3. Consider the problem of moving k knights from k starting squares S₁,..., Sk to k goal squares 9₁,..., 9k, on an unbounded chessboard, subject to the rule that no two knights can land on the same square at the same time. Each action consists of moving up to k knights simultaneously. We would like to complete the maneuver in the smallest number of actions. a. What is the maximum branching factor in this state space, expressed as a function of k? b. Suppose h, is an admissible heuristic for the problem of moving knight i to goal g; by itself. Which of the following heuristics are admissible for the k-knight problem? Of those, which is the best? • min{h₁,..., hk} max{h₁,..., hk) • Σ=1ht c. Repeat (b) for the case where you are allowed to move only one knight at a time.
3. Consider the problem of moving k knights from k starting squares S₁,..., Sk to k goal squares 9₁,..., 9k, on an unbounded chessboard, subject to the rule that no two knights can land on the same square at the same time. Each action consists of moving up to k knights simultaneously. We would like to complete the maneuver in the smallest number of actions. a. What is the maximum branching factor in this state space, expressed as a function of k? b. Suppose h, is an admissible heuristic for the problem of moving knight i to goal g; by itself. Which of the following heuristics are admissible for the k-knight problem? Of those, which is the best? • min{h₁,..., hk} max{h₁,..., hk) • Σ=1ht c. Repeat (b) for the case where you are allowed to move only one knight at a time.
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter14: Game Theory
Section14.3: Linear Programming And Zero-sum Games
Problem 9P
Related questions
Question
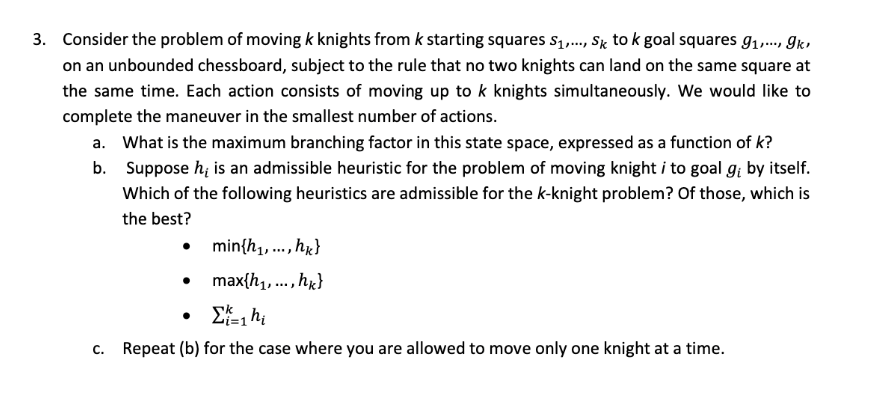
Transcribed Image Text:3. Consider the problem of moving k knights from k starting squares S₁,..., Sk to k goal squares 9₁,..., gk,
on an unbounded chessboard, subject to the rule that no two knights can land on the same square at
the same time. Each action consists of moving up to k knights simultaneously. We would like to
complete the maneuver in the smallest number of actions.
a. What is the maximum branching factor in this state space, expressed as a function of k?
b. Suppose h, is an admissible heuristic for the problem of moving knight i to goal gi by itself.
Which of the following heuristics are admissible for the k-knight problem? Of those, which is
the best?
min{h₁,..., hk}
max{h₁,..., hk}
Σ=1ht
c. Repeat (b) for the case where you are allowed to move only one knight at a time.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole