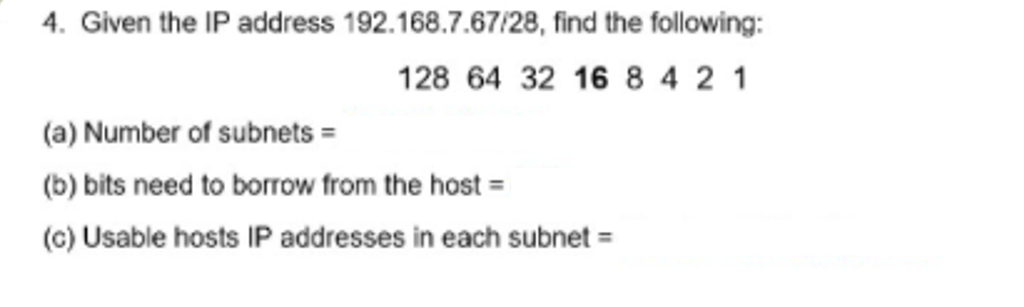
4. Given the IP address 192.168.7.67/28, find the following: 128 64 32 16 8 4 2 1 (a) Number of subnets = (b) bits need to borrow from the host = (c) Usable hosts IP addresses in each subnet
Q: What concerns and obstacles come from the usage of a disjointed data system?
A: Introduction: Computer failure and loss are significant challenges that lead to excessively high exp...
Q: interacted w
A: Instruction set The architecture of an instruction set is commonly referred to as an "instruction s...
Q: Java langauge
A: Given :- A car's mile per gallon can be calculated with the above given formula as, MPG = Miles driv...
Q: Prompt When you use WiFi at home to connect to the internet, you should know that all the internet-...
A: Proxy means ‘in place of’, representing’ or ‘in place of’ or ‘on behalf of’ are literal meanings of ...
Q: Which IP addressing technique subnets a subdivide to make smaller subnets?
A: Explanation: Technique for IP (Internet Protocol) addressingAs the IP address space grows, the subne...
Q: What does the following code display? ArrayList mylist mylist.add("XRAY"); mylist.add("YELLOW"); myl...
A: The given list is mylist. First XRAY will be added, then YELLOW, then ZING will be added to the lis...
Q: set is orthog
A: given - Justify why an instruction set is orthogonal by describing what it means in terms of symmetr...
Q: 5.7 Clone of LAB: Arrays: Output numbers in reverse
A: Note: Programming language is not mentioned so I am doing in Java In this question, we are asked to ...
Q: Which IP addressing technique subnets a subdivide to make smaller subnets?
A: Subnets are created from a larger set of ip to create networks for regional departments in a complet...
Q: Represent 5.75 in IEEE 745 Single Precesion using the Digital design of computer system by using nor...
A: 5.75 in binary form is: multiply the decimal number with the base raised to the power of decimals in...
Q: Decimal to Binary 1. 55 in decimal is ______ in binary. 2. 125 in decimal is ________in binary
A: The decimal representation is a number system representation that includes 10 digits from 0 to 9 had...
Q: Where does a transitory application save the current environment string's segment address?
A: Given
Q: Create a program that uses C language that solves the function below: f(x) = 3x = ex
A: C code for ex to show the value equal to f(x) #include <stdio.h> float exponential(int a, floa...
Q: Consider the function below written in Python3: def foo(a, b=[1]): if a <= 1: return b b_new = [b[i]...
A: SUMMARY: -Hence, we discussed all the points.
Q: olve the following recurrence by method of backwards substitution A(n)=2A(n-1)+1 for n>1 , with ...
A: Answer : The complexity will be n.
Q: 3. Let A = {1, 2, 3} and B = {4,5}. %3D a) Find A x B b) Find B x A
A: A = {1, 2, 3} B = {4, 5} A*B = {1, 2, 3} * {4, 5} A*B = {(1, 4), (1,5), (2, 4), (2,5), (3, 4),(3, 5...
Q: If the data were collected as a function of time at regular intervals, what operator should be used ...
A: If the data were collected as a function of time at regular intervals, what operator should be used ...
Q: Propose ideas for the following problems: 1) We have an array of integer numbers with the length of...
A: Iterate from 1 to N+1 Search for each of the value and if the element if not found in the given arra...
Q: Which of the following answers are part of a well-structured relational database? Select all that ap...
A: Separate tables or linked data make up a relational database. A relational database is a collection ...
Q: A local area network is a communications network that interconnects a variety of data communications...
A: Various terminologies used are : Interconnect Data communications devices Broadcast Data Data Trans...
Q: 1. (Store numbers in a linked list) Write a program that lets the user enter numbers and displays nu...
A: Use a linked list to store the numbers. Do not store duplicate numbers. Add the buttons Sort, Shuf...
Q: Q1- Write a matlab program to print the name of the day depending on the entered number (1.. 7), use...
A: Please refer to the following steps for the complete solution to the problem above.
Q: Given: Consider the function below written in Python3: def foo(a, b=[1]): if a <= 1: return b b_new ...
A: Given: Given the function of the code in python 3 We have to answer Worst case time complexity of...
Q: 6. Create a flowchart that will input for two numbers then get the sum,difference,products and qouti...
A:
Q: Practice problem: use DFS version of topological sort for the following DAG J6 DFS(G) I for each ver...
A: The Answer is
Q: lease explain step by step (see attached photo) the process of this solution of the running time in ...
A: The image represents the calculation of the time complexity for the code fragment present in the ima...
Q: Explain how in-database analytics works.
A: Ans: The database analytics working is: 1) In this first step it is determine the data requirements ...
Q: Which of the following is printed to standard output when the following expression is executed fprin...
A: The Syntax of fprintf() is wrong in the given question so it won't print any options which are given...
Q: What are the benefits and drawbacks of using virtual memory?
A: Step 1 The answer is given in the below step
Q: You have procrastinated too long and now your final paper for your junior English course is due in j...
A: Answer:
Q: Provide a concrete example of inter-process communication using pipes (write a small piece of unix c...
A: The answer for the above given question is given below:
Q: How would you add up multiple processes in openMPI? An example would be P0:1 P1:2 thus the sum of tw...
A:
Q: Write a program to find the area of a rectangle, square and triangle using abstract class.
A: PROGRAM INTRODUCTION: Import the required libraries. Start the definition of an abstract class that...
Q: Explain cloud computing, IoT, and the wireless revolution.
A: Cloud Computing and IoT are both connected to each other with the Internet so let's talk about Inter...
Q: 3. Display the sum of 28 + 2, using two variables: x and y. int y = 2; System.out.println (x + y); %...
A: Answer - int x = 28;
Q: Which of the following statements are generally true? (A) Memory hierarchies take advantage of tempo...
A: The data in a processor can be either stored in main memory, secondary memory, or cache. The main me...
Q: How can I convert seconds to hour, minute and seconds Take the Seconds from the user. Programming la...
A: import java.util.*;public class Main{public static void main(String[] args) { Scanner in =...
Q: Prove that the running time for comparison sorts is N(n log n).
A: There are so many reasons that the running time for comparison sorts is Ω(N Log(N)) beacuse, first o...
Q: In computer networks, what is the value of an IP address?
A: Introduction: IP addresses may identify your computer, a favourite website, a network server, or eve...
Q: 1. Create a web page which should contain a table having two rows and two columns. 2. fill in the da...
A: Here is the approach :- Table tag is used to create the table. inside the table tag we need the t...
Q: Create a c++ program and flowchart, algorithm. that will input for prelim, midterm and finals then c...
A: Start Read prelim score Read midterm score Read final score Calculate average If average>50 print...
Q: One of the advantages of a pie chart is that it shows that the total of all the categories of the pi...
A: According to the question the best pie chart only create when you add up to the 5-6 category only do...
Q: Simplify using DeMorgan's theorem A + BC + D (E + F)
A: The De Morgan's theorem:
Q: ate class methods (Setters and Getters) that load the data values. The Setter methods will validate ...
A:
Q: Difference between NFA & DFA? Explain
A: DFA is the short form for the deterministic finite automata and NFA is for the Non-deterministic fin...
Q: Add a firstname parameter of type String to myMethod, and output "Azeneth Garcia". static void myMet...
A: - We need to complete the java code provided for the name string output. - For executing the code,...
Q: 1.) Create a flowchart to find the roots of a quadratic equation by taking a, b and c as an input fr...
A: Answer 1. Algorithm start Declare the variables . Show the statement on screen that ask user to ent...
Q: Instantiate a default_random_engine object called 'randObj'. Declare a vector named 'intVec', and (u...
A: default_random_engine is a number generating engine which generates pseudo-random number class.
Q: HW 6 Solve equation X times X =X for all 2x2 real-valued matrices {a_11, a_12, a_21, a_22}, where "t...
A: ANSWER:-
3.
Step by step
Solved in 2 steps

- 52- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; What will be the subnet mask of Subnet A? Select one: A. 255.255.255.192 B. 255.255.128.255 C. 255.255.255.128 D. 255.255.192.192 E. 255.255.192.054- A network for a local office requires 4 LAN subnets as follows: · Subnet A - North Office with 31 hosts; · Subnet B - East Office with 15 hosts; and · Subnet C - South Office with 7 hosts. · Subnet D – West Office with 4 hosts. Given the IP Address 192.168.15.0 /24 and above described network requirements: 1. Design an optimal address scheme using Variable Length Subnet Mask (VLSM) method; and What will be the subnet mask of Subnet B? Select one: A. 255.255.128.255 B. 255.255.192.0 C. 255.255.192.192 D. 255.255.255.192 E. 255.255.255.224Suppose 198.53.202.0 is a network address and we want 4 subnets. Find the following: - Number of bits required for subnetting - Subnet mask - Range of address in each subnet - Broadcast address for each subnet
- 3.1 An end device was given the IP address of 198.168.4.35/28. Consider this address and indicate: 3.1.1 The network ID/address to which the host belongs. 3.1.2 The network broadcast address to which the host belongs. 3.1.3 The total number of hosts available in the network. 3.1.4 The total number of networks. 3.2 Consider two neighbours, Alice and Bob. Each have wireless IPv4 routers with integrated NAT. Each neighbour connects their laptop to their own wireless router, and each uses appropriate utilities to examine the IP address of each laptop. They realise the laptops have the same IP address. 3.2.1 How is that possible? 3.2.2 Justify one reason that wide-spread deployment of IPv6 would remove the need for the NAT devices.1.4.12.2 End-to-end Delay. Consider again the network shown above. The links again have transmission rates of R1 = R2 = 100 Mbps (i.e., 100 x 106 bits per second), and each packet is 1 Mbit (106 bits) in size. Assume that the propagation delay is 1 msec per link. What is the end-to-end delay of a packet from when it first begins transmission at the sender, until it is received in full by the server at the end of the rightmost link. Assume store-and forward packet transmission. You can assume the queueing delay is zero. Answer choices: A. 2 x 106 msec b. 2.01 msec C. 1.1 msec D. 2.02 msec 1.4.12.3 Maximum Throughput. Consider again the network shown above. The links again have transmission rates of R1 = R2 = 100 Mbps Assume that the link R2 is fairly shared (as we've seen is done via TCP) between the two sessions. What is the maximum end-to-end throughput achieve by each session, assuming both sessions are sending at the maximum rate possible? Answer choices:…Consider the following diagram: A,B,C and D are subnets, R1, R2, and R3 are routers. Default signifies theentire rest of the internet. All 4 subnets each contain the same number of hosts.Consider the following routing table at R3: CIDR Mask Link 0.0.0.0/0 L4 128.4.6.0/24 L3 128.4.8.0/24 L5 1. If 128.4.6.0 is in A, what is the routing table at R1? 2. The ISP that owns all these networks is short on IP addresses, so theyuse a NAT router for R2. How many public IP addresses will C andD use together assuming they use as many private 10.X IP addresses asthey can? How many total public IP addresses will be used by the entirenetwork? Why doesn’t the ISP care about how many private IP addressesare used? 3. Fix R3’s routing table now that we are using NAT: 4. A node in C is given the IP address 10.0.0.1 and only sends and receivespackets on port 1234. A packet destined for this node reaches R2 witha source of (IP=128.4.6.6, Port=3000) and destination of (IP=128.4.8.0,Port=10000).…
- 1-In a network based on the bus topology, the bus is a non-shareable resource for which the machines must compete in order to transmit messages. How is deadlock controlled in this context? 2-Using 32-bit Internet addresses was originally thought to provide ample room for expansion, but that conjecture is not proving to be accurate. IPV6 uses 128-bit addressing. Will that prove to be adequate? Justify your answer’ (for example, you might compare the number of possible addresses to the population of the world).q no 5: In the above network diagram, IP and MAC addresses are given for network nodes. Suppose Host1 (Shahid) sends a datagram to Host2 (Khalid). What IP and MAC addresses (source and destination) will be written in IP and Data link layer headers respectively, for the following intermediate points from Host1 to Host2? Host1 to Router1 (R1) Router1 to Router2 (R2) Router2 to Host2Solve the Subnetting using FLSM & VLSM " Solve the following : a . 192.168.33.0/24 Requirement 6, 15 , 22 b . 10.0.0.0/8 subnet 14 , 22,30 c . 172.16.0.0/16 hosts 25,96 , 2040 d . 10.0.0.0/8 hosts 512 , 32,000
- A large number of consecutive IP addresses are available starting at 198.16.0.0. Sup- pose that four organizations, A, B, C, and D, request 4000, 2000, 4000, and 8000 ad- dresses, respectively, and in that order. For each of these, give the first IP address as- signed, the last IP address assigned, and the mask in the w.x.y.z/s notation. A router has just received the following new IP addresses: 57.6.96.0/21, 57.6.104.0/21, 57.6.112.0/21, and 57.6.120.0/21. If all of them use the same outgoing line, can they be aggregated? If so, to what? If not, why not? The set of IP addresses from 29.18.0.0 to 19.18.128.255 has been aggregated to 29.18.0.0/17. However, there is a gap of 1024 unassigned addresses from 29.18.60.0 to 29.18.63.255 that are now suddenly assigned to a host using a different outgoing line. Is it now necessary to split up the aggregate address into its constituent blocks, add the new block to the table, and then see if any reaggregation is possible? If not, what can be…Given a Class C subnet Mask 255.255.255.192. what will be the subnet address and host number for a machine with IP address 197.1.2.67. Select one: a. second subnet and host 2 b. Third subnet and host number 3 c. second subnet and host 4 d. First subnet and host number 3 e. None f. Second subnet and host number 3Computer Networks Assume the given class C IP Address, 192.168.0.X, where; X is 49 )Apply subnetting of 3 bits and write about: First and last valid IP of the subnet in which this IP 192.168.0.X belongs to. Sub-net mask of this IP after subnetting.

