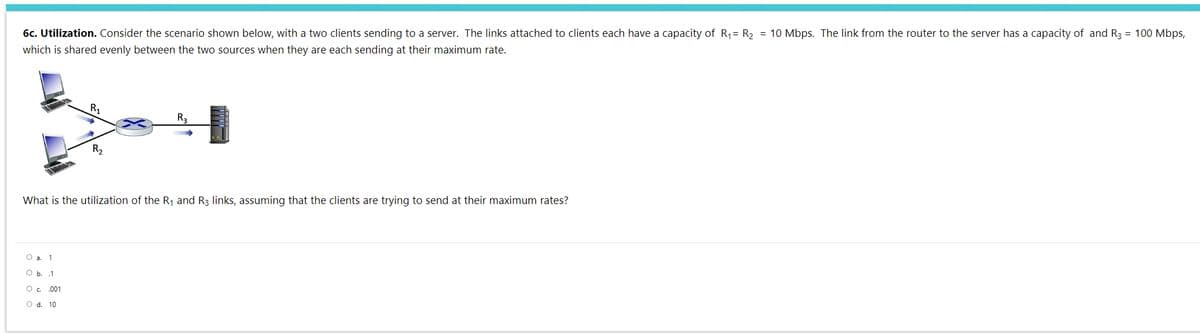
6c. Utilization. Consider the scenario shown below, with a two clients sending to a server. The links attached to clients each have a capacity of R= R2 = 10 Mbps. The link from the router to the server has a capacity of and R3 = 100 Mbps, which is shared evenly between the two sources when they are each sending at their maximum rate. R R2 What is the utilization of the R, and R3 links, assuming that the clients are trying to send their maximum rates?
Q: 1. Do you tend to acquire new technological devices before or after the majority of your friends?…
A: - We are talking about technical devices.
Q: Describe the sorts of information that the four different categories of users need.
A: Application Users are one of the user classes; these users of the system may install and execute…
Q: This is an SQL question, which is correct: Which of the following statements about JOINs are true?…
A: We are given 5 statements of SQL, we are going to see which of the given statement is right and why…
Q: Input a line of text containing numbers, and determine whether any two consecutive numbers add up to…
A: I've executed your code and it is running correctly. Incase there is any indentation problem please…
Q: [1 1-1] [1 1 -1] Given: A= 2 2 3 B= | 2 2 3 4 0 0 4 0 0] 1.9.1 Find -A+ 3B 1.9.2 Find B+(A'+A)
A: As we know A-1=Adj(A) / |A| |A| = 20 |B| = 20 A-1 = 0 0 1/4 3/5 1/5 -1/4 -2/5 1/5 0 B-1…
Q: In an eye-glass shop, a customer can buy either a pair of single prescription glasses (or a pair of…
A: Code: import java.util.*;public class MyClass { public static void main(String args[]) {…
Q: Any 10(ten) functionalities of hardware devices that might be added to assist a company's day-to-day…
A: Hardware refers to computers' actual, tangible components that perform critical functions such as…
Q: Do open source programming languages have advantages and disadvantages compared to proprietary…
A: Let's see the solution in the next steps
Q: 10. What are the most serious threats ( like bias, transparency, privacy) a law firm can face from…
A: Answer : Bias is most serious threats that a law firm can face by using AI and algorithms.
Q: What are the various stages of the Von Neumann Cycle? What happens to the CPU and main memory during…
A: Von Neumann Cycle: In the von Neumann architecture, seven stages make up the fetch-decode-execute…
Q: Identify circumstances when information utility is a meaningful criteria that isn't covered by the…
A: Multi-factor authentication enables many methods to establish identity if one of the data is…
Q: What is the difference between an embedded system, an embedded control system, and an instruction…
A: Given: An embedded system is a computer system that is part of a larger mechanical and electrical…
Q: Explain if the keyboard and scanner are input or output devices. Make a note of it on each one.
A: Explain if the keyboard and scanner are input or output devices.
Q: In terms of user and kernel threading, why not try the Sun Solaris operating system? What are the…
A: Explanation: Solar micro systems produced the Sun Solaris os, a Unix operating system. Lightweight…
Q: Any 10(ten) functionalities of hardware devices that might be added to assist a company's day-to-day…
A: According to the question, we must list ten hardware functionalities that might be deployed to…
Q: Which Azure Domain features are most beneficial? There are a slew of other cloud service providers…
A: Azure domains come with a plethora of benefits : The following are a few of them: Management of…
Q: What is the number of nodes in the sfortest linkedlist? and which is the longest?
A: LinkedList: The linked list data structure is capable of overcoming all of the restrictions of an…
Q: Write a program that calculates the points earned by a soccer team. The program reads from the user…
A: The Java code along with the snapshot of code and output is given below:
Q: given dt=datetime(2022,4,15,10,6,10),how can you output the datetime'format is "22/4/15" in python
A: In this program we have to format the date in the python code in the format "22/4/15" Let's Code…
Q: What exactly is the distinction between the von Neumann and Harvard computer architectures, please?
A: von Neumann and Harvard computer architectures are mainly tells about the ways that which of the…
Q: 43,44
A: Lets see the solution.
Q: Difference between software and web development?
A: Difference between software and web development.
Q: One of the advantages of computers is that they process data according to instructions. Choose one:…
A: answer is
Q: What are the benefits and drawbacks of using open-source programming languages against those that…
A: Drawbacks of open source vs proprietary programming languages: A language creator, a programmer…
Q: Since when has programming been around
A: Answer :
Q: Discuss how important it is to follow a well-integrated change control approach while working on it…
A: We will resolve the first three subparts for you, since your query has several subparts. To have the…
Q: Two sorted files containing sn and sm records respectively can be merged together to obtain one…
A: 1. a . pseudocode int mergeFile(int files[]) priority_queue que; //min priority queue int count=0;…
Q: Find all numbers between 100 and 999 that are equal to the sum of the cubes of their digits. Print…
A: The Answer start from step-2.
Q: Explain briefly the influence of Web services on the web development process. Give some instances of…
A: You can't say "web services" these days without immediately waking up to Amazon Web Services or the…
Q: What seems the problem here? Im using Programiz's Javascript compiler
A: You can't read data from user/console in the online editors because you can't install any libraries…
Q: What are the benefits of utilizing formal approaches in medical and aviation software development?
A: Avionics software is embedded software with legally mandated safety and reliability concerns used in…
Q: List the advantages of the top five Java frameworks for Microservices. check to ensure that you…
A: List some advantages of the best Java framework for microservices. Spring Cloud and Spring Boot The…
Q: How would you describe the characteristics of the Ubuntu operating system in terms of a server…
A: Essentially, Ubuntu's desktop edition is compatible with all of the standard Windows applications,…
Q: QUESTION 2 For each pair of functions f(n) and g(n) in the following table, pick f(n) = 0(g(n)),…
A:
Q: Provide clear, concise answers to each of the following related questions. .-.). Prove that n + n?…
A: Given: We have to proved the following related questions.
Q: List and describe any ten hardware functionalities that might be deployed to assist the business's…
A: Justification: According to the question, we must list the following ten functions of hardware…
Q: Do you know how many steps there are in web design? Each phase should be identified and explained in…
A: Web design refers to the design of websites that are displayed on the internet.
Q: there a certain number of phases involved in the web development process? Go through each step in…
A: Please find the answer below :
Q: What are the differences between how we express operations in ordinary life and how we state them in…
A: No there are no difference differences between how we express operations in ordinary life and how we…
Q: Explain me please step by step the answer is pc is 007 and ac 0077
A: PART A: PC register stands for Program Counter. The Program Counter register points to the memory…
Q: Programming languages have been developed for a variety of reasons.
A: Computer programming language is a language for displaying a precise set of digital computer…
Q: A network contains 2 routers and a number of hosts. Router 1 links with a number of hosts and forms…
A:
Q: Investigate the different information systems used by various businesses.
A: Main kinds of Information System use in Businesses: Executive Support System (ESS), Management…
Q: Do you think von Neumann's architecture is one-of-a-kind?
A: Von Neumann Architecture: A single shared memory for programmes and data, a single bus for memory…
Q: Can you help me answer these questions?
A: What is the purpose of a slack variable? These are simply the difference between the right-hand side…
Q: How many stages are in web design? In-depth explanations of each phase's importance
A: Web Design: Web design is the process of creating and displaying websites for use on the internet.…
Q: answers following Prove that n + n² +n = 0(n*). Prove that n+n² + 1 = N(n*). s). Prove that n² +n+1…
A:
Q: Where does Microsoft Azure differ from Amazon Web Services?
A: Microsoft Azure is an open source and flexible cloud platform which helps in development.
Q: What are the differences between how we express operations in ordinary life and how we state them in…
A: Introduction: Sequential operations are those that are performed one after the other. Conditional…
Q: s Google a networked s
A: Lets see the solution.
3
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Consider the extended LAN connected using bridges B1 and B2 in the Figure given below. H1 shown in the figure is a hub which has the property of taking an input on one port and forwarding it on all other ports. Suppose the forwarding tables in the two bridges are empty. List all ports on which a packet will be forwarded by bridges B1 and B2 for the following sequence of data transmissions: a) A sends a packet to C b) E sends a packet to F c) F sends a packet to E d) G sends a packet to E e) D sends a packet to A f) B sends a packet to FConsider a short, 10-meter link, over which a sender can transmit at a rate of 150 bits/sec in both directions. Suppose that packets containing data are 100,000 bits long, and packets containing only control (e.g., ACK or handshaking) are 200 bits long. Assume that N parallel connections each get 1/N of the link bandwidth. Now consider the HTTP protocol, and suppose that each downloaded object is 100 Kbits long, and that the initial downloaded object contains 10 referenced objects from the same sender. Would parallel downloads via parallel instances of non-persistent HTTP make sense in this case? Now consider persistent HTTP. Do you expect significant gains over the non-persistent case? Justify and explain your answerAccording to the given figure, assume that, PC0 wants to send a message to PC4. If the distance between the two points is 22,000 km, 3.2-kbyte message sends in 2.4 x 100000000 mls speed through cable and the transmission link has 1.5 Gbps Bandwidth. When the message arrives at Routers , Router0 already has 4 packets to process in the queue and each will need 2ms. Router1 has no packets in the queue, but if it had then would require 3ms to process. Router2 already has 5 packets to process in the queue and each will need 1ms. Calculate the total time to send the message from PC0 to PC4.
- Consider the following diagram: A,B,C and D are subnets, R1, R2, and R3 are routers. Default signifies theentire rest of the internet. All 4 subnets each contain the same number of hosts.Consider the following routing table at R3: CIDR Mask Link 0.0.0.0/0 L4 128.4.6.0/24 L3 128.4.8.0/24 L5 1. If 128.4.6.0 is in A, what is the routing table at R1? 2. The ISP that owns all these networks is short on IP addresses, so theyuse a NAT router for R2. How many public IP addresses will C andD use together assuming they use as many private 10.X IP addresses asthey can? How many total public IP addresses will be used by the entirenetwork? Why doesn’t the ISP care about how many private IP addressesare used? 3. Fix R3’s routing table now that we are using NAT: 4. A node in C is given the IP address 10.0.0.1 and only sends and receivespackets on port 1234. A packet destined for this node reaches R2 witha source of (IP=128.4.6.6, Port=3000) and destination of (IP=128.4.8.0,Port=10000).…Consider a network with 4 links between two hosts where the maximum allowable packet size is 1000 bits; each link has a transmission rate of 2000 bits per second, except the second link has a transmission rate of 1000 bits per second. How long does it take to send 6000 bits from one host to the other? You may ignore propogation delay, assume there is no other traffic on the network, and assume that no routers drop packets due to queue length. Round your answer to two decimal places.Consider this multihpop network running the 802.11 MAC protocol in ad-hoc mode (RTS-CTS-DATA-ACK) and a link speed of 1 Mbps: A === B === C === D Edges ‘===’ represent connectivity, so, for instance, nodes B and C can communicate with each other directly, but A and C cannot. All nodes are able to route packets on behalf of the other nodes and they employ store-and-forward to deliver packets to the destination. Suppose nodes A, B, and C have to send a lot of data frames to node D and have their link layer queue always full. What is the average data rate for A, B, and C assuming no DATA frames get lost due collisions? Explain your answer. Compare the data rates with the link rate.
- Consider a scenario in which Host A and Host B want to send messages to Host C. Hosts A and C are connected by a channel that can lose and corrupt (but not reorder) messages. Hosts B and C are connected by another channel (independent of the channel connecting A and C) with the same properties. The transport layer at Host C should alternate in delivering messages from A and B to the layer above (that is, it should first deliver the data from a packet from A, then the data from a packet from B, and so on). Design a stop-and-wait-like error-control protocol for reliably transferring packets from A and B to C, with alternating delivery at C as described above. Give FSM descriptions of A and C.Consider the scenario shown below, with four different servers connected to four different clients over four three-hop paths. The four pairs share a common middle hop with a transmission capacity of R = 300 Mbps. The four links from the servers to the shared link have a transmission capacity of RS = 50 Mbps. Each of the four links from the shared middle link to a client has a transmission capacity of RC = 90 Mbps. Assuming that the servers are all sending at their maximum rate possible, what are the link utilizations of the client links (with transmission capacity RC)? Enter your answer in a decimal form of 1.00 (if the utilization is 1) or 0.xx (if the utilization is less than 1, rounded to the closest xx). The utilization of client link is:Consider the scenario shown below, with four different servers connected to four different clients over four three-hop paths. The four pairs share a common middle hop with a transmission capacity of R = 300 Mbps. The four links from the servers to the shared link have a transmission capacity of RS = 50 Mbps. Each of the four links from the shared middle link to a client has a transmission capacity of RC = 90 Mbps.......Assuming that the servers are all sending at their maximum rate possible, what are the link utilizations for the server links (with transmission capacity RS)? Enter your answer in a decimal form of 1.00 (if the utilization is 1) or 0.xx (if the utilization is less than 1, rounded to the closest xx)?
- Consider the scenario below where 4 TCP senders are connected to 4 receivers. The servers transmit to the receiving hosts at the fastest rate possible (i.e., at the rate at which the bottleneck link between a server and its destination is operating at 100% utilization, and is fairly shared among the connections passing through that link). R =1 Gbps and Rc is 300 Mbps and Rs is 400 Mbps. And that all four senders have data to send, What is the minimum value of Re that will ensure that the connections to Host-1 and Host-2 are not bottlenecked at links with capacity Rc or Re?Consider the following configuration to connect host A to host B through the three middle nodes with using packet switching to forward packets. Assume the throughput rates for links are R1= 10Mbps, R2=15Mbps, R3=7Mbps, and R4= 10Mbps. How long takes to transfer a file with size of 500MB from host A to Host B? (No queuing, processing delay)?1.4.12.2 End-to-end Delay. Consider again the network shown above. The links again have transmission rates of R1 = R2 = 100 Mbps (i.e., 100 x 106 bits per second), and each packet is 1 Mbit (106 bits) in size. Assume that the propagation delay is 1 msec per link. What is the end-to-end delay of a packet from when it first begins transmission at the sender, until it is received in full by the server at the end of the rightmost link. Assume store-and forward packet transmission. You can assume the queueing delay is zero. Answer choices: A. 2 x 106 msec b. 2.01 msec C. 1.1 msec D. 2.02 msec 1.4.12.3 Maximum Throughput. Consider again the network shown above. The links again have transmission rates of R1 = R2 = 100 Mbps Assume that the link R2 is fairly shared (as we've seen is done via TCP) between the two sessions. What is the maximum end-to-end throughput achieve by each session, assuming both sessions are sending at the maximum rate possible? Answer choices:…

