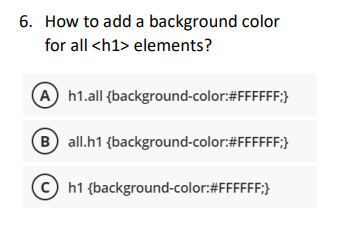
6. How to add a background color for all elements? A h1.all {background-color:#FFFFFF;} B) all.h1 {background-color:#FFFFFF;} Ch1 {background-color:#FFFFFF;}
Q: C++ tutorial on how to make a structure. Detail all of the positive aspects that come from using C++…
A: Introduction : Bjarne Stroustrup created the general-purpose computer language C++ in the middle of…
Q: F Source For the network shown below, the arc capacity from node i to node j is the number nearest…
A: For example, using Dijkstra's algorithm, you can start at node 1 and find the shortest path to node…
Q: With relation to civil rights, what are the risks provided by databases?
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: You can use the command touch to change the time stamp of a file or create a new file with a size of…
A: Introduction of commands in computer science: A command in computer science is an instruction that…
Q: Within the framework of information security, how would you characterize the concepts of confusion…
A: CONFUSION 1) In the event that there is confusion, we make an effort to complicate the relationship…
Q: Question 1 You are given a list of characters in Harry Potter. Imagine you are Minerva McGonagall,…
A: We need to define a function called character_gryffindor() that return the names of character that…
Q: Create a mask to read the 9th LSB of a 16 bit binary number. int a = rand()%; unsigned int mask mask…
A: NOTE: The hint for Question 7 is missing. Given, int a=rand()%; unsigned int mask=_______;…
Q: Web servers are often targeted by cybercriminals because they provide a lucrative opportunity for…
A: There are several techniques that can be used to prevent attacks on web servers, including: Keep…
Q: public class TestShape { public static void main(String[] args) { /* Circle c1 = new Circle(2.67);…
A: public class TestShape { public static void main(String[] args) { Circle c1 = new Circle(2.67);…
Q: Output is nearly correct, but whitespace differs. See highlights below. Special character legend…
A: Algorithm of the code: 1. Ask the user to input a highway number2. Create a variable to store the…
Q: Write a procedure to remove the nth element (from the top) of a linked stack with the rest of the…
A: pointers, the first will point to the beginning of the linked list and the second will point to the…
Q: What Characteristics Best Define Decision Patterns in Manufacturing?
A: Decision patterns in manufacturing Decision-pattern is often understood to involve choosing among…
Q: in haskell: Write a function sumNums that adds the items in a list and returns a list of the…
A: Haskell is a high-level programming language. It is a purely functional programming language.…
Q: At least four (4) of the best practices for internet security should be addressed, along with an…
A: Introduction : Internet security is the process of protecting and preserving data or information…
Q: What are the privacy and civil liberties concerns of utilizing databases?
A: The purpose of this inquiry is to bring attention to the dangers that the database system presents…
Q: You are working on problem set: Lab 1 copy (Pause) problem ID #6049 ? addStars Language/Type:…
A: In this question we have to write a function named addStars with the following given problem…
Q: It is necessary to have a conversation about best practices for internet security and how such…
A: Introduction: Network access security is the set of security features that enables a user to access…
Q: It is essential to have a clear understanding of the difference between a vulnerability screening…
A: Vulnerability Scanning: Vulnerability scanning identifies known vulnerabilities in the system or…
Q: A program may choose UDP over TCP for a number of reasons.
A: Internet Protocols Overview: Internet Protocols are a set of rules and standards used to control…
Q: Could you provide me some examples of companies that make use of databases in your IT…
A: The term "DBMS" (Database Management Systems) refers to a group of information and management…
Q: Take careful note of the essential procedures involved in delivering a website in response to a user…
A: Here are the essential steps involved in delivering a website: Requirements gathering: Gather the…
Q: What are some ways that you may protect yourself from falling prey to a phishing scam? To begin,…
A: When someone sends a false communication that looks to be from a reliable source, it is known as a…
Q: OpenDNS ROUGE 1 PC1 0001.C930.5C5C Edge Hubo PC2 0003.E418.B94B Modemternet CoreSW PC3…
A: ore Switch Port Security Fix tejeshnaiduponnamaneni@gmail.com Company ABC is currently…
Q: consider a population where 30% is in poverty. If you randomly sampled 10 people, how many would you…
A: In this question we have to discuss if a population where 30% is in poverty. If we randomly sampled…
Q: Every file and directory in a Linux system has a numerical permission value assigned to it. This…
A: Answer is attached in below step. This is related to Linux's permission set on file and directory.
Q: Create a node server with the following requirements: Use the dotenv package to manage your…
A: Here is an example code to implement the node server with the given requirements using express:…
Q: Web servers are attractive targets for attackers because it is so simple to access them. An in-depth…
A: Introduction: Website material is stored and delivered via web servers. Web servers, which are…
Q: In terms of bandwidth, do access points act more like switches or hubs?
A: 1. A computer network refers to interconnected computing devices that can exchange data and share…
Q: Given the following data definition in assembly: .data myBytes BYTE 10h,20h,30h,40h myWords WORD…
A: - We have to work on the questions in reference to the data provided in assembly. - The data ::…
Q: A case study of an existing MIS is required. (MIS)
A: A MIS is a system intended to manage information inside an organisation or business. It provides…
Q: • Prove the absorption law AU (ANB) = A. by universal generalization, applied twice to use the…
A: Double-Subset property: The double subset property states that if A is a subset of B and B is a…
Q: What is the main difference between a centralized repository and a distributed repository A. In a…
A: Please find the answer below :
Q: In the context of C, C++, and Java, what other name would you use to describe heap allocation?
A: The allocation of heap space "dynamic memory allocation" is a synonym for the phrase "heap…
Q: Internet is an international computer network that connects billions of computers located all over…
A: The Internet's underlying network infrastructure provides a number of services to its dispersed…
Q: Discuss the impact that the Internet and information systems have had on Porter's competitive forces…
A: Porter's Five Forces model developed by Michael Porter in 1979, is a framework that is used to…
Q: How would I write an operative clause on a seventh-grade level, and what is an operative clause?
A: NOTE :- Below i explain the answer in my own words by which you understand it well. The…
Q: It's impossible to build a computer without both hardware and software.
A: Hardware and software are both necessary for computers: Hardware and software are both necessary for…
Q: Using the print function, print "Happy Earth Day".
A: Algorithm: 1. Start 2. Print "Happy Earth Day" 3. End
Q: 19. Turtle Graphics: Hit the Target Modification Enhance the hit_the_target.py program that you saw…
A: Set up the turtle window with the specified width and height Draw the target at the specified…
Q: In order to fix your basic network, what network commands would you use? For a more extensive…
A: A network is defined as the connection of two or more computers to exchange information and…
Q: I need the code from start to end with no errors and the explanation for the code Objectives Java…
A: Introduction Java class: Class is a blueprint or template used to create objects in Java. It defines…
Q: What are the overarching goals and primary applications of the GROUPING SETS subclause?
A: 1. A Database Management system (or DBMS). 2. It is essentially nothing more than a computer-based…
Q: Who was the first known user of an abacus, and when did this begin to take place?
A: here is the answer:-
Q: Review the DonationTimeLeft function as a group. What value do you think the function will return if…
A: Function in programming is a sequence of instructions that performs a specific task. It takes some…
Q: Read the following description and answer all the questions below. As a project manager at the…
A: Intelligent software: Intelligent software is a type of computer program that performs tasks that…
Q: The corporation has assigned you the task of developing a plan to mitigate potential threats. The…
A: The following describes the relationship between impact, vulnerability, and threat: When a company…
Q: From both the perspective of cloud service providers and their customers, what would you say are the…
A: The difficulties of cloud computing from the standpoint of the provider The most difficult aspect is…
Q: Does making a website include several steps? Give reasons and explanations for everything you do.
A: Website: A website is a collection of webpages and related content that is hosted on a web server…
Q: It is important to explain the necessity for firewalls in order to protect the security and privacy…
A: Firewalls are an essential component of any professional network environment. The purpose of…
Q: Create a program that accepts a non-negative float as input and returns a float that has just the…
A: Algorithm : 1. Start2. Declare a float variable 'num'3. Declare an int variable 'integerPart'4.…
CSS
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Java Question - (Has 2 Parts). Based on each code, which answer out of the choices "A, B, C, D, E" is correct. Each part has one correct answer. Thank you. Part 1 - Which can nullify a JPanel’s layout manager? A. pane1.setLayout(void);B. pane1.setLayout(no);C. pane1.setLayout(false);D. pane1.setLayout();E. pane1.setLayout(null); Part 2 - Which can set the background color of "panel1" to red? A. panel1.setBackground(red);B. panel1.setBackgroundColor(red);C. panel1.setBackground(Color) = "red";D. panel1.setBackground(Color.red); E. panel1.setBackground = Color.red;True or False: By default, a JTextArea component does not perform line wrapping.It allows to change the appearance of elements in order to rotate,skew...etc as desired. transform animate keyframe transition
- Java Questions - (Has 2 Parts). Based on each code, which answer out of the choices "A, B, C, D, E" is correct. Each part has one correct answer. Thank you. Part 1 - Which sets the frame (or a "form") width to 100 pixels and the height to 200 pixels? A. setSize(100, 200);B. setSize(200, 100);C. setDims(100, 200);D. setDimensions(200, 100);E. setWidth(100); setHeight(100); Part 2 - In Java, which can ensure the "Form" class to inherit from JFrame class? A. public class Form gets JFrame { }B. public class Form inherits JFrame { }C. public class Form extends JFrame { }D. public class Form : public JFrame { }E. public class Form implements JFrame { }Draw a pokemon character using lines and shapes. Apply colors. Feel free to use the following methods:• drawLine()• drawRect()• fillRect()• drawRoundRect()• fillRoundRect()• drawOval()• fillOval()• drawArc()• fillArc()• drawPolygon()• fillPolygon()• copyArea()• setPaint()• fill()• setStroke()• draw()JAVAFX: Allowed functions for drawing (Ellipse2D,CubicCurve,QuadCurve,Arc2D) [draw all of these shapes please] ID ended with 0.1 ID ended with 2.3 ID ended with 4,5 ID ended with 6.7
- flex container is created with six elements labeled A through F as shown. A F D E C B Which declaration produce the presentation of the elements shown in the image? Flex-direction: row; justify-content: space -between Flex-direction: row- reverse; justify-content: center Flex-direction: row- reverse; justify-content: space – around Flex-direction: row-reverse; justify – content:space-between(JAVA) Draw a pokemon character using lines and shapes. Apply colors. Feel free to use the following methods:• drawLine()• drawRect()• fillRect()• drawRoundRect()• fillRoundRect()• drawOval()• fillOval()• drawArc()• fillArc()• drawPolygon()• fillPolygon()• copyArea()• setPaint()• fill()• setStroke()• draw()this is given code ShapeLab.py # create classes here and their methods def main(): win = GraphWin("Shape Test", 600, 600) l1 = Line(Point(300, 0), Point(300, 600)) l2 = Line(Point(0, 300), Point(600, 300)) l1.draw(win) l2.draw(win) shapes = [] shapes.append(Square(Point(50, 20), Point(100, 280))) # shapes.append(Ball(Point(350, 20), Point(400, 280))) # remove comment to test Ball # shapes.append(Triangle(Point(50, 320), Point(100, 570))) # remove comment to test Triangle # shapes.append(Octagon(Point(350, 320), Point(400, 570))) # remove comment to test Octagon for shape in shapes: shape.displayName(win) shape.displayNumSides(win) shape.drawShape(win) win.getMouse() win.close() if __name__ == '__main__': main() in python please
- Given the following JavaScript code: elem = document.createElement('span'). Which statement can be used to add the new element to the DOM. document.body.childNode(elem) document.body.appendChild(elem) document.body.parentNode(elem) document.body.node[1]= elemIn Python, create a GUI using Qt to convert a color to its RGB and hex values. More specifically, use a ComboBox widget to allow the user to select a color (as a string.) Once a color has been selected, the GUI will then display the RGB and Hex values. Use a Python dictionary to store the colors and their RGB/Hex values. DO NOT USE ANY PYTHON PACKAGES OR WIDGETS OTHER THAN THOSE THAT HAVE BEEN SPECIFIED IN THESE INSTRUCTIONS.JAVA APPLET Draw a pokemon character using lines and shapes. Apply colors. Feel free to use the following methods:• drawLine()• drawRect()• fillRect()• drawRoundRect()• fillRoundRect()• drawOval()• fillOval()• drawArc()• fillArc()• drawPolygon()• fillPolygon()• copyArea()• setPaint()• fill()• setStroke()• draw()



