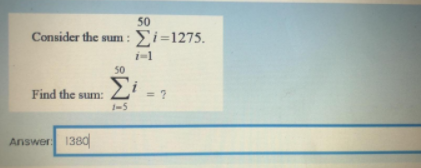
50 Consider the sum: Σ1-1275 50 Σ Find the sum: 1-5 Answer 1380
Q: Mention the differences between the "Power System Planning Studies" and "Power System Operation Stud...
A: answer is
Q: How QPI can ensure data transfer of 8 GBPS with operation speed of 6GT/sec?
A: Answer : If instead you want to convert PCIe 2.x performances: PCIe 2.0 1x can handle up to: 5GT/s (...
Q: using python Use a Lambda function to take a list of numbers and get the square root of each number...
A: The question is to create a lambda function in python.
Q: Question 7. Is the following network structurally balanced? Explain your answer. If it is structural...
A: Below step shows whether the given graph is structurally balanced or not. If it is balanced, then al...
Q: 2. Let R be the binary relation on A= {a, b, c} with the graphical representation shown below: a Ind...
A: To check reflexive, symmetric and transitive nature of graph.
Q: Consider the following pseudocode below (where A is an array of size N). Identify and explain any pr...
A: Given pseudocode: for i < 0 to N { If (A[i]>A[i+1]) { Swap (A[i]. A [i+1]) }}
Q: eded to set up IPsec between two comput
A: Below software is needed to set up IPsec between two computers
Q: Access to the internet and information technologies has widened the social class divide. Explain the...
A: Introduction : The digital gap refers to the discrepancy in access to information technology among d...
Q: What is the importance of HTML Post and Get Method?
A: In the message body of HTTP POST requests, the client (browser) sends additional data to the server....
Q: multiplies two unsigned integers without using MUL or iMUL commands.
A: C code: int multiply(int x, int y) { if(y == 0) return 0; if(y > 0 ) ...
Q: What will be the implementation of motivational strategies to boost employees performance
A: Solution: The way we communicates and interact with the employees will have the big impact on the mo...
Q: Suppose you have a RISC machine with a 2.7 GHz clock (i.e., the clock ticks 2.7 billion times per se...
A: The answer is
Q: Consider the following nested while loop a = 0 while a < 1000: b = 1 while b <= 1000: print(a,b) b =...
A: Please find the answer below :
Q: Use Java multi-threading to calculate the expression: (n!) / 2. 1. Create a method called factorial ...
A: Introduction
Q: Cloud computing has the potential to have a substantial impact on the broader community. Is it possi...
A: Introduction: Cloud computing is the use of the internet to access resources such as programs, ser...
Q: ximum number of vertices in a full binary tree of height 3 is O 9 • 15 O 16 8.
A:
Q: What is the purpose of an IP address mask? Suppose an IP address is identified as 200.60.40.88/24. W...
A: The answer is
Q: How do you verify that each machine in an IPsec network utilizes its own private key pair while usin...
A: Introduction: IPsec is a network security protocol that is used to encrypt sensitive data, such as f...
Q: Show that in a tree, any edge is a bridge
A: Introduction of a graph We all know a basic thing is that a graph which creates a connection in betw...
Q: H.W:- Find the deteminant for the following matrices: 2 3 5. B =0 -2 answer: [B| = -20 -21
A: Here is the detailed explanation of the solution
Q: Explain how the fetch-decode-execute cycle works. What is occurring in the different registers shoul...
A: The program counter stores the address of each instruction and tells the CPU in what order they shou...
Q: Give an example of each of the following or explain why no such example exists. a) A graph that is ...
A: Answer :
Q: Use the screenshot below to code a Depth-first search (DFS) algorithm in C++. Please explain what ea...
A: About DFS: Depth-first search is an algorithm for traversing or searching tree or graph data structu...
Q: List the reasons why a company would want and why they would not want firewalls for physical securit...
A: The Answer is
Q: I mean these Instructions: BSF, BCF, MOVLW, MOVWF, CLRW, BTFSS, GOTO, RETURN ,DECF, ... etc Thank yo...
A: 1. BSF Bit Set F Bit ‘b’ in register ‘f’ is set Syntax: [ label ] BSF f,b Operation: 1 → (f<...
Q: What is the network portion of the address 172.16.30.5/16?
A: answer is
Q: Given three arrays a=[1 2 3; -1 -2 -3], b=[2;4;6] and c=[0 5 7]. Write one single statement in MATLA...
A: Use the following code to Define the given Arrays Initially : a = [1 , 2 , 3 ; -1 , -2 , -3] b = [2...
Q: Start the program.Declare the pid and get the pid by using the getpid() method.Create a child proces...
A: Introduction Start the program.Declare the pid and get the pid by using the getpid() method.Create...
Q: What are the similarities and differences between authentication and authorisation. When it comes to...
A: Authentication and authorisation are both used to provide access.
Q: ) Accept 3 inputs 1. A vector of structs containing the 2. The name of the field as a chara 3. A num...
A: Write a C++ program to calculate earnings of the employee and calculate the income tax to be paid.
Q: Read the following main class. Try to guess what will be its output. class Test { public static vo...
A: The output of the program is as follows: I am in Main thread.
Q: Which of the following statements correctly describe a Python dictionary? Select all that apply. The...
A: Answer. The keys in a dictionary are unique
Q: Two channels one with a bit rate of 190Kbps and another with a bit rate of 180 Kbps are to be multip...
A: The answer is
Q: What are the three classes of procedural programming languages? Give each a short definition.
A: answer is
Q: Explain the display method or mechanism
A: The answer has given below:
Q: Define/Explain the topic fully and identify the role that particular term, concept, or analysis play...
A: Given: Define/Explain the topic fully and identify the role that particular term, concept, or ana...
Q: Convert the following hexadecimal expansion ( CA2 )16 to an octal expansion. Please break this one...
A: Steps: 1. First convert the given hexadecimal to binary 2. Now convert binary to octal
Q: Write a function, to be included in a sorted linked list class, called smaller, that will receive an...
A: Answer is given below-
Q: As the advancement of technology, particularly the internet, improves the life of humanity in genera...
A: Part(1) Computer security strategies are rarely considered until a problem emerges, at which point ...
Q: A sphere has a radius of 24 cm. A rectangular prism (shown above) has sides of a, a/2 and a/4.
A: % given radius 24cm r = 24; % we know volume of prinms is l * b * h % so a * a/2 * a/4 == a^3/8 % he...
Q: re reliant on cloud computing. We could create a massive data cluster with the required number of no...
A: The infrastructure of the Big Data Cluster has become more reliant on cloud computing. We could cr...
Q: consider 3 hosts (A , B and C) where A is running 3-TCP process, B has 1-TCP process and Cis running...
A: The answer is
Q: Types of Information System that APPLE INC (AAPL) use?
A: Business work is quickly changing and sitting tight for nobody those organizations who need to be ...
Q: Disk drive "random access device" is a misnomer, in your opinion
A: Yes,it can be misnomer to use random access device for disk drive. The main and the most important...
Q: e time complexity (in milliseconds) of each letter of the given program segment below, then get the ...
A: Given : int main( ) { int a, b, c, d; for (a=0;a<10;a++) for (b=0;b<10;b++) ...
Q: Use RMS and EDF to schedule the real-time processes in the table below. Draw and compare the schedul...
A: RMS:
Q: LVE IN MATLAB. How would I write the code to solve this in matlab?
A: It is defined as a programming language developed by MathWorks. It started out as a matrix programmi...
Q: Compute for the time complexity (in milliseconds) of each letter of the given program segment below,...
A:
Q: Which of these graphs are trees?
A: - We need to select the graphs which are trees. - The options :: In the first option we see 2 di...
Q: Which of the following is not an example of ?system software Language Translator Word Processors Uti...
A: Explanation given below :
Step by step
Solved in 2 steps

- A = [1 1; 1 -1];b = [80; 20]; A_inverse = inv(A);x = A\b; disp('A inverse is');disp(A_inverse);disp(['x1 is ', num2str(x(1)), ' and x2 is ', num2str(x(2))]); if isequal(round(x), [50; 30]) disp('Success');else disp('Incorrect: Please try again');end. Output matlab. .Hand written answer plzzPlease help 2. Please make the epsilon-NFA for the following RE:(a | b) ? a(b|ab)*

