5.) T(n) = 2T (n/6) + √n f(n) = versus nog a = Which is growing faster: f(n) or nlogs a? Which case of the Master Theorem does that potentially put us in? If you're potentially in case one or three, is it possible to find an epsilon which makes either f(n) € O(noga-) (if you're in case one) or f(n) = (nloa+e) (if you're in case three) true? Choose one or show an inequality. If you're potentially in case three and there is an e, try to find a constant d < 1 such that af (n/b) ≤ df (n) for large enough n's. What can you conclude?
5.) T(n) = 2T (n/6) + √n f(n) = versus nog a = Which is growing faster: f(n) or nlogs a? Which case of the Master Theorem does that potentially put us in? If you're potentially in case one or three, is it possible to find an epsilon which makes either f(n) € O(noga-) (if you're in case one) or f(n) = (nloa+e) (if you're in case three) true? Choose one or show an inequality. If you're potentially in case three and there is an e, try to find a constant d < 1 such that af (n/b) ≤ df (n) for large enough n's. What can you conclude?
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter11: Nonlinear Programming
Section: Chapter Questions
Problem 14RP
Related questions
Question
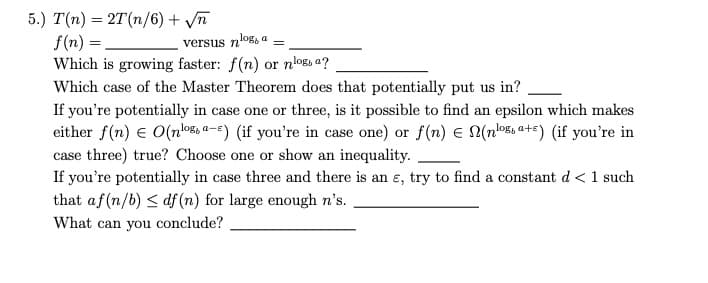
Transcribed Image Text:5.) T(n) = 2T (n/6) + √n
f(n) =
Which is growing faster: f(n) or nlogs a?
Which case of the Master Theorem does that potentially put us in?
log, a
versus n'
=
If you're potentially in case one or three, is it possible to find an epsilon which makes
either f(n) = O(nosa-) (if you're in case one) or f(n) € (nosa+) (if you're in
case three) true? Choose one or show an inequality.
If you're potentially in case three and there is an e, try to find a constant d < 1 such
that af (n/b) ≤ df (n) for large enough n's.
What can you conclude?
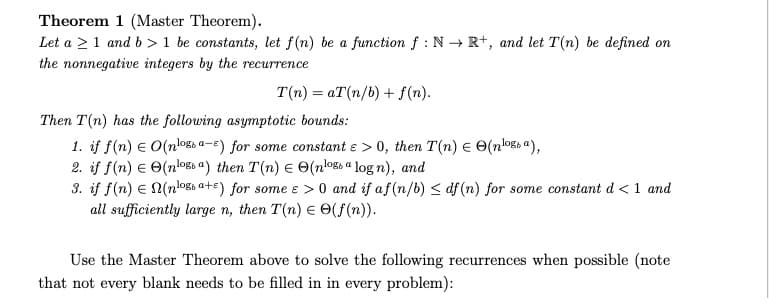
Transcribed Image Text:Theorem 1 (Master Theorem).
Let a ≥ 1 and b> 1 be constants, let f(n) be a function f: N→ R+, and let T(n) be defined on
the nonnegative integers by the recurrence
T(n)= aT(n/b) + f(n).
Then T(n) has the following asymptotic bounds:
1. if f(n) = O(nlogs a-E) for some constant e > 0, then T(n) = (nossa),
2. if f(n) = (nlos a) then T(n) = (nloga log n), and
3. if f(n) = N(n¹og a+s) for some e > 0 and if af (n/b) ≤df (n) for some constant d < 1 and
all sufficiently large n, then T(n) = (f(n)).
Use the Master Theorem above to solve the following recurrences when possible (note
that not every blank needs to be filled in in every problem):
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole