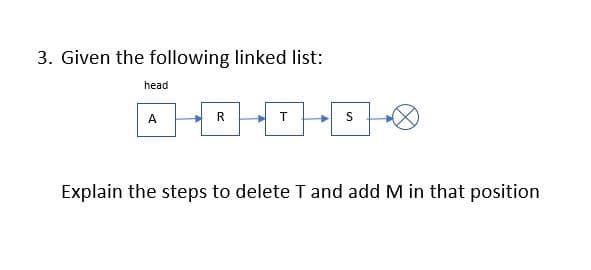
3. Given the following linked list: head A R T Explain the steps to delete T and add M in that position
Q: Say you have a table called Exercise with two fields: Type_of_Exercise and Calories_Burned. How woul...
A: Answer: MySql Query: create table Exercise( Type_of_Exercise varchar(50) not null, Calories_Bu...
Q: Explain various addressing modes available in computer organization with a neat example
A: The way of specifying the operand of an instruction is known as the addressing mode. A microprocesso...
Q: What is the most crucial piece of computer hardware in a personal computer?
A: Introduction: Computer Hardware and Software: A computer is a digital device made up...
Q: This is the default value for fields declared to "hold" object instances.
A: Here the question is related to the default value for fields declared to hold object instances.
Q: Excell Spreadsheet 1. If you have a list of numbers in cells B2 through B20 and you wanted the ave...
A: Introduction: The Excel AVERAGE function computes the average (arithmetic mean) of the data given. A...
Q: using python In a jupyter notebook, implement a recursive function anagrams() that computes anagram...
A: The answer is given below:-
Q: Big data has become a part of every organization's information technology systems in today's world.,...
A: like you doing utilizing big data at your own business or any work .some of the benefits are Using...
Q: s it possible to run a custom format script on Adobe acrobat pro (prepare forms tab) to temporarily ...
A: Adobe Acrobat pro is an OCR system. it is used to transform scanned files, PDF documents, and image ...
Q: ecture that has two sepa
A: It's a type of memory architecture that has two separate channels for each piece of memory.
Q: It's a type of memory architecture that has two separate channels for each piece of memory.
A: Computer Networks: Operating systems and other systems in computer science work together to provide ...
Q: When is it most appropriate to do a binary search?
A: 1) Binary Search is a searching algorithm used in a sorted array by repeatedly dividing the search i...
Q: In terms of system ideas, what does the phrase "interdependence" signify, and how does it compare to...
A: Introduction: Interdependence is described as being reliant on one another or just being dependent o...
Q: Who made the first flash drive?
A: Answer :
Q: I have the code bellow. Now I'm ask to display the number of elements in the arrays read from files...
A: #include <iostream>#include <fstream>using namespace std; class Multiplicity { //Class p...
Q: enter this task, ask the user for a word and then search for a file to see if that word is among the...
A: Importing modules Create file descriptor Initializing words array Initializing file reader Taking in...
Q: Write a C++ program to create a Postfix Expressions Calculator by using Stack
A: I give the code as per your requirement along with output and code screenshot
Q: Suppose you wish to store utility bills for a large number of users, where each bill is identified b...
A: The range query is the basic operation of the database. It displays the quantity in the certain as l...
Q: (b) p→~9
A: Lets see the solution.
Q: Write a C++ program to demonstrate the use of the scope resolution :: operator in the case of global...
A: Write a C++ program to demonstrate the use of the scope resolution :: operator in the case of global...
Q: number = input() while number!=id: print("This is not your ID number.") number = input() ...
A: Actually you can do without f strings too. Just put whatever you want to put after "...ID number:(he...
Q: what is host machine and machine controller in universal testing machine?
A: HOST MACHINE: A host machine is a virtual computer that is controlled and hosted by a cloud server ...
Q: GoldStar Bank is helping companies to do money transaction for their customers who holds their credi...
A: The solution is given below for the above given question:
Q: a * (b - c / d) + ++ Num2 where a, b, c and d are float type variables. b) Write a program that def...
A: The solutions for the given three scenarios is being explained in the below steps which is being imp...
Q: Enter an integer : 9 Enter an integer : 10 Enter an integer : 3 Enter an integer : 7 Sum is 22
A: Since you did not mention any language, i am coding in python.
Q: Python Question 3-1-2 1 point possible (graded) Which of the following will add the NumPy arrays x =...
A: The answer is given below.
Q: linear and differential cryptanalysis for each of these two, give some mathematical explanations abo...
A: Given two types of Cryptanalysis are Linear and differential cryptanalysis. Linear Cryptanalysis is...
Q: Is it possible to manage data better using dynamic memory allocations?
A: Dynamic memory allocation is a process of allocating the memory during the run time. It uses some fu...
Q: Which of the following is logically equivalent to (p ∧ q ∧ r) ∨ (p ∧ q ∧ ¬r) ∨ (p ∧ ¬q ∧ r) ∨ (p ∧ ...
A: Equation is (p ∧ q ∧ r) ∨ (p ∧ q ∧ ¬r) ∨ (p ∧ ¬q ∧ r) ∨ (p ∧ ¬q ∧ ¬r) ∨ (¬p ∧ ¬q ∧ r). We brake the ...
Q: Email me the answers to the following questions. If you are not familiar w look it up online.
A:
Q: Prove that x, where y is the domain of all real numbers, if x²(y² - 2y) is odd, then x and y are
A: A function f is termed as odd if the condition f (-x) = -f (x) holds. Whereas a number is odd if it ...
Q: What exactly is the function of a coax shield?
A: 1) Coaxial cable is a type of cable that has an inner conductor surrounded by an insulating layer, s...
Q: Subject - Data Communication Networks. Explain how CSMA/CD work Discuss the benefits and drawbacks ...
A: The above question that is work of csma/cd and drawback and benifits of TDM is answered below step ...
Q: public class Bicycle { public int cadence; private int gear; protected int speed; int id; public sta...
A: Hello student Greetings Hope you are doing great
Q: What language does the CPU speak?
A: the answer is given below:-
Q: Describe how functional dependencies may be used to denote the following: • The entity sets student ...
A: Functional dependency is a relationship that exists between two attributes. It typically exists betw...
Q: Use plot_surface to view the convolved images from part 2 in 3D part (2) my_filter=np.ones((15,15)...
A: import numpy as np import matplotlib.pyplot as plt from scipy import ndimage from mpl_toolkits impor...
Q: A multicore computer is a computer that has a lot of different parts.
A: > True A multicore computer is a computer that has lot of different parts
Q: codes that overload the applyBrake method. To better view the option, right-click the image and sele...
A: A class has many methods having same name but different in parameters, it is called as Method Overlo...
Q: one page on introduction of security
A: The quantity and aggregate of data recognizes the personal information that we portion or divide and...
Q: What is a default browser?
A: The answer is given below for the above given question:
Q: Create a class named Employee. The class must contain private member variables: name and salary. It ...
A: public class Employee{ //declaring instance variables as private private String name; priva...
Q: What are the most pressing email security issues?
A: Introduction: The most serious security problems concerning email communications security,
Q: The non-preemption of fair queues leads to a different transmission order than with bit round-robin ...
A: The non-preemption of fair queues leads to a different transmission order than with bit-by-bit round...
Q: A Smart Contract which locks up one cryptocurrency in return for a token, and Allows redemption A to...
A: What Is a Stablecoin? A stablecoin is a type of cryptocurrency whose value is tied to an outside ass...
Q: SELECT ALL of the valid statements that instantiate an object from the Bicycle class shown below
A: Valid statements are: cadence gear setCadence setGear
Q: Let f(n) and g(n) be asymptotically positive functions. Prove or disprove each of the following conj...
A:
Q: type of memory architecture
A: The type of memory architecture that has two separate channels for each piece of memory:
Q: The quality management plan documents how the project team will implement the quality policy. It mus...
A: For project execution, program management, and business operations, the "Plan-Do-Check-Act" cycle is...
Q: Create a function that takes the age in years and returns the age in days. Notes • Use 365 days as t...
A: We need to write a function that takes the age in years as input and return the age in days. We have...
Q: Is there a difference between a system subsystem and a logical division?
A: The subsystem is where work is processed on the system. A subsystem is a single, predefined operatin...
DATA STRUCTURES AND ALGORITHMS I
Step by step
Solved in 3 steps

- Write your own functions to create, insert nodes (both from the front and the end of the list), delete nodes, count the number of nodes, display all the nodes, display a specific node for the linked list. C++ and JavaCreate a function that takes the first Node in a linked list as an input, reverses the list (destructively), and then returns the original Node.int F(node<int>&p){int c=0; while(p!=0){p=p->next; c++; } return c;} This function is a. return the number of items in the linked list b. return the number of items in a linked list and destroy the linked list c. None of these d. destroy the list and free all allocated nodes
- Create a function that will perform the "Remove" operation of nodes in a Linked List.Assume the Doubly Linked List as follows, please write a code to deleted a data node from the list and show the result of each line of code in step-by-step mannerWhen we delete the last node from the non-empty linked list Select one: a. All of them b. The next of the previous pointer always points to the follow node c. Freeing the deleted node using follow pointer d. The head never be changed
- Use the standard linked list below to answer True/False statements 9-10: 9) The “head” pointer of this list is pointing to Node 4 10) If we called “insert(5)”, the new node’s “next” pointer will point to Node 8q6) Which of the following linked list can move only in one direction to access the data of the node? a. Single linked list b. Circular Double linked list c. None d. Double linked listTRUE or FALSE? Answer the following question and state the reason why: The delete operation only involves the removing of the node from the list without breaking the links created by the next node. You need an array to represent each node in a linked list. STL lists are also efficient at adding elements at their back because they have a built-in pointer to the last element in the list. A circular linked list has 2 node pointers. cout<<list.back()<<endl; = The back member function returns a reference to the last element in the list. In a Dynamic Stack, the pointer top stays at the head after a push operation. During a Pop operation in Static Stack, the elements are being moved one step up. In a dynamic implementation of stack, the pointer top has an initial value of null. In a dynamic stack, the node that was popped is deleted. In a dynamic stack, the pointer top stays at the head after push operation. STL function top returns a reference to element at the top of the…
- q9) In which of the following linked list there will be no beginning and ending? a. Depends on the Problem. b. Single Linked List. c. Double Linked List. d. Circular Linked List.C++ What is the output of following function for start pointing to first node of following linked list? 1->2->3->4->5->6 void fun(Node<ItemType>* start) { if(start == nullptr) return; cout << start->getItem() << " "; if(start->getNext() != nullptr ) fun(start->getNext()->getNext()); cout << start->getItem() << " ";} eof.Use the standard linked list below to answer True/False statements 9-12: 9) The “head” pointer of this list is pointing to Node 4 10) If we called “insert(5)”, the new node’s “next” pointer will point to Node 8 11) If we called “delete(10)”, Node 7’s “next” pointer will point to Node 8 12) If we called “search(20)”, the “head” pointer will be at Node 4 after the search function ends

