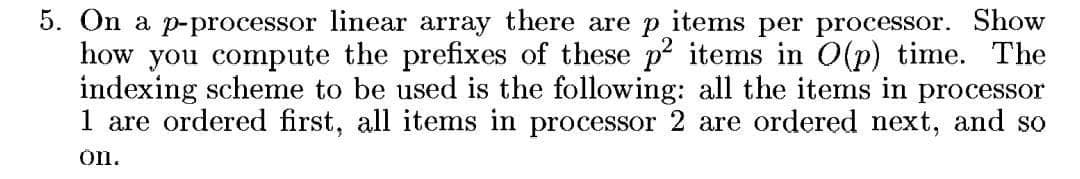
5. On a p-processor linear array there are p items per processor. Show how you compute the prefixes of these p2 items in O(p) time. The indexing scheme to be used is the following: all the items in processor 1 are ordered first, all items in processor 2 are ordered next, and so ón.
Q: Computer science How public is it before your privacy is jeopardised?
A: Introduction: The government's authority, as well as the power of private businesses, is constrained...
Q: What does universal design entail, and how does it function?
A: Introduction: Universal Design is the process of designing and composing a space so that it may be a...
Q: Describe the differences between maps, scenes, apps, and files.
A: Introduction: A scene is similar to a map in that it is a mashup of data layers that may be seen in ...
Q: Discuss optical discs such as pits,lands,CDs,DVDs,Blu-ray, and high definition.
A: Introduction: Pits,lands,CDs,DVDs,Blu-ray, and high-definition optical discs
Q: Why is the transport layer installed in the end system?
A: Let us see the answer:- Introduction Transporting data beyond the confines of an address space nece...
Q: Based on the maturity of the testing process, write a short essay on three testing goals.
A: Introduction
Q: cter at the end of the strin
A: The option as, Apply operation 1 three times and operation 2 two times.
Q: PHP includes all the standard arithmetic operators. For this PHP exercise, you will use them along w...
A: PROGRAM INTRODUCTION: Start the required tag for the HTML file that includes HTML, HEAD, META, and ...
Q: Explain the operation of virtual memory in operating systems.
A: Introduction: The operating system moves data from inactive programmes out of RAM and stores it in v...
Q: Please identify two types of antipatterns (also called code smells) in the following source code: p...
A: Here, I have to provide a solution to the above question.
Q: SeaMoney has a feature to transfer money between users. Let's imagine a simple scenario. N usernames...
A: Using hashmap to store the username as key and balance as associated value with the key. Below is th...
Q: Vhat are the different types of security control families?
A: Security controls are safeguards or countermeasures to avoid, detect, counteract, or minimize securi...
Q: In terms of data transmission, how does the size or width of a bus effect or influence the architect...
A: answer is
Q: Consider the grammar E TE' E'- →+TE' |e T FT' T' FT' |e F (E) digit For the given expression (9 + 8 ...
A: Here in this question we have given a grammer and we have asked to draw annotated parse tree for exp...
Q: Find the missing heuristics to ensure it is consistent given the following question. You can provide...
A: X Y A >=3 <=8 E >=4 <=6 D >=3 <=8 ...
Q: Explain the major differences between multiprogrammed batch processing and time sharing systems in a...
A: Solution Time sharing system : Time sharing is a technique which enable many people, located at var...
Q: What exactly is system change-over?
A: Intro System changeover is a process of changing the way a thing is done to another and how other ac...
Q: 1. What are functional requirements? 2. What are non-functional requirements? 3. What is software me...
A: - We need to talk about the terms asked.
Q: What is the CPU time if the programme executes 500 instructions at 5 cycles each instruction and the...
A: Intro CPU time: The formula for computing the CPU time is provided below:
Q: Given the following binary number in 32-bit (single precision) IEEE-754 format, the decimal value cl...
A: Given binary number 0011 1110 0110 1101 0000 0000 0000 0000 In this left most bit represents sign bi...
Q: In python) Skeleton code for the function count_evens is below. The function takes in an array of nu...
A: def count_evens(n_array): num_events = 0 for number in n_array: if numb...
Q: 3. Grade is an unsigned byte stored in the program memory (PM). Letter is a byte stored in the data ...
A: Find the code given as below and output: As per company guidelines we are supposed to answer only on...
Q: Make a thorough note on software testing concepts, issues, and techniques.
A: Given: we have to discuss Software testing concept, issues and techniques.
Q: What governance mechanisms need to be put in place to ensure common customer data and a shared custo...
A: Let's see the solution in the next steps
Q: Consider a case in which recursive binary search might be useful. What would you do in such situatio...
A: Let's see the solution in the next steps
Q: Write a Python program to convert JSON data to Python object. import json json_obj = '{ "Name":...
A: Here I written python program for given problem. I hope you like it.
Q: After the successful conduct of Mid Term Examinations, the HOD of the Department of Examinations has...
A: The Answer is
Q: 3. Change the following IPV4 addresses from binary notation to dotted decimal notation. [ a. 1000001...
A: We have 2 IPv4 addresses given in binary notation. We need to convert these addresses from binary to...
Q: Write an explanation of polymorphism and its applications in software in no more than 250 words.
A: Intro Polymorphism: Definition The meaning of polymorphism is having many forms. Polymorphism is the...
Q: When does caching go wrong?
A: Introduction: When programmes display local property, temporary storage is the best option. However,...
Q: What are the most prevalent types of functions in C++? Using a program, define three typical types o...
A: Introduction A function is a block of statements that can be reusable and part of our program Based ...
Q: In terms of security, distinguish between symmetric and asymmetric cryptography (key length, securit...
A: Introduction: Key Length is a word that is used to describe the length of a key. The key length in...
Q: Consider an array of N integers. Describe an algorithm with an 0(N) runtime that processes the array...
A: Please refer below for your reference: Below is a O(n) approach: I have counted the number of null a...
Q: 2. Using JCreator, create a new Java application file and write the following code. Name the file as...
A: //This interface contains the code that is shown in Sports interface public interface Sports{ pub...
Q: Assume you have a one-to-one adviser connection. What additional restrictions must the relation advi...
A: Cardinality restrictions are specified, generalized, and used to simplify design, enhance maintenanc...
Q: of a data hierarchy must be recognised all the way up to the database layer.
A: given - To work successfully, the components of a data hierarchy must be recognised all the way up t...
Q: Define data mining as an enabling technology for corporate intelligence, as well as the applications...
A: Definition Data mining is defined as a process that analyzes the data from various sources and summa...
Q: ID Major Avg. project score Avg. exam score Employed? Salary Computer 82 76 Yes 90,000 Engineering 8...
A: a. Data Cleaning: Step 1: Remove irrelevant dataStep 2: Deduplicate your dataStep 3: Fix structural ...
Q: Which email protocol enables an email client to download emails to a local computer? a. IMAP4; b....
A: Intro Option C (TCP)A Transmission Control Protocol (TCP) is used for maintaining and establishing n...
Q: Create a python/matlab code that finds all complex roots using Bairstow’s Method with deflation
A: Let's see the solution in the next steps
Q: Python's syntax is as follows: Print a list of all seats in a theater based on the parameters num r...
A: Note: Please take care of indentation while writing the code.
Q: What is a screened subnet firewall? Why is the most commonly used firewall in businesses
A: What is a screened subnet firewall? Why is the most commonly used firewall in businesses? in...
Q: CASE STUDY #1: Uber Announces New Data Breach Affecting 57 Million Riders and Drivers Ridesharin...
A: As per our company guidelines, we are supposed to answer only the first 3 sub-parts. kindly repost o...
Q: What is the effective memory access time if the memory access time is 450 ns and a page fault takes ...
A: Effective access time The 'effective access time' is essentially the (weighted) average time it take...
Q: Design a customer care class for AIRTEL. Hava sufficient variables and operations maintain the log d...
A: Airtel.java import java.io.IOException; import Assignment.*; public class Assignment4 { public s...
Q: How to calculate the time efficiency in adding searching using C++ or
A: First i give the code in C++ with output screenshot then I explain the time efficiency in both the c...
Q: A process that spawns or initiates another process is known as. a. a child process b. forking c. bra...
A: Intro The process initiating another process Forking happens when developers take a copy of source ...
Q: PHP exercise 7 HTML tables involve a lot of repetitive coding - a perfect place to use for loops....
A: use two for loops, one nested inside another. Create the following multiplication table
Q: The architecture of a company's network is one of the most essential decisions it can make in terms ...
A: Introduction: Network equipment for small businesses: routers, switches, and firewall servers
Q: Find sop (sum of Poreluct) of this the follow ing Expresion. F(x%,z)= Em[011, 3,5,6)
A:
Step by step
Solved in 2 steps

- Given an integer n and an array a of length n, your task is to apply the following mutation to a: Array a mutates into a new array b of length n. For each i from 0 to n - 1, b[i] = a[i - 1] + a[i] + a[i + 1]. If some element in the sum a[i - 1] + a[i] + a[i + 1] does not exist, it should be set to 0. For example, b[0] should be equal to 0 + a[0] + a[1].Given an integer array nums and an integer val, remove all occurrences of val in nums in-place. The order of the elements may be changed. Then return the number of elements in nums which are not equal to val. Consider the number of elements in nums which are not equal to val be k, to get accepted, you need to do the following things: Change the array nums such that the first k elements of nums contain the elements which are not equal to val. The remaining elements of nums are not important as well as the size of nums. Return k. Example 1: Input: nums = [3,2,2,3], val = 3 Output: 2, nums = [2,2,_,_] Explanation: Your function should return k = 2, with the first two elements of nums being 2. It does not matter what you leave beyond the returned k (hence they are underscores). Example 2: Input: nums = [0,1,2,2,3,0,4,2], val = 2 Output: 5, nums = [0,1,4,0,3,_,_,_] Explanation: Your function should return k = 5, with the first five elements of nums containing 0, 0, 1, 3, and 4.…Given an array of integers arr, sort the array by performing a series of pancake flips. In one pancake flip we do the following steps: Choose an integer k where 1 <= k <= arr.length. Reverse the sub-array arr[0...k-1] (0-indexed). For example, if arr = [3,2,1,4] and we performed a pancake flip choosing k = 3, we reverse the sub-array [3,2,1], so arr = [1,2,3,4] after the pancake flip at k = 3. Print out the k-values corresponding to a sequence of pancake flips that sort arr. Example 1: Input: arr = [3,2,4,1] Output: 4, 2, 4, 3 Explanation: We perform 4 pancake flips, with k values 4, 2, 4, and 3. Starting state: arr = [3, 2, 4, 1]. After 1st flip (k = 4): arr = [1, 4, 2, 3] After 2nd flip (k = 2): arr = [4, 1, 2, 3] After 3rd flip (k = 4): arr = [3, 2, 1, 4] After 4th flip (k = 3): arr = [1, 2, 3, 4], which is sorted. Another potential solution is: Output = 3, 4, 2, 3, 1, 2, 1, 1 with a similar explanation. All potential solutions that solve the problem are…
- Given an array of locations in memory of n dimensions we want to find out what ordering it has in memory. For example, given the following input array [[[ 0 4 8 12] [16 20 24 28] [32 36 40 44]] [[48 52 56 60] [64 68 72 76] [80 84 88 92]]] your function has to return the tuple: [2,1,0] As a suggestion: - Loop through the number of dimensions - For each dimension generate a list of slices equivalent to the above indexing notation - Get the first two elements of each axis - Order the axes by the difference between those two elements Complete the code: def get_storage_order(r): import numpy as np return to check the code manually: r = np.array([[[ 0, 4, 8, 12], [32, 36, 40, 44], [64, 68, 72, 76]], [[16, 20, 24, 28], [48, 52, 56, 60], [80, 84, 88, 92]]]) get_storage_order(r)Given an array of locations in memory of n dimensions we want to find out what ordering it has in memory. For example, given the following input array [[[ 0 4 8 12] [16 20 24 28] [32 36 40 44]] [[48 52 56 60] [64 68 72 76] [80 84 88 92]]] your function has to return the tuple: [2,1,0] As a suggestion: - Loop through the number of dimensions - For each dimension generate a list of slices equivalent to the above indexing notation - Get the first two elements of each axis - Order the axes by the difference between those two elements Complete the code: def get_storage_order(r): import numpy as np returnPlease Help me with This Problem Language = C++ Take an array of name A of size 4 X 4. Take input and then take B with size 4 X 4. Add them.And show result after taking transpose.Formally, the i th row, j th column element of C T is the j th row, i th columnelement of C:1. write the rows of C as the columns of C T2. write the columns of C as the rows of C TC is an m × n matrix then C T is an n × m matrix.Then save the result in a file named “result.txt”, according the matrix spaces and newline. Note:Understand the Question Properly and Kindly Answer
- 1) Consider an integer array a of length n with indexing starting at 0, where n is a positive integer.If the elements of array a are to be written out in reverse order, which of the following C++ code fragment does NOT do the job? Question options: a. int i=n-1; while (i>=1){cout << a[i] << endl; i = i-1;} cout << a[i] << endl; b. int i=n-1; while (i>=1){cout << a[i] << endl; i = i-1;} c. int i=n-1; while (i>=0){cout << a[i] << endl; i = i-1;} d. int i=n; while (i>0){cout << a[i-1] << endl; i = i-1;} 2) Assume we use 8-bit cell to store floating point numbers, 1 bit for sign, 3 bits for excessed exponent, and 4 bits for significand. What is the decimal value for a cell with bit pattern 0 111 1101 Question options: a. 125 b. 224…Multiplying Factors For a pair of integers (x,y) and an integer k, the multiplying factor is defined as minimum positive integer m such that LCM(x,y) * m is divisible by k. Here LCM(x,y) represents the smallest positive integer divisible by both x and y, their least common multiple. Given an array arr of n integers and an integer k, find the sum of multiplying factors over all pairs of integers (arr[i], arr[j]) and k0 <= i,j < n. Example Suppose n=3, arr =[4,5,6] and k=12. Pair Multiplying Factor Remarks (4, 3 LCM(4,4)**3=4**3 =12 4 ) LCM(5,5)**12=5** 12=60 (5, 12 LCM(6,6)**2=6**2 5) (6, 2 12 6 )Let A be an array of numbers. In the maximum sub-array problem, your goal is to determine the sub-array A[x . . . y] of consecutive terms for which the sum of the entries is as large as possible. For example, if A = [−2, −3, 4, −1, −2, 1, 5, −3], the maximum sub-array is [4, −1, 2, 1, 5], and the largest possible sum is S = 4 − 1 − 2 + 1 + 5 = 7. Suppose A = [1, 2, −4, 8, 16, −32, 64, 128, −256, 512, 1024, −2048]. Determine S, the largest possible sum of a sub-array of A.
- Create an ABM function that takes the following parameters: n := number of paths to be simulated m := number of discretization points per path S0 := initial starting point dS=μdt+σdW Program the function by using two nested "for loops" def ABM(n,m,S0,mu,sigma,dt): np.random.seed(999) arr = # create 2D zeros array with the correct dimensions arr[,] = #initialize column 0 # fill in array entries for i in : for j in : arr[i,j] = return arr1. Consider a problem of computing the prefix average of a sequence of numbers stored in an array P consisting of P integers. We want to compute an array P such that P is the average of P for P . Consider the two algorithms related to the above problem. Answer the questions given belowWap Given a sorted array nums, remove the duplicates in-place such that each element appears only once and returns the new length. Do not allocate extra space for another array, you must do this by modifying the input array in-place with O(1) extra memory. Clarification: Confused why the returned value is an integer but your answer is an array? Note that the input array is passed in by reference, which means a modification to the input array will be known to the caller as well. Internally you can think of this: // nums is passed in by reference. (i.e., without making a copy) int len = removeDuplicates(nums); // any modification to nums in your function would be known by the caller. // using the length returned by your function, it prints the first len elements. for (int i = 0; i < len; i++) { print(nums[i]); } Example 1: Input: nums = [1,1,2] Output: 2, nums = [1,2] Explanation: Your function should return length = 2, with the first two elements of nums being 1 and 2…

