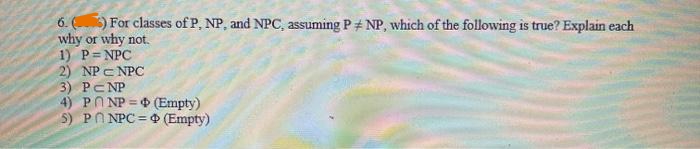
6. () For classes of P, NP, and NPC, assuming PNP, which of the following is true? Explain each why or why not. 1) P=NPC 2) NPC NPC 3) PCNP 4) PNP = (Empty) 5) PNPC = (Empty)
Q: I'm curious to know more about multifactor authentication. How does it help to keep passwords safe…
A: The Approach: Authorization is subject to a variety of conditions, like as The user must provide…
Q: Write a program to do linear search for an integer number in an array of 20 distinct numbers. The…
A: Given Question: To write a C++ Program.
Q: You should next discuss THREE different types of computing environments that exist in this…
A: Computing Environments: When a problem is solved by a computer, throughout that process, the…
Q: What is the execution of the following co mport math K-4 Y=math.pow(X,2) print (Y)
A: It is defined as an interpreted, object-oriented, high-level programming language with dynamic…
Q: what happens when people do illegal things online and how they do it. How can you make sure you…
A: Computers and online networks are involved in cybercrime: It is not impossible that a crime was…
Q: In your opinion, what is the most crucial component of the transition to a batch processing system?…
A: Introduction: For businesses and organisations to effectively manage massive amounts of data, batch…
Q: Data, address, and control buses are distinct from one other.
A: Answer:
Q: The task is to use structures and arrays, make a list of 30 students and store their information in…
A: Note: As no language is specified, the below code is in python language. Start. Read the inputs.…
Q: Discuss the importance of agile development and identify its four core values. – – –
A: It is important to use Agile development: Stakeholders should be involved in the process.…
Q: What steps would you take if you were troubleshooting a computer bug?
A: Required: What steps would you take to troubleshoot a computer problem code? No operating system or…
Q: Explain the need of creating both user and technical documentation for software in three simple…
A: Why is user documentation crucial? Anyone who is expected to utilise the system will benefit from…
Q: XYZ school has the following grading policy: If mark is less than or equal to 50, the student gets…
A: Algorithm: Firstly we will take the input from the user Then we will check on the output as per the…
Q: Make sure to include information about how Personal Operating Solutions will share personal data…
A: Personal Operating Solutions's privacy policy is as follows: Personal Operating Solutions gathers…
Q: Is agile development best suited to what sorts of systems?
A: Agile is an iterative method to project management and software development that enables teams to…
Q: which of the following IP address is a class A address? a. 200.121.199.100 b. 100.121.3.4 c.…
A: Divison of ip address:- Class A:- 0-127 Class B:- 128-191 Class C:- 192-223 Class D:- 224-239…
Q: A certain grade of steel is graded according to the following conditions: (i) Hardness must be…
A: Let in the following code, h = Hardness of steel cc = Carbon content ts = Tensile strength…
Q: Analyze the results of any yearly or company-sponsored surveys on the adoption of an agile…
A: Agile model: The phrase "Agile approach" refers to a technique that promotes iterative software…
Q: How can a computer accomplish multitasking in a single machine scenario? Explanation utilising a…
A: Multitasking is the execution of numerous tasks (also known as processes) simultaneously over a…
Q: Write a program that accepts an input grade percentile form and output its grade equivalent; based…
A: #include<stdio.h>int main(){ // variables int score; double grade; // take score…
Q: These values when define in the program cannot be manipulated or be changed to another value? A.…
A: Find the answer with reason given as below :
Q: Write a program to do linear search for an integer number in an array of 20 distinct numbers. The…
A: 1) Since you have not specified programming language, I hvae written program in C. 2) Program to do…
Q: In the search method of a circular list, care must be taken to store the pointer (or reference) of…
A: The question is to comment on the given statement: In the search method of a circular list, care…
Q: An Abstract Data Type's interface is comprised of what? Here's where you put your reply.
A: Abstract Data type (ADT) is a class or type for objects whose behaviour is specified by a collection…
Q: Virtual Address S ry with page siz size is 4 bytes ar ago the numbo
A:
Q: Why aren't safety measures like banning, blocking, and deleting accounts on any given social media…
A: Cyberbullying bullying refers to the use of digital technology to harm other people. This often…
Q: is a database system that is impervious to failure. Does this system need the recovery manager? Why?
A: Website Acquisition Manager In the event of data loss, performance failure, disk failure, or system…
Q: drink
A: Having an online presence is advantageous for almost all businesses. But before you hastily publish…
Q: What is static variable and static method? Explain why main method in java is always static.
A: Find the required answer given as below :
Q: Keep in mind the possible reactions of computer and mobile device users when there are issues with…
A: Foundation: Any portable computer may be referred to by this term; they are designed to be tiny…
Q: You may tell me what's different between the UML model and EER model by comparing them. How has the…
A: UML and ERDs are both used by software developers to map out software systems and databases before…
Q: Security, cybercrime, personal privacy, social interaction and governance are only few of the areas…
A: Organizations and individuals that use computers may express their expectations for system trust and…
Q: What are some of the advantages and disadvantages of using convolutional neural networks (CNN)?…
A: CNN's key advantage over its predecessors is its ability to recognise essential characteristics…
Q: (S), Il ally, I ) #include main() { int x[5], *y,z[5] for(i=0;i void main(){ int x,y; cin>>x; for…
A: Answer is given below. (i) Will encounter a following syntax error(s): The variable ‘i’ is not…
Q: Give people a chance to talk about how they use tablet computers and smartphones at work.
A: Tablets Computers: Yes, cellphones and tablets are classified as computers. A computer is any device…
Q: Python programming language. The chef gets into trouble and asks his mathematician to calculate the…
A: The Answer start from step-2.
Q: There is a general review of virtualisation and the many forms it might take (Language, Operating…
A: Virtualization is a practise that has become quite common in the growth of IT firms. The economics…
Q: The designer may mould and shape rather than create an item using a sequence of lines when employing…
A: That's why: Instead of constructing an item from a set of lines, the designer may moulds and form it…
Q: Write brief notes on the following process concepts. (Mention what they are and give examples where…
A: The question has been answered in step2
Q: Which of the following is true about Procedural-Oriented Programming? A.lt is bottom-up approach…
A: 1) Procedural-Oriented Programming is derived from structured programming, based upon the concept…
Q: What is the execution of the following code? The programming language is Python What is the…
A: We know programming language used is Python, hence we are using python online compiler to compile…
Q: As far as I know, this is the only way to explain the kernel components of an operating system.
A: The kernel is a piece of software that runs at the heart of an operating system on a computer and…
Q: 1. Consider the following instruction: Instruction: AND Rd, Rs. Rt Interpretation: Reg[Rd]= Reg[Rs]…
A: a) ALU Operation is AND,BSrc will look to register,OpSel will tell ALU to perform AND. MemW is…
Q: Design a GUI for Book view class for the following Library Information System, which you have…
A: Library item Design and Testing Program : Library Item.java public class LibraryItem { private…
Q: When does a person start thrashing? What is the system's mechanism for detecting thrashing? Is there…
A: Given Question: When does someone begin to thrash? What technique does the system use to recognize…
Q: Because of their inherent features, wireless networks face a broad variety of challenges. Define…
A: Given: Wireless networks are critical to the success of today's industrial businesses. Technology…
Q: Sequential and direct access are two methods for finding data in memory. Who gains from immediate…
A: The Solution: Instead of needing to start over, direct access data can be read immediately. When…
Q: What exactly is it that we mean when we say "hybrid language"?
A: Hybrid programming language: Many programming languages can share the same code sheet when using a…
Q: Tony is great cook and a great mathematician. When a chef gets caught in any trouble, he asks his…
A: Answer: Algorithm Step1: we have define fibsum() function to input start and end point Step2: then…
Q: Succinct or quick access may be made to data stored in memory. Why has direct access become so…
A: Two methods access memory data: directly and successively Data may be accessed promptly by using the…
Q: a с user defined Write function that take an array and a value which you want to find in the array.…
A: Step-1: StartStep-2: Declare two variable n and valueStep-3: Take input size of array and store in…
Step by step
Solved in 2 steps with 2 images

- 1. Name five of your favorite fictional/anime character. Let A be the set containing these characters, and B be the set containing your age, last name, favorite number, and expected grade in this course. Take X= A U B. Do the following: [ Set A = {Iron Man, Scarlet Witch, Thor, Shinichi, Ran} , Set B= {21, Melgar, 14, 70}] b. Enumerate the equivalence classes induced by the equivalence relation ρ. Use the roster method in writing each class.[21:46, 2020年12月8日] Antoni: The following class Pizza has incomplete codes. Write setter and getter methods for all instance variables of this class. In addition, complete the missing lines of codes for the given default constructor method and isLargePizza () method.[21:47, 2020年12月8日] Antoni: class Pizza { private string name; private double diameter; public Pizza () { //Missing lines of codes to be completed by the student } public boolean isLargePizza() { //Missing lines of codes to be completed by the student } //Missing lines of codes to be completed by the student }//end class definition Hint: When the diameter of a pizza is more than 20cm, then it is considered to be a Large Pizza. The method isLargePizza () has to return a boolean value indicating whether the Pizza object is a large pizza or not. Note: You must add required member functions or data members/variables in your program to complete its execution.in c++ write aprogram to Create a class Rectangle with length and breadth as private data members and also provide the following member functions: getdata(): gets the length and breadth of rectangle. calarea(): return the area of the rectangle. calperi(): return the perimeter of the rectangle. issquare(): return true if the rectangle is square
- Suppose that you have the declarations of Exercise 7. Write the definitions of the member functions of the classes circle and cylinder. Identify the member functions of the class cylinder that overrides the member functions of the class circle. (2, 3, 4)11-Define the following:(Python) i- OOP ii- Class iii- Class instance iv- ___init()__ function v- Self parameter[2/25, 05:28] Vishal Singh Rawat: Kindly store employee details using class with python program [2/25, 05:28] Vishal Singh Rawat: There are 4 employees Details of all employee: Name: John , Designation: Manager , Salary: 80000 Name: Mike , Designation: Team Leader , Salary: 50000 Name: Derek , Designation: Programmer , Salary: 30000 Designation: Assistant , Salary: 25000 Name: Raj
- Let l(x) be "x has an internet conection" and C(x, y) be "x and y have chatted over the internet". Assume the domain is all students in a class. Express the following using quantifiers. 1. Jerry does not have an internet connection 2. Exactly one student in the class has an internet connection 3. Someone in your class has an internet connection but has not chatted with anyone else in the class.c++ Implement a MyInt class. An object in the MyInt class must be able to hold a single dynamically allocated integer. MyInt should have the following members: A member variable ptr of type int *.A parameterized constructor that takes nums of type int as input parameters.A destructor.A superimposed assignment operator (). The copy must be deep.A function set that sets the value of the number.A function get that returns the value of the number.The members must be encapsulated in accordance with the convention. Memory leaks must be avoided. To test your class, create objects and call functions according to the comments below. All tests must be validated. Input Expected output5 11 27 5 11 271 2 3 1 2 319 21 30 19 21 30Describe a class's public and private members.
- C++ implement a class car.car shall have the following membersa member variable model_year of type int.a member variable model_name of type std :: stringa parameterized constructor that takes both member variables as input parametersa function to retrieve model_yeara function for to retrieve model_name members' visibility must follow the usual convention overlay the outflow operator (<<) for class car.input follows the format[model_year] [model_name] output must have format:Model: [model_name], produced: [model_year] example:input: 2015 PeugeotOutput; Model: Peugeot, produced: 2015C++ Implement a Rational Number class with the following specifications. Data members a) numerator and denominator Functions a) Constructors: 1) default constructor 2) single parameter constructor to create numerator/1 3) dual parameter constructor to create numerator/denominator 4) Use constructor delegation across all constructors. b) Accessors and Mutators for both data members. c) Static recursive GCD function using Euclid’s algorithm. d) Static LCM function for two numbers. e) Reduce function simplify a rational number. This function modifies its calling object. f) Your program should work with the supplied driver program Notes LCM (Least Common Multiple) This function returns the smallest multiple of a and b. Step 1: Multiply a and b to find a common multiple. Step 2: Divide the common multiple by the GCD of a and b. Step 3: Return the result of Step 2. Reduce: This function reduces a fraction to simplest terms (i.e. 9/12 to 3/4). Step 1:…6. Write an abstract class “Student” that has the attribute “name”, “id”, “cgpa”, totalFees.“Student” class has an abstract function fees(totalFees), concrete function toString().The fees function varies student to student. If any student has CGPA more than 3.90then he/she study with full free. If any student has CGPA more than 3.50 then he/sheget the 50% waiver of the total fees. The rest of the student have to pay the total fees.Design a JAVA class “CurrentStudent” that can be used in the “Student” class as localinner class to rewrite the given function. Also implement the system in main methodwith appropriate objects.

