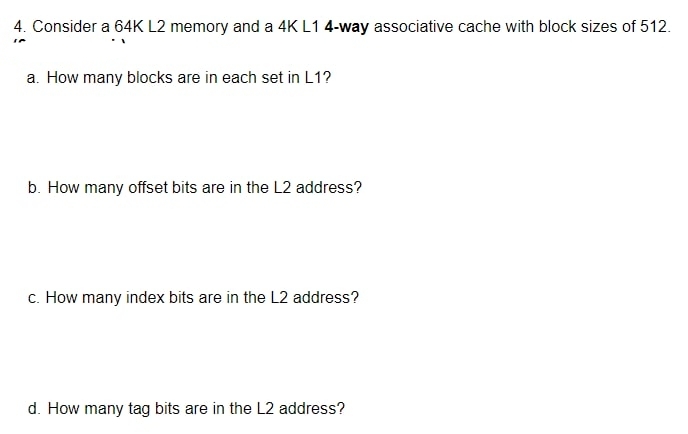
4. Consider a 64K L2 memory and a 4K L1 4-way associative cache with block sizes of 512. a. How many blocks are in each set in L1? b. How many offset bits are in the L2 address? c. How many index bits are in the L2 address?
Q: Agile development is characterized by its emphasis on rapid development and delivery of software sys...
A: Introduction: Pair programming is when two developers work together on a single computer, as the nam...
Q: Insert a statement in the while loop that will cause it to print all numbers except 400
A: num = 0while num <= 1000: num += 1 if num == 400: print(num)
Q: Examine the relationship that exists between information technology and automating processes. Why is...
A: Introduction: Businesses use information technology to automate many kinds of tasks, which can save ...
Q: What role does a pilot project play in the analysis of information systems? Why do you think Petrie'...
A: The answer is given in the below step
Q: Write a Java program that searches an array of 10 million randomly generated id numbers using the bi...
A: INTRODUCTION: Java program. Using the binary search.
Q: How will a doctorate degree set you up for success in a brand-new career?
A: Please find the answer and detailed explanation in the following steps.
Q: Write a program that reads the marks of a student in the test (te), midterm (mid), assignment (assig...
A: Since no programming language is mentioned, I am using python. Program: print("Enter test, mid, assi...
Q: What is the definition of the word data leakage?
A: Answer :
Q: What are the Linux Virtual Memory Areas and how do they work?
A: Introduction: Linux offers virtual memory, which entails utilizing a disc as a RAM extension to incr...
Q: In what way does system reserved memory serve a purpose?
A: Given: We have to discuss In what way does system reserved memory serve a purpose.
Q: To sort an array of N elements, how many passes does insertion sort goes through? Choose an answer ...
A: To sort an array of N elements, how many passes does insertion sort goes through?
Q: Assume the following JavaScript program was interpreted using static-scoping rules. What value of x ...
A: The answer is given in the below step
Q: A Locker can be opened by A and B when they are both there, as the locker has two keys, one of which...
A: Given: A locker can be opened by A and B when they are both there, as locker has two keys , one o...
Q: Explain what the following R code does. 1 sales_grouped <- group_by (house_data, suburb, sale_month)...
A: We need to explain, what the given R code does.
Q: What role does a pilot project play in the analysis of information systems? Why do you think Petrie'...
A: Pilot Project : Small-scale tests of a new technology, invention, or concept are called pilot projec...
Q: 0012012116 OA01503116
A: In this, we are going to add two hexadecimal numbers using 2's complement method. In 2's complement ...
Q: Consider a 64K L2 memory and a 4K L1 2-way associative cache with block sizes of 512. a. How many ...
A: Given, size of L2 = 64K and size of L1 = 4K associativity = 4 - way and , block size = 512
Q: Given a variable x of type double. Which one is a valid statement to compute the half of x?
A: All of the above is the correct option a) x*=0.5 => This is multiply and assignment operator....
Q: Q.1 What is the shell, and what command would you use in Linux to edit, search, and replace text?
A: Introduction: To summarise: What is Shell? Which command is used in Linux to edit, search for, and r...
Q: Please copy and paste and use this code below. Please post out the complete code with comments and a...
A: The complete code with proper comments and output is attached in below steps
Q: A relational database's internal schema can be optimized for processing and storage. How so?
A: Introduction: The processing and storage efficiency of a relational database may be improved by cont...
Q: What are some of the most important physical security aspects that enterprises should take into cons...
A: Introduction: Physical security refers to security measures intended to prevent illegal access to bu...
Q: Simplify the digital logic circuit shown below.
A: Simplify equation will be: b'c' + a'b
Q: 4. What is the output of the following Java code? int mark[ ] = { 50,60,70,80}; mark[5 ] = 15; Syste...
A: The output is as follows: Exception in thread "main" java.lang.ArrayIndexOutOfBoundsException: 5
Q: Write a program that reads the marks of a student in the test (te), midterm (mid), assignment (assig...
A: HI THEREI AM ADDING ASNWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: What is the meaning of a relocatable object file?
A: To find meaning of relocatable object file.
Q: In most cases, two ISP installations at the same level of the hierarchy can communicate with one ano...
A: Explanation: There is no need to pay an intermediate ISP provider when two ISPs at the same hierarch...
Q: What exactly is a flowchart?
A: INTRODUCTION: FLOWCHART A flowchart is a representation of a process, system, or computer algorithm ...
Q: ARDUINO IDE list and state the function of the different Arduino programming commands.
A: Introduction: Arduino is a prototype platform based on an easy to use hardware and software. It con...
Q: What phrase do you use to describe the element of issue resolution that is judgemental or common sen...
A: Introduction: The phrase used to describe the judging or commonsense element of issue resolution i...
Q: What is the meaning of a relocatable object file?
A: Introduction: A relocatable object file is a file that contains parts of code and data. This file is...
Q: What happens if we permute the loops, which appears to be a little change?
A: Introduction: In the case of more than two loops being reordered, loop permutation (also known as lo...
Q: Distinguish between the architecture of a monolithic kernel and the structures of a microkernel appr...
A: EXPLANATION: Monolithic Kernel: This is an operating system architecture in which the kernel's space...
Q: What are the drawbacks of isolation?
A: Introduction: Military funds are being slashed: When a government adopts an isolationist position, i...
Q: What were the goals of the early Internet research? And what were the difficulties' final solutions?
A: Introduction: The use of Internet information, particularly free material on the World Wide Web, or ...
Q: (True/False): A function ending in W (such as WriteConsoleW) is intended for use with a wide (16-bit...
A: A function ending in W (such as WriteConsoleW) is intended for use with a wide (16-bit) character se...
Q: What is the meaning of a relocatable object file?
A: The answer of this question is as follows:
Q: For each of the following numbers, state the base in use; that is, what is p, q, r, s? 100001p ...
A: Below is the complete solution in detail for the given questions. Please take a look below.
Q: What is the best way to handle virtual memory using explicit memory mapping and function calls
A: Please refer below for your reference: Inorder to to handle virtual memory using explicit memory map...
Q: Describe the many types of data transformations that are required to prepare data for a data warehou...
A: Introduction: Describe the many types of data transformations required to prepare data for a data wa...
Q: 1) Write a PIC 24 assembly code that implements the following C code i = 0x1234; j = 0XDCBA; i+j; k ...
A: As per guidelines only 1st question is to be answered in case of multiple questions. For other quest...
Q: What is the motivation behind the corporate enterprise's desire to connect its employee computers to...
A: Introduction: The corporation wants to connect its staff computers to a computer network, and many n...
Q: Write a function that counts the number of times a given integer occurs in a Linked List.
A: A linked list is a sequence of data structures, which are connected together via links.
Q: Explain the concept of throughput and techniques by which throughput is increased.
A: Throughput is a proportion of the number of units of data a framework can process in a given measure...
Q: Explain the term "Software Engineering" in your own words and using your own understanding.
A: Software engineering is a detailed study of engineering to the design, development and maintenance o...
Q: Describe the elements for project failure and what are the stakeholders for the project
A: Elements for Project Failure : 1. Goals that are unclear or changingEach venture should have a parti...
Q: Design ER diagram (database) for blog aplication. note: not html or php ER diagram (database) must c...
A: Here we have given an ER diagram based on the admin and user view. you can find it in step 2.
Q: What are some of the most important physical security aspects that enterprises should take into cons...
A: Introduction: Protect physical activities and occurrences that might cause major loss or harm to a c...
Q: What occurs when a load instruction reads the byte at address 0x03d4 on the CPU?
A: Introduction: Byte addressability, which highlights the fundamental distinction between memory and s...
Q: a. vọid b. $my_num c. 123friend d. student 1) Which one is a valid variable identifier?
A: Identifier is sometimes refered as variable names. There are rules to declare a identifier. 1) it ...
Step by step
Solved in 4 steps with 3 images

- Consider a 128-word L2 memory and a 16-word direct mapped L1 cache.a. How many bits are in the address of the L2 memory?b. How many index bits are in the L1 address?c. How many tag bits are in the L1 address?d. How many words from the L2 memory will map to the same word in L1?Suppose a computer using direct mapped cache has 4G Bytes of main memory and a cache of 256 Blocks, where each cache Block has 16 Words, and Word Size is 4 Bytes. a)How many blocks of main memory? b)What is the format of a memory address as seen by the cache (Tag, Block and Word fields)? c)To which cache block will the memory reference 0000146A in Hex?Find the total bits required for given data size and calculate overhead in percentage: - How many total bits are required for a direct-mapped cache with 8KB of data and 4-word blocks, assuming a 32-bit address?
- A computer using direct mapping cache has 256Mbytes of byte addressable main memory and cache size of 32k lines and each cache block contain 8 bytes. How many blocks of main memory are there?What are the size of the tag, line number and words?To which cache block will the memory address 13ADEF9H map?To which line number will the memory address 17FEAD8H map?A computer is using a fully associative cache and has 216 bytes of main memory (byte addressable) and a cache of 64 blocks, where each block contains 32 bytes. a. How many blocks of main memory are there? b. What will be the sizes of the tag, index, and byte offset fields? c. To which cache set will the memory address 0xF8C9(hexadecimal) map?Suppose we have a byte-addressable computer using direct mapping with 16-bit main memory addresses and 32 blocks of cache. If each block contains 16 bytes. a. Determine the number of bits of the offset field. b. Determine the number of bits of the block (or slot) field. c. Determine the number of bits of the tag field. d. To which cache block would the hexadecimal address 0x2468 map? e. What is the tag of the hexadecimal address 0x2468 f.To which cache block would the hexadecimal address 0x864A map? g. What is the tag of the hexadecimal address 0x864A?
- 1. For a direct-mapped cache design with a 32-bit address, the following bits of address are used to access the cache. Tag Index Offset 31-14 13-7 6-0 a. What is the cache block size (in words)? b. How many entries does this cache have? c. What is the ratio between total bits required for such a cache implementation over the data storage bits?Suppose a computer using set associative cache has 221 words of main memory and a cache of 64 blocks, where each cache block contains 4 words. a)If this cache is 2-way set associative, what is the format of a memory address as seen by the cache, that is, what are the sizes of the tag, set, and word fields? b)If this cache is 4-way set associative, what is the format of a memory address as seen by the cache?How many total bytes would be necessary for a 4-way set associative cache with 64 KBytes of data and one word blocks, assuming a 32-bit addressing used?. A 96 KBytes B 106 KBytes C 105 KBytes D 102 KBytes E 100 KBytes F 109 KBytes
- Suppose a computer using direct mapped cache has 4M byte of byte-addressable main memory, and a cache of 512 blocks, where each cache block contains 64 bytes. a) How many blocks of main memory are there? b) What is the format of a memory address as seen by the cache, i.e., what are the sizes of the tag, block, and offset fields? c) To which cache block will the memory address 0x00007266 map?Suppose a computer using fully associative cache has 4G bytes of byte-addressable main memory and a cache of 512 blocks, where each cache block contains 128 bytes. a) How many blocks of main memory are there? b) What is the format of a memory address as seen by the cache, i.e., what are the sizes of the tag and offset fields? c) To which cache block will the memory address 0x018072 map?Suppose we have a byte-addressable computer using direct mapping with 16-bit main memory addresses and 32 blocks of cache. If each block contains 8 bytes. a. Determine the number of bits of the tag field. b. To which cache block would the hexadecimal address 0x2468 map? c. What is the tag of the hexadecimal address 0x2468



