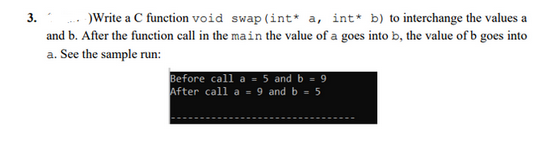
3. -)Write a C function void swap (int* a, int* b) to interchange the values a and b. After the function call in the main the value of a goes into b, the value of b goes into a. See the sample run: Before call a = 5 and b = 9 After call a = 9 and b = 5
Q: Assume you have a connection that includes restaurant names and their x, y coordinates. Assume that…
A: In the following case, the B-Tree index structure would be better, since the query is not a range…
Q: Are intrusion detection and prevention technologies still relevant in today's internet security…
A: An programmed called an intrusion detection system (IDS) is used to spot abnormal activities in…
Q: Please define the term a. data stripping and b. cylinder. b. Try to find some time
A: Data stripping is the process of separating data blocks and distributing data blocks to multiple…
Q: How is the evolution of outdated systems guaranteed?
A: Outdated Systems: Any piece of the hardware or software that was previously widely utilized but has…
Q: Define a class named Movie. Include private fields for the title, year, and name of the director.…
A: Below I have provided a C++ program for the given question. Also, I have attached a screenshot of…
Q: what is more important – precision or accuracy? State a real-life scenario where it shows the more…
A: Introduction: Accuracy: How closely a measurement resembles the actual/recognized value…
Q: Procedural programming and object-oriented programming are contrasted and compared. What character…
A: Basics:Object-oriented programming uses "objects" to store information and code: fields and methods.…
Q: (a) Write an 8085 assembly language program to solve the following equation. X=(PxQ) + (R x S)…
A: Below I have provided assambly language for the given question. Also, I have attached a screenshot…
Q: Write a recursive function maxArrayList (ArrayList Write a recursive function searchArrayList…
A: Here is the java program of above problem. See below step for code.
Q: Passwords to a certain system are required to have: at least one uppercase letter, at least one…
A: Below I have provided the java program also i have attached the screenshot of the code and output:
Q: What exactly are a computer's components, and how do you use them
A: Introduction: A computer is a programmable electrical device that receives unprocessed data as input…
Q: How is a data dictionary used? What is it? Can I still help you in any other way?
A: Answer: data dictionary is used as Data dictionaries are used to provide detailed information…
Q: What is a pointer variable? Next, what? It is a dynamic array. What's the thing with pointers and…
A: introduction: To put it simply, a pointer is an object in a programming language that is employed…
Q: Write a report outlining how the system could be improved to render decisions faster.
A: Four Simple Steps to Boost System Performance Remove Cache. Clear your cache sometimes, then restart…
Q: Describe a real-world CSP, the issue it addressed, and the results it had on the local and global…
A: Constraint fulfillment issues are mathematical problems that are described as a set of objects whose…
Q: How would you summarize the functions of each component in the kernel of a typical operating system?
A: What are the primary responsibilities of an operating system's core component, the kernel? The…
Q: A variable's "type" must be followed by "additional characteristics" in order to be fully defined.…
A: The term "variable" refers to a region in memory that may be utilised to hold a value. Variables…
Q: Write a program in C++ to calculate the actual maximum number of people on the subway at the same…
A: Here is the c++ code: See below step for code:
Q: 2. Vrite a function int number_of_divisibles (int a, int b, int* c) where *c will store the first…
A: Here is the c code: See below steps for code.
Q: What does the term "Abstract Data Type" (ADT) refer to? What are a few advantages of ADTs? How can…
A: Introduction: Type of Abstract Data A data type is defined by its behaviour from the perspective of…
Q: What distinguishes several threads from multiple processes? Could you kindly provide a brief…
A: Comparative Table: COMPARISON MULTIPROCESSING AND MULTITHREADING AS THE FOUNDATIONBy adding CPUs,…
Q: What is the difference between memory mapping in a microprocessor and memory- mapped I/O?
A: Memory Mapping is a method to expand the memory of the microprocessor. Microprocessors have a…
Q: 1.The use of computing for the encryption of information enabled the emergence of ciphers, where the…
A: (1) DES: The Data Encryption Standard is a symmetric-key calculation for the encryption of…
Q: Book ISBN title 2220000002 The Age of Innocence 5550000005 Lolita 9990000009 On the Road BookCopy…
A: A foreign key is a single column or group of columns that establishes a connection between two…
Q: You've deduced from your observations of the neighborhood minimart that it keeps its records on…
A: Please check the solution below
Q: 10 nano seconds clock cycles. It uses four cycles for ALU operations and branches
A: The answer is
Q: What's the quick response to "Data vs. Information"?
A: According to the information given:- We have to define the "Data vs. Information"
Q: Describe each of the following with an example: Surrogate primary keys are utilized in lieu of the…
A: Natural Key: A Natural key is a sort of unique key that is produced in a database by an attribute…
Q: Each of the three units—the control, arithmetic, and logic—serves a particular function.
A: Arithmetic: The term arithmetic is used to describe the fundamentals of counting, measuring, and…
Q: Does Data Cleaning in Computer Science Offer?
A: Data cleansing is a process in which incorrect, malformed, or disordered data is sorted and…
Q: Consider a hypothetical Python decision program called noOnSelf.py that takes a parameter P and…
A: Let's try proving yesOnSelf and noOnSelf
Q: Why is hashing passwords preferable to encrypting them when storing them in a file? ..
A: Let's discuss why hashing is considered as important while storing password in a file rather than…
Q: 1. Front-Running Detector Front-running is defined as trading a stock or another financial asset by…
A: Option (A) is correct. "Front running" is an illegal practice in which broker/specialists trade…
Q: 2. There are, by hypothesis, infinite number bases, but in computing we use hexadecimal, octal and…
A: The complete answer is below:
Q: Defineanomaly? Having three abnormalities in a database? Will you see the problems and provide a…
A: Abnormalities in a database can cause problems with data integrity and accuracy. To resolve these…
Q: Why is it feasible to combine computer gaming with wearable computing, such virtual reality?
A:
Q: 2. Write Grafstate code for a mapping Turing machine that computes the two's complement of a binary…
A: Solution in JFLAP below:
Q: An ethical hacker makes multiple guesses at the admin password for a local school's web-server but…
A: Below I have provided the solution of the given question:
Q: Explain how you could use a complete numerical representation table for a function to determine its…
A: TO do Finding the domain and range
Q: How would you summarize the functions of each component in the kernel of a typical operating system?
A: introduction: The kernel of a typical operating system must be listed, along with a brief sentence…
Q: Computer science vocabulary includes phrases like Data Dictionary and Contrast Repository
A: Introduction: A repository is simply a hub for the storage and upkeep of data. A Data Repository is…
Q: using visual studio and the C# please dont copy the previous answered questions because the solution…
A: Let's do the following First get the data from the file and push in to the array list then we check…
Q: Discuss the following subjects: i. Where does the thrashing come from? ii. How does the system…
A: Identifying Thrashing: Monitoring the frequency of page faults and CPU use may reveal this. The…
Q: Defineanomaly? How probable is it to find three abnormalities in a database? Exists a strategy for…
A: Database: A database anomaly is a flaw in a database that typically occurs as a result of bad design…
Q: What is the output of this code? int main(int argc, _TCHAR* argv[]) { char s1[] = "September 1";…
A: The strncmp() function take three parameters first the string 1, second string 2 and third the size.…
Q: The process model for RAD Software is rapid development of software applications. Application…
A: Definition: Prototyping and iterative models with no (or less) detailed preparation are the…
Q: Do Windows Services really exist, and if so, how do they work? Is creating a Windows Service…
A: Introduction: Services, which are an integral component of the Microsoft Windows operating system,…
Q: Explain in detail how this concert fits into an organization and why the top-down approach is better…
A: Introduction: The top-down technique picks sectors and industries to balance a portfolio. The…
Q: Describe the significance of firewalls as a key element of network security and cybersecurity. Make…
A: "Firewall" this term represents the security. In If we talking about in the computing language,…
Q: Comparisons between a parallel simulation environment and a fully integrated test facility are…
A: Test data is the auditor, which is sending fictitious data to the client's system in order to verify…
Step by step
Solved in 4 steps with 2 images

- 3. Using c++ Write a function that accepts an integer n and returns -1 if n is less than zero and the sum of all the integers between 0 and n (inclusive) if n is greater than or equal to zero.6. use c ++ to Write a function sumDigits, that accepts a positive integer n and returns the sum of the digits in that integer; thus, sumDigits(34) would return 7 (e.g., 3+4). Use the techniques from the roman numeral problem to extract the digits.3. Write the appropriate function definition for each of the following situations:b) Write a function that computes two sums from the elements of an array of integers. Each element of the array contributes to one of the two sums, depending on whether the element itself is even or odd. Your function definition should look like this:void sum(int x[ ]){ int n;int sum_even;int sum_odd;::}
- 7. Write a function password_check() that takes as input two stringsnewpassword and oldpassword, and that accepts the new password (i.e., returnsTrue) if newpassword is different from oldpassword and newpassword is atleast 6 letters long. If the new password fails the check, your functions should returnFalse.>>> password_check('E10-s2ff', 'E10.s2ff')True>>> password_check('E10sf', 'E10.s2ff')False>>> password_check('E10-s2ff', 'E10-s2ff')False(Extra Credit) For extra credit, extend your password function so that it also checks thatthe new password contains a digit.>>> password_check('E10-s2ff', 'E10.s2ff') True>>> password_check('Eej-sdff', 'E10.s2ff')FalseC Programming-Plz fix this code We can return multiple values from functions using pointers. Let's see an example. # include <stdio.h> void add Gr.marks (int * m) { *m = * m + 10; } void main ( ) { int marks; clrscr ( ); printf("enter actual marks:"); scanf(" % d", & marks); add Gr.marks (& marks); printf(" \n the graced marks is :\t % d", marks); }(a) Write the C++ function, operator+(const Matrix& b) const, which returns the matrix *this + b.
- Write overloaded function calculate() with following function definitions.void calculate(int x, int y ) – to calculate the sum of all even numbers from xtill y and print the sum .void calculate(char a,char n) – to print all vowels from variable a to n if anyvoid calculate(int x, int y, int z) – to print the middle number from x,y,z ifyou arrange them in ascending order.NEED CODING IN PYTHON OR JAVASCRIPT BUT NOT C++ consider an input string TAM of letters ‘A’, ‘M’, and ‘T’. This string, which is given by the user, ends with ‘#’. It should be stored in a table (or array), called TAMUK. The number of each of these letters is unknown. We have a function, called SWAP(TAM,i,j), which places the ith letter in the jth entry of string TAM and the jth letter in the ith entry of TAM. Note that SWAP(TAM,i,j) is defined for all integers i and j between 0 and length(TAM)–1, where length(TAM) is the number of letters of TAM. 1. Using our algorithmic language, write an algorithm, called Sort_TAM, which sorts the letters in the array TAMUK in a way that all T’s appear first, followed by all A’s, and followed by all M’s. The algorithm Sort_TAM should have one parameter: The array TAMUK. Also, your solution is correct only if the following four constraints are satisfied: - Constraint 1: Each letter (‘A’, ‘M’, or ‘T’) is evaluated only once. - Constraint 2: The…3. Write a function which will swap its arguments if the first argument is greater than its second argument, but will not interchange them if the first argument is smaller than or equal to the second argument. The function should return 1 if a swap was made, and 0 otherwise. (Hint: Make sure to use call by reference.) Write also a short test driver(i.e. a main() invoking your function).
- Functions- Write a C++ function that takes an integer argument, say n, and prints hello n times.3. Write the appropriate function definition for each of the following situations:a) Write a function that separately sums the even indexed elements and old indexed elements of an array of doubles. Each element of the array contributes to one of the two sums, depending on whether the index of the element is even or odd. Your function definition must have a heading like this:void sum(double b[ ]){ int n;double *sum_even;double *sum_odd;::}36- Consider the following function call: min(x, y) What is the function name and what is the first argument? a. The function name is min and the first argument is x b. Functions in Python don't have names (they're anonymous functions), but the first argument is x. c. The function name is min, but you need to see the function definition to determine the arguments. d. Functions in Python don't have names (they're anonymous functions) and you need to see the function definition to determine the arguments



