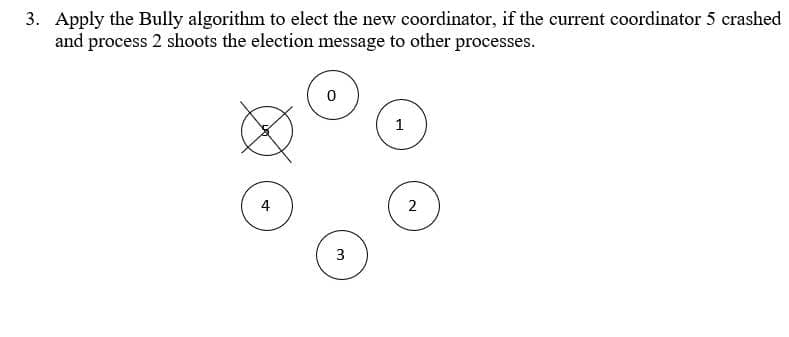
3. Apply the Bully algorithm to elect the new coordinator, if the current coordinator 5 crashed and process 2 shoots the election message to other processes. 4 3 1 2
Q: In what year did the first hand-held computer debut?
A: Computers on the Go: The first portable computer was the Osborne 1. It was first made available to…
Q: ✓ Allowed languages C Problem Statement Create a program that will print the nth row of Pascal's…
A: The program starts by including the stdio.h header file, which provides access to the standard input…
Q: You may want to think about describing the processes that are not covered by a systems analysis…
A: Structured analysis is a development method that allows the analyst to understand the system and its…
Q: Just what function does the northbridge integrated circuit on the motherboard serve? - Please…
A: Introduction The motherboard serves as the central hub for all network communications between a…
Q: Texas Hold em poker game 2 to 8 human or computer players Each player has a name and stack of…
A: Stack: Stack is a linear data structure that operates on the principle of Last-In-First-Out (LIFO).…
Q: What are database queries? How do they work?
A: A query can either be a request for data results from your database or for action on the data, or…
Q: In what ways would you recommend to your employees that they adapt to the many different kinds of…
A: Both of these questions are solved and explained below.
Q: Process control is a type of system calls Select one: True False Correct solution with explanation.
A: Process control is the system call that is used to direct the processes. Some process control…
Q: es RAM fit in? There are two types of groups listed below. Can it be used to save prog
A: Introduction: FB-DIMMs feature advanced memory buffer (AMB) chips to promote reliability, maintain…
Q: Like other distributed systems, managing concurrency in a distributed database is challenging. In…
A: Introduction: Simply simply, a database management system is a computerised data storage system. For…
Q: The term "bridge/joint table" describes exactly what it is. Is there another option? In what way is…
A: Introduction: We need to write what the bridge or connect is in the table, as well as what the…
Q: IDPS, or intrusion detection and prevention systems, are a subset of the larger field of computer…
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: The following are the variables that impact the Big-O performance of a hash table, listed from most…
A: The following are the key factors that determine a hash table's Big-O performance: INTRODUCTION : A…
Q: I'm trying to understand the Internet's architecture and was wondering what its different layers…
A: The Open Systems Interconnection model describes the seven layers that computer systems use to…
Q: When it comes to using computers and other technological tools, what are the benefits of having…
A: The amount of proficiency needed to effectively use computers and related technology is known as…
Q: Please elucidate User Datagram Protocol (UDP) for me
A: User Datagram Protocol (UDP) is a connectionless, unreliable transport-layer protocol used to…
Q: How many of your inquiries will get complete and correct responses? If such is the case, it is no…
A: An application-level protocol for distributed and collaborative hypermedia information systems is…
Q: Consider a hypothetical microprocessor generating a 16-bit address (e.g., assume the program counter…
A: In the question, the hypothetical microprocessor are given that generating a 16-bit address and…
Q: What is the Domain Name System (DNS), and how does it function? Please provide a detailed,…
A: A hierarchical, decentralised naming system for resources connected to the Internet or a private…
Q: Convert each ER into a relational schema mapping I attached the images
A: Entity-Relationship(ER) modeling is a technique used to represent the data in a database as entities…
Q: Compare and contrast RISC and CISC microprocessor architectures (complex instruction set computer).
A: RISC and CISC provide two different sets of instructions and computing procedures for computer…
Q: Concurrency control is a problem for distributed database systems, just as it is for other kinds of…
A: Introduction: Database management systems (DBMS) employ the technique of concurrency control to…
Q: Explain what "Domain Name Server" really is and how it works.
A: Answer: We need to write the what is the Domain Name Server So we will see in the more details…
Q: Methods for measuring empirical performance and its relationship to the more theoretical asymptotic…
A: In computer science and software engineering, it is often necessary to evaluate the performance of a…
Q: When it comes to using computers and other technological tools, what are the benefits of having…
A: Computer literacy Computer literacy alludes to a singular's capacity to really utilize computers…
Q: Communications protocols for the transport layer Complicating factors of modern network TCP and UPD…
A: INTRODUCTION: Communication protocols are structured definitions of the formats and rules for…
Q: One of the components of a composite primary key might be a candidate key. What would you do if you…
A: Composite primary key is a combination of multiple columns and these columns are used to identify…
Q: Windows tokens have two portions, which are Group of answer choices Accounts Identity Group…
A: Please refer to the following step for the complete solution to the problem above.
Q: Is the hard disk in a computer main or secondary storage? - Please explain your reasoning. - Explain…
A: INTRODUCTION: The primary storage type used in contemporary computers is the hard disc. As…
Q: Learn more about the distinctions between TCP and UDP.
A: The answer is given below step.
Q: How does it function, and what does it mean when people talk about HTTP?
A: Hypertext Transfer Protocol (HTTP) is a set of protocols for transferring files such as text,…
Q: Which are The basic steps in setting up an initial tableau?
A: Initial Tableau:- An initial tableau is a mathematical representation of the linear programming…
Q: We have a crude hash map where all values are concatenated into a single bucket (that is, they are…
A: In this question, a hash map is given where all the values are concatenated in form of a single…
Q: 6. For the showa device, determine the output for the inputs 0110 , \[ \$ 1=1, S 0=1 \text {, and…
A: 6. Solution : The correct answer for the given quest is option B, Zero. Explanation : As there is an…
Q: found at the transport layer, TCP and UDP. If you could elaborate on why an application would be…
A: Major difference is that TCP is connection oriented reliable transmission stream based with…
Q: Define a named tuple Player that describes an athlete on a sports team. Include the fields name,…
A:
Q: Sniffing the network and wiretapping are two common methods for identifying eavesdropping.
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: A. What is your Public and Privet IP address?
A: Answer: An IP (Internet Protocol) address is a unique numerical label assigned to every device…
Q: 5 often disregarded disadvantages of cloud computing.
A: Cloud computing is the delivery of computing services including servers, storage, databases,…
Q: Is there a way to summarize the differences between 2NF and 3NF and their more common usages?…
A: Introduction 2NF: This defines a first normal form relation without any non-prime characteristics…
Q: How does your organization identify vulnerabilities in its network infrastructure before they become…
A: Your organization can identify vulnerabilities in its network infrastructure by implementing the…
Q: Describe the different components that comprise a quantum computer and their respective functions.
A: Introduction : A quantum computer is a device that harnesses the power of quantum mechanics to…
Q: If given the chance, how would you answer these questions? When making backups and restoring them,…
A: Data backup: Data backup is the practise of copying data so that, in the event that we lose all of…
Q: Is the functionality of the Internet and the World Wide Web essentially distinct?
A: We must now talk about the differences between the Internet and the World Wide Web (WWW) Solution:…
Q: When it comes to the IoT, what are the many steps that make up the deep learning process?
A: The answer to the question is given below:
Q: Is there anything you can think of that exemplifies how far computers have come since the 1950s?
A: Answer: Since 1950 to 2021, computers have seen the most significant evolution. Earlier, they were…
Q: When would be the greatest moment to investigate queueing procedures?
A: When there is a Ranking systems which should be simplified mathematical models for explaining…
Q: How often do entirely satisfactory answers that address all aspects of the topic appear? In every…
A: Introduction: The Hypertext Transfer Protocol (HTTP) is a distributed, cooperative application…
Q: What are the primary distinctions between asynchronous, synchronous, and isochronous connections, as…
A: Asynchronous connections refer to a type of communication in which data is transmitted without a…
Q: What separates the Ubuntu Server Operating System from other server operating systems, and what are…
A: Ubuntu is a free and open-source software operating system that can be installed on personal…
Step by step
Solved in 2 steps

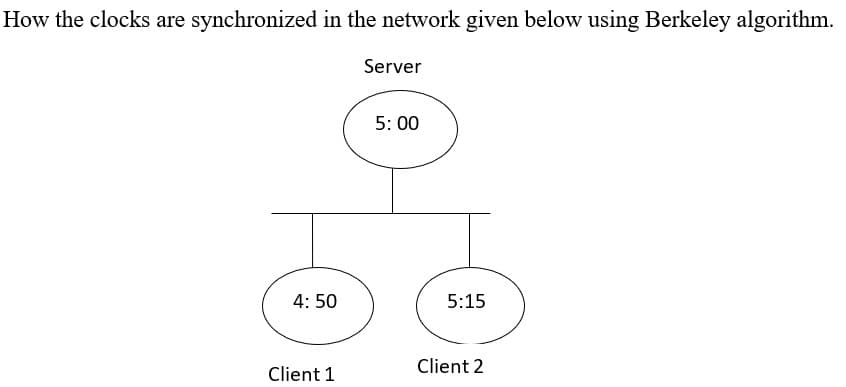
- The following frame should be transmitted over a given network (the frame is shown in hexadecimal): 7E DB DD 7E C0 7D DB DC FF C0. a) If the SLIP framing protocol is used; what are the bytes that are sent on the wire (after framing)? Show your workUsing the process of ANDing determine the network ID of the following addresses: a. 192.168.3.115 255.255.255.240 b. 172.16.230.15 255.255.224.0 – use a spreadsheet and show work to receive creditConsider a distributed system where every node has its physical clock and all physical clocks are perfectly synchronized. Develop an algorithm to record global state assuming the communication network is reliable.
- If you're talking about a private network, what is the address of that system? If a datagram is sent from a private network, is it conceivable for it to end up on the open Internet? Explanation?Is that so, or not? Consider a TCP connection where the most recent SampleRTT was 1 second. It is recommended that the TimeoutInterval be set to more than one second.Using vlsm, subnet the network 192.168.42.0/24, there are 3 departments, ensure there’s enough address to accommodate the needs of each department. Department A has 70 hosts, Department B has 50 and Department C has 28, find the subnet, first host, last host, Broadcast id and Mask
- Your task is to compute a session key in a DHKE protocol based on elliptic curves. Your private key is a = 6. You receive Bob’s public key B =( 5,9). The elliptic curve being used is defined by y^2 ≡x^3+x+6 mod 11. \ no hand writtenName the protocols that are assigned to the following ports: Port 21: ______ Port 25: ______ Port 80: ______ Port 110: ______The critical path of a network is the the shortest path (in time) from Start to Finish True False
- QUESTION 6 BGP is used to compute the shortest path in an Autonomous System (AS) True False 5 points QUESTION 7 Applications directly interacts with services provided from network layer. True False 5 points QUESTION 8 TCP provides a guarantee on the timing. True False 5 points QUESTION 9 UDP communications are secure by default. True False 5 points QUESTION 10 Http protocol is an example of stateful protocols True FalseAs another example, consider a circuit-switched network that connects computers in two remote offices of a private company. The offices are connected using a T-1 line leased from a communication service provider. There are two 4 × 8 (4 inputs and 8 outputs) switches in this network. For each switch, four output ports are folded into the input ports to allow communication between computers in the same office. Four other output ports allow communication between the two offices. Figure shows the situationA TCP connection is using a window size of 8,000 bytes and the previousacknowledgment number was 10,001. It receives a segment with acknowledgment number 12,001 and window size advertisement of 7,000 bytes. Draw a diagram to show the situation of the window before and after.

