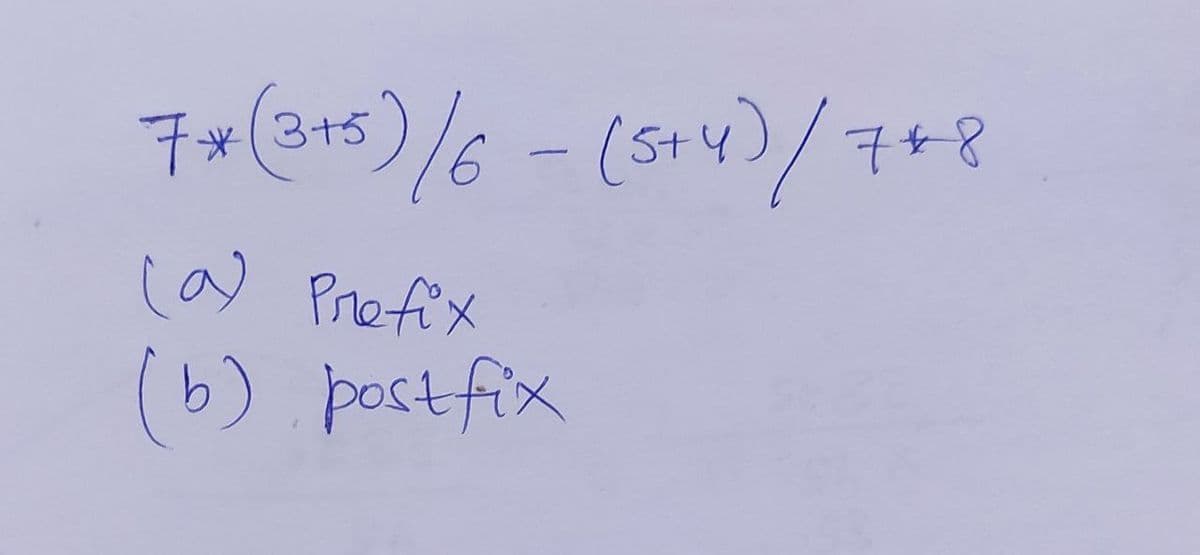
7*(3+5 5/6-(544)/7+8 ca) Prefix (b) postfix
Q: 2. Create a program that implements all different kinds inhenitance. Use any object to represent you...
A: Introdution:There are 6 types of inheritance in total. Single inheritance Multi-level inheritanc...
Q: What will be printed after executing the following statement: Blank 1 cout << 30 % 4 * 5; Blank 1 Ad...
A: The given problem can be solved with the knowledge of operator precedence. Operator precedence means...
Q: protected void onSavelnstanceState(@NonNull Bundle outState) { outState.putlnt("userID", 101); super...
A: Introduction:The Snippet tells about the on saved instance state of the input that is being passed.T...
Q: 1) . ....reliable transport between sending and receiving process (TCP, UDP) 2) does not provide flo...
A: 1. Answer. TCP 2.answer UDP 3.answer. TCP 4.answer. Client
Q: I do not need any working , need corect option please very fast Please very fast What are the smalle...
A: As we know that in the 16 bit numbers The largest positive number is 32767 and smallest number is ...
Q: Calculate the results (both binary and hexadecimal values) with calculation step and show the status...
A: Here is the detailed explanation of the solution
Q: Take two 3*2 matrix from user input. Then find the sum and average of column1,row1 of both matrix. ...
A: Algorithm: Import the scanner class Create a class named TwoMatrixOperations Create a public stati...
Q: 1). ....reliable transport between sending and receiving process (TCP, UDP)
A: As per guidelines I can answer only first 3 sub-parts. I hope you will understand. Thank You. 1. TC...
Q: Decide on the definition of the binary digit.
A: EXPLANATION AND ANSWER: Binary digit: The smallest unit of information is the binary digit. It is us...
Q: create a circle using javafx , count how many times the circle is being clicked and change its color...
A: Create a javafx code Create a circle Count how many times circle clicked. Change the color When clic...
Q: In Insertion Sort Ascending Order Show the step by step process on how sorting was done such as ...
A: Insertion sort has the time complexity of O(n2).
Q: 1. The following is a (silly) decision structure: a, b, c = input('Enter three numbers: ') if a > b:...
A: First note that there are some errors in the program -- clearly the author wrote this for python 2 a...
Q: ID: A 9. Directions: The question or incomplete statement below is followed by four suggested answer...
A: We have been given a question in which four statements are provided which result in correct form of ...
Q: Python code for Turtle Race Write the name of the winner turtle on the screen and on the console. Ad...
A: Code : from turtle import Screen, Turtle, mainloopfrom random import randint COLORS = ['red', 'blue'...
Q: Given a BSC with p = 0.8 and P = 0.7 Compute the output probability distribution: q, and pte qo = Pr...
A: A probability distribution depicts the expected outcomes of possible values for a given data gener...
Q: What are the repercussions of the cloud computing movement in terms of business? Do you have the abi...
A: Introduction: What implications does the cloud computing trend have?Are you a person who collaborate...
Q: To be able to use cin,cout we need to include this library <include<cmath# <include<string# <include...
A: Answer is in step 2
Q: In JAVA I need a program that has 5 attributes for one object.
A: A java class can have attributes. The attributes can be defined as the data types of data that is pl...
Q: velop and test a program according to the following specification. Consider a class Student with ins...
A: Lets see the solution.
Q: Minicomputer, mainframe and supercomputer are the three different kinds of computers available in th...
A: MINICOMPUTER: A minicomputer is a computer that is smaller, cheaper, and less powerful than a mainf...
Q: On Our Everyday Lives and in Society: The Effects of Information Technology Make a convincing argume...
A: Introduction: The Impact of Information Technology on Our Everyday Lives and Society Make an argumen...
Q: I'm not sure I understand what you mean by "two level logic." Is there any form of relationship betw...
A: A logic architecture that employs no more than two logic gates between input and output is referred ...
Q: What exactly is the Protector role?
A: What exactly is the Protector role?
Q: Assume that you are working in a cloud consulting company and part of the team for generating a clou...
A: Cloud computing - Cloud computing technology enables the users access to software, storage, servers,...
Q: a. Discuss what will happen you decide to change the splitting criterion. Explain how you are changi...
A: As per bartleby policy I have to answer only one question but still I answered for both. Hope this w...
Q: n which static testing techniques, we may use and maintain testing metrics? Technical reviews Desk...
A: Static testing is done so as to correct out basic code errors before moving the application into pro...
Q: Draw the following DFA over the alphabet E ={0,1}with 3 final states. →1 2 V3 V4 /5 2 2 6 1 5 2 4 3 ...
A: Here, we are going to find the minimum DFA and also it's simplified regular expression.
Q: 13. Encrypt the plaintext message GOLD MEDAL using the RSA algorithm with key (2561,3).
A: NOTE :- Below i explain the answer in my own words by which you understand it well.
Q: What is the decimal value of var1 at the end of following program? char vari = 8, var2 = 3; short in...
A: The assembly language contains registers and instructions. It is not easily understandable by humans...
Q: When it comes to port scanning, how do the four different Nmap scanning types interact with the thre...
A: Introduction : It was used to map out the network that the Network Administrator was in charge of. I...
Q: 2. Let D be a distribution over R where the mean is 5 and variance is 9. Suppose x1, . . . , x10 are...
A: Python Programming Language has been used for the sample and plot generation. import numpy as npimpo...
Q: the several types of cybercrime and the consequences of each Determine the most effective measures f...
A: Introduction: The internet is a primary driver of technological advancement. The internet has broug...
Q: Write a class called Name that has one instance variable to store the full name of a person. A name ...
A: public class Main{ public static void main(String[] args) { Name name = new Name(" Bartleby Expert...
Q: what’s with these double-underlined links in the middle of the page that pop out ads when you mouse ...
A: This sounds like an advertisement coming from the website. Advertising funds websites that deliver o...
Q: Gambling And Casino PROBLEM 23 – 0553: roulette with a basic program. Simulate a game of American
A: Step1:Te above game can be written in C/C++ programming .
Q: a. Write a python program that writes data to a file. The data consists of a series of records, each...
A: the answer for above question is :
Q: X y
A: Here are some of the laws that had been used in the question which are laws of the boolean algebra ...
Q: a) Draw the state diagrams for the finite-state machines with the following state tables. f Input 1 ...
A: Obtaining a diagram of the regional transformation in the system follows almost the backward process...
Q: (a) If r and s are regular expressions, explain why (r+s)* # r* + s* . (b) Also carefully explain wh...
A: let us see the answer:- "Since you have asked multiple questions I am solving the first for you if ...
Q: Used Python programming. Let's think of some creative ideas and implement them in this project. Yes!...
A: Now at first you can collect the images of the gates and truthtables as you want . Make sure the ima...
Q: In the below code segment, the Age item that is with the red font color represents: class Employee {...
A: The code is written in C#.
Q: cts might arise when designing an architecture for which both availability and secu
A: Design conflicts might arise when designing an architecture for which both availability and security...
Q: What is the stated mission of the SANS organization? Specifically, what role does it play in the pro...
A: Introduction: SANS was founded in 1989 as a cooperative for information security thought leadership ...
Q: 1. Let G be a graph with spectrum (.3.6 ). 3,3,6 (a) How many vertices does G have? Is G bipartite? ...
A: Let G = (V, E) be the graph. V-shaped elements are called vertices ofG and E elements are called G e...
Q: 8. a Write a program that will predict the size of a population of organisms. The program should ask...
A: The following step illustrates the implementation of the prediction about the population size of org...
Q: Statisticians use the concepts of mean and standard deviation to describe a collection of numbers. T...
A: Find the required code given as below and output:
Q: Consider the following three case studies in which discrete event simulation was used.
A: Introduction: Simulating discrete events (DES), which has been used in many different fields for yea...
Q: Explain the differences between three different types of networks and their applications and limits.
A: Introduction Explain the differences between three different types of networks and their application...
Q: CREATE A SCENARIO WITH TWO COMPUTER DEVICES TRANSFERRING A VIDEO FILE USING AN UNSECURED FTP CONNECT...
A: Introduction: Given that a common scenario includes two computers transferring a video file over an ...
Q: ployee struct as a single struct. You wi employees out to a file. The SAVE com Y argument and return...
A: The file code is given as,
Step by step
Solved in 2 steps

- C program A decimal number between 0 and 32 exclusive can be expressed in binary system as x4x3x2x1x0, where xi ’s are either zero or one. Write a C program that accepts (from the terminal) a decimal number in the above range and prints out the equivalent binary representation.Correct this in C <declares> -> <keyword> <ident> ; | <keyword> <ident> ; <declares>Basic C OperationsQ1. The Fibonacci numbers are computed according to the following relation: F, = F4 + F.-2 with F, = F = 1 Write a program that ask the user to input an integer n and then output all Fibonacci numbers from F0 to Fn. (convert the previous matlab code to C)
- C Language Explain the terms infix expression, prefix expression, and postfix expression. Convert the following infix expressions to their postfix and prefix equivalents: (a) A * B + C (b) A / B * C - D (c) A + (B - C) / D * (E + F) Thank youJAVA and Netbeans Using Looping Statement, Create a simple Multiplication Table for user input number (same as below):Define escape character.



