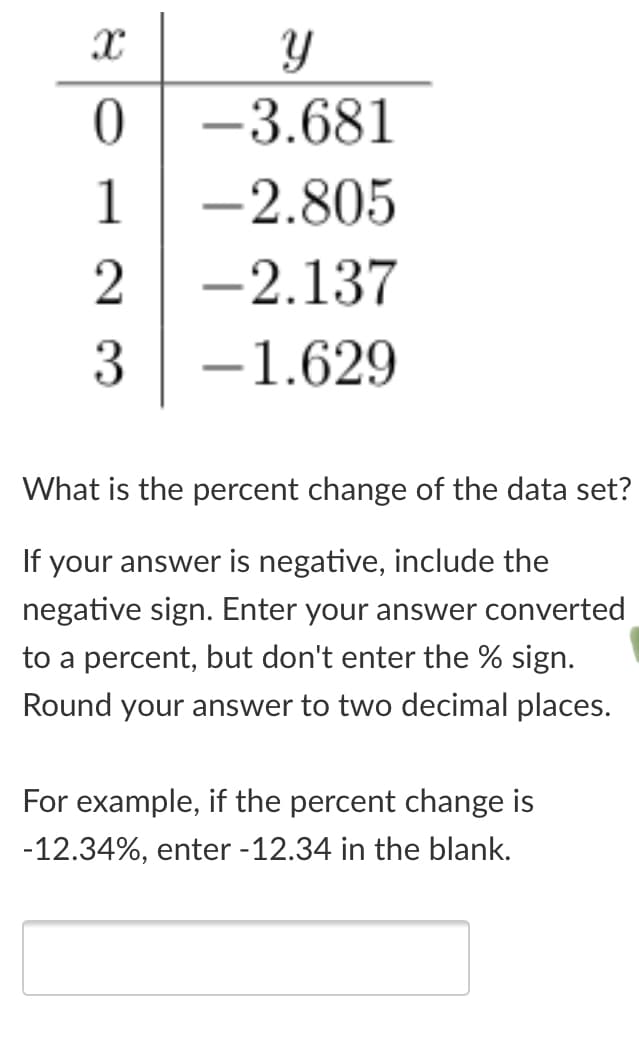
-3.681 1 -2.805 2 -2.137 3 -1.629 What is the percent change of the data set If your answer is negative, include the negative sign. Enter your answer converted to a percent, but don't enter the % sign. Round your answer to two decimal places. For example, if the percent change is -12.34%, enter -12.34 in the blank.
Q: L = {X₁#x₂#X3 | X₁, X2, X3 € {0, 1}*, and for some i and j € {1, 2, 3}, i ‡ j, xi
A: The answer is
Q: a) f(x) - x{x-2) (x-1)(x+1) b) f(x) =-(x-2) (x-(*+1) O f(x) = -x{x-1)(x+)(x-2) ) flx) - (1-x)}(x+1)…
A: (a.) f(x) = x(x-2)2(x-1)(x+1) (b.) f(x) = -x(x-2)2(x-1)(x+1) (c.) f(x) = -x(x-1)(x+1)(x-2)2…
Q: What character is missing from the following code? (Your answer should only be that one character)…
A: Comma missing after 60 mutate(flights_sml, gain = dep_delay - arr_delay, hours = air_time / 60,…
Q: g VRs: .00, 1.0
A: Step 1: Interpret the following VRs: .00, 1.00, .43.
Q: Find the value of A for the following: A=(5+2*3+((3–2)*7)+ -9)/2.
A: we need knowledge of BODMAS Bodmas stands for B-Brackets O-Orders (powers/indices or roots)…
Q: What is the value at out if: a=1001 b=1000 Cin = 0 S₁So= 00 O 1000 O 1001 0000 Undetermined. What…
A: The solution for the above given question is given below:
Q: In determining the error-detection/correction capacity of a code it is important to know how many…
A: (i) There are 6 different letters in the word MONDAY.Number of 4-letter words that can be formed…
Q: Q6/ What is the output of the following code? slose all: clear all; t=0:0.01:20; duty cycie-50; * -…
A: Answer: option(a) Continue Time Square Signal given code, let's run the code and see the output…
Q: If another code D is 3-error correcting, what can we deduce about its minimal distance? O The…
A: If another code D is 3-error correcting its minimal distance and about D's error detection capacity
Q: Read a 3 digit number N from keyboard and find individual digits in unit’s place (U), ten’s place…
A: Program code: #include <iostream>using namespace std; /* Function to get sum of digits */ //…
Q: Find the value of A for the following: A = (5 + 2* 3+ (( 3-2)* 7)+ -9) /2.
A: Division and Multiplication has almost same precedence Addition and Subtraction has almost same…
Q: Find the approximations Ln, R, Tụ and M, for n = 5, 10, and 20. Then compute the corresponding…
A: Question
Q: Q8/F(A,B,C,D)= Σm(0,2,5,8,10,13)+Σd(1,7,12,15) G(A,B,C,D)= [m(6,7,11,12)+Σd(0,2,3,8,13,15) Chose the…
A:
Q: is h admissible * 10 A B h-9 h-4 h-2 S h-7 h-0 2 D E h-5 h-3 O yes no
A: The given graph is:
Q: Q7/ If G(A,B,C,D)= AC'D'+ CD+ ABCD+ A'C Chose the correct answer G(A,B,C,D) = Em(2,3,6,7,8,11,12,15)…
A: Given G(A,B,C,D) = AC'D' +CD+ABCD+A'C G(A,B,C,D) = AC'D'+CD(1+AB)+A'C G(A,B,C,D) = AC'D'+CD+A'C…
Q: Use modus ponens or modus tollens to fill in the blanks If 1 − 0.99999 is less than every positive…
A: Before proceeding to the problem let us understand what the Modus Ponens rule is- p→qpq Modus ponens…
Q: an not use any control constructs such as if, do, while, for, switch, etc. /* * bitCount - returns…
A: We construct the methods tmax, minusTwo, bitCount and conditional as per the requirements of the…
Q: 1- How many mistakes are in the below solution? Q4/A/ This code below using to show the 3 waves like…
A: Q4/A Given code: x=1:0.025:11 y1=sin(4x) y2=cos(x+2*x) y=x+1 Plot(x,y1,'y',x,y2,'b',x,c,'r')…
Q: The essential prime implicants of the function below is/are: 00 01 11 10 wx 00 1 1 1 01 0 0 1 11 0 1…
A:
Q: Q8/F(A,B,C,D)= Σm(0,2,5,8,10,13)+Σd(1,7,12,15) G(A,B,C,D)= [m(6,7,11,12)+[d(0,2,3,8,13,15) Chose the…
A:
Q: Which of the following statements is true? -bit depth of 16 is sufficient to represent over 100,000…
A: Explanation: -bit depth of 16 is sufficient to represent over 100,000 magnitude levels in an…
Q: In cyclic redundancy checking, if g(x) =1011, d(x)= 0100, and the remainder to be 111, what is the…
A: In CRC first take the datapart d(x)= 0100. The datapart is append with the 0's where the number of…
Q: The opposite of (x >4 && x 11). True False
A: Whenever you do opposite of > it changes to < . Also AND changes to OR.
Q: CD+ ABCD+ A'C Chose the correct answer O G(A,B,C,D)= Em(2,3,6,7,8,11,12,15) O G(A,B,C,D)=…
A: Here in this multiple question we have given booean expression and we have asked to find minterm…
Q: In Figure 5, what is the value of F if A= '1',B='1' ,C='1'? 2x1 MUX So D' F 2x1 MUX D' So F 2x1 MUX…
A: Here we are using Multiplexer at different levels. Depending upon the value of select line, the…
Q: Which of the following is NOT true? Select one: When representing a π = 3.1415926... value in a…
A: Quantization (truncation) Converts infinite range of values to a finite one example: o 1/3 ~ 0.3333…
Q: Which of the following g(x) values guarantees that a single-bit error is caught? For each case, what…
A: The answer is in step 2
Q: time_t now=time(0); char*tm = ttime(&now); can you please explain this code? it is for c++. and…
A: time and ttime functions: The date and time of the current system time can be obtained in C programs…
Q: Can someone explain what each line of this Assenbly code does, and what you would put in place of…
A:
Q: If a is an unsigned integer variable whose value is hx6db7, what is the value of -a? A. h llhhhhl B.…
A: Solution: Option D: hx9248
Q: 4) For IEEE 754 single precision floating point numbers, what is the exponent of a denormalized…
A: you have posed various inquiries we will solve first for you. If you need us to tackle some other…
Q: Q8/F(A,B,C,D)= Em(0,2,5,8,10,13)+[d(1,7,12,15) G(A,B,C,D)= [m(6,7,11,12)+[d(0,2,3,8,13,15) Chose the…
A: Here in this question we have given two function with minterm. We have asked to find expression form…
Q: The 2’s compliment of the binary number (1101100)2 is: Select one: a. None of the given…
A: Que. The 2’s compliment of the binary number (1101100)2 is: Select one: a. None of the given…
Q: 1. Write the converse of the following: If you are happy, then you will sing. b) Convert (94A8)16 to…
A: The above question is solved in step 2:-
Q: which is transmitted over the channel. Let T(w) de
A: The answer is
Q: Which one of the following is not correct about RSA? a. RSA makes use of an expression with…
A: RSA scheme is developed by Rivest, Shamir and Adleman. In this it makes use of an expression with…
Q: 29 - When you consider the significant numbers, which one is the result of (1,500 x 2.0) +…
A: Given: 29 - When do you consider the significant numbers, which one is the result of (1,500 x…
Q: x:5, 15 and y: 10, 30 are given value What is the value of y for x=6 (use interpolation) A) 20…
A: To determine the value of y when x=6 using interpolation.
Q: Given the code Consider the following statements: (1) The code C can correct up to 1 bit error.…
A: The statement for the code c can correct up to 1 bit error and The minimum distance of code C is 3.
Q: F(A,B,C,D)= Σm(0,2,5,8,10,13)+[d(1,7,12,15) G(A,B,C,D)= [m(6,7,11,12)+Σd(0,2,3,8,13,15) Chose the…
A:
Q: In c++ What is the compression ratio if you use Huffman coding to compress the following term?…
A: Solution: Given, hippopotomonstrosesquippedaliophobia: it a s phobia where a person fears long…
Q: B-State the difference between those commands give an example of each one. choose (Five): 1-all(x),…
A: State the difference between the given commands.(any five): 1. all(x), any(x) 2. clc, clear 3.…
Q: Draw the ASK signal? Q2: write a Matlab code to simulate a ASK modulation signal only. A. generate…
A: Solution: ASK signal: Amplitude Shift Keying It is a type of Amplitude Modulation which represents…
Q: Write a MIPS program that asks the user to enter an unsigned number and read it. Then swap the bits…
A: The, code has given below:
Q: L = {w € {!,0}* | w = vw'v where v, w' e {!,D}*, \w'| = 2, and |v| = 3}
A:
Q: x:10, 18 and y: 32, 56 are given value What is the value of y for x=14 (use interpolation)…
A: Answer : - option E) 44
Q: 2-Give the full term of the following: RST, INTA, INTR
A: The Answer for the given question in step-2.
Q: q2) Choose the correct result of the following given code. m = (lambda x, y: x if x < y else y)…
A: Python lambda functions: Python lambda are anonymous functions that have the following syntax lambda…
Q: 23 - When you take into account the significant figures, which one of the followings is the correct…
A: Given: 23 When you take into account the significant figures, which one of the followings is the…
Q: In general, how many things can be represented by n bits?
A: A bit is generally a memory which can store a value either 0 or 1. In this way, each bit has the two…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- A B C D X1 a1 b1 c3 L X2 a2 b1 c1 L X3 a2 b2 c1 H X4 a2 b2 c2 H X5 a2 b1 c1 L X6 a2 b2 c1 H X7 a2 b1 c2 H X8 a1 b2 c2 L From the table above, assuming the min confidence is 35%, and minsup is 37%, which of the following rules are strong? a. a1 => c3 b. L => b1 c. a2, b2 => H d. a1, b1 => LA B C D X1 a1 b1 c3 L X2 a2 b1 c1 L X3 a2 b2 c1 H X4 a2 b2 c2 H X5 a2 b1 c1 L X6 a2 b2 c1 H X7 a2 b1 c2 H X8 a1 b2 c2 L Using the table above, calculate the following, there measures (1) support, (2) confidence, (3) all confidence. a) A1 ==> L b) A2, B2 ==> H c) A2, C2 ==> HThe following message arrived protected by the following CRC polynomial. Does the message have an error or not? Why? In the below table, show your work that allowed you to make the determination of whether an error exists in the message or not. Add rows and columns to the below table as necessary. M(x): 11010011100011 CRC-3-GSM: x3 + x + 1 CRC that was in the message: 011 X0 T(x) C(x) Remainder
- Choose the best answer :What is the Cardinality of the power set of the set { 0,1,2,4} ?a) 8b) 16c) 14If P(x) denotes x > 7 and Q(x) denotes x ≤ 7, where x is a real number then ∀ x, (P(x) V Q(x)) is Select one: True False Need perfect explanation Else leave to other expertH1. are any of these wrong?
- Answer asap !!!! Can not use any control constructs such as if, do, while, for, switch, etc. /* * bitCount - returns count of number of 1's in the bit pattern for x * Examples: bitCount(5) = 2, bitCount(7) = 3 * Legal ops: ! ~ & ^ | + << >> * Max ops: 40 * Rating: 4 */ int bitCount(int x) { return 2; } /* * conditional - same as x ? y : z * Example: conditional(2,4,5) = 4 * Legal ops: ! ~ & ^ | + << >> * Max ops: 16 * Rating: 2 */ int conditional(int x, int y, int z) { return 2; } /* * minusTwo - return a value of -2 * Legal ops: ! ~ & ^ | + << >> * Max ops: 2 * Rating: 10 */ int minusTwo(void) { return 2; } * TMax - return maximum two's complement integer * Legal ops: ! ~ & ^ | + << >> * Max ops: 6 * Rating: 10 */ int tmax(void) { return 2; }You are placing an order with an online retailer. To complete a purchase, your web browser sends a single encrypted, MAC-authenticated message to the web site, consisting only of the following information: a) your credit card information, b) the item number and quantity being ordered. a. Write a formula using the function symbol MAC(…) to indicate what is being authenticated. You may choose any reasonable variable names for the data items. b. Say an adversary is sitting between you and the retailer, with the ability to intercept traffic and send messages. Assume the authentication is not vulnerable to length extension. Describe a cryptographic attack the adversary could carry out to “max out” your credit card. What type of attack is this? c. What could the retailer do to prevent this attack, simply by changing what data is sent in that single encrypted, authenticated message? Write a new MAC() formula to show the new construction.Use chatbot GPT 3.5 and collect questions and answers for which GPT gives a wrong answer. Questions should be about data 101 such as basic R code, choice of plots, hypothesis testing and related tests, normal distribution.
- Suppose you have two columns, [Text1] and [Text2], in a MS Access table, how do you enforcethat only one of them can have a value?A) Apply the validation rule to either [Text1] or [Text2] column: ([Text1]="" And [text2]<>"") Or ([Text1]<>""And [text2]="" B) Apply the validation rule to either [Text1] or [Text2] column: ([Text1]="" And [text2]!="") Or ([Text1]!=""And [text2]="" C) Apply the validation rule to the table: [Text1] or [Text2] column: ([Text1]="" And [text2]!="") Or([Text1]!="" And [text2]="" D) Apply the validation rule to the table: ([Text1]="" And [text2]<>"") Or ([Text1]<>"" And [text2]="" E) none of the aboveWhat is the VALUE of tuple after executing the following codes? (hint: I know you will get an error as a result after executing the second line. But what is value saved in the tuple?) tuple =(1,2,'tommy')tuple[1]= 'tommy' Select one: a. (1,2,'tommy') b. (1, 'tommy','tommy') c. (1, 'tommy',2,'tommy') d. ('tommy',2,'tommy') Which of the following data mining methods can be used to predict the sale of a particular product? a. Market Basket Analysis b. Decision Tree Analysis c. K-means Cluster Analysis d. OLS Regression Which of the following database application is open source? Select one: a. Access b. DB2 c. SQL Server d. MySQLYou own a fruit shop. You buy fruit from suppliers by weight (cost per kg), and then you sell it either loose or pre-packaged for a fixed price. For example, a typical sale could be: 1. Apples Pink Lady 1.360kg x $3.50/kg = $4.76 2. Pears Golden 3.400kg x $1.75/kg = $5.95 3. Apples Green Smith 2.180kg x $2.50/kg = $5.45 4. Breakfast package 2x $5/pk = $10 5. Mandarins package 1x $3/pk = $3 -- Total $29.16 Where "Breakfast package" might consist of: a. Bananas Cavandish 500g b. Apples Green Smith 500g c. Mandarin Imperial 500g And "Mandarins package" is: a. Mandarins Imperial 600g b. Mandarins Queens 400g Question ----------- How can I create a relational database schema to record stock and sales? MYSQL

