4. Based on the following image, the number of tables in the database is: A. One B. Two C. Three D. Four Ba New Meer All Access Obje Faldes HC External Data Datab For SAL Alax (New) S fo DYSUATION Ale 4 Dani The Teen T Fel Mohammad Nabil - Atentat AUT whic Σ ALAMED B fchen TARAN roseraiendem Membership, activation Co D 13 30 a 1079) 256-5001 12 1030 10) 281-4429 (072) k 520 6-1452 Ch Rapharn Seleit!
4. Based on the following image, the number of tables in the database is: A. One B. Two C. Three D. Four Ba New Meer All Access Obje Faldes HC External Data Datab For SAL Alax (New) S fo DYSUATION Ale 4 Dani The Teen T Fel Mohammad Nabil - Atentat AUT whic Σ ALAMED B fchen TARAN roseraiendem Membership, activation Co D 13 30 a 1079) 256-5001 12 1030 10) 281-4429 (072) k 520 6-1452 Ch Rapharn Seleit!
Fundamentals of Information Systems
8th Edition
ISBN:9781305082168
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter3: Database Systems And Applications
Section: Chapter Questions
Problem 3PSE
Related questions
Question
dbms
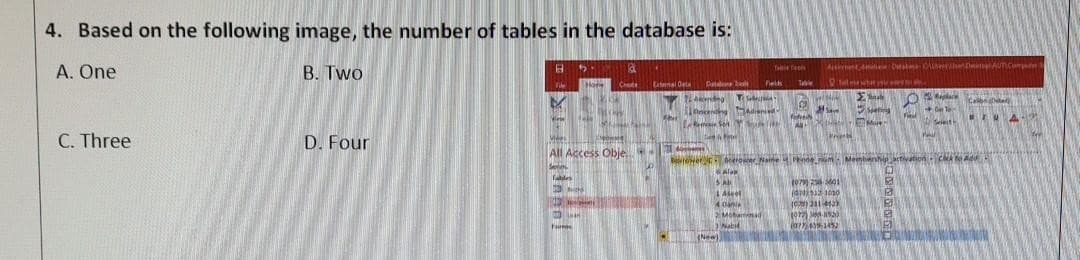
Transcribed Image Text:4. Based on the following image, the number of tables in the database is:
A. One
B. Two
C. Three
D. Four
B
Vide
M
Tablet
5.
Ha
Mies
All Access Obje
Seven
Mich
F
Form
3
Canal Deta
Abi
21 d
Table feels
Datbl Fields Ta
c
Ve
SAL
A
SHASTRA
(New)
4 Dani
2 Mohamad
Nabil
All
Actement de Catate: OlhereTo
Te
Σμαρ
#Save
Print
More
1079) 256-5001
(425121030
(0) 231-4429
1072) 8530
(077) 439-1452
Boer Name inde Membership, activation Cack to Adu
Alam
O
E
E
016-
Seleith
Wall
Ca
UA
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning