4 2 7 1 3 5 8 6.
Q: Write a program that reads the height h and radius r of Right Circular Cone and finds the surface ar...
A: In this question, we are asked to create a java program to calculate the surface area and volume of ...
Q: Explain why planning and distributing a mass-market system release is costly.
A: Introduction
Q: Consider a project and map it both without and with architecture included. What effect it will have ...
A: Intro The matching of strategic needs with architectural choices is specified by software architect...
Q: What is the difference between redundancy and variety, and how do you explain t?
A: Introduction: When a position is no longer required, redundancy is a sort of dismissal. If your busi...
Q: Why is it necessary to create a virtual base class while using hybrid inheritance?
A: In the given question hybrid inheritance is a combination of more than one type of inheritance. Hybr...
Q: Give an example of how a full denial of service attack on a user (where the user receives no answer ...
A: Introduction A denial of service (DOS) assault on a computer is an example of a cyber-attack. By ...
Q: What are the advantages and disadvantages of employing thin clients in a university computer lab rat...
A: Introduction: Advantages of a laptop computer over a desktop computer: Laptop computers are very por...
Q: Explain why planning and distributing a mass-market system release is costly.
A: Introduction: The task of determining a path of action that will assist a group of agents in a given...
Q: 2. Write a method that calculates the tax on a price. The price and tax percentage should be doubles...
A: Hello student Greetings Hope you are doing great. As per our policy guidelines, in case of multiple ...
Q: Explain why distributed software systems are more difficult than centralised software systems, which...
A: Introduction: A distributed computer system is made up of several software components that operate o...
Q: In a nutshell, what are the four reasons why computer incidents have become more common?
A: Computer incidents are security incidents that may happen on either software or hardware components....
Q: 1- Show the output of the code. 2- Which method will you use to sort the elements in list, list1 an...
A: a) import java.util.*; public class Main { public static void main(String[] args) { List<...
Q: What is the definition of normalization in a database management system?
A: Normalization: - It is a technique in database architecture that decreases data redundancy and remov...
Q: Why is networking expertise required of a computer scientist?
A: The above question that is reason for networking expertise required of a computer scientist is answe...
Q: Define a real-time operating system with the help of examples. Describe how it differs from a standa...
A: Operating system is the system software and it is a interface between the system hardware and users....
Q: What exactly is the distinction between a homogeneous and heterogeneous relational database manageme...
A: Intro What is Relational Database: A relational database is a digital database based on E. F. Codd'...
Q: Where is the supertype of the object stored?
A: Introduction: description, examples, and explanation of the supertype entity in the data model
Q: What is the significance of defining exceptions in service engine
A: Introduction: Exception handling refers to how a programme responds to unusual circumstances. Softw...
Q: Define Exception Classes? what are the characteristics of these classes in a nutshell?
A: An exception is a run time error of the particular program.Exceptions Also provides the means to s...
Q: What is the distinction between SRAM and DRAM?
A: Introduction: Static Random Access Memory (SRAM): SRAM is a static memory that does not require inta...
Q: Create a website using HTML and CSS. Apply internal CSS. Minimum of 3 webpages.
A: Using HTML and CSS simple design of the webpages. Using anchor tags creating simple webpage like emp...
Q: What are the advantages of utilising a linked list instead of an array? When should a Linked List...
A: Intro 1) Dynamic Data Structure: A linked list is a dynamic data structure that can shrink and grow ...
Q: Show why it's frequently required to expand and adapt components for reuse, using the example of a c...
A: Here i explain about abstract data type like a stack or a list: =============================== Sta...
Q: Create the following table in your database with the following schema: Table: Products I Column Name...
A: Create table syntax : CREATE TABLE TABLE_NAME( column_name data_type, column_name data_type, ...
Q: In what circumstances do conventional files perform effectively for data storage? Computer scienc...
A: Introduction: For data storage, conventional files work well. File processing is less expensive and ...
Q: 1. Ask the user to enter any real number (i.e. a double) and output a. The number rounded to the nea...
A: In Java, we have Math.round() method which rounds the number to the nearest whole number. we have D...
Q: What impact has technology had on our ability to communicate?
A: Introduction: On the one hand, technology has an impact on communication since it makes it easier, f...
Q: what types of facilities use Application Based IDS?
A: Answer :
Q: What is an apg? What is a clg? What are the traits of a bastion host? Why do we need host-based fire...
A: Gateway on the circuit level: According to the OSI model, circuit-level gateways work as a "shim-lay...
Q: A Moving to the next question prevents changes to this answer. Question 1 When sorting 6, 2, 5, 4, 3...
A: By Insertion sort 6,2,5,4,3 first step: 2,6,5,4,3 IV Second Step: 2,5,6,4,3 I Third Step: 2,4,5,...
Q: 12. What is the decimal equivalent of this binary fraction 0.110011? 0.324521 0.546875 0.872343 0.79...
A: To calculate the decimal equivalent, we multiply each binary number before decimal(.) point with 2n...
Q: What exactly are the benefits of database encryption ?
A: Introduction: Everyone is concerned about the migration of private data to the cloud since many firm...
Q: What is the difference between redundancy and variety, and how do you explain it?
A: INTRODUCTION: The term redundancy can also refer to something extraneous or unnecessary. If you ope...
Q: What is the purpose of an algorithm analysis?
A: Intro Analysis of algorithm is the process of analyzing the problem-solving capability of the algor...
Q: 4. (Calory.java) Write a program that asks the user to enter the number of calories and fat grams in...
A: PROGRAM INTRODUCTION: Import the required libraries. Start the definition of the main function. Cre...
Q: How does the kernel communicate (deliver) a signal to a target process?
A: The answer is given below.
Q: or software failures in the hi
A: Software Failure When a user feels that the software is no longer delivering the desired outcome in...
Q: Isn't it true that various operating systems store disk folders at different track locations on the ...
A: Introduction: The system's file and directory management. Internally, the system uses nodes to keep ...
Q: Why is data encryption critical to your business or organization?
A: Introduction: Encryption is the process of altering data in such a manner that it is incomprehensibl...
Q: Demonstrate the prospects and benefits of a loT-based M2M solution by using a health band as an exam...
A: Demonstrate the prospects and benefits of a loT-based M2M solution by using a health band as an exam...
Q: What is the process of making an HTTP request?
A: Answer: HTTP request works mainly for transmitting the communication between the client and the serv...
Q: Explain why distributed software systems are more difficult than centralised software systems, which...
A: Let's see why distributed software system are more difficult than centralised software system
Q: Which of the following is correct code (compiles correctly and has the correct effect) for doing the...
A: Ans: The following code that is correct code for the following task : "Take an ArrayList of any elem...
Q: What does it mean to be a privileged individual?
A: In general, a privileged individual is one who enjoys a special right or advantage that most people ...
Q: What are three security measures that will help a company while reducing productivity?
A: Introduction: Low workplace productivity refers to a situation in which one or more employees accomp...
Q: 30. The eof character which is at the end of an input buffer is called Sentinel Pattern Lexeme O Tok...
A:
Q: Assume you work for a database company that caters to people and small enterprises. This company wan...
A: Introduction: The corporation wishes to quantify its software development so that measurements on it...
Q: How can a bus architecture manage multiple computers transmitting at once?
A: INTRODUCTION: A bus is a communication mechanism in computer architecture that transports data betw...
Q: this sql code is wrong ,can someone help me see whats the wrong with this code ? CREATE TABLE SAL...
A: The answer is given below.
Q: .globl "_*add_forty_two:Int32": .cfi_startproc pushq %rbp tmp1992: .cfi_def_cfa_offset 16 tmp1993: ....
A: Below the Assembly code which resolve the code
What are the black height (bh) and the height (h) of the node with key 7 in the following tree?
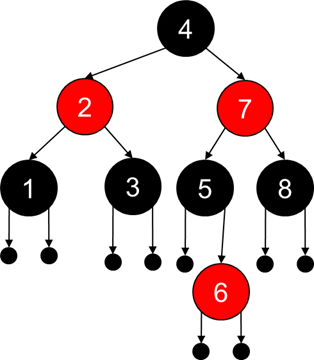
Step by step
Solved in 2 steps


