6. Assume that the full name is written in the form of first name, middle name (optional), last name. Example: Minh Van Nguyen. Get 5 full names then find the first names and print them out in one line as below. Here is a sample run: Enter full name 1: John Doe Enter full name 2: Andrew Smith Enter full name 3: Mike James Austin Enter full name 4: Duy Thien Pham Dang Enter full name 5: Minh Ngọc Dinh The first names are John, Andrew, Mike, Duy, and Minh.
Q: https://apnews.com/article/technology-social-media-hacking-73a37d3f1e67ec5832ccd10a8e02c7e6 After…
A: Answer: Our guidelines is the answer the first three question from the first question So we will see…
Q: Describe what the terms CRUD and RESTful imply.
A: CRUD stands for Create, Read, Update, and Delete.
Q: Some magnetic disk-based databases only utilize the outside tracks of the disks, leaving the inside…
A: The information stored on a magnetic disc, a sort of secondary memory, is contained on a flat disc…
Q: An organization has a class C network 196.10.10 and wants to for departments, which host as follows:
A: The answer is
Q: write algorithm: Input: Parameters for the GA. Output: Population of solutions, P. Each of these…
A: Input: Parameters for the GA.Output: Population of solutions, P. Each of these solutions can be used…
Q: In lecture 5 we discussed statements that are valid and inconsistent. Are the following statements…
A: a. A+ negation A b. A+B c. negation B AND B ANDNEGATION B d. negation A AND (A OR B) AND NEGATION B
Q: Can I apply data structure like Queue in creating a Java GUI like queue system?
A: The question has been answered in step2
Q: NW_Q3) IP addressing operates at the network layer (Layer 3) of OSI, IP addresses must be able to…
A: IP address A device can be identified by its IP address on the local network or the internet.…
Q: What TextAlign values are available?
A: TextAlign property values that may be used: If the text in the label is positioned at the top and…
Q: It is possible to have a schema and a decomposition that were not produced by the process, are in…
A: Introduction: It is feasible to have a lossless decomposition into 3NF itself instead of BCNF. It is…
Q: In terms of cryptography, what precisely separates a private key from a public key?
A: the distinction in cryptography between a private key and a public key
Q: A new architecture, with N layers, is proposed. User application at the top layer generates a…
A: Answer:-
Q: 5.1 Calculate EAX* 24 using binary multiplication
A: The answer to the question is given below:
Q: List and explain the safeguards that businesses use to preserve the integrity of their partners,…
A: Introduction The essential objective of embracing Hierarchical Integrity, which incorporates the…
Q: 9 Q1: Based on Hill cipher algorithm, if the key is 8 5 Lo uppercase in addition to the following…
A: Given that,for Hill cipher algorithms, Key is 56789-1056 Uppercase in addition to special…
Q: 4.5 People's Weight (Java) (1) Prompt the user to enter five numbers, being five people's weights.…
A: logic:- use loop to read 5 values and store in double array. set max=arr[0] use loop from i=0 to…
Q: An actual data flow diagram differs from a conceptual data flow diagram in that the latter is more…
A: Conceptual-data-flow-diagram: A conceptual data flow diagram is one that is focused on business data…
Q: Asymmetric encryption methods, such those used in public-key cryptography, provide a wide range of…
A: Intro: Cryptography using public keys: This kind of encryption is also known as public-key…
Q: What three fundamental operations are there in cryptography?
A: Introduction: Cryptography is a data security method that protects personal data from attackers (or…
Q: What are the similarities and differences between the program?
A: The most notable difference between projects and programmes is that projects are concerned with the…
Q: The following code computes the sum of the first 10 numbers in revert order (10+9+...+1): 1-10…
A: Here is the explanation of the above output of the program. See below steps.
Q: Tell us about at least three tables that may be used to store information in a Facebook-like social…
A: Lets see the solution.
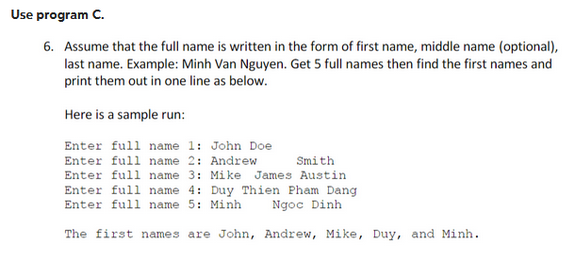
Q: Use program C. 6. Assume that the full name is written in the form of first name, middle name…
A: Here is the explanation of the above output of the program. See below steps.
Q: It is possible to have a schema and a decomposition that were not produced by the process, are in…
A: It is feasible to have a lossless decomposition into 3NF itself rather than utilising BCNF. It is…
Q: Why is hashing passwords preferable than encryption when keeping them in a secure location?
A: Introduction Passwords must be kept secure so that they cannot be accessed by an attacker, even…
Q: The usage of asymmetric encryption techniques, such public key cryptography, has several advantages.
A: Introduction: Asymmetric cryptography benefits Authenticates messages Practical... It's…
Q: What precisely are the distinctions between MIME and S/MIME in the context of cryptography?
A: Introduction: S/MIME (Secure/Multipurpose Internet Mail Extensions) permits securely signed and…
Q: I don't believe there is much of a difference between the two types of cryptography.
A: Introduction: The study of cryptography focuses on the development of secure communication…
Q: One of the characteristics of big data is the variety of the data. Justify the usage of languages…
A: Huge Data Big data is a collection of organised, semistructured, and unstructured business data that…
Q: What distinguishes local user authentication from remote user authentication? Which one of the two…
A: The answer of the question is given below
Q: What trade-offs do buffer trees have in comparison to LSM trees?
A: The LSM tree uses an algorithm that defers and batches index updates. This technique cascades the…
Q: List each possible value for the BackgroundImageLayout property on a form.
A: A form's BackgroundImageLayout attribute may take on a several different values, including: The…
Q: Was ASCII designed with a specific use in mind?
A: We have to explain that ASCII was designed with a specific use in mind?
Q: Why is scrubbing important in RAID systems and what does it entail?
A: Introduction: Data scrubbing: Data scrubbing is also called data cleaning which completely suggests…
Q: How does IP spoofing operate? What is it? Does IP spoofing pose a security threat?
A: IP Spoofing IP spoofing is the process of creating false source Internet Packet (IP) address tp…
Q: 12. If some resources have only a single instance, then we can use the wait-for graph. True False
A: wait for graph: This graph is used to avoid deadlock and identify the deadlock.
Q: Describe the applications of motion input in the sports, entertainment, and medical sectors.
A: Gesture input is often used to refer to motion input. Users that utilise motion input or gesture…
Q: An essential component of modern computers is cache memory. Describe the purpose of cache memory and…
A: Introduction In this question we have asked about the cache memory and Describe the purpose of cache…
Q: Show off your understanding of prototyping.
A: In this question we have to understand the prototyping. Let's understand
Q: Explain why the concept of mutual exclusion (ME) is seen as a crucial mechanism for an operating…
A: As a key mechanism, mutual exclusion Mutual exclusion is a property used to control concurrent…
Q: In terms of cryptography, what precisely separates a private key from a public key?
A: Introduction: the following describes the difference between a secret key and a public key in…
Q: iii) Write a Java program to find the count of binary elements in the array given below. int…
A: We are given an array elements [] with some elements and we are asked to write a java program to…
Q: Examine the relationship between network and computer security and the various forms of malware. Is…
A: Introduction: To ensure confidentiality, integrity, and availability in a system environment, a user…
Q: Explain why the concept of mutual exclusion (ME) is seen as a crucial mechanism for an operating…
A: Your answer is given below. Introduction :- A programme object called a mutual exclusion (mutex)…
Q: What techniques are used to combat resource hogging?
A: What is a resource of hogging in Computer/Operating systems? This is when the operating system is…
Q: Describe the distinctions between a decision support system's capabilities and a manager's ability…
A: Management Information System: The study of people, technology, organizations, and their…
Q: What three key performance indicators (KPIs) may a medical or dental office use to gauge how well a…
A: Below are the three key performance indicators (KPI); Key performance indicators (KPIs) are a…
Q: What advantages and challenges does the business world face as a consequence of the paradigm shift…
A: Introduction: Most essential, consider what a paradigm shift is: It reflects a profound…
Q: What are a few real-world uses for Splay tree?
A: Definition Playing tree One kind of binary search tree is the splay tree. In this, the most recent…
Q: Tell us about at least three tables that may be used to store information in a Facebook-like social…
A: Tables: The table is the most significant of the many components that make up a relational database.…
Step by step
Solved in 4 steps with 3 images

- Write a program, USING C, to read and display the information employees in a group. Then edit the details of the employee and redisplay the entire information. Here is the list of 3 employees in a group: Employee ID Employee name Experience Salary Department 5561 Richard 1 68000 Product Development 5562 Callum 2 100000 Product Development 5563 Elon 4 150000 Product Development Your Code should generate the following output for each of the employees. Example: ********DETAILS OF Employee 1******* Employee ID = 5561 Employee Name = Richard Salary = 68000 Experience = 1 Department = Product Development Richard started learning Data Structure well and applied for a different position in the same company. He was chosen for the new role under a different department. As a result, his salary raised to 200000 and his new Department is Data Science. Modify the details of Richard and…1. Write a Python regex pattern that matches a valid email address, assuming that an email address consists of a username, followed by the "@" symbol, followed by a domain name, which in turn consists of one or more subdomains separated by dots, and ending with a top-level domain (e.g., .com, .org, .edu, etc.). 2. Using the re.findall() function in Python, write a Python code snippet that takes the text string and the regex pattern from Q4 and returns a list of all the email addresses found in the string. 3. Suppose you want to modify the regex pattern from Q4 to also match email addresses that contain hyphens ("-") in the username and/or domain name. What changes would you make to the pattern, and why? 4. Using the modified regex pattern from Q6, write a Python code snippet that takes the text string and the modified regex pattern, and returns a list of all the email addresses found in the string. Note: You can assume that the text string contains valid email addresses separated by…FOR C++, PLEASE SEND THE CODE IN 30 MINUTES. WRITE THE ANSER OF THIS QUESTION IN THE GIVEN CODE. Write a function that checks whether the furniture is in good quality. Assume that it is in good quality if the average quality of the materials exceeds 0.5. #include <iostream>#include <string>#include <vector> using namespace std; class Material { private: string name; int amount; float quality; public: Material() { } Material(string name, int amount, float quality) { this->name = name; this->amount = amount; this->quality = quality; } string getName() { return this->name; } int getAmount() { return this->amount; } float getQuality() { return this->quality; } void print() { cout << "Name: " << this->name << " Amount: " << this->amount << " Quality: " << this->quality << endl; }}; bool…
- write a C++ program. In the heyday of the British empire, Great Britain used a monetary system based on pounds, shillings, and pence. There were 20 shillings to a pound, and 12 pence to a shilling. The notation for this old system used the pound sign, £, and two decimal points, so that, for example, £5.2.8 meant 5 pounds, 2 shillings, and 8 pence. (Pence is the plural of penny.) The new monetary system, introduced in the 1950s, consists of only pounds and pence, with 100 pence to a pound (like U.S. dollars and cents). We’ll call this new system decimal pounds. Thus £5.2.8 in the old notation is £5.13 in decimal pounds (actually £5.1333333). Write a program to convert the old pounds-shillings-pence format to decimal pounds. An example of the user’s interaction with the program would be:Enter Pounds:7Enter Shillings:17Enter Pence: 9Decimal Pounds: £7.89(C++) Write a program with total change amount as an integer input, and output the change using the fewest coins, one coin type per line. The coin types are Dollars, Quarters, Dimes, Nickels, and Pennies. Use singular and plural coin names as appropriate, like 1 Penny vs. 2 PenniesThis is for c++. I need a program that asks whether any members of your party are vegetarian, vegan, or gluten-free, then displays only the restaurants that you may take the group to.
- In C++, Write a program that asks a user to input five numbers on the same line separated by spaces, then do the following:a. Print out the five numbers (with spaces or tabs between them).b. Calculate and print the sum, average, and product of the numbers.Write a C++ program to read two lengths l1, l2 in the form of meters and centimetres by using a class length. Add these two lengths and return the result to another length l3. Hint: 1 meter=100 centimetre (same as in lecture notes feet and inches program)Using C++, write a whole program to ask the user for his/her name, age, and gpa, then print on the screen "Hello NAME!, you are AGE years old and your Grade Point Average is GPA.", where NAME, AGE, and GPA are replaced by the values that the user typed.User data should be stored in a class variable of type userType, which has three private components: name of type string, age of type int, and gpa of type double.
- Write a program in C++ with total change amount as an integer input, and output the change using the fewest coins, one coin type per line. The coin types are Dollars, Quarters, Dimes, Nickels, and Pennies. Use singular and plural coin names as appropriate, like 1 Penny vs. 2 Pennies. If the input is: 0 The output should be: no change If the input is: 45 The output should be: 1 Quarter 2 Dimes only using: #include <iostream> using namespace std;Write a C program that reserves flight tickets for 150 customers to Germany. Write afunction RegCust that for each customer gets name, surname, Passport ID, and age. If the age ofthe customer is less than 18 years old, the customer is not allowed to buy a ticket and the programmust show a warning message to the user. Write another function ResTCKT that reserves thetickets by saving the Passport ID and seat number for the customers. Seat numbers must beassigned randomly between 1 and 150 with no repeating random number. Write a third functionPrintTCKT that shows the complete name of customers and their seat number as tabular formatshown below. You need to use array of structures and pointers for implementation of thisprogram.Struct Customer{char *name;char *surname;int passID;int age;} Custs[150]; Struct Ticket{int passID;int seatNum;} TCKT[150];You must implement a C++ program that calculates the position and velocity of a body thrown with an initial velocity (v0) and with an angle to the horizontal (angle). The results should be displayed on the screen every some time (0.1 seconds) in a horizontal row. To validate your program, use the following example run where v0=10 and angle=53o as shown in the image: The data must be printed with two decimal places, find out how to do this in C++.Once all the calculations are printed, the program must ask if you want to repeat or if you want to exit the program. You implement the way to do it.As always the report should include (use the standard report): Cover page with title, course and section, names and student numbers of your team members in alphabetical order by last name.Introduction indicating in one paragraph what the program does and pseudocode/algorithm of the program. Detailed flowchart. Source code. Pictures of a running example. Next, the theory of ballistics problems:…

