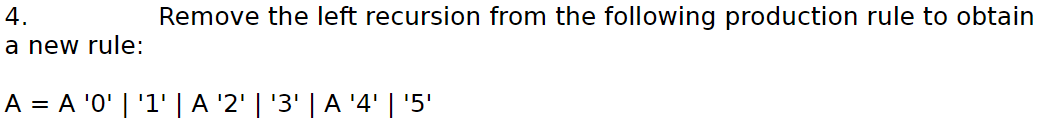
4. Remove the left recursion from the following production rule to obtain a new rule: A = A 'O'L'1'LA '2' L'3' LA '4' | '5'.
Q: based on data encryption standard (DES), if the shared key is "Computer" and the input of S-box in r...
A: A Des is a system that takes the input as plain text or string and then converts it into small parts...
Q: What are the various purposes of the following categories of application software? Enterprise resou...
A: Introduction: In information technology, an application, application programme, or application softw...
Q: order for wireless systems to be developed to enable the Internet of Things, explain why public-key ...
A: In order for wireless systems to be developed to enable the Internet of Things, explain why public-k...
Q: What is the Payment Card Industry Data Security Standard (PCI DSS) and why is it crucial for informa...
A: The PCI DSS is also known as Payment Card Industry Data Security Standard.
Q: Regarding to Free Speech in "Net Neutrality Regulations or the Market?" Should companies be permitte...
A: Net Neutrality Regulations or the Market: Direct censorship is not the only factor that can limit th...
Q: access advanced audit policy settings, what tool is used
A: A) Group Policy it is used to access advanced policy settings
Q: Data base development process is comparable to software development process, and there are different...
A: Introduction: The following is the process of developing a database: One of the most critical aspect...
Q: how to sort with bubble sort a list of words in text file using linked list and data structures?
A: The answer is given below.
Q: Explain the potential and benefits of an IoT-oriented strategy over an M2M-oriented approach by usin...
A: The Internet of Things (IoT) describes the network of physical objects. That are embedded with senso...
Q: Convert 7654321g to X2. O 111100101100111010001 111110101110011010001 O 111110101100011010001 O 1111...
A: The answers to both questions can be found in the photographs below. The answer to the first questio...
Q: An summary of the systems design phase should be provided.
A: System design bridges the gap between the issue domain and the current system, This phase focuses on...
Q: When an optimistic approach to concurrency control is applied, it is common for transactions to take...
A: Introduction: Positive concurrency control techniques, often known as validation or certification me...
Q: Clock cycles on the CPU are defined.
A: Introduction: A clock is a CPU component with a defined number of clock ticks to perform each operat...
Q: i. Find the output string for the input string babbab. ii. Determine whether the input string aabcab...
A: 1) string : babbab String b a b b a b State X X Z X X Z X Output 0 1 0 0 1 0
Q: Write a program that prints an nxn multiplication table, given a positive integer n. Input Each test...
A: Python Program: # Taking the number n as user inputn = int(input("Enter the number n: ")) # Display ...
Q: A 1 2 Problem 1 3 No Default Default 4 Married 5 Single 66 79 101 39 6 7 Create a joint probility ta...
A: When two events say A and B occur together, then its probability is known as Joint probability. P(A ...
Q: Define the concept of dynamic random access memory.
A: Introduction: Computer processors often require data or program code to work correctly, and dynamic ...
Q: Which statute in the United States was expressly designed to cope with the country's encryption poli...
A: Introduction: The ENCRYPT Act would prohibit states and municipal governments in the United States f...
Q: Javaprogram - Using a nested loop, create a program that produces the following output: ...
A: class Test { public static void main(String[] args) { int i,j=3,k; for(i=1;i<=3...
Q: The on-board train protection system may use a periodic procedure to gather data from a trackside tr...
A: We will describe the on-board train protection system and how it is planned to gather data from the ...
Q: lity to all compute
A: The single greatest hazard to all computer systems and networks is malware and social engineering at...
Q: Question 24 Convert 1234567890, to Xg. O 11144501322 O 11145403122 O 11145401322 O 11145041322 O 111...
A: NOTE :- As per our company guidelines we are supposed to answer only one question at a time. Kindl...
Q: Write a program to solve for integral zero of a third-degree polynomial. Evaluating Functions
A: Here, I have to provide a solution to the above question.
Q: Write the same splice method for an ArrayList with member variables called data and size and methods...
A: The method splice is used to modify the contents of an arraylist , this has the following parameters...
Q: Referring to the code below, without changing the program flow and requirements, convert the program...
A: #include <iostream>#include "queue.h"#include <string> using namespace std ; struct car ...
Q: Difference between real and pseudo parallelism in microprocessor.
A: Real parallelism applies to multi-processor(or multicore) system where each processor(or core) initi...
Q: (C PROGRAMMING ONLY) 1. Leap Year Detector by CodeChum Admin Let’s try to find out whether a year ...
A: I have provided C CODE along with CODE SCREENSHOT and 2 OUTPUT SCREENSHOTS-------------
Q: Make a C++ program with class, object, constructor, data member with access modifier and member func...
A: Data.cpp #include<bits/stdc++.h>using namespace std; class Formula{//Declaring all the given ...
Q: Take a new smartphone and be excited about the apps available. You read about a great new phone game...
A: To download and install the gaming program, the user must agree to certain access permissions, such ...
Q: The three main settings in which concurrency might occur, as well as examples of each, should be des...
A: Introduction: Concurrency is the process of executing several instructions at the same time. It is a...
Q: MATLAB Write a function CalFunc.m that can receive multiple math function as input arguments in the
A: function N = CalFunc(varargin) N=length(varargin); x=linspace(0,10,100); if N==0 f=input('Enter ...
Q: please code in python Write a function that receives a string and a number (n) as parameters and re...
A: To implement everyNth(), strings concept in python is used.
Q: Lets the user enter courses and prints them out correctly at the end Catches there being six courses...
A: Program is very easy to construct here is the approach First create the empty list and create the v...
Q: the different binary codes? Briefly describe
A: Lets see the solution.
Q: Examine the pros and disadvantages of enterprise-based systems in terms of maximising the use of inf...
A: Introduction: ICT ICT is an abbreviation that signifies Information Communications Technology.ICT in...
Q: How would you address the potential for misleading sharing?
A: Introduction: In frameworks with suitable, lucid stores at the size of the smallest asset block cont...
Q: Draw a single diagram that illustrates how the following concepts are related: • Data • Database • D...
A: Database, data, or information is organized in such a way that allows for quick access and retrieval...
Q: What are the steps in solving basic mathematical operations on different number system?
A:
Q: Consider two advantages of employing linear search rather than binary search in your research
A: Introduction : Significant Distinction Binary Search should be used to sort the input data, not Line...
Q: Explain in detail what cloud computing is and what the advantages of utilising it are.
A: Cloud Computing- Cloud computing is an overall term for whatever includes conveying hosted services ...
Q: Write a Python function that returns the position of the element in a vector of numbers nearest the ...
A: To implement vectorMeanPos(), list are used. For finding position of element in a vector of number n...
Q: studies justify
A: IPsec VPN: IPsec was developed for remote users to connect to networks over the internet without the...
Q: How can data visualisation make use of the following five graphical data features in order to emphas...
A: Data visualization is a graphic representation of organized or unstructured data that displays infor...
Q: Create using the c++ string class. Write a function that counts the occurence of each letter in the ...
A: Given :- Create using the c++ string class. Write a function that counts the occurence of each lett...
Q: Question1: define two lists of numbers (arrays) and ask the user to give the size of each, and then ...
A: First check whether the lengths are same or not Then every element in both the arrays and check whet...
Q: Compiler should be defined.
A:
Q: Explain why it is critical in the construction of secure systems to keep track of what users are doi...
A: Introduction: The development and implementation of security countermeasures are components of overa...
Q: Write a program in Matlab that can read 33 numbers Then it prints the numbers that are divisible by ...
A: MATLAB CODE: a=33; disp('Given number is divided by 5' + a); number = 1; while number<=a if mo...
Q: Write the Java statement for the following. Declare an array of integer named numbers allocating 10...
A: In Java, syntax of creating an array are : data_type[] array_name = new data_type[size]; data_type[]...
Q: Describe how the arguments are used in the following code: def display_state_...
A: EXPLANATION: Their are two general functions along with the main function that is present in the gi...
Step by step
Solved in 2 steps with 1 images

- Remove the left recursion from the productions: S ->A a |b A ->A c |S d | €Q4. Recursion Find how many possible combinations that a number can be decomposed into the multiple of integers (smaller than the number itself) by a recursion function.Suppose we have a positive number Y as input, and it need to be decomposed into the multiple of several integers, Yi, where each Yi, is smaller than Y(e.g., Y=Y1∗Y2∗ Y3∗...∗Yn). In addition, these decomposed integers can only be arranged in an ascending order (Y1Remove left recursions only from:S -> Sa | SBa | aS | bA -> aa | bAB -> ba | b |
- Remove indirect recursion A---->aA | Ab | Bab | C | d B---->AC | Ad | C C----> Ad | dQuestion 10 Code the following in Java using Recursion1. Write a recursive function named RecursiveSum that, given a positive number n (n> 0), returns the sum of the numbers from 1 to n. Also, show the process of finding the result using a recursion tree.
- ce from the user t using recursion.Task 4: The first problem that you solve recursively is to implement enoughGate() to check if the dogMaze has at least two gates (one for the entrance and one for the exit). This problem must be solved recursively, however there is no limitation on what type of recursion (i.e., direct or indirect recursion) you use . As a reminder, a direct recursion refers to the function that calls itself to solve the given problem. However, by indirect recursion, more than one function involves in solving the problem. It is possible that a non-recursive function solves a small part of the problem and then calls the recursive function to finish the job. /** * This method returns true if the number of * gates in dogMaze >= 2. * @return it returns true, if enough gate exists (at least 2), otherwise false. */ publicboolean enoughGate (){ // insert your code here. Change the return value to fit your purpose. return true; }For function decToBinary, write the missing parts of the recursion case. This function should return a string that stores the binary equivalent for int variable num. Example: The binary equivalent of 13 may be found by repeatedly dividing 13 by 2. So, 13 in base 2 is represented by the string "1101". Examples: decToBinary(13) -> "1101" public String decToBinary (int num) { if (num < 2) return Integer.toString(num); else return <<Missing recursive call>> + <<Missing calculation>>;}
- PLZ help with the following: In Java Write a program using recursion to display all valid (i.e. properly open and closed) combinations of n-pairs of parentheses.The following recursion occurs when there are more than two calls for each non-base case: : c)Multiple recursion d)Two Step Recursion a)Linear recursion b)Binary recursionQuestion#1: Let P and Q be integers and suppose F (P, Q) is recursively defined by: F(int P, int Q) if (P == 0) return Q else return F(P- 1, P + Q) Find and Trace F(8,1)

