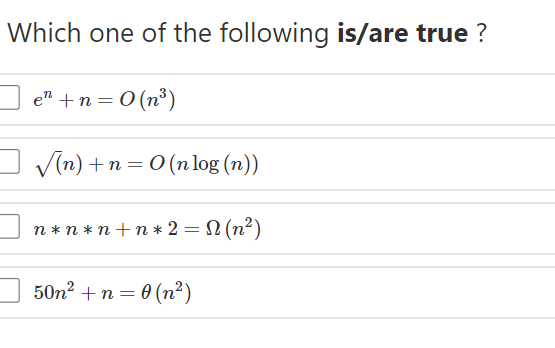
Which one of the following is/are true ? e" +n = 0 (n³) V(n) + n = 0 (n log (n)) n* n * n +n* 2 = N (n²) 50n2 + n = 0 (n²)
Q: 2. FA,B,C,D) - Σ (0,6, 8 , 13, 14) d(A,B,C,D) - Σ (2, 4, 10) %3D
A: C'D' C'D CD CD' A'B' 1 X A'B X 1 AB 1 1 AB' 1 X
Q: A. Write an Assembly program to load the register E with the value 12 and the register H with the va...
A: Assembly program to load the register E with the value 12 and the register H with the value 8, then ...
Q: *** Entity and Attributes *** · PKG_CUSTOMER CS CO CODE CS CODE VARCHAR2(4 BYTE) VARCHAR2(20 BYTE) V...
A: Answer: I have given answered in the handwritten format in brief explanation.
Q: I need help in evaluating World Wide Web (WWW) in terms of reliability in distributed system
A: The introduction of the Internet and the World Wide Web revolutionized the way academics obtain deta...
Q: 2. Expand the following recurrence to help you find a closed-form solution, and then use induction t...
A: Since you have asked multiple questions, we will solve the first question for you. If you want any...
Q: Creating systems that provide data in near real time is sometimes more complex and expensive than ge...
A: Developing real-time data-gathering systems A marketer evaluates the success of internet advertising...
Q: Provide the instruction type and assembly language instruction for the following binary values: 100...
A: Ans: Assuming MIPS assembly set 0000 00_10 000_1 0000 _1000 0_000 00_10 0000 Last 6 bits correspond ...
Q: Describe authentication, authorization, accounting, and auditing procedures
A: The answer of this question is as follows:
Q: Tb=1; fc=10; t=0:Tb/100:1; c=sqrt(2/Tb)*sin(2*pi*fc*t);
A: The goal of these BASK commands is to imitate fourier series noise. The result is a curve with a pea...
Q: SUBJECT= CLOUD COMPUTING Study about a paravirtualization based hypervisor and explain its working ...
A: Hypervisor virtualisation: Hypervisor, also known as para-virtualization, is really a virtualized st...
Q: B- Answer the following questions? 1. Multiply (10010), (11110), using binary multiplication method?...
A: The problem statement is all about performing binary multiplication addition subtraction and divisio...
Q: ved by default?
A: given - Where are the system journals saved by default?'
Q: a) Hadoop files are broken into large blocks. A typical block size used by HDFS is 128 MB. Illustrat...
A: Answer: I have given answered in the handwritten format in brief explanation
Q: Convert the following decimal fractions to binary with a maximum of six places to the right of the b...
A: Convert Decimal fractions to Binary a) Consider decimal fraction i= 25.84375 First convert the integ...
Q: Write a Java program to find the second highest number from an user entered array of integers.
A: Answer: Java Code: import java.util.*;public class Main{ public static void main(String[] args) {Sc...
Q: NA. F
A: An assembly language is a programming language that usually has one instruction for the processor to...
Q: a. Why is it dangerous for an email program to open attachments automatically, without waiting for t...
A: We need to answer the questions related to email and wifi security.
Q: Consider the function F(a,b,c) given attachment below a. Redraw the logic diagram using only NOR g...
A: Consider the function F(a,b,c) given attachment below a. Redraw the logic diagram using only NOR ...
Q: Determine the machine code of the given instructions. Include operand or address size prefix. For th...
A: We have given a assembly code instruction : MOV (DI+9DFH), DEFAH , we have asked to change it to Ma...
Q: Explain Symmetric and Asymmetric Encryption that are commonly applied in protecting the client serve...
A: Symmetric encryption : Symmetric encryption is a well established encryption technique that has b...
Q: Identify the data structure to move first bought product to be sold out first. Take sample data and...
A: A structure of data is basically data storage wherein data gets allocated in an appropriate format. ...
Q: Isn't it true that different systems place disk folders at different track places on the disk for a ...
A: Introduction: They effectively treat uncommon disorders or diseases with a long latency period betwe...
Q: Consider the below commands i) sed "s/CSH/csh/g" temp >|Is ~/newtemp 11) Is -v grep wc -1 111) Is -a...
A: Some operating systems used need commands to execute the functions unlike the operating system used ...
Q: V ( ץר) V ץר )ה
A:
Q: Convert each of the following expressions into sum of products and product of sums. 1. (u + x'w)(v +...
A: First lets understand sum of products and product of sum forms: product term means : AND operation b...
Q: What are the four distinct design considerations in a multiprocessor operating system?
A: Introduction: A multiprocessing operating system is one in which the computer's operations are contr...
Q: Do you agree with this statement or disagree with it? Give reasons to back up your claim.
A: Disagreeing with the following statement: "Agile isn't a methodology, it's a particular manner of b...
Q: Discuss how to break through deadlocks in a variety of situations.
A: Introduction : Basics: Several processors in the multiprogramming working framework fight for a limi...
Q: Provide a summary of the security services.
A: the answer is given below:-
Q: When was security the most important in the history of computing?
A: Computing: Computing is the process of completing a job using a computer or computer technology. The...
Q: A flattened Neural Network for handwritten digital classification takes in 43X43 pixel images. How m...
A: The answer is
Q: Sex Name Address SSN PERSON BirthDate Salary MajorDept EMPLOYEE ALUMNUS STUDENT Degrees Degree Major...
A: A relational schema is a blueprint used in database design to represent the data to be entered into ...
Q: Tell us about the software you used to automate data collection.
A: the answer is given below:-
Q: what are the refernces you used?
A: refernces : Using a reference, readers may learn more about the source and, if required, locate it o...
Q: Write a Java program to find the second highest number from an user entered array of integers.
A: Algorithm: for (initialExpression; testExpression; updateExpression){ // body of the loo...
Q: Explain the difference between an application programming interface (API) and an application binary ...
A:
Q: Describe a recent security compromise involving access control or authentication in the headlines. H...
A: Beach with security: A security breach occurs when an unauthorized party gains access to your data w...
Q: What exactly does "open architectural design" imply?
A: Open architecture can be simply described as an architecture whose all details are open to public. T...
Q: It is vital to comprehend how multiprocessor systems interact with one another in order to classify ...
A: let's see the solution to the question
Q: For microprocessors and their accompanying systems, power supply and dissipation limits have become ...
A: Introduction: A microprocessor is a computer processor that combines data processing logic and contr...
Q: Describe a recent security compromise involving access control or authentication in the headlines. H...
A: Any event that leads to unauthorized access to computer data, applications, networks, or devices is ...
Q: Explain the difference between an application programming interface (API) and an application binary ...
A: Introduction: Binary software modules communicate through an application binary interface (ABI). In...
Q: The CustomString class also has a “remove” method which returns a new string version of the current ...
A: Program Explanation: Define a class for string operations Define the constructor, getter, and sette...
Q: void squire(int n) { if( n <= ) time++; else { squire (n/2); squire (n/2); for (int i=0; i<n; i++) f...
A: O(N) for(int i=0;i<n;i++) : O(N) -level 1 for(int j=i;j<n;j++) : O(1) -level 2
Q: For microprocessors and their accompanying systems, power supply and dissipation limits have become ...
A: The objective is to state the reason why for microprocessors and their accompanying systems, power s...
Q: unction with one reference parameter is a pointer to an integer. The function allocates a dynamic ar...
A: The answer is an : void exercise(int*& p, size_t n);
Q: To declare a variable, 'Type' is insufficient. To put it another way, all variables contain data typ...
A: Storage Variables and functions may be identified by their class labels. Several of these qualities,...
Q: Draw the following diagram and label each component and explain the basic operation of autopilot sys...
A: The Autothrottle computer conducts the computations required for automated engine thrust control and...
Q: build a simple graphical application that is responsive and that uses basic widgets and demonstrates...
A: To get started, set up your workspace as follows: In the Project window, open app > res > lay...
Q: Why do interrupt-driven operating systems outperform non-interrupted operating systems in terms of p...
A: Introduction: Why do interrupt-driven operating systems outperform non-interrupted operating syste...
Step by step
Solved in 3 steps

- If f(n) belongs to θ( g(n)) then it belongs to O(g(n)) True or False?Consider f(n)= n2 log (n), g(n)= 0.01 n + 0.5 n2 which of the following is true? Theta = θ Omega = Ω الاجابات f(n)=O(g(n)) f(n)=Omega(g(n)) f(n)=Theta(g(n)) g(n)=O(f(n))Choose ALL correct statements if more than one are correct. Which of the following statements are true as (n gets large or n →∞)? A. n2 * 5n = O(5n) B. n5 * 2n + n2 * 5nn = O(n2 * 5n ) C. log(n5 + 7) +n2 + n = O(n) D. n0.5 + (0.5)n = O(n0.5) E. None of the above is correct.
- Find the values of a, b, c and d needed to solve this puzzle int a = ? int b = ? int c = ? int d = ? char expect[128] = "There are 10 kinds of people in the world: those who understand binary and those who don't"; char actual[128] = {}; strcpy(actual,expect); int location1 = 5; int location2 = 17; ((int *)actual)[location1] = 0x58585858; ((int *)actual)[location2] = 0x59595959; *(((int *)actual) + a) = b; *(((int *)actual) + c) = d; if(strncmp(expect,actual,BUFSIZE) == 0){ return; } failure("Here are hints:\n- use two ints with 4 bytes to make the message right\n- beware of endian ordering angst\n");Find the value of n that solves this puzzle. At what value of n does s reach 39?The code is in C int n = ? int m = 39 int t = 39; int s = 0; while(n>1){ if(n & 1){ n = (n<<2) - n + 1; } else { n = n >> 1; } if(s == t && m == t){ return; } s++; } failure("Seems you forgatz the essence of Collatz");PYTHON! How is the ouput of this 13? This confuses me def Q2(n): if (n <= 0): return 1 return 1 + Q2(n-2) + Q2(n-3)print(Q2(6))

