6. Given the following directory tree structure, write the full command you can use to move the “dumpling" directory into the "asian_food" directory? Hint: You can either use the full path or the relative path. If you use the relative path you should specify where in the tree you are at currently. home. miniconda3 resequencing food asian_food dumpling mexican_food
Q: Done in C language and must use multi-threaded socket programming Create a UDP client that is able ...
A: // Server side implementation of UDP client-server model #include <stdio.h> #include <stdli...
Q: Python program that takes two values as user input, x and y; then applies the following equations ...
A: def functionForValues(x,y): return x*10 - x*3 , y*y*y* ((2 - y) * y + y) x = float(input("Enter t...
Q: Which kind of program-level parallelism (data or control) is best suited to SIMD? What kind of progr...
A: let us see the answer:- Introduction:- SIMD stands for Single Instruction/Numerous Data, and SIMD op...
Q: How is the output for frequency of a DDS changed?
A: DDS (direct digital synthesis )is used for creating waveforms while digital to analog conversion.
Q: Use a truth table to represent the following statement. Ensure that you ...
A: The truth table is a table that includes results for all conceivable input values. If we examine thr...
Q: What are the benefits and drawbacks of caching disc write operations?
A: Disk caching reduces the time it takes to read or write data from or to a hard drive. In modern comp...
Q: What do you consider to be critical infrastructure? Give three examples. Why are critical infrastruc...
A: The network of physical and virtual assets that keep our country and the world running is known as c...
Q: Using C++ common year in the modern Gregorian Calendar consists of 365 days. In reality, Earth take...
A: Logic:- check for leap year logic. If userYear%400==0 then it is leap year simply return 1 from ...
Q: Which of the following is a legal identifier? a. 1st b. legal1 c. legalidentifier! d. Le...
A: Answer : b. legal1 Rules for legal identifier : 1. Don't start with number 2. does not contain sp...
Q: Three missionaries and three cannibals are standing at one side of a river and need to be transferre...
A: Draw the state space
Q: Consider the function F(a,b,c) given attachment below a. Redraw the logic diagram using only NOR g...
A: Consider the function F(a,b,c) given attachment below a. Redraw the logic diagram using only NOR ...
Q: In terms of emphasis, what distinguishes the TPC from the SPEC?
A: Let's see the solution in the next steps
Q: 2. a. What kind of hazard may exist in clock cycle 11 and why it may exist? b. Why there is no struc...
A: Below is the answer of the above question. I hope this will be helpful.
Q: What is the time complexity of the following function- 5T(n/5+50)+n,T(1)=1 (a) θ(50logn) (b) θ(n5...
A: What is the time complexity of the following function- 5T(n/5+50)+n,T(1)=1 (a) θ(50logn) (b) θ(n...
Q: Computer Science Need Debugging following these guidelines: program produces correct output ...
A: The errors has been removed from the existing code.
Q: addre
A:
Q: Examine the advantages and disadvantages of various system models.
A: Given: We have to discuss the advantages and disadvantages of various systems models.
Q: Solve this recurrence equation T(1) = 1 T(n) = T(n/2) + bnlogn
A: Defined the complexity of the given recurrence relation
Q: In C++ Define a function named CoinFlip that returns "Heads" or "Tails" according to a random value...
A: I have provided C++ CODE along with CODE SCREENSHOT and also provided TWO OUTPUT SCREEN...
Q: Please type your answer not picture Complete the RTN for the MARIE instruction Load X.
A: Here X is stored in MAR Later MBR is stored in accumulator
Q: Is it easier for you to identify someone using their fingerprints, speech intonation, face features ...
A: INTRODUCTION: Individuals may be uniquely identified via the use of biometrics, which are measures o...
Q: Use the following schema and query plan to answer the corresponding questions S(d,e,f,g) B(S) = 1000...
A: I'm providing the answer to above question. I hope this will be helpful for you.
Q: You need to show detail work on how you get the answer. Dont use answers from other websites please...
A: Following is the RTN for the MARIE instruction Load X: The instruction retrieves datum X from memory...
Q: Consider that you hav excention 1 and 30%
A: Number of instructions that cause Exception 1: 20% of 400,000 = 80,000 Number of instructions that ...
Q: What exactly is multifactor authentication and how does it work? What role does it play in password ...
A: Introduction: Multifactor authorization is a type of security that requires the use of multiple secu...
Q: Which search engines are lawful and ethical?
A: Introduction: Which search engines are lawful and ethical?
Q: Write a program that asks the user for a negative number, then prints out the product of all the num...
A: Solution: Since any specific language for the above question is not mentioned, we have solved thi...
Q: Write a C++ program that checks if a number is Palindrome (use recursive function as you code). A pa...
A: Start define a recursive function rev that calculates reverse input integer number if reverse is eq...
Q: Comvert 253 to a numeral in base 7 253-
A: Steps Divide the number by 7 each time and store remainder. When quotient is less than 7 . Display ...
Q: What is the function of a firewall, and how can it be employed in your organisation?
A:
Q: You need to show detail work on how you get the answer. Dont use answers from other websites plea...
A: According to the information given:- We have to define the write MARIE assemble language
Q: Additionally, state briefly what you understand a file extension to be and what its purpose is. Go t...
A: The file extension, also known as a file suffix or filename extension, is the string of characters f...
Q: How is data sent from a sequentially accessed device to a device that only enables direct access??
A: Introduction: In response to your query, Sequential access is a technique for retrieving data from a...
Q: Write a small program that uses the dynamic binding. In your comments explain which statement(s) is ...
A: Answer :-
Q: Run a python command with "run" on gdb-peda$ gdb-peda$ run python -c 'print "A"*(5)' I got pytho...
A: print("A"*(5)) don't use any inverted comas after 5 .
Q: 1. What is comparator in Python? 2. What is logical operators? 3. What are input and output operat...
A: 1. What is comparator in Python? 2. What is logical operators? 3. What are input and output operator...
Q: Write a PL/SQL program using an explicit cursor that displays all patients PLCO_ID numbers from t...
A: Here we write PL/SQL program using explicit cursor : ===============================================...
Q: In the Histogram chart, edit the bin size to be 10.0 data polnts and then close the Format Axis pane...
A: The solution is given below for the above given question:
Q: Convert the binary number 101011002 to its decimal (base 10) equivalent:
A: convert binary number to decimal number binary number to 10101100
Q: implemented with a linked list. Which of these operations are likely to have a constant worst-case t...
A: insertion into a LinkedList takes place in a constant time-you just have to create a node and assign...
Q: A list of five common network topologies should be included. Which one do you think is the most trus...
A: There are six types of topology. Bus topology Ring topology Mesh topology Star topology Tree top...
Q: What exactly is multifactor authentication and how does it work? What role does it play in password ...
A: Multifactor authentication (MFA) is a kind of security solution that requires a user to provide seve...
Q: Is it easier for you to identify someone using their fingerprints, speech intonation, face features ...
A: Biometrics validation gadgets depend on actual qualities like a unique mark, facial examples, or iri...
Q: In terms of emphasis, what distinguishes the TPC from the SPEC?
A: TPC and SPEC are two terms that are used interchangeably. The Transaction Procession Council, or TPC...
Q: Which one of the following is/are true ? e" +n = 0 (n³) V(n) + n = 0 (n log (n)) n* n * n +n* 2 = N ...
A: The answer is
Q: We believe Flynn's taxonomy should be expanded by one level. What differentiates a higher-level comp...
A: Introduction: Michael J. Flynn developed Flynn's taxonomy in 1966, a categorization of computer arch...
Q: What are the five layers in the TCP/IP Internet protocol stack? What are the principal responsibilit...
A: Ans: The five layers of TCP/IP internet protocol stack is: 1) Application layer 2) Transport layer ...
Q: 14. Convert the following decimal number to negative binary number, using 2's complement in 8 bits a...
A: a) Given number is in decimal form that is: 87 Binary form of 87 is: Division Quotient Remainde...
Q: Write an 8086 assembly code (using an 8086emu) that calculates the summation of 11 data bytes (21H, ...
A: Algorithm for above program 0.Start 1.Initialise data bytes numbers to contain the given numbers 2. ...
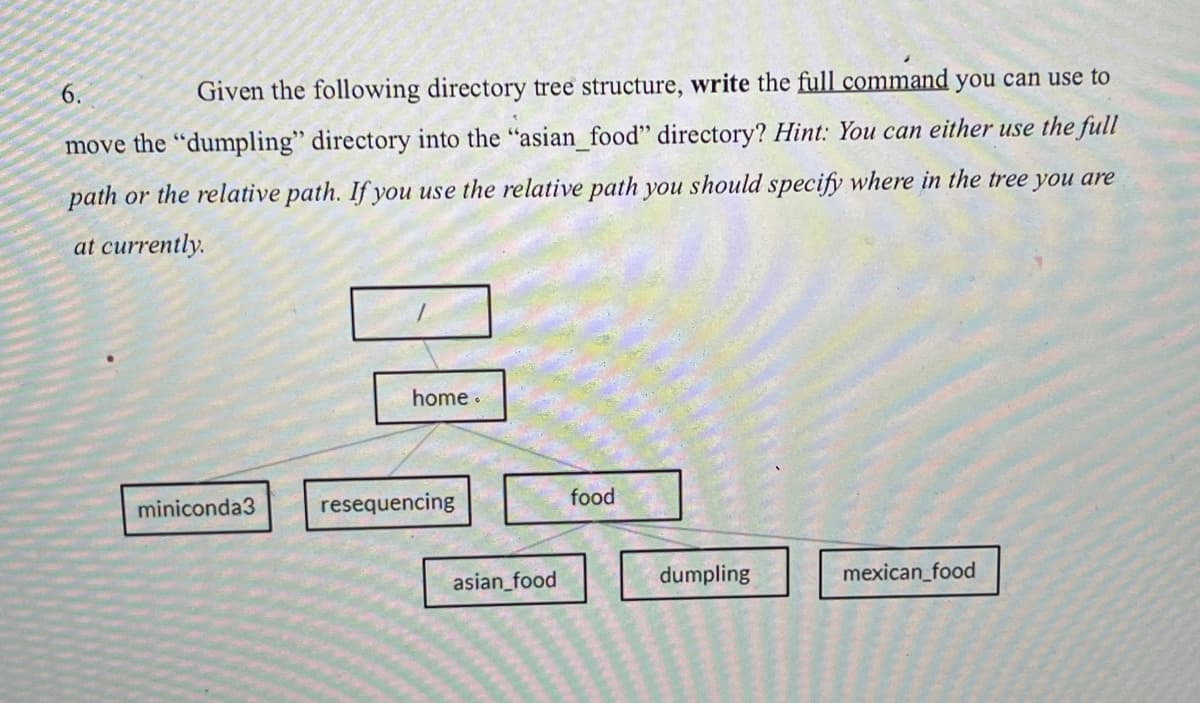
For the given question, we need to write a command that moves the "dumpling" directory to "asian_food" directory.
Here, the absolute path is used to access the directory.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- The command find . -name "*.png" will send to stdout a list of all the files in the current directory and all of its descendent directories that have a .png extension. Give a command that uses command substitution to copy all such files to the directory ~/imagesWrite the command that can be used to perform the following:a. Compress the symbolic link /root/sfile using the compress utility and display thecompression ratio.b. Compress the contents of the directory /root/dir1 using the gzip utility and displaythe compression ratio.c. Decompress the file /root/letter.bz2.d. Compress the file /root/letter using gzip fast compression.e. Find the compression ratio of the file /root/letter.gz.f. Perform a test compression of the file /root/sample using the bzip2 utility.g. Compress the file /root/sample using the bzip2 utility while minimizing memoryusage during the compression.What happens if you provide the which utility the name of a command that isn't in a directory that's in your search path?
- Hello! I need to create a new Order with an API but I can't get it to work. My code so far is: //POST (create a new record (table)) http:API, (with additional body elements, OUCU=****, password=******, client_id=1. latitude=89, longitude=-20). function orderCreated() { let data = {oucu:"xxxxxxx",password:"xxxxxxx",client_id: 1,latitude:89,longitude:-20};var formBody = [];for (var property in data) {var encodedKey = encodeURIComponent(property);var encodedValue = encodeURIComponent(data[property]);formBody.push(encodedKey + "=" + encodedValue);}formBody = formBody.join("&"); fetch('httpAPI)', {method: 'POST',headers: {'Content-Type': 'application/x-www-form-urlencoded;charset=UTF-8'},body: formBody})}; So, it must retur: {"status" : "success","data" :[{"id":"****","client_id":"***","date":*************","latitude":"****","longitude":"-******"}]}1. Write a program to ask customer what are the bucket name and folder name in AWS S3, and which local directory wish to save in AWS S3. Then create bucket and folder with given names and upload all files in the requested local directory to AWS S3.What is the result of giving the which utility the name of a command that resides in a directory that is not in your search path?
- What happens if you provide the which utility the name of a command that is not in a directory in your search path?Write a program that prompts the user for a path and displays the directory structureon the command tool as follows:def count_never_close(directorypath,list_of_locations,distance):"""return how many of the entities in the directory are never withinthe distance of any of the locations in the list.:param directorypath::param list_of_locations: list of tuples (lat,long):param distance::return: the count"""passENTITIES:ID,City,State,Latitude,LongitudeA45419E,Plattsburgh,NY,44.704021,-73.471148A19312D,Aiken,SC,33.554433,-81.69588A90172S,Tuscaloosa,AL,33.170238,-87.616169A19394D,Alexandria,VA,38.819853,-77.059645A27218D,Pittsburgh,PA,40.47441,-79.950968A68626D,Meadville,PA,41.611599,-80.114891A17494D,Allentown,PA,40.602658,-75.469236A86034S,Tonawanda,NY,42.99704,-78.878659A45142D,Asheville,NC,35.602711,-82.567281A38298S,Atlanta,GA,33.844371,-84.47405A14497Y,Roswell,GA,34.055198,-84.370475A25954D,Austin,TX,30.326374,-97.771258B46374X,Fairhope,AL,30.480713,-87.861306B52199S,Cedar…
- Given the following ls -l output: drw-r-xr-x. 2 root accounting_grp 4096 Jan 28 19:0 accounting/ What is the access permission for the ‘accounting’ folder (directory)? Write the command to change the access permission of the accounting folder (directory), so that the owner can read and execute, and the group and everybody else (world) can only read the file.In your storage space, you may find two documents with the same name. Let's pretend that the directory you're in right now is your house. To move a file named florence to a Proposals subfolder of the home directory, use the following command.Write a C++ program using Windows API to CreateDirectory – For Creating the Directory BOOL CreateDirectory(LPCSTR lpPathName, LPSECURITY_ATTRIBUTES lpSecurityAttributes ); Return Type – Boolean (TRUE or FALSE). LPCSTR – Long Pointer to constant String. lpPathName – Where your directory will reside. lpSecurityAttributes – Security for Directory and default it is NULL. If this function Fails then its return FALSE or ZERO. Also We can print the Error Information with the help of GetLastError() function. CreateDirectory Function Link.

