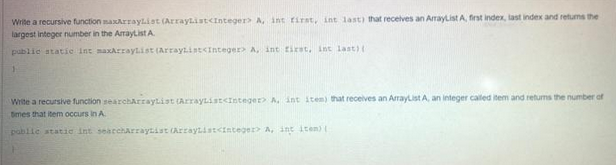
Write a recursive function maxArrayList (ArrayList Write a recursive function searchArrayList (ArrayList
Q: How and to what extent is physical security distinct from other forms of security? We must be aware…
A: Physical security is the protection of personnel, hardware, software, networks, and data from…
Q: The answer is just an option. I still don't know which one I should select
A: Nope. The answer is not just an option. This is NOT a multiple-choice question. There can be…
Q: How is it possible for a two-tier client-server architecture to have a fatal flaw? What is the…
A: Introduction: There are several types of architecture in the web application life cycle, including…
Q: An ethical hacker makes multiple guesses at the admin password for a local school's web-server but…
A: Below I have provided the solution of the given question:
Q: What options are there in computer science for maintaining data integrity?
A: Introduction: The data developer is in charge of including components that raise the reliability and…
Q: MATLAB has a number of data sets built in that can be used for testing purposes. One of these data…
A: The following is the MATLAB code for the above given problem : clc clear all close all format…
Q: Defineanomaly? Having three abnormalities in a database? Will you see the problems and provide a…
A: Abnormalities in a database can cause problems with data integrity and accuracy. To resolve these…
Q: What's the quick response to "Data vs. Information"?
A: According to the information given:- We have to define the "Data vs. Information"
Q: What are the various logical levels to take into account while creating a distributed client-server…
A: Introduction: The bulk of the resources and services that the client receives are hosted, provided,…
Q: There are various techniques to authenticate messages.
A: The techniques of message authentication are discussed into below step
Q: What is wrong with my code, why is my if statement not working Public Class Form1 Function…
A: The error is because the usage of the Mod operator is wrong. Mod operator required two operands for…
Q: a. Find the subnet mask b. How many valid hosts are created?
A: The answer is
Q: Which three graphical programs are most often used for data and process modeling?
A: Answer: Three graphical programs are most often used for data and process modeling? 1. Business…
Q: Think about the distinction between slotted and pure ALOHA under light loads. Which one is the…
A: Pure ALOHA: The data are always being transferred in pure ALOHA format. When there is just a little…
Q: Write a report outlining how the system could be improved to render decisions faster.
A: Four Simple Steps to Boost System Performance Remove Cache. Clear your cache sometimes, then restart…
Q: Construct a standard Turing machine that accepts the set of palin- dromes over {a,b}.
A:
Q: What traits distinguish NoSQL databases?
A: Given: Dear student we need to explain about , What traits distinguish NoSQL databases.
Q: What exactly does "logical addressing" mean
A: Answer is
Q: At least three of the most popular sensor types used in the Internet of Things should be included…
A: List of sensors found in Internet of Things devices: Infrared cameraTemperature gaugeVisual…
Q: What do you predict for artificial intelligence's future, given its past development?
A: Introduction: Practically every sector and person on the world will be affected by artificial…
Q: What characteristics does an operating system for a mobile phone have?
A: Introduction: Mobile operating systems execute apps on cell phones, tablets, and other devices (…
Q: What is the printout of the following code segment? void fun(int *a) { *a *= 2; } int main() {…
A: The complete answer is below:
Q: A set of integers are relatively prime to each other if there is no integer greater than 1 that…
A: If n is Prime then φ(n)=n-1 In then Given options Options A and E have n as Prime. So…
Q: Define parallel processing, often sometimes referred to as multiprocessing. concurrent processing…
A: Parallel computing explained: Multiple computer cores are used in parallel computing to tackle…
Q: IT security Compare these encryption products' CIA (Confidentiality, Integrity, Availability)…
A: The United States intelligence agency triad, often known as confidentiality, integrity, and…
Q: Each of the three units—the control, arithmetic, and logic—serves a particular function.
A: Central processing units (CPUs), also called processors, are the brains of computers, which process…
Q: What part, in your opinion, does the internet play in helping the disabled? What technological…
A: Web accessibility means making your website usable for people who might have barriers to accessing…
Q: The system's method for detecting incursions
A: An internal network is protected against unauthorised servers and networks using a firewall based on…
Q: Give a brief explanation of the main 6G disruptive technologies that, in your opinion, will help…
A: Intro The fifth-generation (5 G) cellular communication is replaced by the sixth-generation (6G)…
Q: Given a graph data structure: G= (K, R) where, { +, -, *, /, %, = } R= { (+,*), (=, %), (=,+),…
A:
Q: About AP's, analyze the following statements
A: This is very simple. Option I) is CORRECT. The reason is Stack Automata is simply a Finite…
Q: As a result of technological breakthroughs like the internet and social media, is society becoming…
A: Introduction: The Internet is the key technology of the information age, much as the electric motor…
Q: What make up a typical operating system's kernel components and how are they used?
A: Typical OS kernel components:- I/O Manager Cache Manager Object Manager Power Manager Virtual…
Q: In computer science, what do rollback and rollforward mean?
A: Moving Forward The roll forward capability is by default activated when a database, tablespace, or…
Q: Describe a real-world CSP, the issue it addressed, and the results it had on the local and global…
A: Constraint fulfillment issues are mathematical problems that are described as a set of objects whose…
Q: Call a Function conditionally on minus result (flag S=1)
A: The answer is
Q: Which three graphical programs are most often used for data and process modeling?
A: Explanation of the concept of Data and Process Modeling and the tools for it. Solution…
Q: What is the value of R3 after the execution of the following program if the value of "NUM"…
A: The following solution has been developed in a step-by-step manner. Given , "NUM" is…
Q: What are Windows Services, and how do they work?
A: Here in this question we have asked about Windows Services, and how they work?
Q: What is the general name for the AMD-created Hyper-Transport feature of CPUs? ?
A: Hyper-Transport: It is a technology that allows computer processors to be connected to one another.
Q: The CRC is nearly often placed in the trailer rather than the header by data connection protocols.…
A: answer is
Q: 1. Design a Turing machine that accepts the language L(aaaa*b*), where Σ = (a, b). 2. Design a…
A: All answers are below:
Q: What two types of data processing techniques are now used in contemporary systems?
A: Introduction: Any company cannot benefit from data in its raw form. Data processing is the process…
Q: What is covered by the Rand Report? What inspired its construction, if anything?
A: Introduction: Report from RAND Corporation: The conclusions of RAND publications are based on…
Q: What is the general name for the AMD-created Hyper-Transport feature of CPUs? ?
A: Answer: HT was AMD's bus for connecting multi-socket computer systems into a single coherent memory…
Q: It is an organized body of knowledge based on truths identified via investigation and close…
A: statement: Science is the methodical investigation of the nature and behavior of the material and…
Q: Data transformation may range from something as simple as a change in the format or representation…
A: Introduction: In a typical data integration scenario, the client queries the master server for…
Q: What substitutions are there for message authentication?
A: There are many techniques that can be alternative for message based authentication , Message based…
Q: How can write-ahead logging guarantee atomicity when a computer system malfunction is possible?
A: ATOMICITY IS PROTECTED BY LOGGING IN ADVANCE. Despite the potential for a computer system to…
Q: Which is a proper way to free the following dynamic array? double *sales = new double[ count ]; A.…
A: Explanation: In addition to dynamically assigning individual values, we can also dynamically…
Trending now
This is a popular solution!
Step by step
Solved in 6 steps with 4 images

- Write a recursive Java function displayOutIn that displays two items from an array list at one instance from out-to-in. until one or last two items displayed and the process stops. For example, given array A = {15, 74, 106, 10, 9, 86, 34} the displayOutIn function displays the following: 15, 34 74, 86 106, 9 10Write a recursive function that finds the minimum value in an ArrayList. Your function signature should be public static int findMinimum(ArrayList<Integer>) One way to think of finding a minimum recursively is to think “the minimum number is either the last element in the ArrayList, or the minimum value in the rest of the ArrayList”. For example, if you have the ArrayList [1, 3, 2, 567, 23, 45, 9], the minimum value in this ArrayList is either 9 or the minimum value in [1, 3, 2, 567, 23, 45] ================================================ import java.util.*; public class RecursiveMin{public static void main(String[] args){Scanner input = new Scanner(System.in);ArrayList<Integer> numbers = new ArrayList<Integer>();while (true){System.out.println("Please enter numbers. Enter -1 to quit: ");int number = input.nextInt();if (number == -1){break;}else {numbers.add(number);}} int minimum = findMinimum(numbers);System.out.println("Minimum: " + minimum);}public static int…Write a recursive function named reverseWithinBounds that has an argument that is an array of characters and two arguments that are bounds on array indices. The function should reverse the order of those entries in the array whose indices are between the two bounds (including the bounds). For example, if the array is: a[0] == 'A' a[1] == 'B' a[2] == 'C' a[3] == 'D' a[4] == 'E' and the bounds are 1 and 4, then after the function is run the array elements should be: a[0] == 'A' a[1] == 'E' a[2] == 'D' a[3] == 'C' a[4] == 'B' Embed the function in a program and test it. After you have fully debugged this function, define another function named reverseCstring that takes a single argument that is a C string and modifies the argument so that it is reversed. This function will include a call to the recursive definition you did for the first part of this project, and need not be recursive. Embed this second function in a program and test it.
- Write a recursive function named reverseWithinBounds that has an argument that is an array of characters and two arguments that are bounds on array indices. The function should reverse the order of those entries in the array whose indices are between the two bounds (including the bounds). For example, if the array is: a[0] == 'A' a[1] == 'B' a[2] == 'C' a[3] == 'D' a[4] == 'E' and the bounds are 1 and 4, then after the function is run the array elements should be: a[0] == 'A' a[1] == 'E' a[2] == 'D' a[3] == 'C' a[4] == 'B' Embed the function in a program and test it. After you have fully debugged this function, define another function named reverseCstring that takes a single argument that is a C string and modifies the argument so that it is reversed. This function will include a call to the recursive definition you did for the first part of this project, and need not be recursive. Embed this second function in a program and test it. Turn in only this final result (with output,…Implement a recursive C++ function which takes an integer array (A) and the starting (start) and ending(end) indices of that array, and returns the sum of all elements present in that array. The prototype ofyour function should be:int findSum (int* A, int start, int end)Write a RECURSIVE function, without using any loops, that prints the contents of a matrix with 3 columns. The function should take the matrix and the number of rows as arguments. void print_matrix(int arr[][3], int num_rows);
- Write a recursive function recursiveMinimum that takes an integer array, a starting subscript, and an ending subscript as arguments, and returns the smallest element of the array. The function should stop processing and return when the starting sub- script equals the ending subscript. c++In C language, implement two recursive versions of the linear search that gets an array of songs and a title and searches for a song with the given title in the array. 1. In this version the function returns the first index of the array containing the number. If the number is not in the array, the function returns -1. int linear_search_rec_first(int* ar, int length, int number); 2. In this version the function returns the last index of the array containing the number. If the number is not in the array, the function returns -1. int linear_search_rec_last(int* ar, int length, int number); Example of test for case 1: void test_q3() { int ar1[]={1,2,3,4,5,4,3,2,1}; if (linear_search_rec_first(ar1,9,2)==1) printf("Q3-1 ok\n"); else printf("Q3-1 ERROR\n"); } Example of test for case 2: void test_q3() { int ar1[]={1,2,3,4,5,4,3,2,1}; if (linear_search_rec_last(ar1,9,2) == 7) printf("Q3-3 ok\n"); else printf("Q3-3 ERROR\n"); }Write a recursive function that, given a sequence of comparable values, returns the count of elements where the current element is less than the following ( next ) element in the given sequence. See the examples given below. def count_ordered ( seq ) : """ Input : A sequence of comparable elements Output : The number of elements that are less than the following element in the sequence Example : >>> count_ordered ( [ 1 , 2 , 3 , 4 , 5 , 6 ] ) 5 >>> count_ordered ( ( 1 , 12, 7.3 , -2,4 ) ) 2 >>> count_ordered ( 'Python' ) 2 >>> count_ordered ( [ 6 ] ) 0 >>> count_ordered ( [ ] ) 0 """ In the first example above , count_ordered ( [ 1,2,3,4,5,6 ] )the returned answer is 5 because for all the first 5 numbers the current number is less than the next number. In the second example above, count_ordered ( ( 1,12,7.3 , -2,4 ) )the…
- Write an iterative function that determines the number of even elements in an array a of integers of size n. The function should return the number of elements that are even in array a of size n. Propose an appropriate prototype for your function and then write its code. Write a recursive function to solve the above problem. Propose an appropriate prototype for your function and then write its code.IN C Programing Let us define the weighted sum of an integer array a[0], a[1], a[2], …, a[n-1] be a[0]*1 + a[1]*2 + a[2]*3 + …+a[n-1]*n. For example, the weighted sum of the array [5,2,6] would be 5*1+2*2+6*3 = 27. Write a recursive function that takes in an array numbers and its length n, and returns its weighter sum. You can assume n is non-negative integer. int weightedSum(int numbers[], int n) {Implement a recursive C++ function which takes an array of integers (arr) and the starting (start) andending (end) indices of a portion (part) of this array, and returns the index of thelargest element present in that portion of array arr. The prototype of your function should be:int findLargest (int* arr, int start, int end) For example, the function call findLargest(arr,3,8)should determine and return the index of the largest element present in the array arr between the indices 3and 8 (both inclusive)

