A: JavaScript and jQuery : The importance of JavaScript and jQuery events, event handling, and…
Q: Write a basic algorithm in Java that will use recursion to print out all the even elements in a…
A: All the elements in the stack which are divisible by 2 are printed in this code. pop is used to pop…
Q: //ToDo Add Comment const uint8_t BTN_PIN = 2; const uint8_t LED_PIN = 13; //ToDo Add Comment…
A:
Q: What do you do when you see strangers on social media pleading for money or medical help?
A: The question has been answered in step2
4
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- In order for the hash function (a * k)% M to yield separate values (no collisions) for the keys S E A R C H X M P L, a programme must be written to discover values of a and M, with M as little as feasible.A perfect hash function is the end result.Suppose that the size of the hash table is 101. Further suppose that certain keys with the indices 15, 101, 116, 0 and 217 are to be inserted in this order into an initially empty hash table. Using modular arithmetic, find the indices in the hash table if quadratic probing is used?Suppose you have a signature scheme S (which is correct and existentially unforgeable), and S can be used to sign any t-bit message. And you have a hash function H which outputs t bits and is collision-resistant. Consider a modified signature scheme S’ which can sign messages of unlimited length, where: S’.Sign(sk, m) = S.sign(sk, H(m)) Prove that this scheme is existentially unforgeable as long as S is existentially unforgeable and H is collision-resistant.
- Suppose Alice computes the Secret suffix MAC (page 322: secret suffix MAC(x) = h(x || key)) for the message ”AM” with key “G” that both Alice and Bob know. The hash function that is used is h(x1x2x3)= g(g(x1 XOR x2) XOR x3 ) where each xi is a character represented as 8 bits, and g(x) is a 8-bit string that is equal to the complement of bits in x. For example, g(10110011) = 01001100. The MAC is 8 bits. (8-bit ASCII representation of the characters is given below.) What is the Secret suffix MAC computed by Alice? Show the MAC as the single character. What information is sent by Alice to Bob.Q2. Determine the hash (in hexadecimal) of the message M using Davis-Meyer hash function. GIVEN MESSAGE IS DAB9 NOT AB12 PLEASE SHOW HOW TO DO THE PROBLEM USING DAB9• Block size = 8 bits• Hash size = 8 bits• Encryption function: Divide the key into two halves: LK and RK; Divide the plaintext into twohalves: LT and RT; Then ciphertext= LC||RC where LC=LK XOR RT; and RC = RK XOR LT;where LC, RC, LT, and RT are each 4 bits; Plaintext and ciphertext are each 8 bits.• g(H) = an 8-bit string that is equal to the complement of bits in H; For example, if H=A3 (Hexa)= 10100011 (binary); then g(H)= 01011100 • H0 = Initial hash = F4Use python to solve the below question. Let p = 71; q = 89; n = pq; e = 3. First find the corresponding private RSA key d. Then compute the signature on m1 = 5416, m2 = 2397, and m3 = m1m2 (mod n) using the basic RSA operation (without hashing of the message). Show that the third signature is equivalent to the product of the first two signatures.
- Can an AES key be shared secret encrypted? Justify your response Distinguish between hash and keyed hash See a real-world example of a one-keyed hash function.An affine cipher has the form c = (am+b) mod n. Suppose m is an integer between 0 and 25, eachinteger representing a letter.(a) Let n = 26, a = 3, and b = 123. What is the ciphertext corresponding to the phrase THIS IS A CIPHERMESSAGE.(b) A requirement for a cipher is that every plaintext letter correspond to a different ciphertext letter. If either aand b is not relatively prime to n, does the affine cipher meet this property? Either prove it does or presenta counterexample.Construct the Playfair matrix using the keyword SECRETKEY and then encrypt the message “thisisourfirsttest”. A) cl:fr:fr:mw:si:pb:es:cs:es B) cl:rf:rf:mw:si:pb:es:sc:es C) cl:fr:fr:mw:si:pb:es:sc:es D) cl:fr:fr:mw:si:pb:es:sc:se
- Suppose that Alice and Bob agree to hash an integer by taking the sum of the digits modulo 1212. Also suppose Alice has a public key with modulus 304891304891 and exponent 7373 and Bob has a private key given by the primes 619619 and 799799 with exponent 2323. Give the ciphertext Bob would send to sign the message 6005460054.Alice computes the Secret prefix MAC (page 322: secret prefix MAC(x) = h(key || x)) for the message ”GD” (in ASCII) with key “H” (in ASCII) that both Alice and Bob know. The hash function that is used is h(x1x2x3)= g(g(x1 XOR x2) XOR x3 ) where each xi is a character represented as 8 bits, and g(x) is a 8-bit string that is equal to the complement of bits in x. For example, g(10110011) = 01001100. The MAC is 8 bits. (8-bit ASCII representation of characters is available at https://www.asciitable.com/ Take the Hexa equivalent and convert it to 8 bits each. For example character "A" is hexa 41 or 0100 0001 in bits) What is the Secret prefix MAC computed by Alice? Show the MAC as the single character. What information is sent by Alice to Bob?Find the greatest common divisor of 26 and 5 using Euclidean algorithm. An encryption function is provided by an affine cipher ?:? → ?, ?(?) ≡ (5? + 8)??? 26, ? = {1,2, … , 26}Find the decryption key for the above affine cipher. Encrypt the message with the code 15and 19.

