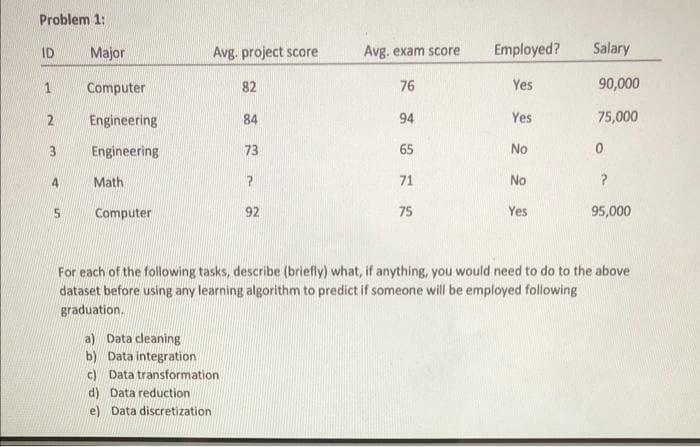
ID Major Avg. project score Avg. exam score Employed? Salary Computer 82 76 Yes 90,000 Engineering 84 94 Yes 75,000 3. Engineering 73 65 No Math 71 No Computer 92 75 Yes 95,000 For each of the following tasks, describe (briefly) what, if anything, you would need to do to the above dataset before using any learning algorithm to predict if someone will be employed following graduation. a) Data cleaning b) Data integration c) Data transformation d) Data reduction e) Data discretization
Q: Examine how various companies employ information systems.
A: Introduction: Managers and other organizational leaders can maintain data in folders and documents t...
Q: A process that spawns or initiates another process is known as. a. a child process b. forking c. bra...
A: Intro The process initiating another process Forking happens when developers take a copy of source ...
Q: hat are the dangers of building a security infrastructure that is available to everyone?
A: Answer: With all of the buzz about cloud adoption, it's tempting to believe that on-premises IT infr...
Q: CPU Priority Scheduling-preemptive: Write a Java program to implement a priority scheduling algorith...
A: Below I have provided the java code:
Q: Given the following binary number in 32-bit (single precision) IEEE-754 format, the decimal value cl...
A:
Q: For Questions 1 and 2, manually enter the word Score into cell A1, and manually enter 87 into cell B...
A: VBA is abbreviated as Visual Basic for Applications which is a coding language of Excel and other Of...
Q: What are the benefits of running both subsystems and logical partitions on the same machine?
A: Intro the above question is about benefits of running both subsystems and logical partitions on the ...
Q: Write a python program for number of circular permutations of m different things taken all at a time...
A: Number of circular permutation =(n-1)! Start define function circular takes n as a parameter init...
Q: For each of the following tasks, describe (briefly) what, if anything, you would need to do to the a...
A: The most important elements in a computer proposal: Ai Technology (AI), Insights, and Predictive Ana...
Q: Prove for all P Q: prop (~Q -> ~P) - > (P -> Q) using Coq programming language. additional axioms...
A: COQ'S Reasons: We've seen a lot of different instances of factual statements (assertions) and how to...
Q: Why is the CPU at the heart of any computer?
A: Introduction: The CPU is regarded as the computer's heart, and the reason for this is explained in s...
Q: Assume your organisation has leased one Class C licence, 120.10.10.0, and wishes to sublet the first...
A: Introduction: CIDR notation is basically a compress representation of the IP address as well as its ...
Q: Commands for disc drive activities can be understood by ?
A: Introduction: Disk controllers can interpret commands for disc drive activities.
Q: What exactly is database security? What are two methods for keeping a database safe?
A: Introduction: What exactly is database security? What are two methods for keeping a database safe?
Q: Assume you have two SS CPUs. How long will it take to run these two threads? How many issue slots ar...
A: Introduction: the question is about Assume you have two SS CPUs. How long will it take to run these ...
Q: Given the following binary number in 32-bit (single precision) IEEE-754 format, the decimal value cl...
A: Given binary number 0011 1110 0110 1101 0000 0000 0000 0000 In this left most bit represents sign bi...
Q: Describe how cryptocurrency mining works.
A: Introduction: Crypto miners validate exchanges in order to get compensated for their efforts in the ...
Q: What does the superparamagnetic limit of disc drives imply?
A: Introduction: Superparamagnetism: A form of magnetism that appears in small ferromagnetic or ferro...
Q: Assume we have a computer with the following specifications: a magnetic disc with a delay of 15 mill...
A: Intro In this problem the computer has a following characteristic: The access latency of magnetic ...
Q: Writes a MIPS assembly language program that reads an input string, reverses the order of its charac...
A: .model stack .stack 200h .data msg1 db 10, 13, "Enter a string (at most 18 characters) : ", 10, 13,'...
Q: a SQL query for the give CSV that have their own table List all airlines. For every airline, comput...
A: the query is an given below :
Q: Invent a program that will determine whether or not a given number is a Perfect Number. An Example ...
A: The code is given in the below step
Q: What is Responsibility Driven Design, and how does it work?
A: Introduction: Object-oriented programming, abbreviated as OOPS, is a programming technique based on ...
Q: ops are very useful in creating lists and tables. In this PHP exercise, you will use a loop to creat...
A: Lets see the solution.
Q: Using a diagram, explain the memory hierarchy.
A: Memory hierarchy : In computer architecture, the memory hierarchy separates computer storage into a ...
Q: Describe five benefits and five drawbacks of building prototypes.
A: Five Benefits: 1) Provide Functionality and interactions- static high fidelity and wireframe are una...
Q: Problem 11: Max heap Build the Max heap with the values: 10, 47, 40, 100, 52, 72. Show the heap afte...
A: First let's understand what is max heap The Max heap is also a simply binary tree with root and not...
Q: Describe enterprise storage systems, file servers, network attached storage, RAID systems, organisat...
A: A storage device is a system or structure that is used to store the data either temporarily or perma...
Q: What is the significance of invention and incubation in the success of technology entrepreneurs?
A: What is the significance of invention and incubation in the success of technology entrepreneurs?
Q: How can we create PDF files in node js node using a library?
A: INTRODUCTION: Here we need to tell how we create PDF files in node.js using the library.
Q: PHP includes all the standard arithmetic operators. For this PHP exercise, you will use them along w...
A: PROGRAM INTRODUCTION: Start the required tag for the HTML file that includes HTML, HEAD, META, and ...
Q: 1. Is Graph G1 strongly connected? 2. Give the 3-edge simple path from Node A to Node E 3 Is the Gra...
A: Yes , the graph G1 is strongly connected as each node of the graph can be reached by each other node...
Q: i need code for face detection using CNN user defined and face recognition using svm clasifier from ...
A: CNN - It is a deep learning algorithm that takes an image as an input and assign some features to va...
Q: Use the pumping lemma to show that the following languages are not context-free. (a) {0 | n is a non...
A: Pumping lemma: If L is a context-free language, there is a pumping length p such that any string w ∈...
Q: Describe the many forms of semantics, when and how they are used, and what the benefits and drawback...
A: Introduction the question is about Describe the many forms of semantics, when and how they are used,...
Q: Task2: In packet switching technology the packet size is an import parameter when it con o efficienc...
A: Bundle exchanging is a technique for moving the information to an organization in type of parcels. T...
Q: What are some of the disadvantages of allowing uncertified individuals to conduct software engineeri...
A: In the current modern technologically driven world, it is true and a necessity that noncertified ind...
Q: How would you explain heaps in general? I mean explain heaps to someone who dont have knowledge abou...
A: A heap is a data structure made up of "nodes" that contain values. A typical heap has a root node at...
Q: Please identify two types of antipatterns (also called code smells) in the following source code: p...
A: Here, I have to provide a solution to the above question.
Q: D TestShape.java X 1 public class TestShape { public static void main(String[] args) { 2 4 int a, b,...
A: Solution :: There are two Java code above and you didn't mention which explanation you want and also...
Q: V. Round Robin and SJF comparison Process Arrival Time CPU Burst Time P1 9. P2 4 4 P3 6. 1 P4 8 6. F...
A: Given: We need to calculate the Average waiting time and turn around time of the given process . Usi...
Q: Assume you need to send 40 Gigabytes of data from Los Angeles to New York City right now. You have a...
A: Intro Data of 40 Gigabytes Data Transfer 500 kilo bits
Q: Describe agile development methodologies.
A: Introduction: Agile Development : Agile is a software development technique that focuses on the wh...
Q: Find sop (sum of Poreluct) of this the follow ing Expresion. F(x%,z)= Em[011, 3,5,6)
A:
Q: What is a wireless network's basic service set configuration? how are they put to use?
A: Let us see the answer:- Introduction As the name implies, a Basic Service Set (BSS) is a network des...
Q: Based on the maturity of the testing process, write a short essay on three testing goals.
A: Introduction
Q: What is the primary role of the 8288 bus controller when combined with 8086/8088 maximum mode operat...
A: In the advanced configuration, the 8288 bus controller should be used to provide all the storage and...
Q: What is open source in computer science?
A: This question comes from Internet Technologies which is a paper of computer science. Let's discuss i...
Q: When does caching go wrong?
A: Introduction: When programmes display local property, temporary storage is the best option. However,...
Q: "The internet is a computer network that connects billions of computing devices all around the world...
A: Introduction: Individuals and businesses can connect to the Internet through computer terminals, com...
Computer Science
Step by step
Solved in 2 steps

- Consider the following task of building a zoo for Drexel! You've gathered m donors to fund the creation ofyour new park, and you've picked the location, so now you just need to choose the inhabitants. Ideally you'dget every animal imaginable, except you just don't have space. As it is, you have room to comfortably tk animals. Since you'd like to ensure that your funding doesn't dry up, you gure your donors should getto make requests about which animals will be kept. After sending out a few emails, you collect from eachdonor i a list of animals Ai which donor i would like to have at the zoo. As you suspected, the total numberof di erent animals appearing on the m lists exceeds k, so you won't be able to satisfy all of their requests.You decide the fairest thing to do is to ensure that at least 1 animal from each Ai is chosen.Given all these lists, we want to know whether we can select a set H of at most k animals to put in thezoo such that each donor i will be able to see at least one…Correct answer will be upvoted else downvoted. Computer science. You are permitted to alter the marks through the accompanying activity: Pick two particular integers I and j among 1 and n. Trade the marks of focuses I and j, lastly Draw the section between focuses I and j. A grouping of tasks is legitimate if in the wake of applying every one of the activities in the succession all together, the k-th point winds up having the name k for all k among 1 and n comprehensive, and the drawn sections don't meet each other inside. Officially, assuming two of the portions cross, they should do as such at a typical endpoint of the two sections. Specifically, all drawn portions should be unmistakable. Track down any legitimate arrangement of activities, or say that none exist. Input The main line contains an integer n (3≤n≤2000) — the number of focuses. The I-th of the accompanying n lines contains three integers xi, yi, man-made intelligence (−106≤xi,yi≤106,…Which of the following examples features a child effectively using hot executive function? In the DCCS, Julian correctly switches from sorting by shape to sorting by color. During the delayed gratification task, Julian rings the bell because he is tired of waiting. Julian solves the Tower of Hanoi problem in the fewest possible moves because he constructed a well-defined problem space. Julian says the color of the ink in the Stroop task, because those are the rules of the task. At home, Julian suppresses his urge to take cookies from the family cookie jar because every time he did that in the past, he was put in time-out.
- Consider the following task of building a zoo for Drexel! You’ve gathered m donors to fund the creation ofyour new park, and you’ve picked the location, so now you just need to choose the inhabitants. Ideally you’dget every animal imaginable, except you just don’t have space. As it is, you have room to comfortably fitk animals. Since you’d like to ensure that your funding doesn’t dry up, you figure your donors should getto make requests about which animals will be kept. After sending out a few emails, you collect from eachdonor i a list of animals Ai which donor i would like to have at the zoo. As you suspected, the total numberof different animals appearing on the m lists exceeds k, so you won’t be able to satisfy all of their requests.You decide the fairest thing to do is to ensure that at least 1 animal from each Aiis chosen.Given all these lists, we want to know whether we can select a set H of at most k animals to put in thezoo such that each donor i will be able to see at least…Correct answer will be upvoted else downvoted. There are n focuses on an endless plane. The I-th point has facilitates (xi,yi) to such an extent that xi>0 and yi>0. The directions are not really integer. In one maneuver you play out the accompanying activities: pick two focuses an and b (a≠b); move point a from (xa,ya) to either (xa+1,ya) or (xa,ya+1); move point b from (xb,yb) to either (xb+1,yb) or (xb,yb+1); eliminate focuses an and b. Notwithstanding, the move must be performed if there exists a line that goes through the new organizes of, another directions of b and (0,0). If not, the move can't be performed and the focuses stay at their unique directions (xa,ya) and (xb,yb), individually. Input The main line contains a solitary integer n (1≤n≤2⋅105) — the number of focuses. The I-th of the following n lines contains four integers ai,bi,ci,di (1≤ai,bi,ci,di≤109). The directions of the I-th point are xi=aibi and yi=cidi. Output :In the primary…The use of computers in education is referred to as computer-assisted instruction (CAI). One problem that develops in CAI environments is student fatigue. This problem can be eliminated by varying the computer's dialogue to hold the student's attention. For each correct answer and each incorrect an- swer. The set of responses for correct answers is as follows: Very good! Excellent! Nice work! Keep up the good work! The set of responses for incorrect answers is as follows: No. Please try again. Wrong. Try once more. Don't give up!No. Keep trying. Use random number generation to choose a number from 1 to 4 that will be used to select an appropriate response to each answer. Use a switch statement to issue the responses. Please write the code in Javascript HTML5
- Consider the Modified tower of Hanoi problem with 2 Pegs (A, B) and 10 Disks. All these disks are placed in Peg A, where the smallest disk is placed on the top and the largest disk is placed on the bottom. We want to move all these disks from A to B.What is the minimum number of moves required to solve this problem. While moving, consider the same rule as shown in the class. Justify your answer.Which of the following can complete the statement below?Different algorithms for the same problem can... never come up with exactly the same outcome can not be generated as algorithms require very specific information have different running times solve the problem differently please tell me the answersQuestion 9 Full explainthe this question very fast solution sent me step by step Don't ignore any part all part work u A and bText typing work only not allow paper work
- You have decided to undertake a project and have defined the main research question as ‘What are theopinions of consumers on a 10 percent reduction in weight, with the price remaining the same, of “Snackers”chocolate bars?’Write both a null and alternative hypothesis that you could test in your project. In your response, also definethe purpose of the study, define the research problem statement, list the research objectives, and researchquestions.Correct answer will be upvoted else Multiple Downvoted. Computer science. Berland local ICPC challenge has quite recently finished. There were m members numbered from 1 to m, who contended on a problemset of n issues numbered from 1 to n. Presently the article is going to happen. There are two issue creators, every one of them will tell the instructional exercise to precisely k back to back errands of the problemset. The creators pick the section of k continuous errands for themselves autonomously of one another. The sections can correspond, meet or not cross by any means. The I-th member is keen on paying attention to the instructional exercise of all continuous errands from li to ri. Every member consistently decides to pay attention to just the issue creator that tells the instructional exercises to the most extreme number of assignments he is keen on. Leave this greatest number alone artificial intelligence. No member can pay attention to both of the creators, regardless of…Which of the following statements about supervised learning is not accurate? * a) It is a form of machine learning known as reinforcement learning b) It doesn't need any response variable at all c) Classification, a kind of supervised learning that falls under this category d) None of the preceding options

