5. The security goal that generates the requirement for actions of an entity to be traced uniquely to that entity is, A. accountability B. authenticity C. privacy D. integrity _ attacks attempt to alter system resources or affect their operation. A. Active B. Release of message content C. Passive D. Traffic analysis 7. A takes place when one entity pretends to be a different entity. A. passive attack B. masquerade C. modification of message D. replay 8. X.800 defines communicating open systems and that ensures adequate security of the systems or of data transfers. _as a service that is provided by a protocol layer of A. replay B. integrity C. authenticity D. security service is a professional membership society with worldwide organizational and individual membership that provides leadership in addressing issues that confront the future of the Internet and is the organization home for the groups responsible for Internet infrastructure standards, including the IETF and the IAB. A. ITU-T B. ISO C. FIPS D. ISOC 9.
5. The security goal that generates the requirement for actions of an entity to be traced uniquely to that entity is, A. accountability B. authenticity C. privacy D. integrity _ attacks attempt to alter system resources or affect their operation. A. Active B. Release of message content C. Passive D. Traffic analysis 7. A takes place when one entity pretends to be a different entity. A. passive attack B. masquerade C. modification of message D. replay 8. X.800 defines communicating open systems and that ensures adequate security of the systems or of data transfers. _as a service that is provided by a protocol layer of A. replay B. integrity C. authenticity D. security service is a professional membership society with worldwide organizational and individual membership that provides leadership in addressing issues that confront the future of the Internet and is the organization home for the groups responsible for Internet infrastructure standards, including the IETF and the IAB. A. ITU-T B. ISO C. FIPS D. ISOC 9.
Principles of Information Security (MindTap Course List)
6th Edition
ISBN:9781337102063
Author:Michael E. Whitman, Herbert J. Mattord
Publisher:Michael E. Whitman, Herbert J. Mattord
Chapter4: Planning For Security
Section: Chapter Questions
Problem 3E
Related questions
Question
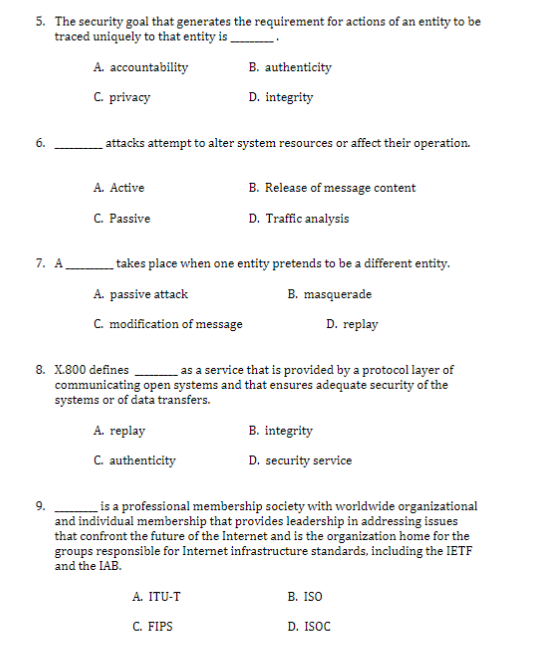
Transcribed Image Text:5. The security goal that generates the requirement for actions of an entity to be
traced uniquely to that entity is,
A. accountability
B. authenticity
C. privacy
D. integrity
6.
attacks attempt to alter system resources or affect their operation.
A. Active
B. Release of message content
C. Passive
D. Traffic analysis
7. A takes place when one entity pretends to be a different entity.
A. passive attack
B. masquerade
C. modification of message
D. replay
8. X.800 defines
communicating open systems and that ensures adequate security of the
systems or of data transfers.
as a service that is provided by a protocol layer of
A. replay
B. integrity
C. authenticity
D. security service
9.
is a professional membership society with worldwide organizational
and individual membership that provides leadership in addressing issues
that confront the future of the Internet and is the organization home for the
groups responsible for Internet infrastructure standards, including the IETF
and the IAB.
В. ISO
A. ITU-T
C. FIPS
D. ISOC
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning